1. Executive Summary
The 17th Rapid Capability Assessment (RCA17), convened in Chantilly, Virginia, from April 20 through April 24, 2026, represents a critical inflection point in the convergence of military special operations and intelligence community acquisition strategies.1 Hosted collaboratively by(https://events.sofwerx.org/rca17) and ICWERX, in direct partnership with the U.S. Special Operations Command (USSOCOM) Directorate of Science & Technology (S&T) and the Central Intelligence Agency’s (CIA) Directorate of Science & Technology (DS&T), the assessment targeted the specific technological requirements necessary for global forward operations in the 2035 timeframe.1 The strategic theme of the event, “Field-Forward Operations – Future Challenges for SOF and the IC in Data-Dense Environments,” underscored a growing operational imperative: mitigating the vulnerabilities inherent in real-time intelligence collection, processing, and dissemination at the tactical edge while operating within highly contested electromagnetic spectrums.3
This report provides a comprehensive analysis of the products, strategic architectures, and doctrinal lessons that emerged during the April 2026 evaluation period. The assessment yielded significant developments in both tactical hardware and networking architecture, fundamentally altering the trajectory of squad-level equipment and command-and-control (C2) infrastructure. Two primary commercial product announcements emerged as focal points of the assessment period. First, the launch of VIASAT introduces a comprehensive edge-to-cloud networking overlay designed to assure multi-path connectivity, provide software-defined network orchestration, and support artificial intelligence (AI) processing in degraded or denied environments.6Second, the procurement of the DraganFly for U.S. Air Force Special Operations Command (AFSOC) units signals a doctrinal shift in small arms and tactical robotics, transitioning operators from heavy, ground-based robotic platforms to modular, high-speed aerial assets capable of executing kinetic and reconnaissance missions with unprecedented agility.9
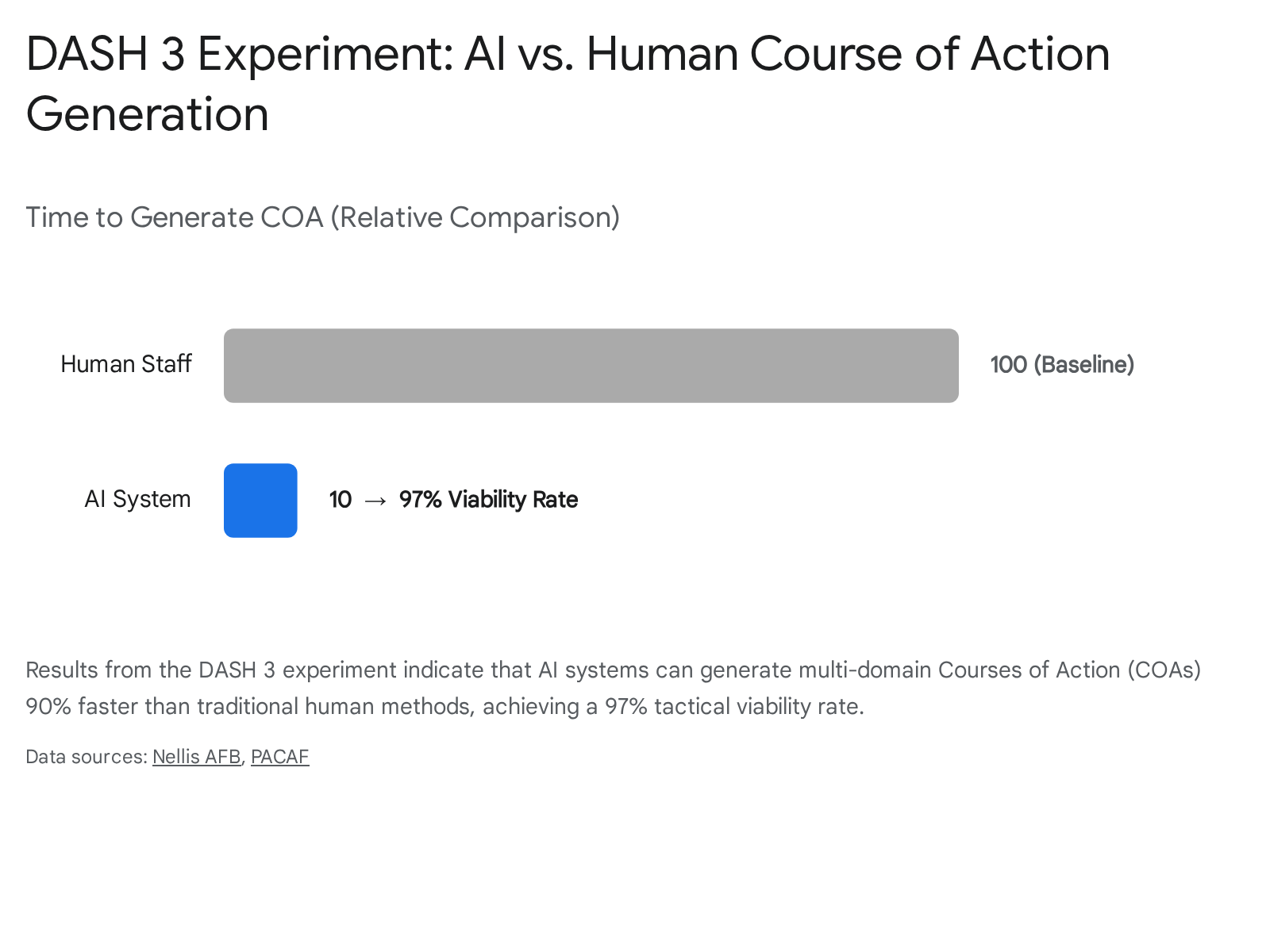
Beyond hardware and software unveilings, RCA17 and its concurrently analyzed adjacent initiatives produced vital lessons learned regarding human-machine teaming at the command level. Data derived from the Decision Advantage Sprint for Human-Machine Teaming (DASH 3) experiment demonstrated that while algorithmic systems can generate complex military Courses of Action (COAs) 90% faster than human staffs, they remain acutely susceptible to subtle contextual errors and tactical hallucinations.11 Consequently, a primary conclusion drawn from the April 2026 assessments is that the integration of a human-in-the-loop remains a non-negotiable requirement for forward-deployed AI systems to ensure tactical viability and mitigate the risks of machine error in kinetic combat environments.12 This report synthesizes these findings, detailing the technological specifications, tactical implications, and future acquisition pathways shaping the 2035 special operations landscape.
