1. Executive Summary
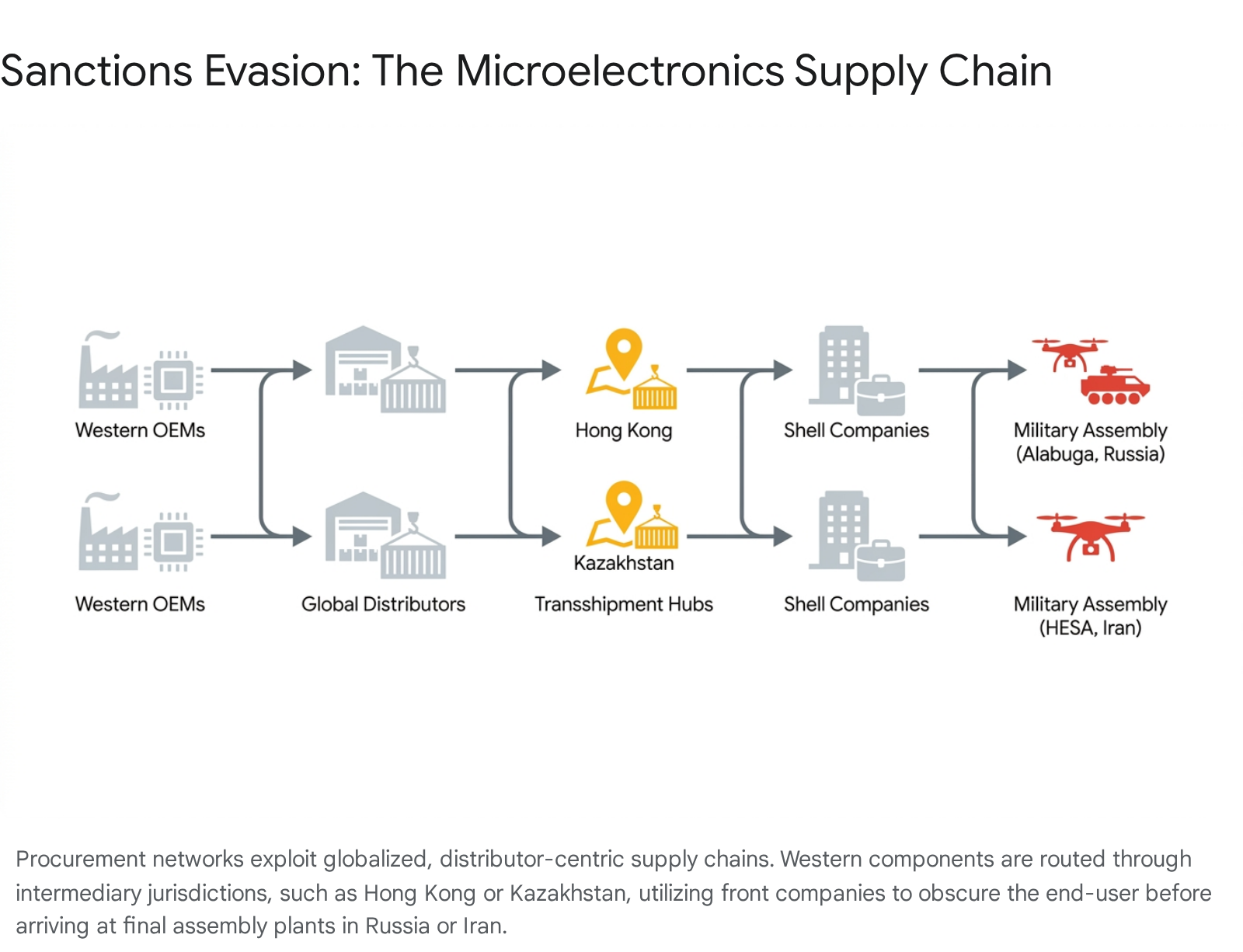
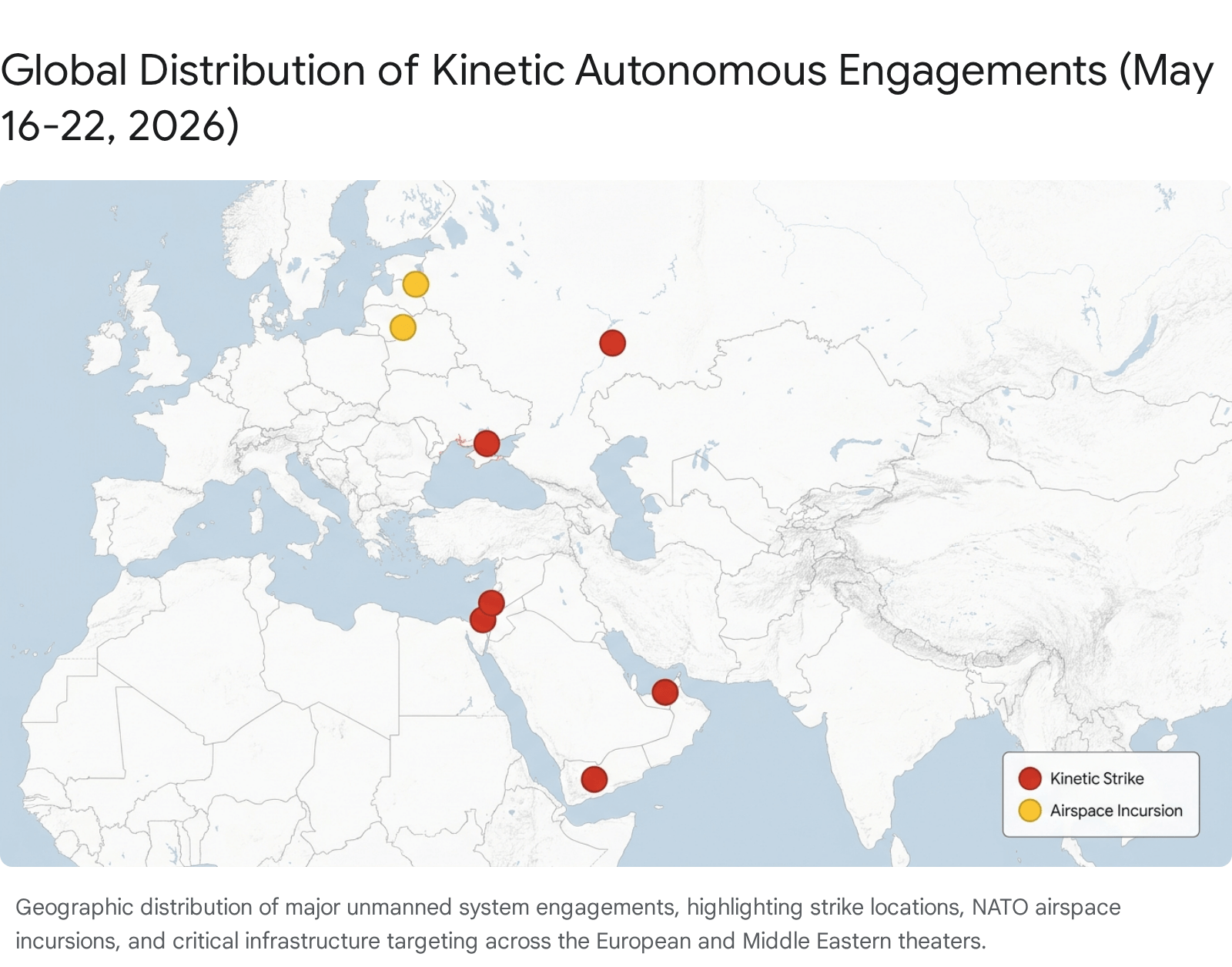
The trailing seven-day reporting period (May 16 – May 22, 2026) marks a critical inflection point in the operational deployment and strategic integration of unmanned systems across the air, land, sea, and space domains. Open-source intelligence collected over this timeframe indicates a rapidly accelerating shift away from centralized, high-cost, exquisite military platforms toward distributed, autonomous, and highly attritable architectures. This transition is no longer theoretical; it is being driven by immediate, unyielding battlefield necessities in the heavily contested environments of Eastern Europe and the Middle East. These pressing operational realities are subsequently catalyzing long-term procurement realignments, legislative adjustments, and doctrinal overhauls among major global powers attempting to adapt to the new character of warfare.
