1.0 Executive Summary
The rapid adaptation of commercial off-the-shelf unmanned aerial systems for tactical deployment represents a profound shift in modern military operations and asymmetrical engagements. The period between 2022 and 2026 has provided empirical evidence that the integration of relatively inexpensive platforms, such as First Person View quadcopters and modified consumer drones, has fundamentally compressed the decision cycle of small tactical units.1 This report investigates the complete lifecycle of these modifications, focusing on the sophisticated firmware reverse engineering required to bypass manufacturer restrictions and the physical engineering required to integrate secondary optical payloads and kinetic release mechanisms.
The first phase of this lifecycle involves defeating digital restrictions imposed by manufacturers, specifically geo-fencing algorithms and Remote Identification broadcast protocols. Analysis of open-source intelligence reveals a mature ecosystem of software tools capable of decrypting proprietary firmware containers, modifying flight controller parameters, and spoofing identification beacons.2 These software modifications are an absolute prerequisite for operating commercial hardware in contested airspace, where factory-coded safety limits and tracking beacons would otherwise compromise the platform and its operator.
The second phase of the lifecycle involves hardware augmentation. Commercial platforms are frequently upgraded with secondary thermal optics, such as the FLIR Boson 640 and FLIR Lepton 3.5, utilizing independent analog video transmission links operating on the 5.8GHz frequency band.4 This allows operators to maintain operational security and bypass encrypted digital downlinks. Furthermore, operators have developed robust, servo-actuated payload release mechanisms that interface directly with open-source flight controllers or rely on external optical sensors to trigger kinetic deployments without altering the host drone’s internal wiring.6
This document details the technical mechanics, software methodologies, and hardware configurations that enable these tactical modifications. A final validation section provides current market availability and verified sourcing links for the commercial components utilized in these integrations, confirming the accessibility of this technology in the current market landscape.
2.0 The Strategic and Economic Paradigm Shift in Unmanned Aerial Warfare
The strategic landscape of localized and theater-level conflicts has been permanently altered by the proliferation of heavily modified consumer drones. These systems have transitioned from passive intelligence gathering tools utilized primarily by hobbyists and videographers into active, precision-strike assets.
2.1 Tactical Network-Centric Warfare and Asymmetrical Economics
The widespread deployment of commercial drones during the Ukraine conflict has been identified by researchers as a catalyst for a new Revolution in Military Affairs.1 This evolution is characterized by the implementation of Tactical Network-Centric Warfare. In this operational model, small infantry units leverage decentralized networks of low-cost drones to achieve real-time information dominance and immediate strike capabilities.1 This architecture compresses the traditional Intelligence, Surveillance, and Reconnaissance to strike loop, allowing operators to detect and engage targets in a matter of minutes rather than hours or days. The sheer mass deployment of these modified platforms has rendered traditional ground-based defense systems increasingly vulnerable.1
The economic asymmetry of this warfare model is highly pronounced and heavily favors the deploying force over the defending force. Traditional air defense economics are actively collapsing under the strain of low-cost unmanned systems.8 For example, a defensive posture may require the launch of a four million dollar Patriot missile interceptor to defeat a drone manufactured for merely twenty thousand dollars, such as the Shahed series.8 This unsustainable cost disparity forces military organizations to rethink their detection, tracking, and interception paradigms. The economic advantage is even more dramatic when analyzing Do-It-Yourself modifications, where a consumer platform costing less than two thousand dollars can deliver ordnance capable of destroying multi-million dollar armored vehicles.
2.2 The Migration Toward RF-Silent and Custom Platforms
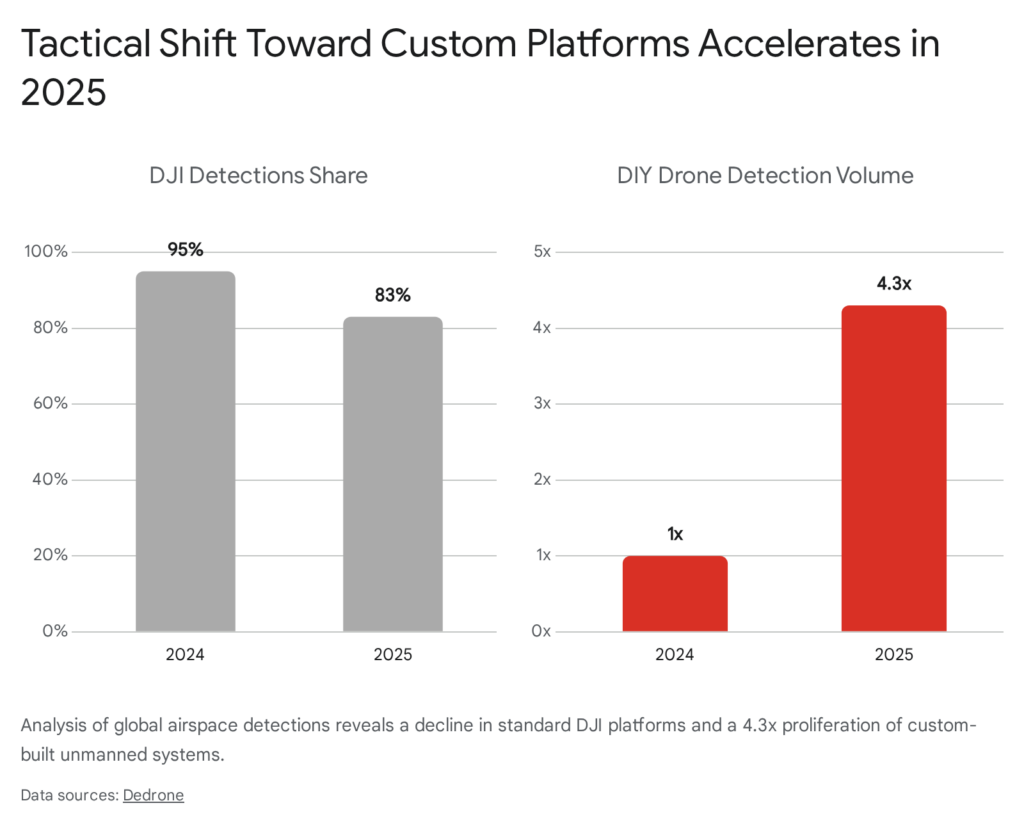
Recent intelligence data highlights a significant shift in the types of drones utilized in tactical scenarios. While proprietary platforms manufactured by industry leaders like DJI historically dominated the airspace, accounting for 95 percent of all detections globally in 2024, this figure experienced a meaningful drop to 83 percent by early 2025.8 Concurrently, airspace security networks recorded a 4.3x increase in the detection of custom, Do-It-Yourself drone platforms.8
This statistical trend indicates a calculated tactical pivot toward systems that are intentionally designed to be radio-frequency silent or to operate on non-standard frequencies, thereby blinding existing commercial sensor networks.8 Operators are actively moving away from closed-ecosystem platforms that enforce compliance and toward open-source flight controllers that offer unrestricted control over radio emissions. Furthermore, tactical operations are increasingly conducted in adverse environmental conditions, with 37.5 percent of drone detections in early 2025 occurring in low-visibility environments.8 This underscores the critical operational requirement for secondary thermal optics, which allow tactical modified drones to function effectively at night or through atmospheric obscurants.