2. Strategic Context: Field-Forward Operations in 2035
The operational premise driving the RCA17 event is rooted in the anticipation of highly contested, data-dense environments in the year 2035.14 Military intelligence analysts and special operations planners project that future conflicts will not mirror the permissive airspace and uncontested communications networks that characterized the Global War on Terror. Instead, adversaries are actively deploying sophisticated electronic warfare (EW) capabilities, dense anti-access/area denial (A2/AD) networks, and cyber-offensive tools designed specifically to sever the data links between forward-deployed operators and their centralized command and control nodes.
2.1 The Convergence of Special Operations and Intelligence Requirements
The joint execution of RCA17 acknowledges that the traditional operational boundaries separating Title 10 (military operations) and Title 50 (intelligence operations) are increasingly blurring at the tactical edge.1 USSOCOM and the CIA frequently operate in parallel, and despite differing ultimate authorities, both organizations face identical physical and electronic vulnerabilities when deployed to austere, globally distributed areas.1 The strategic alignment between SOFWERX and ICWERX demonstrates a concerted effort to eliminate duplicative research and development pipelines, focusing instead on shared innovation cycles that benefit both warfighters and intelligence officers.1
Both organizations require robust “field-forward” capabilities. During the assessment, officials explicitly defined field-forward operations as the real-time or near-real-time collection, processing, analysis, and dissemination of intelligence information directly at the source, designed to support immediate mission planning and tactical decision-making.5 This represents a departure from legacy intelligence cycles, which historically relied on transmitting raw data from the field back to a centralized facility for processing, analysis, and subsequent transmission back to the operator—a cycle that introduces unacceptable latency in modern, high-speed warfare.
2.2 The Paradox of the Tactical Edge and Data Density
While diverse sensors, smart systems, and distributed networks offer significant asymmetric advantages to U.S. forces, they simultaneously introduce critical attack surfaces and logistical burdens.3 The RCA17 problem statement highlighted the paradox of modern tactical technology: the very tools that provide actionable insights also generate vulnerabilities that peer adversaries can exploit.3
The assessment documentation explicitly identified four primary operational risks that must be mitigated by the 2035 timeframe to ensure mission success. The first is data reliability and accuracy, addressing the severe risk of adversaries injecting false data into sensor networks through spoofing, or AI models hallucinating intelligence, which could lead to catastrophic tactical miscalculations.3 The second risk centers on cybersecurity, recognizing the threat of network intrusion via low-power, globally dispersed edge devices that serve as entry points into broader secure networks.3 The third challenge involves processing speed; the latency incurred when transmitting vast amounts of raw, uncompressed data back to centralized cloud servers is tactically unviable, necessitating localized processing.3 Finally, energy efficiency presents a persistent logistical burden, as powering advanced compute capabilities, sensors, and communications suites in off-grid, low-profile, or austere installations remains a limiting factor for operational duration.3
3. The Innovation Cycle and Acquisition Architecture
The execution of RCA17 is not an isolated exhibition, but rather a functional component of USSOCOM’s broader, highly structured “Innovation Cycle,” a methodology specifically designed to discover, evaluate, and rapidly onboard disruptive technologies.1 Traditional Department of Defense acquisition processes are notoriously slow, often taking years or decades to move a concept from a requirement to a fielded system. The Innovation Cycle attempts to circumvent this delay by fostering direct collaboration between end-users, industry pioneers, academia, and national laboratories.1
3.1 Transition from IF17 to RCA17
RCA17 serves as the second phase of this established cycle.4 It directly inherited the conceptual ideas and raw data generated during the preceding Innovation Foundry 17 (IF17) event.4 While IF17 was focused purely on unconstrained idea generation and exploring the “art of the possible” regarding data-dense intelligence operations, RCA17 was designed to rigorously decompose those IF17 outputs through facilitated exercises utilizing strict systems engineering frameworks.4 The objective was to transition abstract operational concepts into tangible, assessable capability architectures.