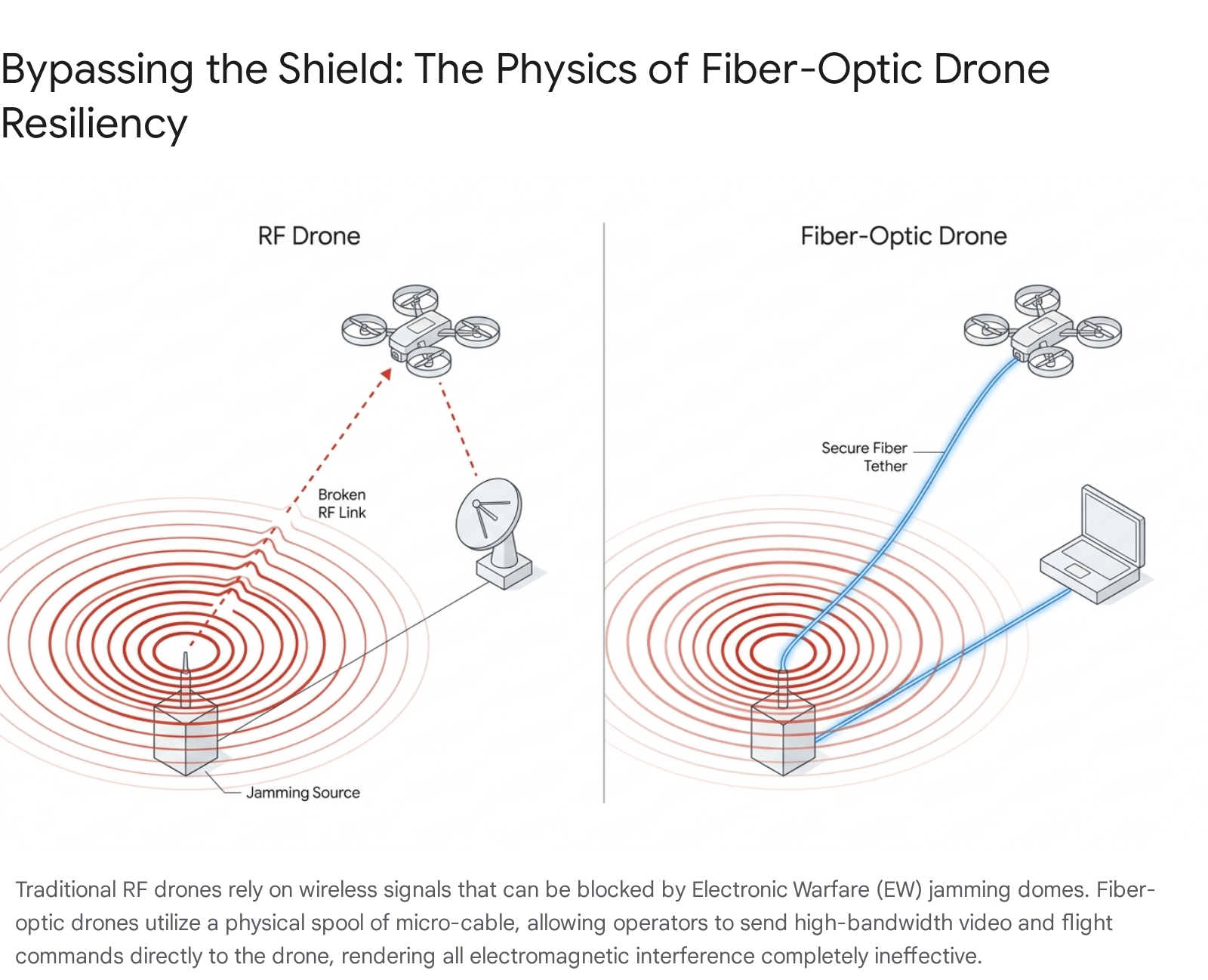
Three primary macro-trends have dominated the global operational landscape over the past week, demanding immediate attention from defense leadership. First, the proliferation of low-cost, fiber-optic-guided First-Person View (FPV) drones has successfully neutralized billions of dollars in traditional Radio Frequency (RF) electronic warfare (EW) investments.1 By utilizing a physical, unspooling micro-cable to transmit high-bandwidth video and command signals, these systems render standard electromagnetic jamming domes entirely obsolete.2 This technological leap has fundamentally altered the tactical geometry of border conflicts, most notably along the Israel-Lebanon border, forcing advanced militaries to resort to rudimentary physical countermeasures such as chain-link fencing and localized kinetic interceptors.1
Second, the strategic hazard of “EW spillover” has manifested vividly and dangerously on the North Atlantic Treaty Organization (NATO) Eastern Flank.7 As Russian forces deploy massive, indiscriminate signal jamming arrays to blind the navigation systems of long-range Ukrainian strike drones, these autonomous systems are being inadvertently diverted deep into alliance airspace.7 This phenomenon has triggered unprecedented civilian bunker protocols in major European capitals, led to the kinetic engagement of drones by NATO fighter aircraft, and caused severe political destabilization, including the collapse of a coalition government in the Baltic region.7 This underscores that modern electronic warfare inherently creates an uncontrollable, physical escalation trap that does not respect international borders.
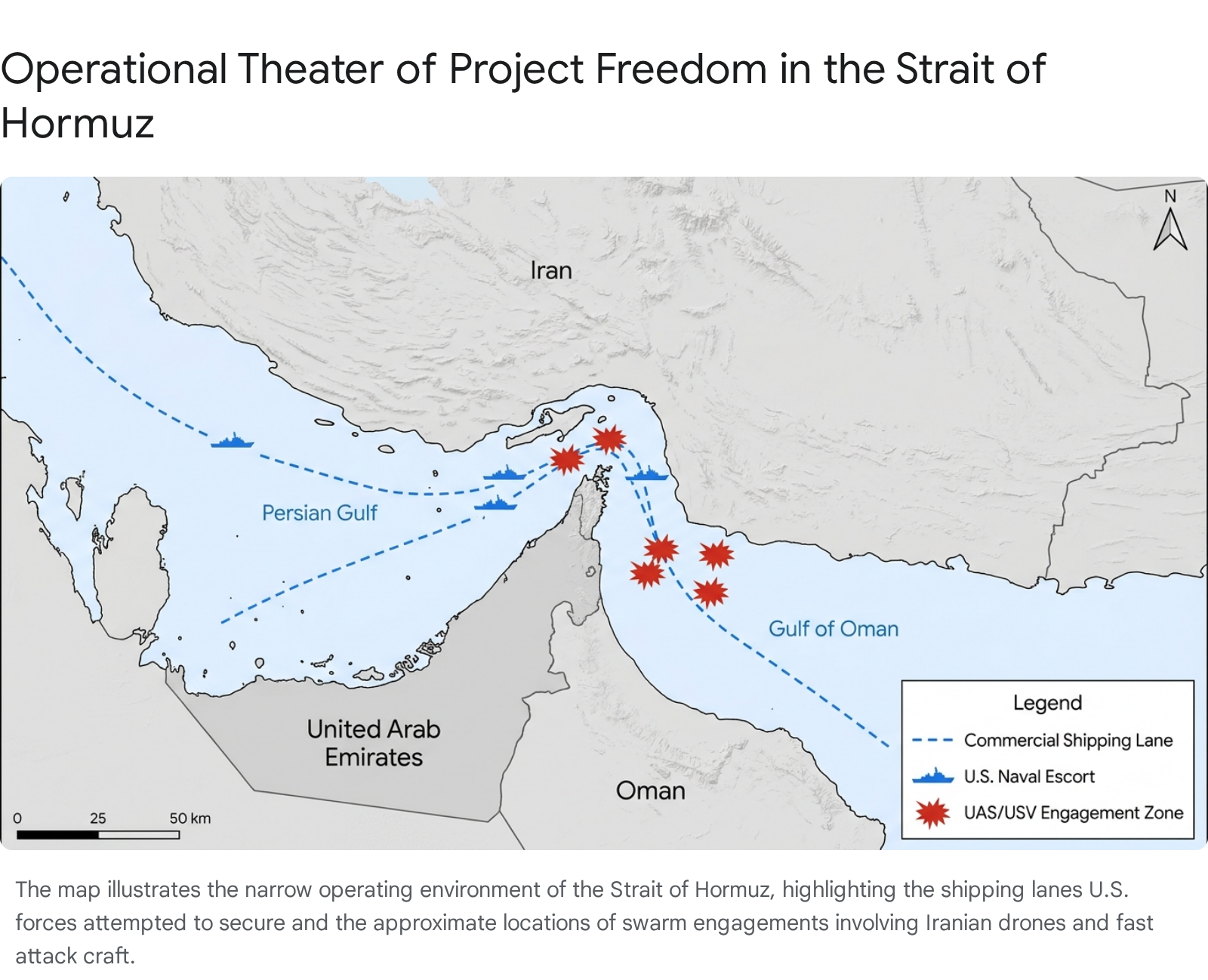
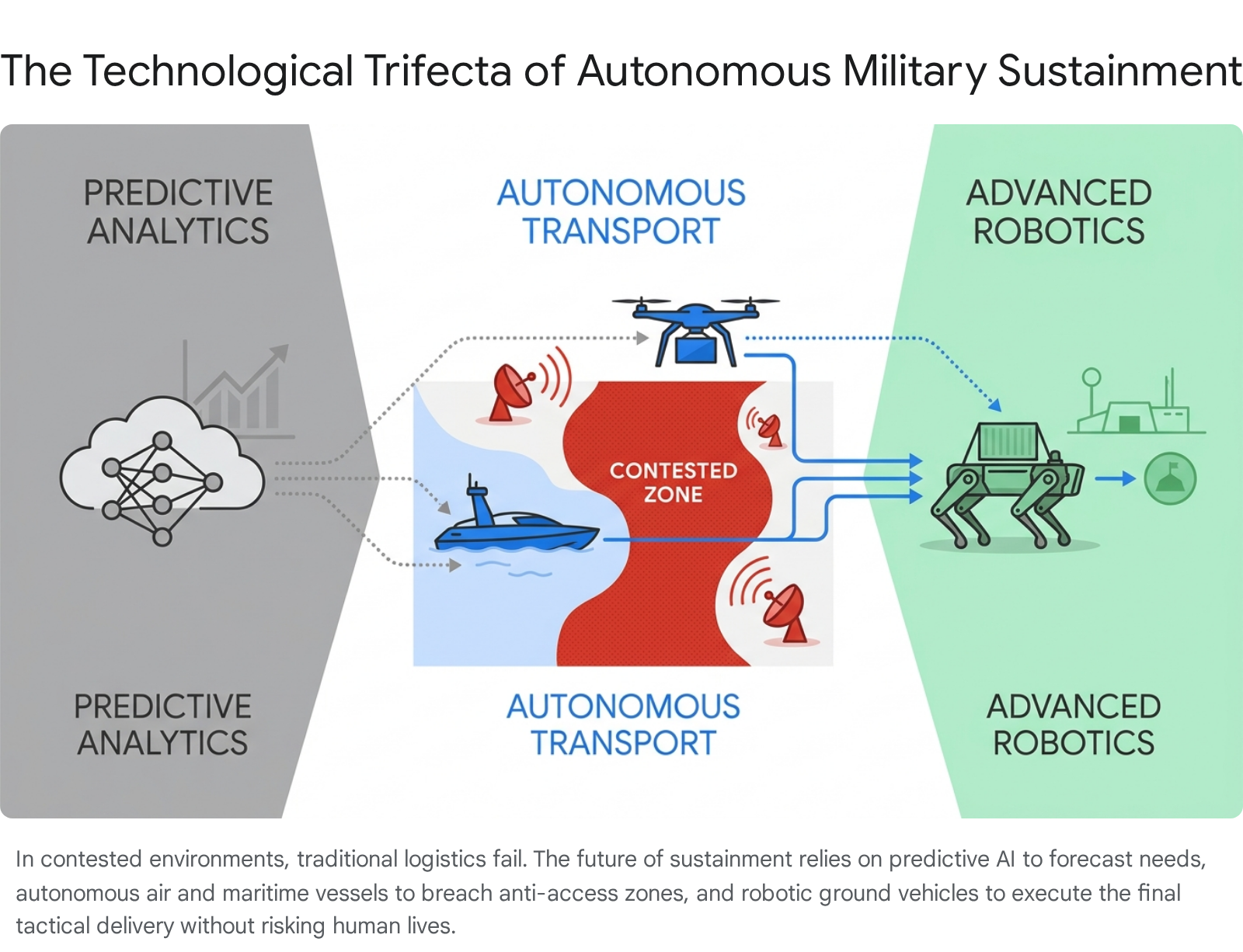
Third, the maritime domain is undergoing a rapid and profound democratization of force. State and non-state actors are increasingly deploying expendable Unmanned Surface Vessels (USVs) and Unmanned Underwater Vehicles (UUVs) to achieve “precise mass” and asymmetric sea denial capabilities.10 This is most evident in the major procurement decisions emerging from the Turkish defense industrial base, which is pivoting heavily toward autonomous naval swarm capabilities designed to threaten traditional surface combatants and submarines without exposing crewed platforms to reciprocal risk.12 Similarly, the United States Navy’s advancement of medium unmanned surface vessel prototypes signals a recognition that distributed maritime operations require platforms that can be manufactured rapidly and risked heavily in contested littorals.10
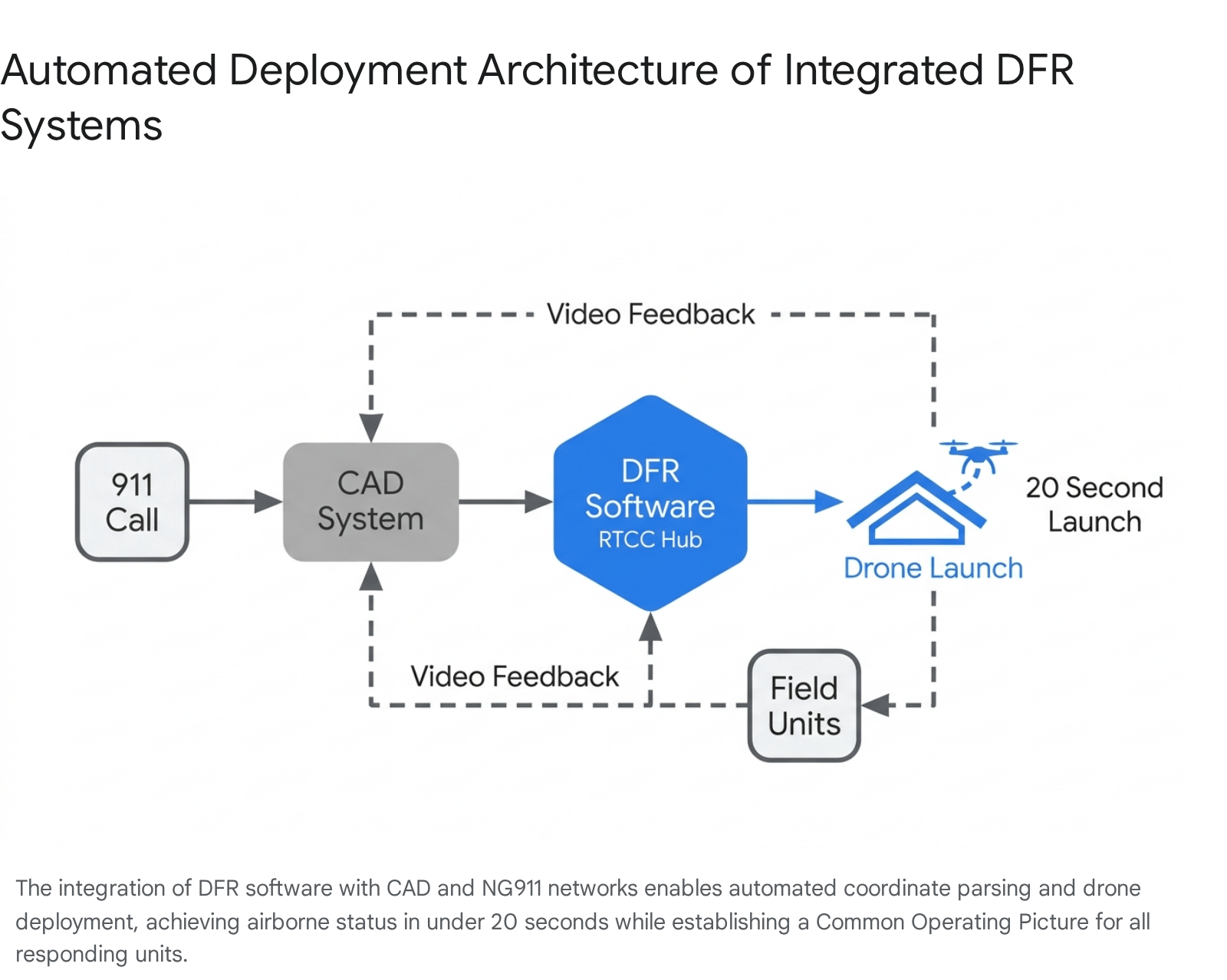
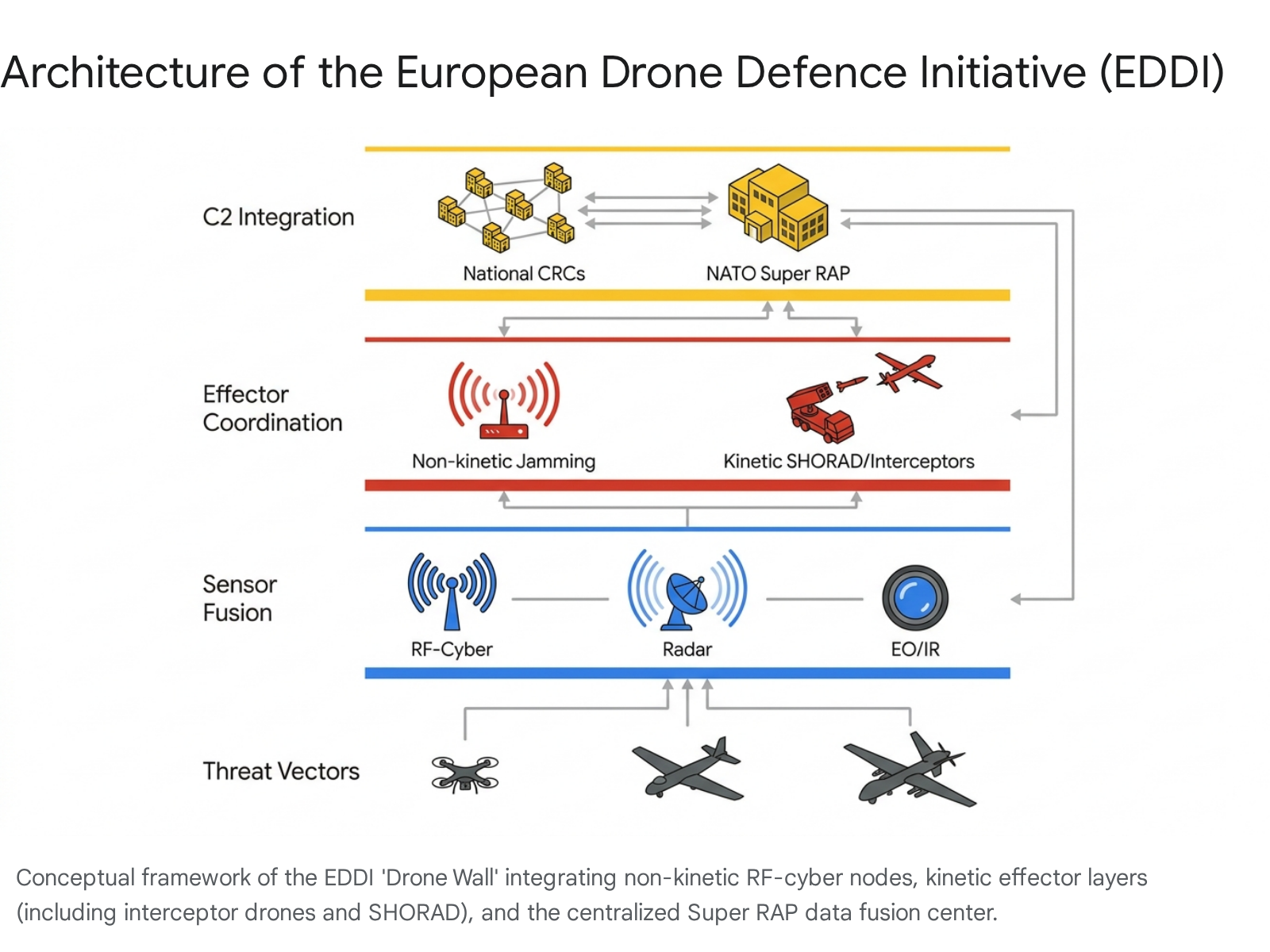
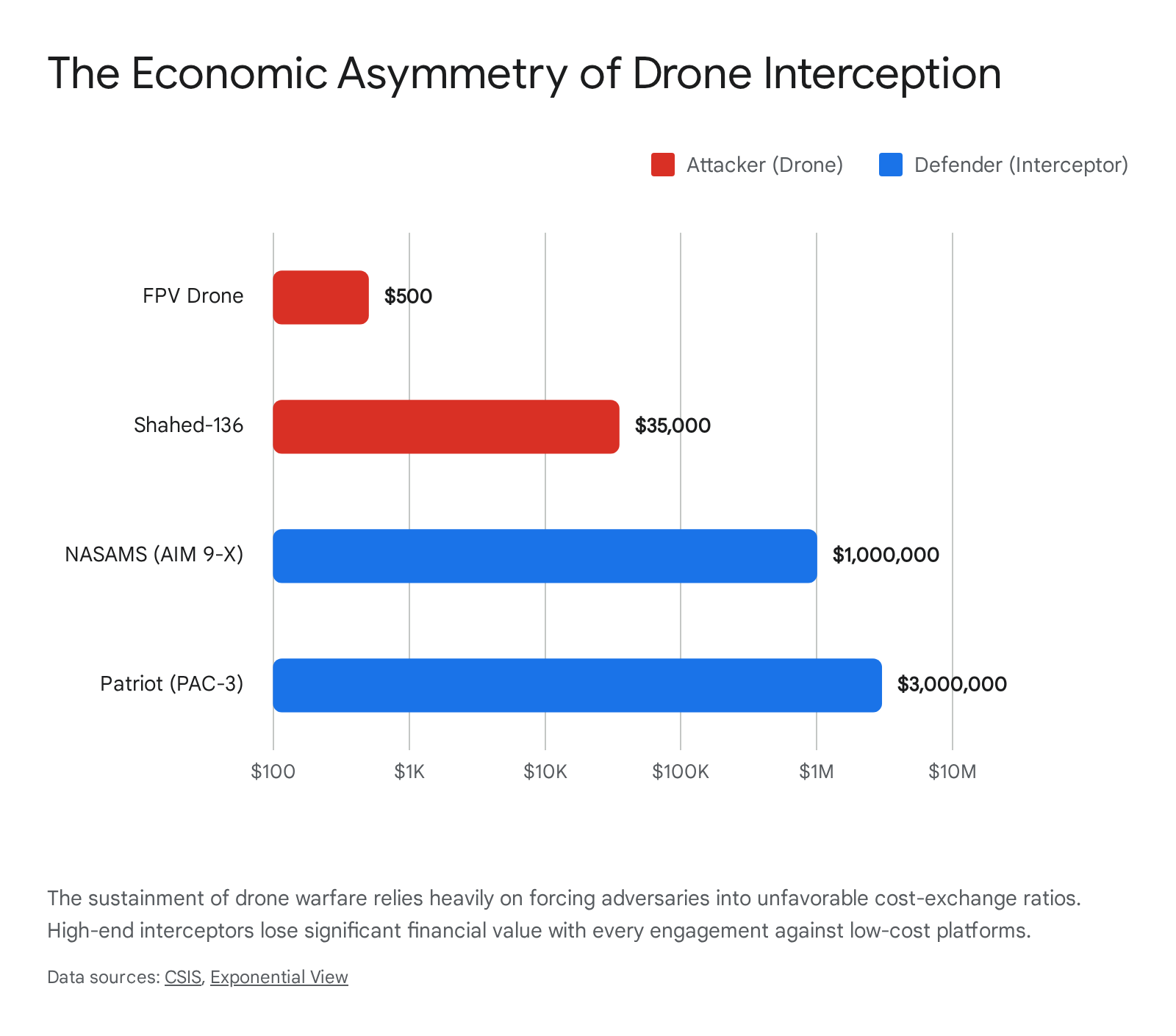
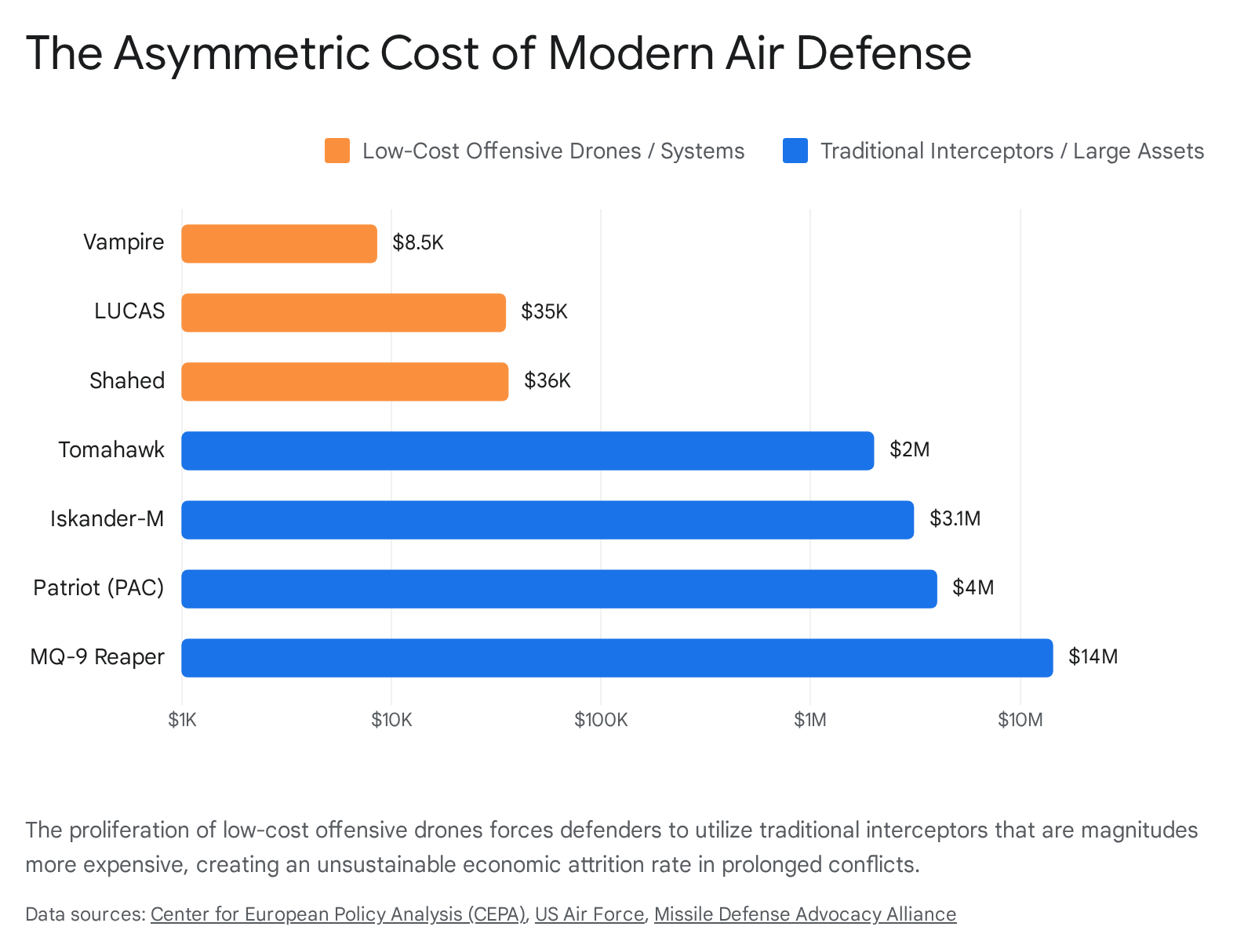
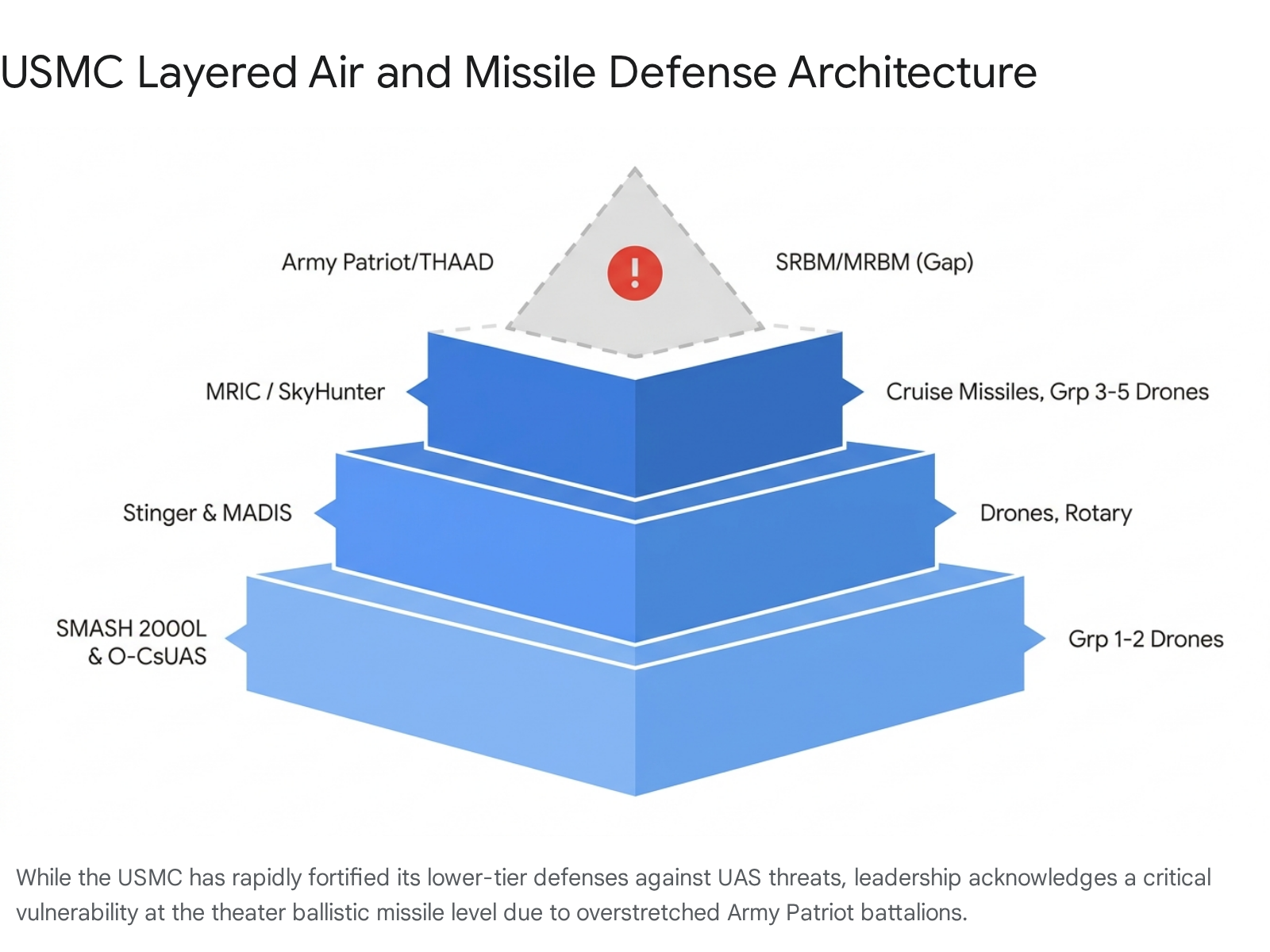
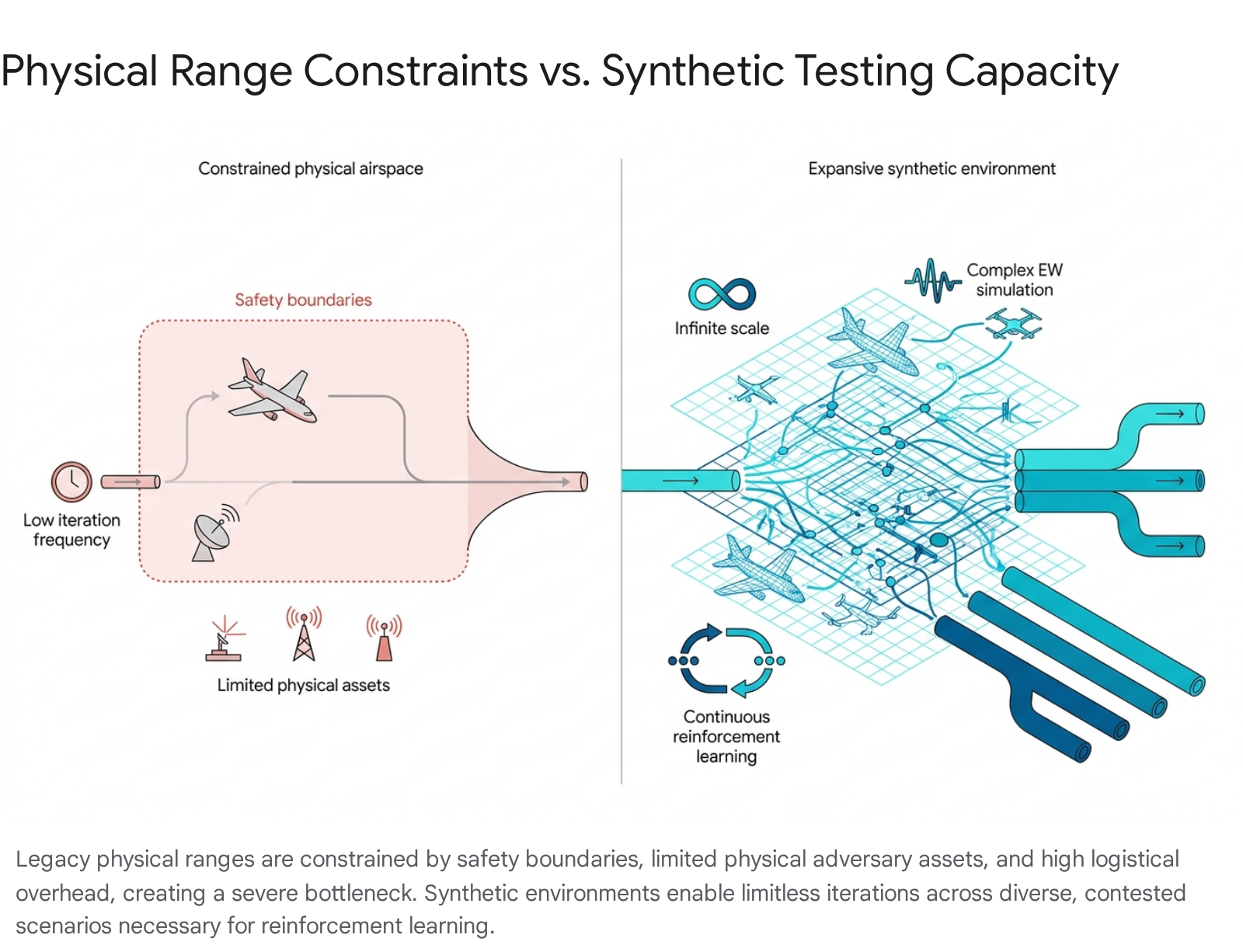
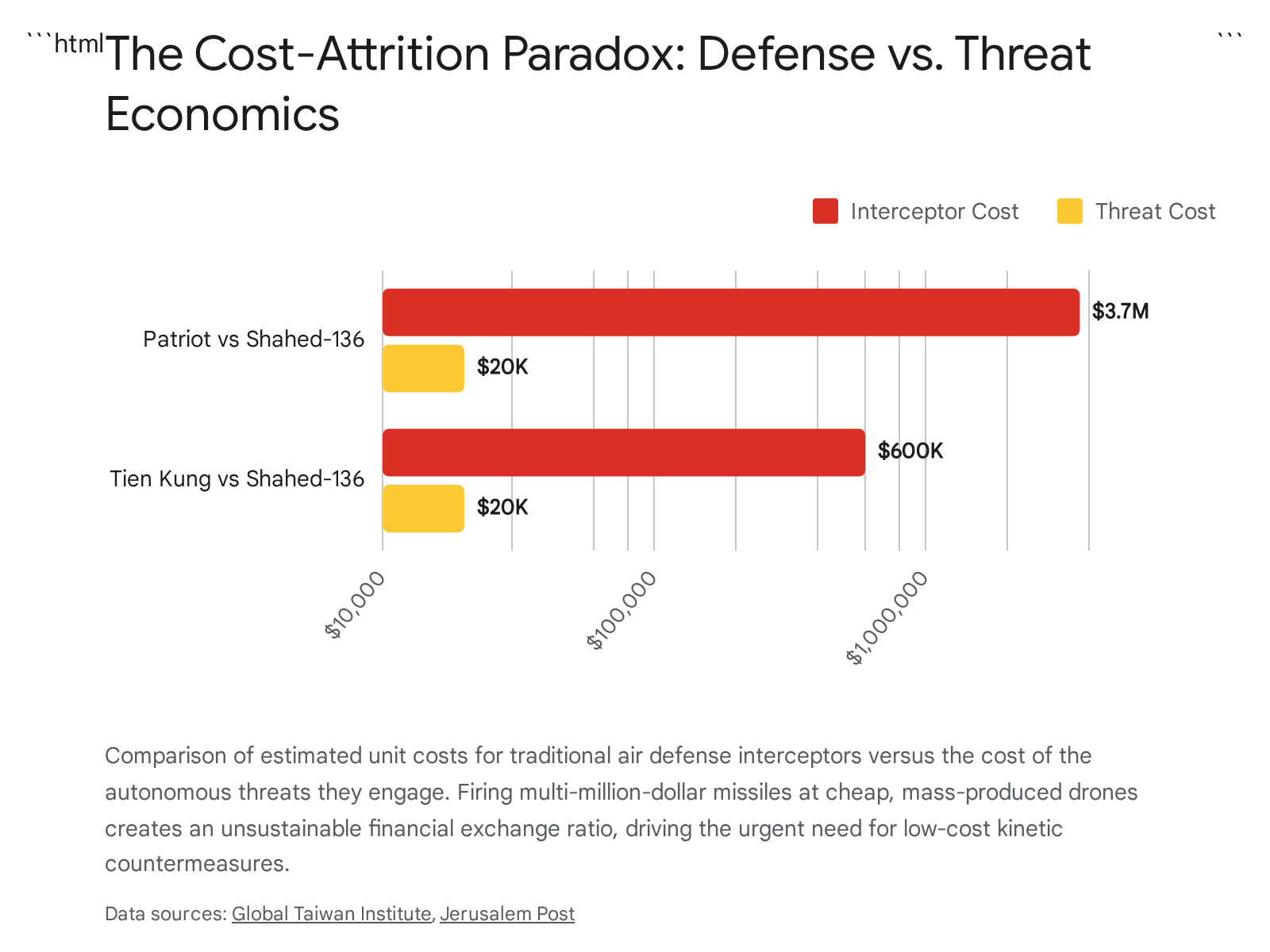
To counter these evolving, multi-domain threats, global defensive architectures are undergoing rapid iteration. The introduction of low-cost kinetic interceptors aims to bridge the currently unsustainable cost-attrition gap that exists between $20,000 offensive drones and multi-million-dollar defensive surface-to-air missiles.14 Concurrently, global legislatures are rapidly advancing policy frameworks to incentivize domestic industrial bases to produce autonomous systems at scale, recognizing that industrial capacity is now a primary deterrent.17 The integration of these systems into legacy command and control networks—such as utilizing utility helicopters as airborne drone control nodes—demonstrates an immediate operational desire to extend sensor and strike ranges while preserving irreplaceable human capital.14