2.3 Broader Strategic Adaptations and State-Sponsored Systems
The principles driving the modification of commercial off-the-shelf drones have also influenced the development of larger, state-sponsored unmanned systems designed for strategic depth. The engineering philosophy of utilizing widely available commercial components to build inexpensive, long-range platforms is evident in systems like the Ukrainian AN-196 Liutyi drone, frequently referred to as the “Ukrainian Shahed”.9 Similar strategic platforms, including the UJ-26 Bober and the AQ 400 Scythe, demonstrate how the cost-efficiency of commercial drone technology has scaled upward to deliver precision munitions over strategic ranges.9
These larger platforms operate on the same fundamental principles as their smaller tactical counterparts, utilizing commercial global positioning systems, standard flight controllers, and commercially available internal combustion engines to achieve ranges that challenge traditional air defense networks. This structural overlap means that breakthroughs in firmware reverse engineering and hardware integration for small quadcopters directly inform the development of larger, more lethal systems.
3.0 Embedded Systems and Firmware Architecture Analysis
A critical requirement for the tactical deployment of consumer drones is the removal of software-level restrictions imposed by the manufacturer. Companies implement geo-fencing to prevent flights in restricted airspace and enforce altitude limits to comply with civilian aviation authorities.10 Tactical operators must bypass these limitations to ensure uninterrupted functionality in contested environments. To achieve this, operators must first understand and deconstruct the drone’s underlying firmware architecture.
3.1 Hardware Modules and Serial Communication Protocols
Modern commercial drones operate as complex embedded systems, relying on an architecture of interconnected programmable modules.2 These modules include central processing microcontrollers, Field Programmable Gate Arrays, and dedicated media processors for video encoding.2 The physical architecture features specialized printed circuit boards for distinct functions. For example, the main flight controller board handles core navigation and stabilization algorithms, while separate encoder boards manage live video streams, and individual electronic speed controllers route modulated power to the brushless motors.2
These internal modules primarily communicate using a binary packet protocol transmitted over serial interfaces like Universal Asynchronous Receiver-Transmitter connections.2 In the DJI ecosystem, this proprietary communication standard is known as the DUML protocol.2 In some instances, a Controller Area Network bus or a Serial Peripheral Interface is utilized for high-speed data transfer between sensors and the central processor.2 Researchers mapping this architecture have found that while the physical design of the printed circuit boards changes between drone generations, the fundamental module identifiers and communication protocols remain highly consistent across product lines.2
3.2 The MAVLink Protocol and Control Vulnerabilities
For open-source platforms, communication between the Ground Control Station and the Unmanned Aerial Vehicle is typically facilitated by the Micro Air Vehicle Link protocol, widely known as MAVLink.11 The MAVLink protocol operates over a telemetry transmitter and receiver, sending structured messages to the drone’s flight controller hardware, which is frequently a Pixhawk unit running ArduPilot firmware.11
The flight controller uses data from internal sensors, including accelerometers, gyroscopes, and barometers, combined with external Global Positioning System data, to maintain stable flight.11 During the system boot process, the ArduPilot firmware loads configuration parameters and performs critical arming checks to ensure all sensors are functioning correctly before allowing the motors to spin.11
However, the MAVLink protocol has been identified as a significant entry point for exploiting unmanned aerial systems.11 Because MAVLink messages are frequently transmitted without robust cryptographic authentication, malicious actors or tactical operators can inject fabricated commands into the telemetry stream. By understanding the controller models implemented in ArduPilot and manipulating the exception-handling mechanisms, operators can override factory safety parameters, force the drone to execute unauthorized maneuvers, or bypass pre-flight arming checks entirely.11
3.3 Dynamic Analysis of Drone Firmware
Because these platforms function as standard embedded systems, reverse engineering their firmware does not require novel computer science techniques. Instead, standard dynamic and static analysis tools utilized for auditing Internet of Things devices are highly effective for analyzing drone code.12
Security researchers and tactical operators routinely utilize the Ghidra software reverse engineering framework to perform disassembly, decompilation, and script-based analysis of the compiled drone binaries.13 Ghidra, originally created and maintained by the National Security Agency Research Directorate, includes a suite of high-end software analysis tools that enable users to analyze compiled code on a variety of architectures, particularly the ARM instruction sets commonly found in drone microcontrollers.13