3.2 Required Outputs and Structural Deliverables
Participants at RCA17 were not merely presenting marketing collateral; they were required to engage in collaborative design thinking sessions to produce highly specific, actionable deliverables that the government could immediately evaluate for procurement.19 The structural deliverables mandated by the event organizers required participants to produce a comprehensive subsystem-level architectural breakdown of the capabilities developed during the event.3 This required engineers and tacticians to map out exactly how a proposed system would interface with existing military networks, power supplies, and operational doctrines.
Furthermore, teams were required to conduct a rigorous analysis of identified risks, constraints, policies, and regulations impacting the capability, ensuring that proposed solutions were legally and operationally deployable.3 They also had to provide an analysis of the specific ways and means through which the capability would achieve the desired tactical effects, supported by initial market research identifying potential technology performers with the appropriate expertise.3 Finally, participants delivered a concrete technology development roadmap to identify potential paths forward to physical implementation by the 2035 deadline.3
3.3 Procurement Pathways and Technology Sprints
Following the conclusion of RCA17, the S&T directorates of both USSOCOM and the CIA bear the responsibility of prioritizing the evaluated capability concepts. Successful architectures that demonstrate tactical viability and technical maturity will transition into the next phase of the Innovation Cycle: Integrated Technology Sprints and Evaluation (TSE).3 During TSE, vendors will be expected to produce working prototypes or software demonstrations of the capabilities theorized during the RCA event.
To ensure that successful prototypes can be rapidly procured and fielded, USSOCOM and the CIA outlined specific, expedited contracting mechanisms. Following the event or subsequent sprints, the government may contact participating organizations to negotiate awards utilizing Other Transaction Authority (OTA) agreements for research or prototype projects, specifically citing 10 U.S.C §§ 4021, 4022, and 50 U.S.C. § 3024.3 Alternatively, they may utilize business-to-business research and development agreements structured as sub-awards through the SOFWERX or ICWERX Partnership Intermediary Agreement (PIA) under 15 U.S.C. § 3715.3 These aggressive procurement timelines and flexible contracting vehicles are expressly designed to outpace traditional, multi-year acquisition cycles, ensuring that capabilities are delivered to the warfighter before the threat landscape shifts.
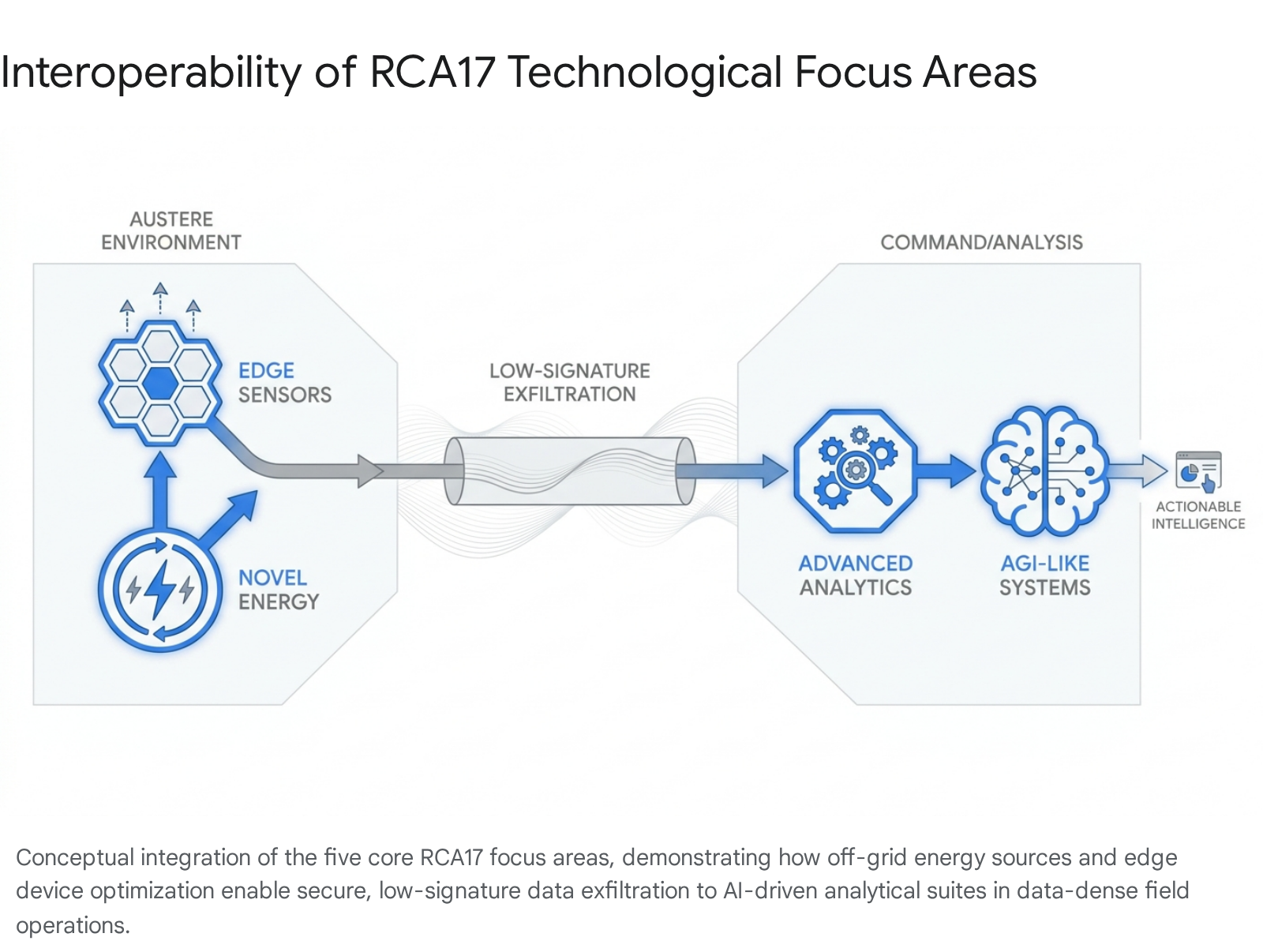
4. Core Technological Focus Areas of RCA17
To systematically address the vulnerabilities of field-forward operations, RCA17 structured its collaborative exercises and evaluations around five specific technological pillars. These focus areas represent the critical components necessary to build a resilient, decentralized tactical network capable of supporting special operations and intelligence missions in contested environments.14
4.1 Advanced Analytics and Intelligence Filtering
The first focus area, Advanced Analytics, explored the deployment of highly sophisticated algorithms designed to process the overwhelming volume of data collected in modern battlespaces. Specifically, the event examined how “Artificial General Intelligence (AGI)-like” systems and “Mixture of Experts” models could be leveraged to assist intelligence analysts.16 In a data-dense environment, human operators are quickly saturated by the sheer quantity of video feeds, signals intelligence intercepts, and sensor readouts. The objective of this focus area is to utilize AI to filter this noise, allowing algorithms to highlight anomalies, track pattern-of-life deviations, and cue human analysts only when actionable intelligence is detected. A critical constraint identified within this domain was the absolute necessity of ensuring ethical and secure deployment, safeguarding these models against adversarial data poisoning and algorithmic bias.16