The following comprehensive report provides an exhaustive, chronologically sorted analysis of the week’s global kinetic events, product reveals, and strategic lessons learned. This synthesis delivers a nuanced understanding of the evolving autonomous battlespace, providing actionable intelligence on the state of military robotics across all operational domains.
2. Global Situation Log
Note: The combined list of events, battles, and kinetic engagements below is sorted strictly by date (chronologically) and then alphabetically by the primary country involved, in accordance with intelligence reporting standards.
May 16, 2026
Israel: Escalation of Fiber-Optic FPV Drone Casualties In southern Lebanon, along the highly contested and volatile Israeli border, an Israel Defense Forces (IDF) officer, Capt. Maoz Israel Recanati, was killed by a Hezbollah-operated First-Person View (FPV) drone.5 This incident marked the seventh Israeli military death resulting from autonomous systems since a nominal, yet heavily violated, ceasefire went into effect in April 2026.5 The engagement underscores the lethal persistence of autonomous threats in active conflict zones, demonstrating that low-cost drones allow non-state actors to maintain high operational tempo and inflict continuous attrition despite diplomatic pauses.3 The event specifically highlighted the growing, complex tactical challenge posed by Hezbollah’s rapid adoption of fiber-optic tethered drones.2 These platforms, which unspool a micro-cable to maintain a physical data link with the operator, are entirely immune to standard Radio Frequency (RF) jamming, presenting a severe force protection challenge for IDF troops deployed along the border and negating millions of dollars of advanced electronic warfare infrastructure.2
May 17, 2026
United Arab Emirates: Strategic Drone Strike on Nuclear Infrastructure A significant and highly provocative escalation in regional hostilities occurred when three unidentified strike drones penetrated the UAE’s western border with Saudi Arabia, deliberately targeting the $20 billion Barakah Nuclear Power Plant situated in the remote Al Dhafra Region of Abu Dhabi.19 The facility is the UAE’s sole nuclear power plant and the only operational commercial nuclear reactor in the Arab world, capable of providing up to a quarter of the nation’s energy needs.19 While UAE layered air defenses successfully tracked and intercepted two of the incoming munitions, a third drone breached the outer defensive perimeter and struck an electrical generator situated outside the plant’s protected inner zone, igniting a localized fire.19
The International Atomic Energy Agency (IAEA), led by Director General Rafael Mariano Grossi, confirmed that the strike caused a fire but resulted in no radiological release, though the incident forced one of the facility’s reactors to temporarily transition to emergency diesel generator power as a safety precaution.19 The attack represents a dangerous threshold crossing, marking the first direct kinetic strike on the Arabian Peninsula’s nuclear infrastructure.20 While no entity immediately claimed responsibility, the UAE government labeled the event an “unprovoked terrorist attack”.19 Regional intelligence assessments indicate the drones were likely launched by Iranian-backed proxy militias operating in Yemen or Iraq.19 The strike is widely interpreted as a deliberate, calibrated warning shot amidst the broader, simmering US-Iran conflict, intended to demonstrate the vulnerability of critical economic and energy infrastructure in Gulf states that host American and Israeli defense personnel.19