Additionally, tools like binwalk are heavily utilized to analyze binary files, identify embedded file systems, and extract executable code from compressed firmware images.15 However, researchers have noted that because drones utilize intricate firmware architectures that do not operate on a singular monolithic binary system, full system emulation is challenging, and the absence of publicly available source code renders many automated fuzzing tools ineffective.12 Therefore, manual static analysis and targeted dynamic analysis remain the primary methods for discovering firmware vulnerabilities.12
4.0 The Firmware Decryption and Parameter Modification Pipeline
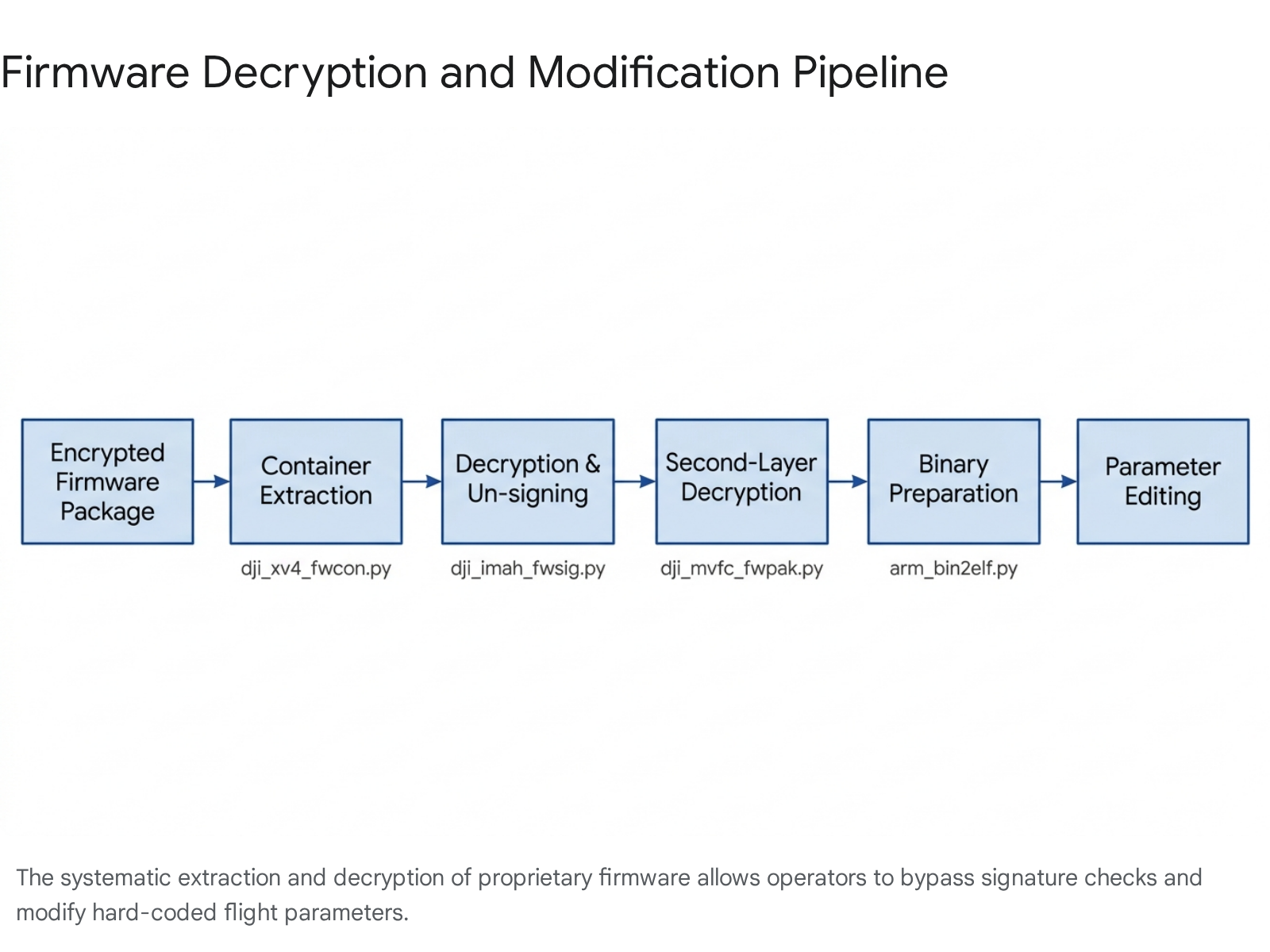
To permanently modify flight parameters and disable restrictions, operators must unpack, decrypt, and alter the manufacturer’s firmware updates before flashing them onto the drone. The open-source community has developed specialized Python toolchains, such as the dji-firmware-tools repository, to execute this highly technical process.2
4.1 Multi-Layer Decryption Mechanics
The decryption pipeline follows a structured, multi-layer approach designed to strip away the manufacturer’s cryptographic protections layer by layer.
The first step is container extraction. Firmware packages often utilize proprietary container formats to bundle multiple module updates into a single file. Scripts such as dji_xv4_fwcon.py are executed from the command line to extract individual hardware modules from package files wrapped in specific headers, such as the xV4 container format.2
The second step is signature removal and decryption. Many critical modules are protected by asymmetric cryptography and digitally signed to prevent tampering. Tools like dji_imah_fwsig.py are designed to decrypt and un-sign modules utilizing known public encryption keys extracted from the drone’s file system, such as PRAK-2017-01 or PUEK-2017-07.2 It is important to note that re-signing these modules is generally impossible without possessing the manufacturer’s private key. Consequently, operators must root the host drone to bypass the operating system’s internal signature verification checks before flashing the modified, unsigned code back to the hardware.2
The third step involves defeating second-layer encryption. On advanced platforms like the Mavic Pro, Spark, and Inspire 2, the flight controller firmware features an additional layer of obfuscation. This secondary encryption is systematically stripped using the dji_mvfc_fwpak.py utility, yielding the raw binary executable.2 For older drones utilizing Ambarella chipsets, such as the Phantom 3 Professional, operators utilize specific scripts like amba_fwpak.py to extract partitions and amba_romfs.py to manipulate the read-only file system, while amba_ubifs.sh is used to mount Unsorted Block Image File System partitions for direct file modification.2
| Decryption Tool Name | Target Application | Primary Function |
| dji_xv4_fwcon.py | Firmware Packages | Extracts modules from standard xV4 container files. |
| dji_imah_fwsig.py | Signed Modules | Decrypts and un-signs firmware using known public keys. |
| dji_mvfc_fwpak.py | Advanced Flight Controllers | Removes second-layer encryption on specific DJI models. |
| amba_fwpak.py | Ambarella Chipsets | Extracts partitions from older drone architectures. |
| arm_bin2elf.py | Raw ARM Binaries | Wraps raw binaries in ELF headers for Ghidra analysis. |
4.2 Binary Preparation and Memory Mapping
Once the raw ARM binary images are extracted and decrypted, they must be formatted for analysis. Raw binaries lack the structural metadata required by standard disassemblers to distinguish between executable code and static data. To solve this, operators utilize the arm_bin2elf.py tool, which wraps the raw ARM binary with an Executable and Linkable Format header.2
This tool performs a critical optimization process. It algorithmically analyzes the binary file to detect the boundary between the code section, known as .text, and the data section, known as .data. It frequently utilizes the .ARM.exidx index table as a separator if it exists within the file.2 Users must define specific base memory addresses, often found in the microcontroller’s technical programming guides, and establish .bss sections. This optimization is absolutely vital to avoid massive memory consumption and prevent disassemblers like Ghidra from crashing during the analysis of large firmware files.2
4.3 Direct Parameter Manipulation
With the architecture mapped and the firmware decrypted, operators can modify the drone’s behavioral parameters. This is primarily achieved through command-line interfaces. Scripts like comm_og_service_tool.py act as a powerful alternative to official manufacturer software, allowing users to interface directly with the drone via serial or Inter-Integrated Circuit connections.2
Using this tool, operators can send specific commands to the flight controller to modify hundreds of parameters that dictate flight behavior. For example, an operator can command the script to query the g_config.flying_limit.max_height_0 parameter and overwrite it with a new integer, effectively lifting the hard-coded altitude ceiling permanently.2
If the required modifications exceed the acceptable ranges hard-coded into the standard flight controller logic, operators must utilize dji_flyc_param_ed.py to edit the parameter definitions directly within the extracted binary modules, repackage the firmware, and flash it back to the rooted drone.2 This invasive level of modification allows operators to completely disable hardware pairing restrictions, enabling the integration of unauthorized third-party batteries or aftermarket camera gimbals.