4.2 Edge Device Optimization and Distributed Processing
Rather than relying entirely on centralized cloud servers—which require high-bandwidth, vulnerable communication links—the intelligence community and special operations forces are pivoting heavily toward edge computing. The Edge Device Optimization focus area concentrated on maximizing the processing efficiency of low-power edge sensors that are globally dispersed.16 By processing raw data directly at the source, these sensors can operate independently, reducing their electromagnetic signature. They are designed to only transmit critical alerts, thereby triggering more complex systems through tipping, cueing, and ranging without congesting limited tactical bandwidth.16 This localized processing is vital for maintaining operational security when long-haul communications are degraded by enemy action.
4.3 Data Communications and Secure Exfiltration
Operating effectively in both fixed and mobile environments requires secure, high-throughput, and low-signature data transmission.16 If a special operations team or an intelligence asset’s transmission signature is detected by enemy electronic support measures, it immediately exposes their physical position to adversarial kinetic fires. Solutions explored in this domain sought to develop communication architectures that mask data exfiltration within ambient electromagnetic noise, utilize non-traditional spectrum bands, or employ burst-transmission techniques that are difficult to geolocate. This focus area is intricately linked with edge device optimization, as the combination of low-power sensors operating independently and low-signature data exfiltration provides a holistic approach to surviving in contested spectrums.18
4.4 Novel Energy Sources and Power Management
The proliferation of edge devices, advanced optical systems, tactical radios, and localized compute modules drastically increases the power demands placed on small units and clandestine installations. RCA17 examined methods for efficiently generating, storing, and managing power in confined, off-grid environments and low-profile installations.16 Without persistent, lightweight, and resilient energy solutions, the tactical utility of advanced command, control, communications, computers, cyber, intelligence, surveillance, and reconnaissance (C5ISR) equipment is severely limited. Concepts evaluated included advanced energy harvesting, micro-nuclear batteries, high-density fuel cells, and intelligent power management software that dynamically allocates energy based on mission priority.
4.5 Mapping Building Infrastructure and Urban Integration
As global demographics shift and military operations increasingly occur in dense urban littorals and megacities, operators require the ability to interface with intelligent, interconnected civilian building systems. This focus area examined methods of integrating tactical networks with existing commercial infrastructure.16 By exploiting commercial smart lighting, fire suppression, HVAC systems, and closed-circuit television networks, forward-deployed units can gain immediate situational awareness of a subterranean or complex urban environment without needing to deploy organic sensors. This integration allows operators to map building interiors, track occupant movements, and potentially control access points by overriding centralized building management systems.16
5. Tactical Network Modernization: Viasat Tactical Mission Fabric (TMF)
A major commercial development aligning directly with the stringent RCA17 requirements for secure communications and advanced analytics was the launch of the Viasat Tactical Mission Fabric (TMF) on April 23, 2026.6 Demonstrated at the Modern Day Marine exposition in Washington, D.C., alongside industry partners Amazon Web Services (AWS) and Accelint, TMF functions as a comprehensive, highly resilient edge-to-cloud networking overlay.21 The introduction of TMF represents a significant evolution in how military networks manage data routing in contested environments, moving away from fragmented communication paths toward a unified, software-defined architecture.