Ukraine: Precision Swarm Attack on Russian Command Infrastructure Ukrainian special operations forces executed a massive, highly coordinated drone swarm attack against the Russian Federal Security Service (FSB) headquarters located on the Arabat Spit in the occupied Kherson region, near the city of Henichesk.26 Utilizing advanced intelligence-driven targeting, the Ukrainian Security Service’s (SSU) Special Operations Center “A” deployed a fleet of medium-range kamikaze drones to strike all nine individual buildings comprising the sprawling headquarters complex.27 The autonomous systems demonstrated exceptional terminal precision by specifically targeting the roofs and flying directly through the windows of the hardened structures, resulting in catastrophic internal detonations and a large-scale fire.27
The extent of the thermal event was independently verified by NASA’s Fire Information for Resource Management System (FIRMS) satellite monitoring, which detected massive heat signatures at the strike coordinates.27 According to statements from Ukrainian President Volodymyr Zelensky, the operation was highly successful, resulting in approximately 100 Russian casualties (killed and wounded) and the total destruction of an accompanying Russian Pantsir-S1 self-propelled anti-aircraft missile and gun system tasked with defending the airspace.27 This strike severely degraded Russian localized command, control, and intelligence capabilities in the southern operational direction.27
May 18, 2026
Norway: Bilateral Maritime Unmanned Integration in the High North In the strategically critical High North, the United States Navy’s Unmanned Surface Vessel Squadron Three (USVRON 3) and Commander, Task Force 68 concluded a major phase of the bilateral Arctic Sentry 2026 exercise alongside the Norwegian Armed Forces.28 Operating out of the Ramsund Naval Base near Harstad, allied expeditionary forces deployed and rigorously tested advanced Robotics and Autonomous Systems (RAS).28 Key platforms evaluated included the Global Autonomous Reconnaissance Craft and the Lightfish Unmanned Surface Vessel (USV).28
The complex maneuvers in the Breivika Bay and surrounding fjords were explicitly designed to validate the operational endurance, high-speed navigational reliability, and sensor integration of autonomous surface vessels in some of the world’s most challenging and unforgiving environmental conditions.28 Concurrently, explosive ordnance disposal (EOD) technicians from the U.S. Navy’s EOD Mobile Unit 8 and Norwegian dive teams utilized remotely operated underwater robots to simulate the location, identification, and neutralization of complex improvised explosive devices (IEDs) and explosive hazards in frigid, contested littoral waters.28 These operations are a direct response to the massive Russian military build-up around the Barents Sea, demonstrating NATO’s commitment to pushing the boundaries of autonomous innovation to maintain a critical defensive edge in the Arctic theater.29
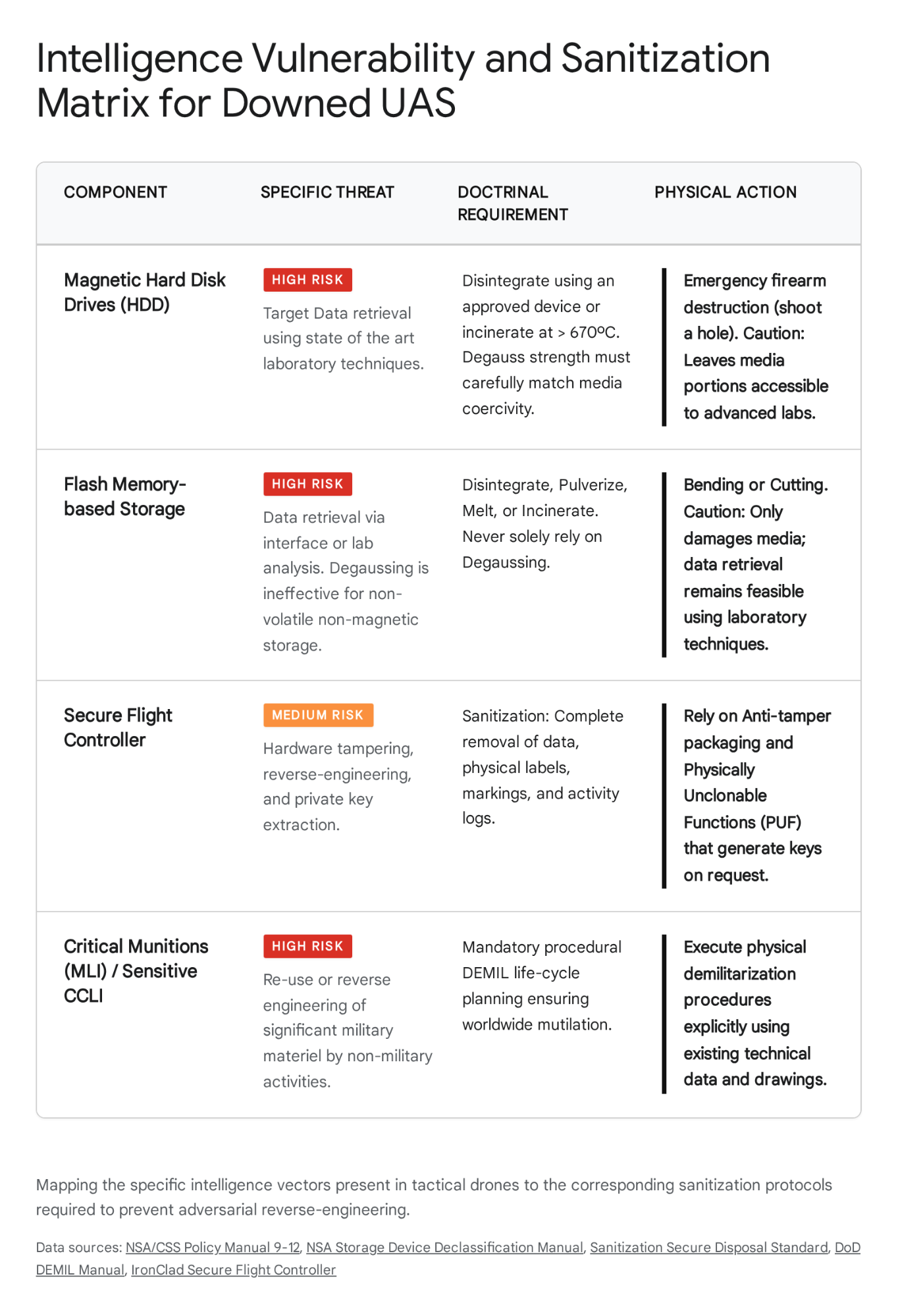
Yemen: Loss of High-Value US Unmanned Asset Houthi militant forces, operating within the context of the ongoing Red Sea crisis, successfully engaged and shot down a United States Air Force MQ-9A Reaper drone operating over the Marib Governorate in central Yemen.30 Video footage circulating across regional media networks corroborated the downing, showing the burning wreckage and distinct fragments of the $150 million intelligence, surveillance, and reconnaissance (ISR) platform scattered across the desert terrain.30
The MQ-9 Reaper represents one of America’s most advanced, heavily relied-upon systems for persistent surveillance and precision strike missions; unconfirmed reports suggest this specific aircraft may have been carrying the highly secretive AGM-114 R9X ‘Ninja’ kinetic missile.30 The incident amplifies deep, ongoing concerns within the Pentagon regarding the severe vulnerability of large, slow-moving, non-stealth unmanned aerial vehicles when operating against increasingly sophisticated, Iranian-supplied air defense systems utilized by non-state actors.30 This shootdown adds to a growing tally of expensive U.S. drone losses in the region, highlighting a shifting balance of power where cheap interceptors can reliably destroy exquisite U.S. reconnaissance assets.30