5.0 Defeating Geographic Restrictions and Remote Identification
The ability to manipulate firmware parameters is most frequently applied to defeat two specific safety mechanisms: geo-fencing and Remote Identification. In a tactical context, these civilian safety features are severe liabilities that can ground a drone during a critical mission or broadcast the operator’s precise physical location to enemy forces.
5.1 Geo-Fencing Bypass Tactics and Signal Amplification
Geo-fencing is a software feature that forces a drone to land or prevents its motors from arming if the onboard Global Positioning System registers a location within a restricted zone, such as an airport or military installation.10 Historically, users could disable this restriction simply by rolling back the drone’s firmware to an earlier version released before the geo-fencing algorithms were implemented.10 Applications like No Limit Dronez provide simple, user-friendly interfaces to execute these downgrades via a Universal Serial Bus connection.10 Other manufacturers, such as Yuneec and Parrot, historically allowed users to disable geo-fencing directly within their native mobile applications without requiring third-party software hacks.10
In addition to removing geographic limits, operators frequently modify parameters to boost radio frequency power output, artificially extending the drone’s operational range. Drones and their controllers are restricted by Federal Communications Commission regulations, which limit the transmission power to prevent interference.10 Tactical operators bypass these limits by hacking the controller firmware to force the hardware into high-power modes, upgrading the standard 2-decibel stock antennas to 4-decibel directional antennas, and adding inline power boosters to the radio controller.10 The Drone-Tweaks application is commonly used to force DJI drones from the restricted European CE mode into the higher-powered FCC mode without modifying the drone’s internal firmware, relying instead on a modified mobile application to send the configuration commands.16
5.2 The Remote ID Protocol and AeroScope Encryption
Remote Identification is a regulatory protocol designed to act as an electronic license plate for drones.17 Dictated by international standards such as ASTM F3411-19/22, this protocol mandates that drones broadcast their identity, precise geographic location, altitude, and the pilot’s control station position to ground receivers using Wi-Fi or Bluetooth signals.17
In tactical environments, broadcasting this telemetry is highly dangerous. Opposing electronic warfare teams utilize sophisticated counter-unmanned aerial systems, such as the DJI AeroScope platform, to intercept these broadcasts and triangulate operator positions for immediate artillery targeting.3 Security firms reverse-engineering the AeroScope platform have discovered that it utilizes a specific protocol structure.20 Recent hardware upgrades to the AeroScope system implemented a layer of encryption over the existing Drone ID protocol, utilizing CRYP packets to encode the aircraft serial number and GPS position.20 This ensures that only authorized AeroScope receivers connected to the manufacturer’s servers can successfully decrypt and process the telemetry packages.20
5.3 Privacy Flag Manipulation via CIAJeepDoors
Disabling Remote ID on modern platforms is intentionally difficult, as manufacturers design the system to be mandatory for flight initiation.17 For example, the FAA Remote ID function is automatically enabled on platforms like the DJI Mini 4 Pro when flown with specific high-capacity batteries and cannot be disabled through standard user interfaces.17
However, operators utilize specific vulnerabilities to halt the transmission of usable data. One prominent method involves a Python utility known as CIAJeepDoors, an anagram for DJI AeroScope.3 This software leverages the proprietary DUML packet protocol to manipulate specific privacy flags residing within the drone’s memory structure.3 By executing a complex command string via a serial connection, such as ./comm_serialtalk.py /dev/ttyACM0 -a 2 -t 1000 -r 0300 -s 3 -i 218 -x 0500000000, the operator alters an internal eight-bit privacy mask.3
Within this specific bitmask, individual bits control distinct telemetry fields.3 Bit 1 controls the broadcasting of the hardware serial number. Bit 2 dictates the transmission of the state matrix, which includes spatial position, roll angle, yaw angle, and raw inertial measurement unit data. Bit 3 hides the Return-to-Home coordinate, while Bit 4 controls the core DroneID broadcast beacon itself. Bit 7 is particularly critical, as it controls the transmission of the pilot’s physical location.3
Setting the entire bitmask string to 00000000 commands the hardware to cease populating these fields.3 It is critical to understand the technical nuance of this exploit: this method does not completely silence the radio frequency emissions. Instead, it forces the drone to transmit validly formatted location packets that contain null data or a fabricated serial number.3 Because the drone’s radio is still emitting an active RF signal to communicate with the controller, electronic warfare specialists can still locate the drone via traditional radio direction-finding techniques, commonly referred to as foxhunting.3 Furthermore, if an operator connects the drone to the manufacturer’s mobile application on an iOS device, the software is known to automatically detect the discrepancy, overwrite the privacy bits, and re-enable the tracking beacons, rendering the modification useless.3
| Drone Model | Remote ID Support | Disablement Capability |
| DJI Avata 2 | Supported Natively | Mandatory; cannot be disabled natively. |
| DJI Mini 4 Pro | Supported Natively | Mandatory when using high-capacity battery. |
| DJI Mini 3 Pro | Firmware V01.00.04.00+ | Automatically enabled regardless of battery type. |
| DJI Mavic 2 Enterprise | Firmware V01.00.06.21+ | Supported via firmware update. |
| DJI Mini 2 SE / 4K | Not Supported | Requires third-party external broadcast module. |
5.4 Remote ID Spoofing and Signal Flooding
To actively counter tracking mechanisms rather than just hiding from them, tactical operators deploy Remote ID spoofers. Because the ASTM F3411 protocol standard lacks cryptographic authentication or data integrity verification, it is inherently vulnerable to message injection and impersonation attacks in uncontrolled environments.18
Security researchers have developed open-source tools, such as the RemoteIDSpoofer repository by developer jjshoots, that run on inexpensive ESP32 microcontrollers to broadcast fabricated Remote ID packets.18 The process requires downloading the Arduino Integrated Development Environment, installing the specific ESP32 board manager packages, and uploading the compiled C-code library at a baud rate of 460800.24
These software tools utilize libraries like scapy to generate raw 802.11 Wi-Fi beacon frames and Bluetooth Low Energy advertisements containing perfectly formatted ASTM F3411 message payloads.18 The opendroneid-core-c library provides the critical functions for encoding and packing these messages accurately.25 By hiding a small ESP32 board in an operational area and flooding the airspace with dozens of simulated drones, each transmitting unique serial numbers and randomized flight paths, operators can completely overwhelm detection networks.18 This tactic effectively blinds the enemy’s AeroScope receivers, burying the true physical location of the actual drone and its pilot beneath a massive volume of phantom radar signatures.