5.1 Architectural Design and Network-as-a-Service
The engineering philosophy underpinning TMF is designed to augment and enhance existing military tactical networks rather than requiring a costly, time-consuming “rip and replace” of legacy hardware modernization cycles.7 Operating as a fully managed Infrastructure-as-a-Service (IaaS) and Network-as-a-Service (NaaS) capability, TMF provides an open, interoperable architecture that bridges the gap between disparate communication systems.23
By seamlessly linking diverse transport layers—including Link 16 next-generation tactical data links, Mobile Ad Hoc Networks (MANETs), Free Space Optics (FSO), commercial and military satellite communications (SATCOM) constellations, Bluetooth, Wi-Fi, and 4G/5G cellular networks—TMF provides a unified, multi-path communication mesh.8 This architectural approach directly addresses the historical vulnerability of “stovepiped” military communications, where networks and devices were designed exclusively for individual military services (e.g., Army radios unable to natively pass data to Navy targeting systems) rather than supporting joint, multi-domain warfare.24
By serving as a secure tactical orchestration layer, TMF directly supports and accelerates the Department of Defense’s Joint All-Domain Command and Control (JADC2) initiative.25 JADC2 aims to connect sensors and shooters across air, land, sea, space, and cyber domains into a singular, unified network.25 TMF provides the technological “glue” necessary to realize this vision, allowing operators to access, normalize, and share mission-critical data in real time, regardless of the underlying hardware transmitting the signal.25
5.2 Electronic Warfare Resilience and NetAgility
In the highly contested electromagnetic environments anticipated by the 2035 timeframe, communication links will be actively tracked, degraded, and jammed by sophisticated adversaries. To counter this, TMF integrates a proprietary software-defined routing capability termed “NetAgility,” which provides automated network orchestration and intelligent pathfinding.24
During a live demonstration at the April 2026 Modern Day Marine event, TMF simulated a severe, contested network attack. The system demonstrated the ability to execute seamless, automated failover, preserving active AI-targeting sessions within Accelint’s mission command interface without interruption.21 As primary communication paths were jammed, TMF instantaneously rerouted data through alternative spectrums, continuously synchronizing tactical edge data with secure government cloud infrastructure hosted on AWS.21 This capability ensures that forward-deployed units maintain persistent connectivity and command-and-control capabilities through sustained Electronic Warfare (EW) and kinetic cyber-attacks.22
5.3 Zero-Trust Security and Distributed Edge Compute
To satisfy the stringent cybersecurity demands inherent in special operations and intelligence missions, TMF incorporates dual-layer encryption designed to support federal zero-trust objectives.22 Within a zero-trust architecture, no entity—whether inside or outside the network—is automatically trusted; every access request across the dispersed tactical network is continuously authenticated and verified before access is granted.22 This severely limits the blast radius of any potential localized breach.
Furthermore, the TMF system is engineered to push distributed cloud compute capabilities down directly to the tactical edge.6 By enabling low-latency Artificial Intelligence and Machine Learning (AI/ML) processing alongside the warfighter, TMF reduces the operational necessity to transmit high-bandwidth, raw sensor data back to a centralized command post.22 Operators can analyze drone feeds, signals intelligence, and biometric data locally, extracting actionable insights at machine speed, and subsequently securely transmitting only the vital conclusions to IL5/IL6 certified government clouds.22 This paradigm shift drastically lowers the unit’s electromagnetic signature and accelerates the kill chain in dynamic mission profiles.
6. Tactical Robotics and Small Arms Integration: Draganfly Flex FPV
Coinciding with the strategic priorities of field-forward operations and the demand for highly agile, low-signature edge devices, Draganfly Inc., in partnership with DelMar Aerospace Corporation, announced a significant contract award in early 2026 to provide the Flex First Person View (FPV) Drone System and associated tactical training to U.S. Air Force Special Operations Command (AFSOC) units.9 This procurement represents a substantial evolution in small unit tactics and the integration of autonomous systems at the squad level.