May 19, 2026
Estonia: First NATO Air-to-Air Engagement of a Diverted Drone A critical and highly dangerous airspace violation occurred over the Baltic states, resulting in unprecedented kinetic action by alliance forces.7 A suspected Ukrainian long-range strike drone crossed deep into Estonian sovereign airspace.7 Advanced Estonian radar networks tracked the unmanned system well before it breached the international border, allowing defense officials to continuously monitor its erratic flight path.7 After analyzing the drone’s trajectory and determining it posed a residual threat to civilian populations, Estonian Defense Minister Hanno Pevkur authorized a kinetic intercept.7
A Romanian Air Force F-16 fighter jet, operating out of the Šiauliai airbase in neighboring Lithuania as part of the rotational NATO Air Policing mission, scrambled, intercepted, and successfully shot down the drone.7 The wreckage fell into a swampy, unpopulated area between Lake Võrtsjärv and Põltsamaa.7 The Ukrainian foreign ministry, through spokesperson Heorhii Tykhyi, promptly issued a formal apology to Estonia for the “unintended incident”.7 Deep intelligence analysis confirmed that the drone was originally programmed by Kyiv to strike legitimate military targets deep inside the Russian Federation.7 However, the drone was pushed severely off course by powerful, indiscriminate Russian electronic warfare (EW) and GPS jamming systems operating along the border, causing its navigation suite to fail and the drone to drift aimlessly into NATO territory.7 This event marks the first time a NATO aircraft has actively engaged a drone over alliance territory due to direct conflict spillover, raising severe concerns regarding the uncontrollable nature of regional electronic warfare.7
Russia: Hardening of Infrastructure Against Autonomous Threats In a direct, physical response to the intensifying mid-range and long-range drone strike campaign orchestrated by Ukrainian forces, Russian military authorities have initiated rapid infrastructural hardening measures.35 Satellite imagery collected over the highly strategic Kaliningrad exclave—a vital Russian outpost nestled between NATO members Poland and Lithuania—revealed fresh construction activity.35 Specifically, imagery from late April through mid-May 2026 showed the rapid erection of four new, heavily reinforced aircraft hangars at the Chkalovsk Naval Air Base.35 This construction represents an explicit operational adaptation designed to shield high-value Russian military aviation assets from pervasive Ukrainian drone reconnaissance and the threat of localized kinetic strikes, acknowledging the inability of localized air defenses to guarantee 100% interception rates.35
May 20, 2026
Lithuania: Unprecedented Civilian Bunker Alert The geopolitical anxiety surrounding stray autonomous systems and EW spillover reached a crescendo in Vilnius, the capital of Lithuania.7 At approximately 10:20 AM local time, the Lithuanian defense ministry and the National Crisis Management Centre detected a radar signature highly consistent with a combat unmanned aerial vehicle crossing into Lithuanian airspace from the direction of Belarus and Latvia.7 In response, authorities triggered a nationwide emergency broadcast, sending mobile phone alerts that urged all residents of the capital to immediately seek shelter.7