6.0 Hardware Augmentation: Secondary Thermal Optics
While firmware modifications enable a drone to fly in contested airspace without broadcasting its location, physical hardware modifications dictate its actual tactical utility. The integration of secondary thermal imaging payloads is one of the most critical and prevalent modifications, allowing commercial platforms to conduct surveillance, targeting, and battle damage assessment in total darkness, heavy fog, or through dense vegetation.26
6.1 Thermal Sensor Specifications and Trade-offs
Commercial thermal camera cores have evolved significantly over the past decade, transitioning from bulky military hardware into highly miniaturized Original Equipment Manufacturer components offering high-resolution imaging with minimal power consumption.5 When selecting a thermal core for integration onto a tactical drone, operators must carefully balance Size, Weight, and Power against the required optical performance.
The FLIR Boson series is a widely utilized professional-grade module in the tactical community. The Boson 640 model utilizes a 12-micrometer pitch Vanadium Oxide uncooled microbolometer detector to deliver a crisp 640×512 pixel thermal resolution.5 The module achieves this impressive performance with a core body weight as low as 7.5 grams and a compact physical footprint measuring just 21 by 21 by 11 millimeters.5 Depending on the specific mission profile, operators configure these cores with varying lenses. For wide-area surveillance, a 4.9-millimeter lens provides a 95-degree field of view. For high-altitude reconnaissance or targeting, a heavier 55-millimeter lens provides a narrow 8-degree field of view, though this lens increases the total weight of the module significantly.5
For lighter payload requirements, or on drone platforms with strict weight limitations like the DJI Mini series, the FLIR Lepton 3.5 provides a viable alternative. While its resolution is substantially lower at 160×120 pixels, it includes radiometric capabilities, allowing it to measure exact temperatures rather than just displaying relative thermal gradients.29 The Lepton interfaces easily with breakout boards via a standard Serial Peripheral Interface, making it highly adaptable for custom Arduino or Raspberry Pi-based payload integration.29
| Thermal Core Model | Resolution | Detector Pitch | FOV Options | Base Weight | Interface |
| FLIR Boson 640 | 640 x 512 | 12 µm VOx | 8° to 95° | ~7.5g | CMOS / USB |
| FLIR Boson 320 | 320 x 256 | 12 µm VOx | Various | ~7.5g | CMOS / USB |
| FLIR Lepton 3.5 | 160 x 120 | N/A | 57° | < 1.0g | SPI |
6.2 Mechanical Integration and Vibration Isolation
Integrating a secondary thermal camera onto a sophisticated commercial platform like the DJI Mavic 3 requires precise mechanical engineering to avoid interfering with the drone’s aerodynamics, primary optical gimbal, and sensitive vision positioning sensors.
Commercial adaptation kits, such as those manufactured by Copterlab, utilize lightweight Carbon ABS components to create precision snap-on mounts that secure to the drone chassis without requiring drilling, permanent adhesives, or screws.4 These comprehensive mounting kits weigh approximately 100 grams and include an independent, video-stabilized two-axis gimbal.4
Vibration isolation is critical for thermal optics, as micro-vibrations from the drone’s high-RPM brushless motors cause a visual distortion known as the jello effect. The Copterlab mounts mitigate this by suspending the thermal core on four specially tuned silicone damper balls.4 This approach mirrors the advanced passive vibration isolation technologies, such as floating wire-rope isolators and Kevlar mounts, utilized in higher-end aerospace applications.31 The mounts can be positioned either below the frame, which is standard, or on top of the drone fuselage to avoid the need for extended landing gear, depending on the operator’s clearance requirements.4
6.3 Power Distribution Architecture
Power management presents a significant engineering challenge during hardware integration. Drawing excessive current from the drone’s internal flight controller or primary power rail to run secondary optics and gimbals can cause severe voltage drops, leading to in-flight processor resets and subsequent catastrophic crashes. Furthermore, splicing into internal wiring instantly voids manufacturer warranties and risks damaging delicate circuitry.
To safely power the thermal payload, operators utilize two primary distribution architectures. The first method involves installing an external 18650 lithium-ion battery holder mounted directly to the carbon fiber payload rig.4 This approach completely isolates the thermal system’s power draw from the host drone, ensuring absolute flight stability at the cost of adding the significant weight of an additional battery cell. The second method involves installing an ultra-lightweight 5-Volt Battery Eliminator Circuit voltage regulator.4 This component safely taps into the drone’s primary high-voltage lithium-polymer battery, stepping the voltage down and providing a clean, stable 3-Amp current directly to the thermal core and video transmitter, adding only about 5 grams of total payload weight.4
6.4 Analog Video Transmission for Latency Reduction
Modern commercial drones utilize highly encrypted, proprietary digital video transmission protocols, such as Orthogonal Frequency-Division Multiplexing, to relay high-definition footage back to the operator’s controller.32 Injecting a secondary video feed from a thermal camera into this closed digital system is exceptionally difficult, requires heavy processing hardware, and introduces unacceptable latency for tactical operations.
Therefore, operators bypass the digital system entirely by integrating independent, analog video transmitters operating on the 5.8GHz Industrial, Scientific, and Medical frequency band.33 By wiring the analog phase alternating line composite video output of the FLIR core directly to a 5.8GHz video transmitter, the drone broadcasts a secondary, unencrypted video signal.34 This signal can be intercepted and viewed by any standard analog First-Person View goggle or ground station monitor.32
This analog approach offers critical tactical advantages over digital systems. First, analog signals degrade gracefully with static as the drone reaches the edge of its transmission range, giving the pilot clear visual feedback of the signal limit. In contrast, digital signals tend to freeze abruptly or drop out entirely, often resulting in a lost aircraft. Second, analog transmission features ultra-low latency, effectively transmitting frames at the speed of light without processing delays, which is an absolute necessity for real-time targeting and high-speed maneuvers.32 An operator might configure the drone with a standard 5.8GHz transmitter, which adds roughly 7 grams of weight, or deploy a higher-powered Full High-Definition 5.8GHz link to achieve a robust transmission range exceeding one mile.4
7.0 Kinetic Payload Release Mechanisms and Tactical Deployment
The final stage of tactical drone modification involves the integration of kinetic payload release mechanisms. These mechanical systems transform a passive surveillance platform into an active delivery vehicle capable of precisely dropping medical supplies, covert communication nodes, or explosive ordnance over a target area.