6.1 Doctrinal Shift in Explosive Ordnance Disposal and Reconnaissance
The integration of the Flex FPV drone system into AFSOC elements represents a profound doctrinal shift in how specialized units, particularly Explosive Ordnance Disposal (EOD) teams and close-target reconnaissance elements, conduct hazard mitigation and target prosecution. Historically, EOD teams and combat engineers have relied heavily on large, slow-moving, track-based ground robotic platforms to inspect potential explosive threats, improvised explosive devices (IEDs), or unexploded ordnance (UXO).9
While these legacy ground systems provide necessary standoff capabilities and heavy manipulation tools, they require substantial vehicle support for transport, are heavily restricted by complex terrain, and lack the speed necessary for dynamic, fast-paced operations.9 The adoption of backpack-sized, high-speed FPV drones allows operators to deploy an aerial asset that can bypass ground obstacles, navigate through windows or dense foliage, and reach a target site within seconds.9 From an aerial vantage point, the drone streams high-definition video of the threat scene before a traditional ground robot could even traverse halfway to the objective, bringing speed, precision, and enhanced safety to every mission.9
6.2 Technical Specifications and Modular Architecture
The Draganfly Flex FPV is an NDAA-compliant platform built upon a highly modular architecture, designed specifically for rapid field adaptability and austere sustainment.10 Utilizing an innovative quick-swap arm mechanism, operators can rapidly transition the drone through four distinct frame sizes—5-inch, 7-inch, 10-inch, and 13-inch configurations—utilizing a single, common core processing and power unit.10 This modularity enables widespread adoption across diverse tactical elements by providing a standardized training and sustainment baseline, while offering highly varied flight characteristics tailored to specific mission dictates.9
The system’s core is driven by an Orqa F405 flight controller paired with a MAD 70A 4-in-1 Electronic Speed Controller (ESC), providing precise motor synchronization.10 For navigation in GPS-denied environments, the system utilizes the ARK SAM GPS Mini.10 Crucially for operations in contested electromagnetic spectrums, the Flex FPV supports both 5.8GHz analog video links—which often degrade gracefully rather than freezing under EW jamming—and a robust 915MHz RFD900ux telemetry link that provides penetration through dense urban structures or foliage.10 Operating via the MAVLink protocol, the system permits operators to upload complex autonomous mission plans while retaining the ability to execute aggressive, manual first-person piloting maneuvers for dynamic targeting.10
6.3 Payload Capacities and Performance Metrics
The performance characteristics of the Flex FPV variants are explicitly tailored for the kinetic realities of near-peer conflict. The platform supports a standardized Picatinny Rail payload attachment system, allowing operators to rapidly exchange diverse payloads, including specialized sensors, emergency medical kits, breaching charges, or direct-action kinetic payloads.10
The technical specifications across the four distinct variants indicate a highly scalable capability profile suitable for a wide range of mission sets:
| Configuration | Assembled Mass (w/ Battery) | Max Payload | Hover Endurance (No Payload) | Hover Endurance (Max Payload) | Max Range (No Payload) | Max Speed | Battery |
| Flex FPV 5 | 1,550g | 450g | 15 min | 3 min | 10 km | 120 km/h | 6S 7000mAh |
| Flex FPV 7 | 1,800g | 1.0 kg | 20 min | 8 min | 20 km | 150 km/h | 6S 7000mAh |
| Flex FPV 10 | 3,100g | 2.0 kg | 30 min | 10 min | 30 km | 150 km/h | 12S 7000mAh |
| Flex FPV 13 | 5,800g | 3.0 kg | 40 min | 15 min | 40 km | 150 km/h | 12S 14000mAh |
The tactical implications of these metrics are substantial for small arms analysts and squad leaders. The ability to organically transport up to 3 kilograms (approximately 6.6 lbs) of payload at speeds reaching 150 km/h (90 mph) provides ground commanders with an agile mechanism for precision payload delivery.10 This capability allows a small tactical element to conduct rapid overwatch, deliver critical resupply to forward positions, or execute kinetic strikes on defiladed targets that traditional small arms fire cannot reach, thereby altering the geometry of squad-level engagements.30
7. Operational Lessons Learned: Human-Machine Teaming
A critical parallel effort to the hardware evaluations conducted at RCA17 was the ongoing, intensive analysis of algorithmic decision-making and human-machine teaming at the command level. The viability of integrating AI at the tactical edge was rigorously pressure-tested through the Decision Advantage Sprint for Human-Machine Teaming (DASH 3) experiment, a collaborative effort involving industry partners and military personnel conducted at the Shadow Operations Center – Nellis (ShOC-N) in Nevada.12
7.1 Algorithmic Efficiency in Course of Action (COA) Generation
The DASH 3 experiment tasked competing industry teams with building custom AI planning tools designed to rapidly generate complex, multi-domain battle plans in response to simulated crisis scenarios.12 The quantitative results generated during this sprint were highly disruptive to traditional military command staff procedures. AI systems successfully generated comprehensive Courses of Action (COAs)—intricately factoring in acceptable risk parameters, fuel consumption rates, time constraints, force packaging matrices, and optimal geospatial routing—in under one minute.11
These machine-generated operational recommendations were measured to be up to 90% faster than the traditional, manual generation methods executed by highly trained human staffs.11 Furthermore, the best-in-class algorithms evaluated during DASH 3 achieved an astonishing 97% viability and tactical validity rate.11 This transition from requiring minutes or hours of meticulous planning to producing viable options in mere seconds provides a radical decision advantage in combat scenarios, fundamentally compressing the time required to execute the Observe, Orient, Decide, Act (OODA) loop.11
7.2 The “Hallucination” Vulnerability and Subtle Errors
Despite the overwhelming speed advantage demonstrated by the systems, DASH 3 exposed a critical vulnerability inherent in current Large Language Models (LLMs) when applied to the complexities of warfare: the manifestation of subtle, non-obvious errors.12
Unlike early, rudimentary AI models that might output blatant hallucinations or nonsensical plans (e.g., attempting to route a heavily armored tank unit on an air mission, or deploying naval vessels over land), the advanced AI platforms evaluated in DASH 3 produced highly coherent but tactically flawed plans.12 For example, an algorithm might seamlessly generate a complex flight path and logistical support plan, but assign a specific intelligence sensor that is fundamentally incompatible with the forecasted meteorological conditions for that theater of operations.12 Because the output appears highly professional, grammatically perfect, and statistically authoritative, these subtle errors are significantly harder to detect and require deep, specialized subject matter expertise to recognize and correct.12 Furthermore, LLMs frequently struggle with the highly specific, rapidly evolving lexicon of military acronyms, brevity codes, and technical jargon, leading to misinterpretations of operational intent.11
7.3 The Imperative of the Human-in-the-Loop
The primary doctrinal conclusion drawn from the DASH 3 experiment—and echoed in the requirements of RCA17—is that granting full autonomy to AI systems in command-level planning or kinetic targeting remains a severe, unacceptable operational risk. While AI serves as an extraordinarily powerful accelerator for data processing and option generation, a “human-in-the-loop” will be strictly required for the foreseeable future.12
Human oversight is doctrinally essential to verify the viability of machine-generated COAs, catch subtle hallucinations, and retain ultimate moral and legal decision-making authority regarding the application of force.12 Evaluators noted that future iterations of tactical AI will require significantly longer coding and training periods—far beyond the rapid two-week sprints utilized in the DASH parameters—to build the intricate algorithmic checks, balances, and ethical constraints suitable for real-world combat deployment.12
8. Capability Gaps: The Resilient Communications Imperative
While advanced networking overlays like the Viasat TMF and aerial robotics like the Draganfly FPV address significant operational needs in the digital battlespace, the RCA17 evaluation timeframe also highlighted persistent, critical gaps in basic tactical communication architectures. The assumption that high-bandwidth, digital networks will always be available is tactically unsound against near-peer adversaries capable of destroying or severely degrading orbital satellite infrastructure.