This event marked a historic milestone: the first time since the onset of the 2022 invasion of Ukraine that a NATO and EU capital city enacted a full civilian bunker protocol.7 Lithuanian President Gitanas Nausėda, Prime Minister Inga Ruginienė, cabinet members, and members of parliament were rapidly evacuated to underground secure facilities.7 Schools moved children into designated basements, and all commercial air and rail traffic around Vilnius was totally suspended for approximately one hour.7 While NATO jets scrambled to intercept the threat, they were unable to physically locate the drone.7 Defense officials later assessed that the anomaly was either a dummy drone designed by adversaries to spoof radar systems and test response times, or a diverted system that subsequently exited the airspace unnoticed.7 The incident drew fierce condemnation from European Commission President Ursula von der Leyen, who stated that Russia and Belarus bear “direct responsibility” for endangering the lives of people on NATO’s eastern flank through their reckless use of airspace and electronic warfare.7
May 21, 2026
Ukraine: Sustained Mid-Range Interdiction Campaign Overnight, Ukrainian armed forces continued a highly systematic, mid-range autonomous strike campaign aimed at degrading critical Russian logistical networks, transport arteries, and supply depots situated deep within occupied territories.37 Coordinated drone strikes successfully hit a major Russian materiel and technical storage warehouse located in occupied Rovenky, a strategic logistics hub positioned roughly 130 kilometers behind the active frontline.37 Concurrently, additional strikes targeted military assets and troop concentrations in occupied Starobilsk in the Luhansk Oblast.37 This sustained strategy of autonomous, deep-area attrition is systematically complicating Russian resupply efforts, forcing commanders to disperse critical ammunition and fuel supplies over wider, less efficient geographical areas to avoid catastrophic losses from relatively inexpensive drones.37
May 22, 2026
Russia: Strategic Energy Infrastructure Targeted Ukrainian long-range autonomous systems demonstrated remarkable penetration capabilities, flying over 800 kilometers deep into sovereign Russian airspace to execute a precision strike against the Syzran oil refinery.38 Located in the Samara region, the facility is a major asset owned by the Russian state oil and gas conglomerate Rosneft.38 The kinetic strike ignited a massive fire at the facility, severely disrupting refining operations.38 This attack directly supports Kyiv’s stated strategic objective for the month of May: the systematic degradation of Russian oil refineries, storage depots, and the broader macroeconomic infrastructure that generates the revenue necessary to fund Moscow’s ongoing military operations.38 The ability of Ukrainian drones to bypass vast swaths of Russian air defense networks to hit strategic energy targets continues to place immense political and economic pressure on the Kremlin.38
Ukraine: Defense Against Massed Autonomous Swarms In retaliation, the Russian Federation launched a highly complex, multi-vector nighttime swarm attack utilizing an astonishing 124 strike Unmanned Aerial Vehicles (UAVs) directed at Ukrainian civilian and military infrastructure.37 The massive drone swarm was launched simultaneously from multiple geographic origin points, including Kursk, Shatalovo, Bryansk, Millerovo, Primorsko-Akhtarsk, and occupied Hvardiiske in Crimea, designed to overwhelm radar operators.39 The attack package was technologically diverse, consisting of a mix of jet-powered Shahed variants, Gerbera, Italmas, and “Parodiya” type decoy drones intended to exhaust interceptor stockpiles.39
Demonstrating high proficiency in integrated air and missile defense, the Ukrainian military mounted a comprehensive response.39 Utilizing a layered defense network comprised of aviation assets, anti-aircraft missile forces, specialized electronic warfare units, and highly agile mobile fire groups equipped with heavy machine guns and searchlights, Ukrainian defenders successfully shot down or electronically suppressed 102 of the 124 incoming drones.39 Despite the high interception rate, authorities recorded hits by 12 strike drones at various locations, highlighting the statistical reality that in massive swarm attacks, a small percentage of munitions will inevitably penetrate even the most robust defenses.39