7.1 Structural Design of DIY Payload Delivery Systems
Operators frequently construct Do-It-Yourself payload release systems utilizing basic, inexpensive hobbyist electronic components.6 While complex electromagnet releases and 3D-printed mechanical grippers exist, the most reliable and widely implemented design in tactical scenarios is the servo-based latch release.6 In this configuration, a standard rotary servo motor actuates a steel pin or a latch arm that secures a payload cradle.6
The mechanical construction begins with the fabrication of a U-shaped or hook-shaped bracket. This cradle is typically manufactured from 3D-printed Polyethylene Terephthalate Glycol, bent 2-millimeter aluminum, or rigid carbon fiber sheet.6 This cradle is meticulously mounted on the underside of the drone’s center plate to align perfectly with the aircraft’s center of gravity.6 Proper placement is critical; suspending heavy loads off-center induces severe aerodynamic instability, causing the flight controller’s PID loops to overcompensate and potentially flip the drone during flight.
A servo motor is mounted adjacent to the cradle. For light payloads, operators utilize small micro-servos such as the SG90 or MG90S.6 For heavier payloads approaching 500 grams, high-torque metal-gear servos like the MG996R are strictly required to prevent the mechanical gears from stripping under load.6 A short length of rigid 0.8-millimeter stainless steel wire connects the servo horn directly to the latch pin.6 In the default, unpowered position, the pin secures a metal ring or carabiner attached to the payload. When the servo receives a signal to rotate ninety degrees, the pin physically retracts, and gravity instantly releases the payload from the cradle.6
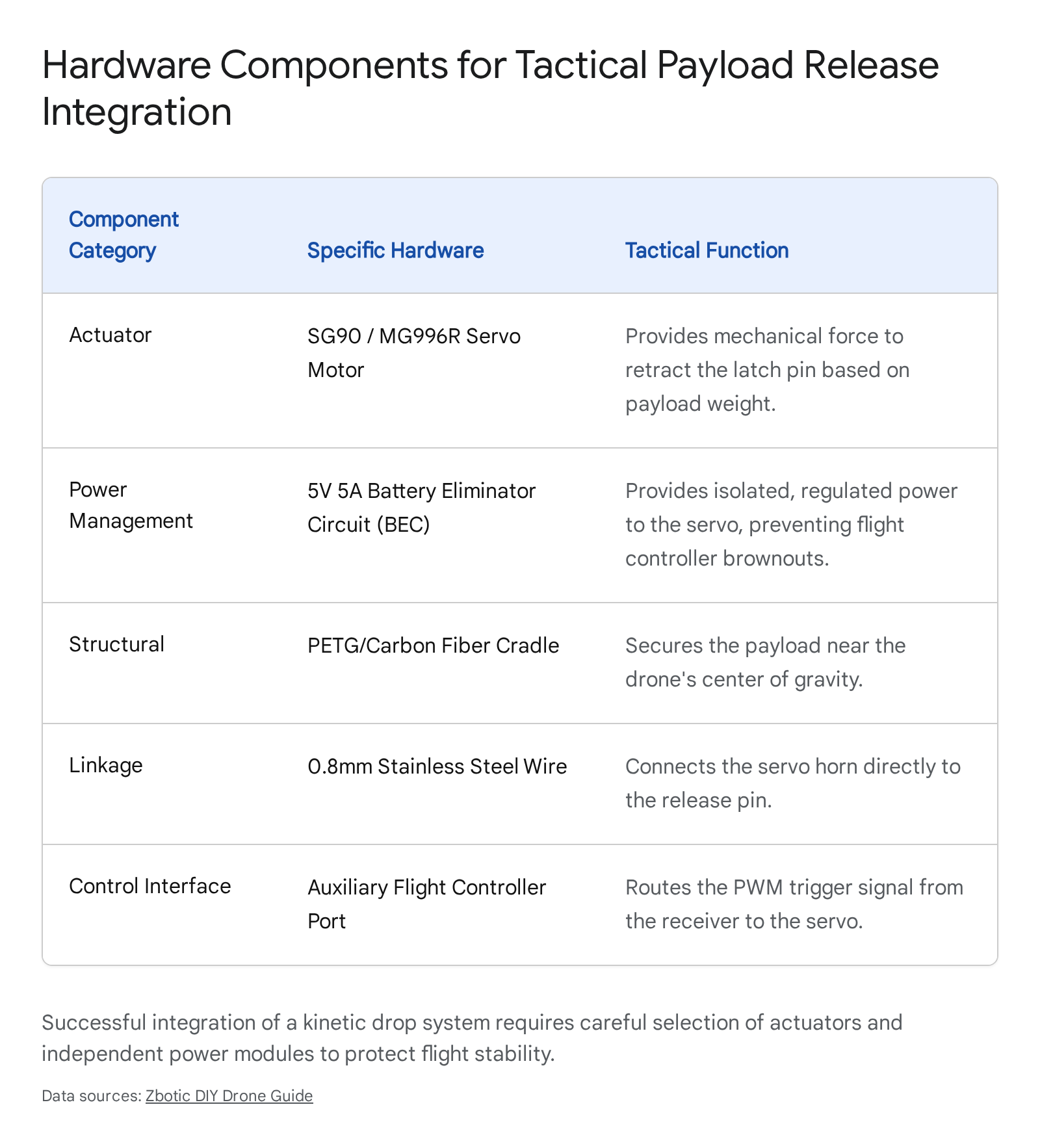
7.2 Flight Controller Integration and Automation
For custom drones built on open-source architectures like ArduPilot or PX4, the payload release mechanism is integrated directly into the flight controller’s logic board.6 The servo’s standard three-wire extension cable, comprising power, ground, and signal wires, connects to a spare auxiliary port on the flight controller, such as AUX1.6
Software configuration requires assigning the specific pin a passthrough function to read the pilot’s radio inputs. In the Mission Planner software interface, an operator navigates to the full parameter list and sets the relevant function, such as SERVO9_FUNCTION, to zero.6 The pulse-width modulation limits are then established to define the servo’s physical travel range. Typically, setting the SERVO9_MIN value to 1000 microseconds represents the locked, closed position, while setting the SERVO9_MAX value to 2000 microseconds represents the fully open, released position.6
Once configured, the release can be triggered manually via a physical switch on the operator’s radio transmitter. More importantly, this deep integration allows for fully automated, network-centric deployments. Operators can program autonomous flight paths utilizing DO_SET_SERVO commands at specific global coordinates within the mission plan, ensuring the payload drops precisely on target without requiring manual pilot input or radio line-of-sight.6
7.3 Commercial Drop Systems and Optical Sensor Triggers
For proprietary consumer drones where internal flight controller wiring is closed, encrypted, and physically inaccessible, operators utilize external, commercially manufactured drop systems. Devices such as the Drone Sky Hook are designed as non-invasive, connect-and-fly attachments that strap onto the exterior fuselage of platforms like the DJI Mavic 3 or Mavic Air series.35
Because these external systems cannot receive electronic signals from the drone’s closed internal network, they employ an ingenious engineering workaround utilizing optical sensors.7 The drop device features a small external light sensor connected to its main processing unit via a dedicated input port.7 During installation, this sensor is physically positioned directly over one of the drone’s auxiliary LED lights, typically located on the bottom of the aircraft’s landing gear.7
During flight, the operator uses the manufacturer’s standard remote controller to remotely toggle the drone’s landing lights or auxiliary LEDs. The external sensor detects this rapid change in illumination and interprets it as a trigger signal, instantly activating the servo and releasing the payload.7 If the mechanism fails to trigger, operators must troubleshoot the physical connection, ensuring the sensor plug is seated securely in the SENS port and verifying that dirt or debris is not blocking the optical sensing hole.7
This optical bridging technique is highly effective, as it allows operators to control third-party mechanical hardware from miles away using the drone’s native, highly encrypted communication link without modifying any code. Advanced versions of these drop kits, such as the Drone Sky Hook PLUS, also include auxiliary power channels and high-intensity LED searchlights capable of projecting 12,000 Lux up to 100 meters away.36 This allows the searchlight to act as a dual-purpose tool, providing visibility while simultaneously controlling payload release sequences in dark environments.37
8.0 Vendor Validation and Equipment Availability
A critical component of this technical research involves verifying the current commercial availability, pricing structures, and active sourcing URLs for the specific hardware modifications discussed in this report. A validation pass conducted on the provided open-source intelligence confirms the following market data for the year 2026.