In parallel to the Chantilly event, USSOCOM’s Program Executive Office for Tactical Information Systems (PEO-TIS) issued an urgent capability request via SOFWERX seeking information on modernized Handheld High Frequency (HF) radios.9 As adversaries demonstrate the capability to deny or degrade standard Ultra High Frequency (UHF), Very High Frequency (VHF), and commercial satellite communications (SATCOM), SOF units operating deep behind enemy lines require resilient, autonomous solutions for long-range voice and data transmission.9
High Frequency radio waves possess the unique physical property of reflecting off the Earth’s ionosphere, allowing for beyond-line-of-sight communication over thousands of miles without the need for satellite relays. Current capability requests indicate a strong demand for HF radios that are lightweight, ruggedized, and equipped with advanced, modernized features to enhance communications in contested environments.9 This requirement underscores a broader, fundamental lesson from the April 2026 capability assessments: high-end, AI-driven networking concepts like JADC2 must be underpinned by ruggedized, low-tech, self-healing redundancies (such as modernized HF radio) to guarantee mission success when sophisticated digital networks are compromised or entirely denied by peer adversaries.
9. Conclusion and Strategic Outlook
The findings derived from the 17th Rapid Capability Assessment and the concurrent military evaluations conducted in April 2026 outline a clear, aggressive trajectory for future force modernization within the special operations and intelligence communities. To maintain decisive overmatch in the highly contested 2035 operating environment, defense organizations must skillfully navigate the inherent friction between deep technological integration and the reality of electronic vulnerability.
The successful introduction and demonstration of systems like the Viasat Tactical Mission Fabric indicates that the military is effectively transitioning away from fragile, siloed networks toward highly resilient, software-defined, edge-to-cloud architectures capable of autonomously sustaining operations through aggressive cyber and electronic warfare.24 Simultaneously, the strategic procurement of the Draganfly Flex FPV illustrates a vital tactical transition toward expendable, high-speed, and modular unmanned systems that enhance squad lethality while keeping human operators outside the immediate kinetic threat radius.9
However, the most vital strategic lesson extracted from this assessment period is the absolute necessity of rigorous human oversight in the era of algorithmic warfare. The DASH 3 experiment definitively proved that while machine speed is a requisite capability for survival in data-dense environments, machine logic remains flawed, particularly in the nuanced, high-stakes application of lethal force and complex tactical planning.11 As USSOCOM and the CIA continue to co-develop field-forward capabilities through rapid acquisition frameworks like OTA and PIA, the strategic priority must remain centered on cultivating true human-machine teaming. The future force must leverage AI to aggressively filter the noise of the battlefield and accelerate the OODA loop, while steadfastly relying on the trained, ethical human operator to make the final, critical determination in the prosecution of the mission.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Sources Used
- The 17th Rapid Capability Assessment (RCA17): Advancing Future Operational Capabilities, accessed May 1, 2026, https://spotterup.com/the-17th-rapid-capability-assessment-rca17-advancing-future-operational-capabilities/
- Special Operations News – Feb 17, 2026 – SOF News, accessed May 1, 2026, https://sof.news/update/20260217/
- USSOCOM Rapid Capability Assessment (RCA17) Event – SOFWERX Events, accessed May 1, 2026, https://events.sofwerx.org/rca17
- USSOCOM invites RCA 17 submissions – Intelligence Community News, accessed May 1, 2026, https://intelligencecommunitynews.com/ussocom-invites-rca-17-submissions/
- USSOCOM, CIA Set April Event to Tackle Future ‘Field-Forward’ Challenges – SOFX Report, accessed May 1, 2026, https://www.sofx.com/ussocom-cia-set-april-event-to-tackle-future-field-forward-challenges/
- Viasat Transforms Tactical Defense Networks through New Assured Edge-to-Cloud Connectivity Service, accessed May 1, 2026, https://www.barchart.com/story/news/1474340/viasat-transforms-tactical-defense-networks-through-new-assured-edge-to-cloud-connectivity-service