Table 1: Global Drone Incident Log (May 16 – May 22, 2026)
| Date | Location | Domain | Primary System(s) Involved | Incident Summary | Strategic Impact |
| May 16 | S. Lebanon / Israel | Air / Land | Hezbollah Fiber-Optic FPV | IDF officer killed by tethered drone immune to RF jamming. | Validated the lethality and EW-immunity of physical fiber-optic command links. |
| May 17 | Abu Dhabi, UAE | Air / Critical Infra. | Unidentified Strike Drones (3) | Drones targeted Barakah Nuclear Plant; one hit an external generator. | First kinetic strike on Arabian Peninsula nuclear infrastructure; high regional escalation. |
| May 17 | Arabat Spit, Ukraine | Air / Land | Ukrainian Kamikaze Drones | Massive swarm destroyed 9 FSB HQ buildings and a Pantsir-S1 system. | Severe degradation of Russian command and control in the southern theater. |
| May 18 | High North, Norway | Sea | USV (Lightfish), UUVs | US and Norwegian forces tested high-speed USVs and EOD robots in the Arctic. | Demonstrated NATO intent to contest the Barents Sea using autonomous naval assets. |
| May 18 | Marib, Yemen | Air | US MQ-9A Reaper | Houthi forces shot down a $150M US intelligence and strike drone. | Highlighted vulnerability of exquisite, slow-moving assets against non-state air defenses. |
| May 19 | Estonia Airspace | Air | Ukrainian Drone, NATO F-16 | Stray drone pushed off course by Russian EW was shot down by a Romanian F-16. | First NATO kinetic engagement of a drone over alliance territory due to EW spillover. |
| May 20 | Vilnius, Lithuania | Air | Unidentified Drone Radar Track | Radar anomaly triggered unprecedented civilian bunker alert and grounded flights. | Demonstrated the massive psychological and societal disruption caused by stray drones. |
| May 22 | Samara Region, Russia | Air | Ukrainian Long-Range Drones | Strike penetrated 800km to hit the Syzran oil refinery (Rosneft). | Continued degradation of Russian macroeconomic energy infrastructure. |
| May 22 | Ukraine (Nationwide) | Air | Shahed, Gerbera, Decoys (124) | Massive Russian multi-vector swarm attack; Ukraine intercepted 102 drones. | Showcased the necessity of deep magazine, layered air defense networks against swarms. |
3. Product Developments
Note: The combined list of product developments, platform reveals, and capability upgrades below is sorted strictly by date (chronologically) and then alphabetically by the primary country involved.
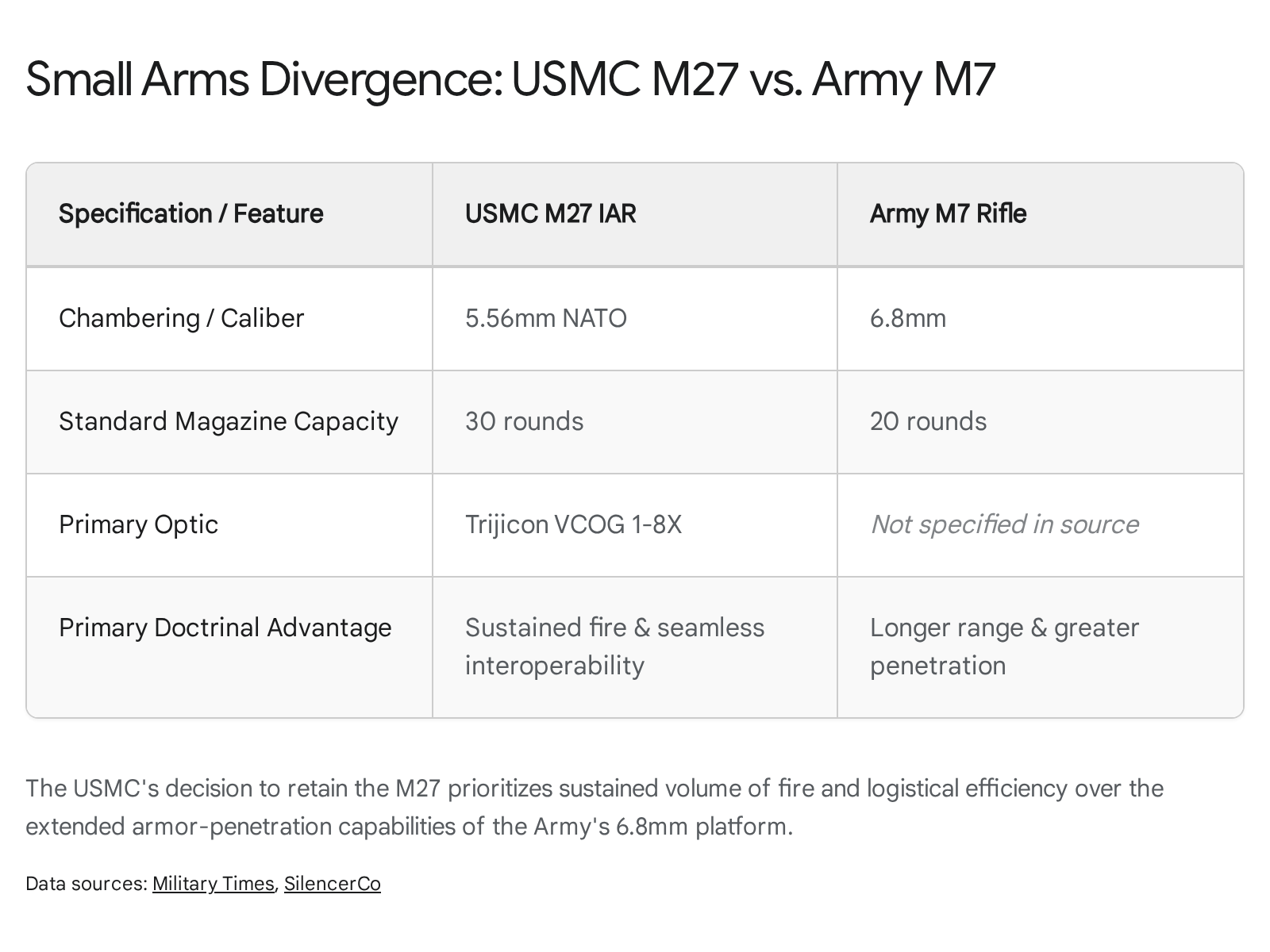
May 18, 2026
United States: Operational Testing of Mission Master SP UGV The United States Marine Corps, operating through Combat Logistics Battalion 2 of the 2nd Marine Logistics Group, commenced rigorous field testing of the Mission Master SP Unmanned Ground Vehicle (UGV) at Marine Corps Base Camp Lejeune, North Carolina.40 Funded by the Marine Corps Warfighting Laboratory, this experimental capability aims to aggressively validate design changes and rigorously assess the operational stability of ground robotics in complex, contested littoral environments.40 The testing paradigm focuses heavily on autonomous resupply, casualty evacuation, and logistics distribution, attempting to connect human command intent to reliable, consistent robotic execution over rugged terrain.40 These field trials are occurring in direct preparation for a major Army and Marine Corps request for proposal regarding autonomous resupply solutions, expected to be released later in the year.41
May 20, 2026