Thermal Imaging Cores The FLIR Lepton 3.5 thermal camera module is actively stocked and readily available through major international electronic component distributors. Validation confirms that DigiKey currently holds 6,360 units of the Lepton 3.5, identifiable by Part Number 500-0771-01, in bulk stock. The module is priced at 164.00 USD per unit.29 URL:(https://www.digikey.com/en/products/detail/flir-lepton/500-0771-01/7606616)
The higher-resolution FLIR Boson 640 core is available through specialized optics vendors such as GroupGets and Infrared Cameras. However, due to its specialized nature and complex manufacturing process, standard lead times of four to twenty-four weeks apply depending on the specific lens configuration and field of view requested.5 URL:(https://groupgets.com/products/flir-boson-640)
Thermal Gimbal Mounting Kits The custom thermal integration mount kit for the DJI Mavic 3 Pro, which includes the necessary Carbon ABS brackets and a 2-axis stabilized gimbal, is actively produced by Copterlab. Validation confirms the product, tracked under SKU SLLTRIC31319, is available for purchase starting at a base price of 1,034.82 USD.39 The vendor does not maintain off-the-shelf inventory for this complex assembly; the kit is manufactured per order request with a standard dispatch lead time of two weeks from the factory in France.39 URL:(https://copterlab.com/2-axis-thermal-gimbal-kit-for-dji-mavic-3-pro)
Commercial Payload Release Systems The optical-sensor-triggered payload release mechanisms manufactured by Drone Sky Hook remain fully available and actively supported. Validation confirms that the advanced Drone-Sky-Hook Release & Drop PLUS model engineered specifically for the DJI Mavic 3, tracked under SKU DSH-SRDP1-M3, is currently in stock. It is presently offered at a promotional price of 319.00 USD, discounted from its regular retail price of 420.00 USD, and includes free international shipping.36 URL:(https://www.droneskyhook.com/product-page/drone-sky-hook-release-drop-plus-for-dji-mavic-3)
9.0 Conclusion
The lifecycle of Do-It-Yourself commercial drone modifications demonstrates a rapid, highly sophisticated adaptation to modern tactical requirements, fundamentally altering the economics of modern conflict. Operators at the tactical edge are no longer constrained by the safety limitations, geographic restrictions, and proprietary software architectures engineered by original equipment manufacturers. By leveraging advanced open-source decryption tools, manipulating binary packet protocols, and executing precise memory address edits, users can successfully strip geographic restrictions, elevate hard-coded altitude limits, and mask identifying telemetry data.
Concurrently, the physical engineering of these platforms has matured into a standardized science. The mechanical integration of compact, professional-grade thermal optics via 5.8GHz analog transmission links allows consumer drones to operate effectively in low-visibility combat environments without compromising their primary control signals or suffering from digital latency. Furthermore, the development of both hardwired flight controller integrations and optically-triggered kinetic drop systems proves that standard commercial chassis can be reliably and cheaply converted into precise delivery or strike mechanisms.
The widespread commercial availability of the underlying physical components, from high-torque servos and microcontrollers to advanced Vanadium Oxide thermal microbolometers, ensures that the barrier to entry for modifying these systems remains exceptionally low. As commercial drone technology continues to advance, the open-source techniques utilized to reverse engineer, secure, and weaponize these platforms will undoubtedly scale in parallel, permanently establishing modified commercial drones as a foundational element of tactical warfare.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Sources Used
- (PDF) Tactical Network-Centric Warfare in Practice: FPV Drones and the Architecture of a New RMA – ResearchGate, accessed April 19, 2026, https://www.researchgate.net/publication/393440325_Tactical_Network-Centric_Warfare_in_Practice_FPV_Drones_and_the_Architecture_of_a_New_RMA
- o-gs/dji-firmware-tools: Tools for handling firmwares of DJI … – GitHub, accessed April 19, 2026, https://github.com/o-gs/dji-firmware-tools
- How to disable DroneID on DJI drones (for free) inc. Mini 2, Mini 3 …, accessed April 19, 2026, https://greyarro.ws/t/how-to-disable-droneid-on-dji-drones-for-free-inc-mini-2-mini-3-mavic-air-2s-etc-using-cia-jeep-doors/52073
- Flir Boson+ Mount Kit For Dji Mavic 3 Classic – Ndaa Compliant, accessed April 19, 2026, https://copterlab.com/flir-boson-integration-mount-kit-for-dji-mavic-3
- FLIR Boson 640 | GroupGets, accessed April 19, 2026, https://groupgets.com/products/flir-boson-640
- DIY Drone Payload Release Mechanism: Step-by-Step Build – Zbotic, accessed April 19, 2026, https://zbotic.in/diy-drone-payload-release-mechanism-step-by-step-build/
- How to Fix Common Payload Release Issue? – Drone Sky Hook, accessed April 19, 2026, https://www.droneskyhook.com/post/how-to-fix-common-payload-release-issue
- Dedrone’s intelligence report shows evolving drone tactics based on 2025 detection data across their Europe, Middle East, and Asia networks, accessed April 19, 2026, https://www.dedrone.com/blog/intelligence-report-2025