- Viasat Transforms Tactical Defense Networks through New Assured Edge-to-Cloud Connectivity Service, accessed May 1, 2026, https://www.viasat.com/news/latest-news/government/2026/viasat-tactical-mission-fabric-edge-to-cloud-connectivity/
- Tactical Networking | Viasat, accessed May 1, 2026, https://www.viasat.com/government/security/tactical-networking/
- Archive for the ‘SOF’ Category – Soldier Systems, accessed May 1, 2026, https://soldiersystems.net/category/sof/page/3/
- Draganfly Flex FPV, accessed May 1, 2026, https://draganfly.com/wp-content/uploads/2026/01/Flex-FPV-Spec-Sheet-Jan-2026-1.pdf
- Human-machine teaming in battle management: A collaborative effort across borders > Nellis Air Force Base > Article Display, accessed May 1, 2026, https://www.nellis.af.mil/News/Article-Display/Article/4370792/human-machine-teaming-in-battle-management-a-collaborative-effort-across-borders/
- Air Force AI writes battle plans faster than humans can — but some of them are wrong, accessed May 1, 2026, https://breakingdefense.com/2025/09/air-force-ai-writes-battle-plans-faster-than-humans-can-but-some-of-them-are-wrong/
- Air Force AI Targeting Tests Show Promise, Despite Hallucinations – The War Zone, accessed May 1, 2026, https://www.twz.com/news-features/air-force-ai-teaming-tests-show-promise-despite-hallucinations
- USSOCOM RCA 17 Event | Bid Banana, accessed May 1, 2026, https://bidbanana.thebidlab.com/bid/phKTOgNTTBp86n6SkQa9
- Soldier Systems Daily Soldier Systems Daily, accessed May 1, 2026, https://soldiersystems.net/page/53/
- CIA, SOCOM gearing up for rapid capability assessment with an eye toward ‘field-forward’ ops | DefenseScoop, accessed May 1, 2026, https://defensescoop.com/2026/02/10/cia-military-special-operations-forces-capability-assessment/
- Innovation Foundry (IF17) Event – SAM.gov, accessed May 1, 2026, https://sam.gov/opp/4c1f4ea9847e46c095d53a01117d836e/view
- USSOCOM RCA 17 Event 2026_RCA_17 – HigherGov, accessed May 1, 2026, https://www.highergov.com/contract-opportunity/ussocom-rca-17-event-2026-rca-17-s-0eb8d/
- Collaborative Event Design Thinking for Strategic Innovation – SOFWERX, accessed May 1, 2026, https://sofwerx.org/categories/collaboration-event
- USSOCOM Rapid Capability Assessment Event 20-24 April 2026 | Soldier Systems Daily, accessed May 1, 2026, https://soldiersystems.net/2026/02/10/ussocom-rapid-capability-assessment-event-20-24-april-2026/
- Viasat Transforms Tactical Defense Networks through New Assured Edge-to-Cloud Connectivity Service, accessed May 1, 2026, https://www.globenewswire.com/news-release/2026/04/23/3279813/0/en/viasat-transforms-tactical-defense-networks-through-new-assured-edge-to-cloud-connectivity-service.html
- Viasat launches military network designed to keep AI links running, accessed May 1, 2026, https://www.stocktitan.net/news/VSAT/viasat-transforms-tactical-defense-networks-through-new-assured-edge-qlccz6pyn8va.html
- Viasat Transforms Tactical Defense Networks through New Assured Edge-to-Cloud Connectivity Service, accessed May 1, 2026, https://investors.viasat.com/news-releases/news-release-details/viasat-transforms-tactical-defense-networks-through-new-assured
- Viasat Unveils Tactical Mission Fabric Edge-to-Cloud Network to Support AI-Enabled Military Missions, accessed May 1, 2026, https://www.executivebiz.com/articles/viasat-tactical-mission-fabric-dow-ai-edge
- Interoperability – Viasat, accessed May 1, 2026, https://www.viasat.com/government/connectivity/interoperability/
- Viasat Tactical Mission Fabric™ (TMF), accessed May 1, 2026, https://www.viasat.com/government/connectivity/interoperability/tmf/
- Flex FPV System – Draganfly Innovations, accessed May 1, 2026, https://draganfly.com/flex-fpv-system/
- Draganfly Announces Delivery of Flex FPV Systems to Major U.S. Prime Defense Contractor, accessed May 1, 2026, https://www.youtube.com/watch?v=OCx3SS5BjJI
- Draganfly – Flex FPV, accessed May 1, 2026, https://draganfly.com/wp-content/uploads/2026/02/Flex-Pager-Jan-2026-1.pdf
- Draganfly Delivers Modular Flex FPV Drone Systems to Major U.S. Defense Contractor, accessed May 1, 2026, https://dronelife.com/2025/06/03/draganfly-flex-fpv-drone/
- Navigating ‘Human-in-the-Loop’ and ‘Human-on-the-Loop’ | AFCEA International, accessed May 1, 2026, https://www.afcea.org/signal-media/navigating-human-loop-and-human-loop
- Combined US-ROK training strengthens Osan security – Pacific Air Forces, accessed May 1, 2026, https://www.pacaf.af.mil/Portals/6/CS%2025-01-16%20DigitalCopy.pdf