- Moving Targets: Implications of the Russo-Ukrainian War for Drone Terrorism, accessed April 19, 2026, https://ctc.westpoint.edu/moving-targets-implications-of-the-russo-ukrainian-war-for-drone-terrorism/
- How to unlock your drone and why we should not rely on UAS manufacturers for safety, accessed April 19, 2026, https://www.airsight.com/blog/how-to-unlock-your-drone-and-why-we-should-not-rely-on-uas-manufacturers-for-safety
- Reverse Engineering and Control-Aware Security Analysis of the ArduPilot UAV Framework, accessed April 19, 2026, https://arxiv.org/html/2512.01164v1
- Challenges in Drone Firmware Analyses of Drone Firmware and Its Solutions – arXiv, accessed April 19, 2026, https://arxiv.org/html/2312.16818v4
- Ghidra is a software reverse engineering (SRE) framework · GitHub, accessed April 19, 2026, https://github.com/nationalsecurityagency/ghidra
- ghidra_scripts/binwalk.py at master – GitHub, accessed April 19, 2026, https://github.com/ghidraninja/ghidra_scripts/blob/master/binwalk.py
- ReFirmLabs/binwalk: Firmware Analysis Tool – GitHub, accessed April 19, 2026, https://github.com/refirmlabs/binwalk
- How to Unlock FCC Mode on ALL DJI Drones & FIX Bad Signal on DJI RC / RC2 / RC Pro Controllers too! – YouTube, accessed April 19, 2026, https://www.youtube.com/watch?v=RlEdi8eKkvg
- FAQs about FAA Remote ID Compliance – Support, accessed April 19, 2026, https://support.dji.com/help/content?customId=en-us03400007747&spaceId=34&re=US&lang=en
- cyber-defence-campus/droneRemoteIDSpoofer: Bluetooth and Wi-Fi based Drone Remote ID spoofer (ASD-STAN) demonstrating protocol security limitations. Tests unauthenticated broadcast vulnerability. – GitHub, accessed April 19, 2026, https://github.com/cyber-defence-campus/droneRemoteIDSpoofer
- How to disable DroneID on DJI drones (for free) inc. Mini 2, Mini 3, Mavic, Air, 2S, etc – using CIA Jeep Doors, accessed April 19, 2026, https://greyarro.ws/t/how-to-disable-droneid-on-dji-drones-for-free-inc-mini-2-mini-3-mavic-air-2s-etc-using-cia-jeep-doors/52073?page=7
- Reverse Engineering the Security Risks of the AeroScope Drone Detection Module, accessed April 19, 2026, https://www.mobilityengineeringtech.com/component/content/article/52998-reverse-engineering-the-security-risks-of-the-aeroscope-drone-detection-module
- accessed April 19, 2026, https://support.dji.com/help/content?customId=en-us03400007747&spaceId=34&re=US&lang=en#:~:text=No.,ID%20system%20cannot%20be%20disabled.
- jjshoots/RemoteIDSpoofer: NodeMCU RemoteID Spoofer – GitHub, accessed April 19, 2026, https://github.com/jjshoots/RemoteIDSpoofer
- RemoteID Cloaking Device How-To! Spoofer generates fake RemoteID signatures! – YouTube, accessed April 19, 2026, https://www.youtube.com/watch?v=Q8jn_6EmYxE
- GitHub – adamhrv/skylift: Wi-Fi Geolocation Spoofing with ESP8266 / ESP32, accessed April 19, 2026, https://github.com/adamhrv/skylift
- opendroneid/opendroneid-core-c: Open Drone ID Core C Library – GitHub, accessed April 19, 2026, https://github.com/opendroneid/opendroneid-core-c
- Thermal & Optical Scopes: Master Dual Systems for Precision Shooting, accessed April 19, 2026, https://www.rixoptics.com/thermal-optical-scope-dual-system-guide/
- Commercial Thermal Camera Systems: OEM Integration Guide – LightPath Technologies, accessed April 19, 2026, https://www.lightpath.com/blog/commercial-thermal-camera-systems-oem-integration-guide
- TELEDYNE FLIR Boson with Shutter 640 Thermal Resolution, Wide Lens, 95° FOV, 4.9mm Fast Frame Rate Industrial Grade – Infrared Cameras, Inc., accessed April 19, 2026, https://buy.infraredcameras.com/products/flir-boson-with-shutter-640-thermal-resolution-wide-lens-95-fov-4-9mm-fast-frame-rate-industrial-grade-1
- 500-0771-01 FLIR Lepton | Camera Modules – DigiKey, accessed April 19, 2026, https://www.digikey.com/en/products/detail/flir-lepton/500-0771-01/7606616
- Teledyne FLIR Distributor | DigiKey, accessed April 19, 2026, https://www.digikey.com/en/supplier-centers/flir-lepton
- 7.0 Thermal Control – NASA, accessed April 19, 2026, https://www.nasa.gov/smallsat-institute/sst-soa/thermal-control/
- Choose the Best FPV Camera For FPV Drones: Comprehensive Guide and Product Recommendations – Oscar Liang, accessed April 19, 2026, https://oscarliang.com/fpv-camera/
- Drone Parts List for Building a Drone – Complete Guide – Robocraze, accessed April 19, 2026, https://robocraze.com/blogs/post/drone-part-list
- Design and Implementation of a 5.8 GHz superheterodyne FM Video Receiver – DiVA portal, accessed April 19, 2026, https://www.diva-portal.org/smash/get/diva2:1375795/FULLTEXT01.pdf
- accessed January 1, 1970, https://www.droneskyhook.com/mavic-3-release-drop-plus
- Drone-Sky-Hook Release & Drop PLUS for DJI Mavic 3, accessed April 19, 2026, https://www.droneskyhook.com/product-page/drone-sky-hook-release-drop-plus-for-dji-mavic-3
- Integrating DJI Drone Searchlight Systems & Payload Devices, accessed April 19, 2026, https://www.droneskyhook.com/post/integrating-dji-drone-searchlight-systems-payload-devices
- Drone-Sky-Hook Bundle Release & Drop PLUS with Searchlight for DJI Mavic 3, accessed April 19, 2026, https://www.droneskyhook.com/product-page/drone-sky-hook-bundle-release-drop-plus-with-searchlight-for-dji-mavic-3
- Dji Mavic 3 Pro Thermal Camera Kit (noN-Ndaa) – copterlab.com, accessed April 19, 2026, https://copterlab.com/2-axis-thermal-gimbal-kit-for-dji-mavic-3-pro