United States: Advancements in Wireless Autonomous Power Architecture Red Cat Holdings, a prominent and rapidly expanding provider of military drone technology, announced the strategic acquisition of Quaze Technologies Inc., a Québec-based developer specializing in wireless power transfer solutions for unmanned systems.42 This acquisition is designed to rapidly integrate advanced wireless power architecture across Red Cat’s entire “Family of Systems,” while maintaining a platform-agnostic model that can support third-party Original Equipment Manufacturers (OEMs) across the air, ground, and maritime domains.42 The development of persistent, reliable wireless charging capabilities is viewed across the defense industry as a critical enabler for persistent Intelligence, Surveillance, and Reconnaissance (ISR) missions.42 By eliminating the logistical tether of human operators needing to manually swap batteries, drones can remain deployed autonomously in forward, highly contested environments for radically extended durations.42
May 21, 2026
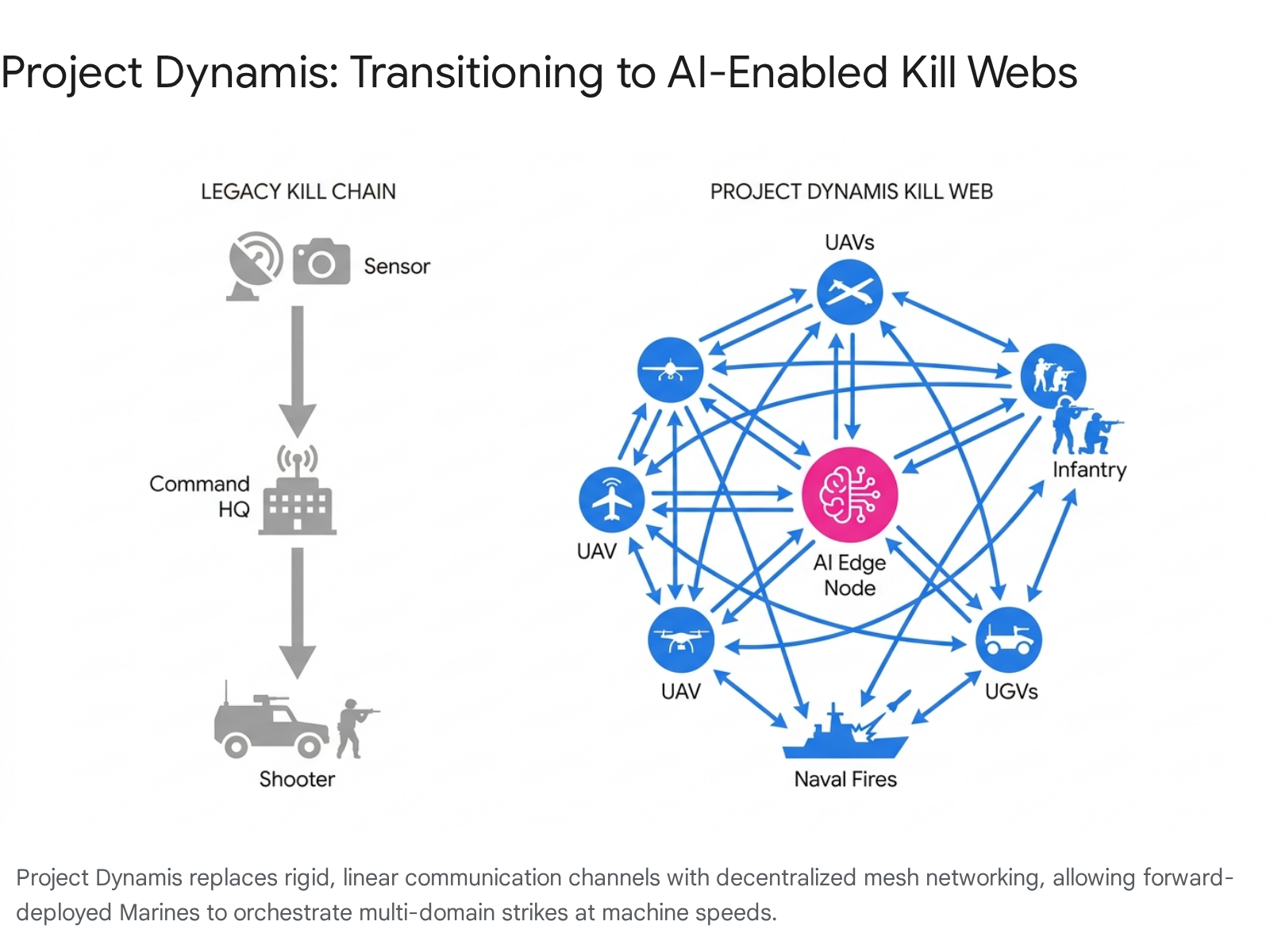
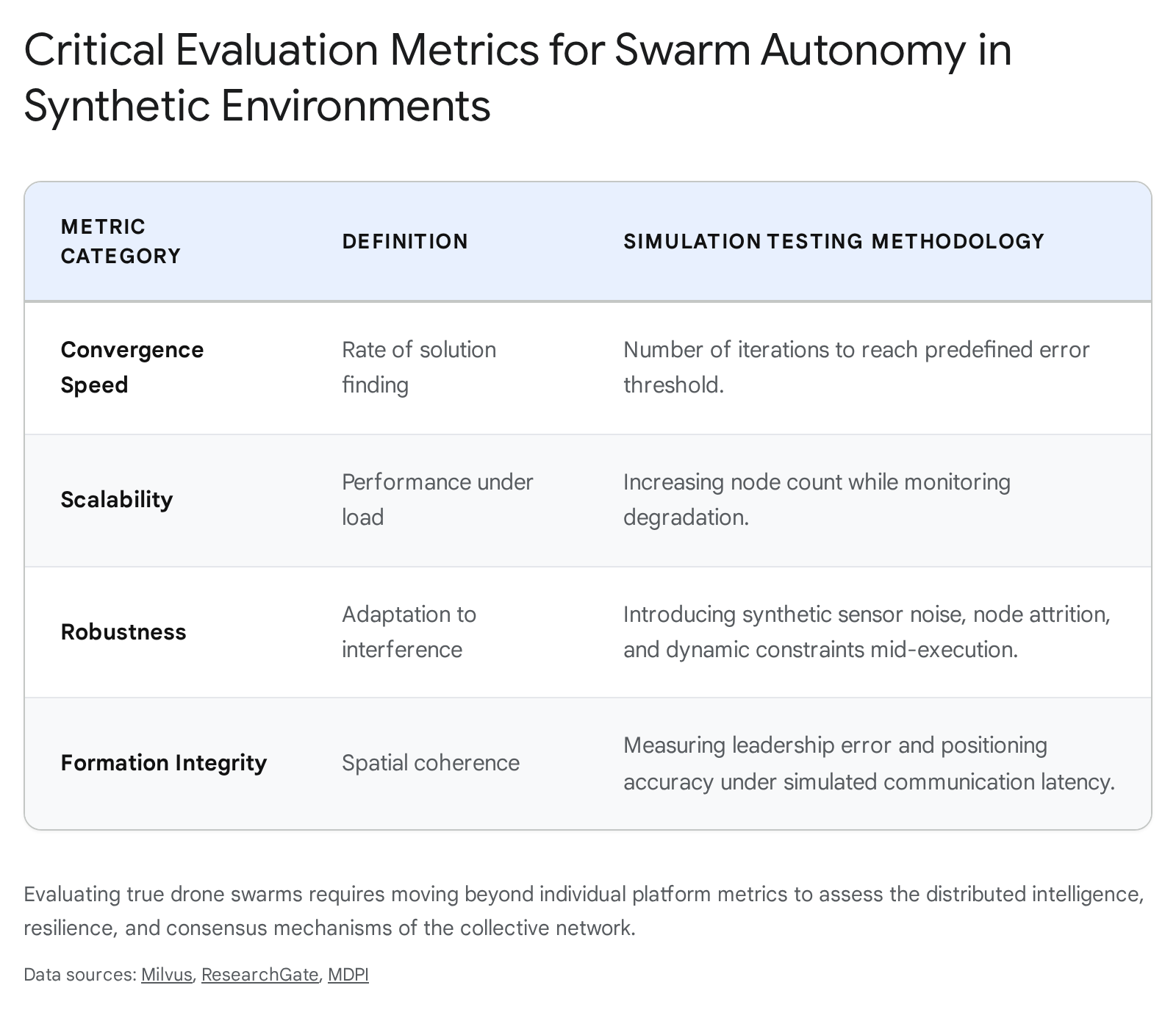
United States: Assessment of IonStrike Kinetic Interceptors The 52nd Air Defense Artillery Brigade (52d ADA BDE), an essential formation supporting U.S. Army Europe and Africa, significantly advanced its operational evaluation of the IonStrike counter-UAS interceptor system.15 Manufactured by DZYNE Technologies, the IonStrike is specifically engineered to serve as a highly scalable, mid-range kinetic layer positioned carefully between non-kinetic electronic warfare systems and high-cost, traditional missile interceptors.15
The technical architecture of the system leverages a highly precise terminal infrared seeker coupled with a proximity-fuzed warhead, allowing the interceptor to reliably detect and destroy one-way attack drones of varying sizes during both day and night operations.15 Crucially, IonStrike is designed to integrate seamlessly into existing Command and Control (C2) frameworks without requiring soldiers to learn a new operational sequence or “kill chain”.15 It connects directly to the Forward Area Air Defense (FAAD) System and the Integrated Battle Command System Maneuver (IBCS-M), allowing operators to cue the interceptors using existing, agnostic radar feeds.15 Unlike traditional fire-and-forget missiles that are permanently expended upon launch, the IonStrike features dynamic in-flight abort and retasking capabilities; if a target is deemed friendly or destroyed by other means, the operator can re-route the interceptor to a new threat, providing commanders with unprecedented flexibility when defending against complex drone swarms.15 The Army is currently testing a 4-interceptor launcher configuration, with active collaborative plans to expand to a 12-interceptor pallet to drastically increase magazine depth against larger raid profiles under the Eastern Flank Deterrence Initiative.15
United States: Integration of AEVEX Disruptor into Multi-Domain Formations During the highly complex Exercise Arcane Thunder 26, held at the National Training Center in Fort Irwin, California, the Multi-Domain Command – Europe (MDC-E) successfully integrated the AEVEX Disruptor unmanned system into their active combat training operations.44 Delivered rapidly by the Capability Program Executive Office Aviation and the Uncrewed Aircraft Systems Project Management Office, the modular architecture of the Disruptor platform significantly advances the Army’s long-range precision strike capabilities.44 The successful deployment of this system at Fort Irwin directly aligns with the Department of War’s overarching strategy for achieving “Drone Dominance” and multi-domain superiority in contested environments, proving that modular systems can be rapidly delivered and effectively utilized by conventional forces.44
May 22, 2026
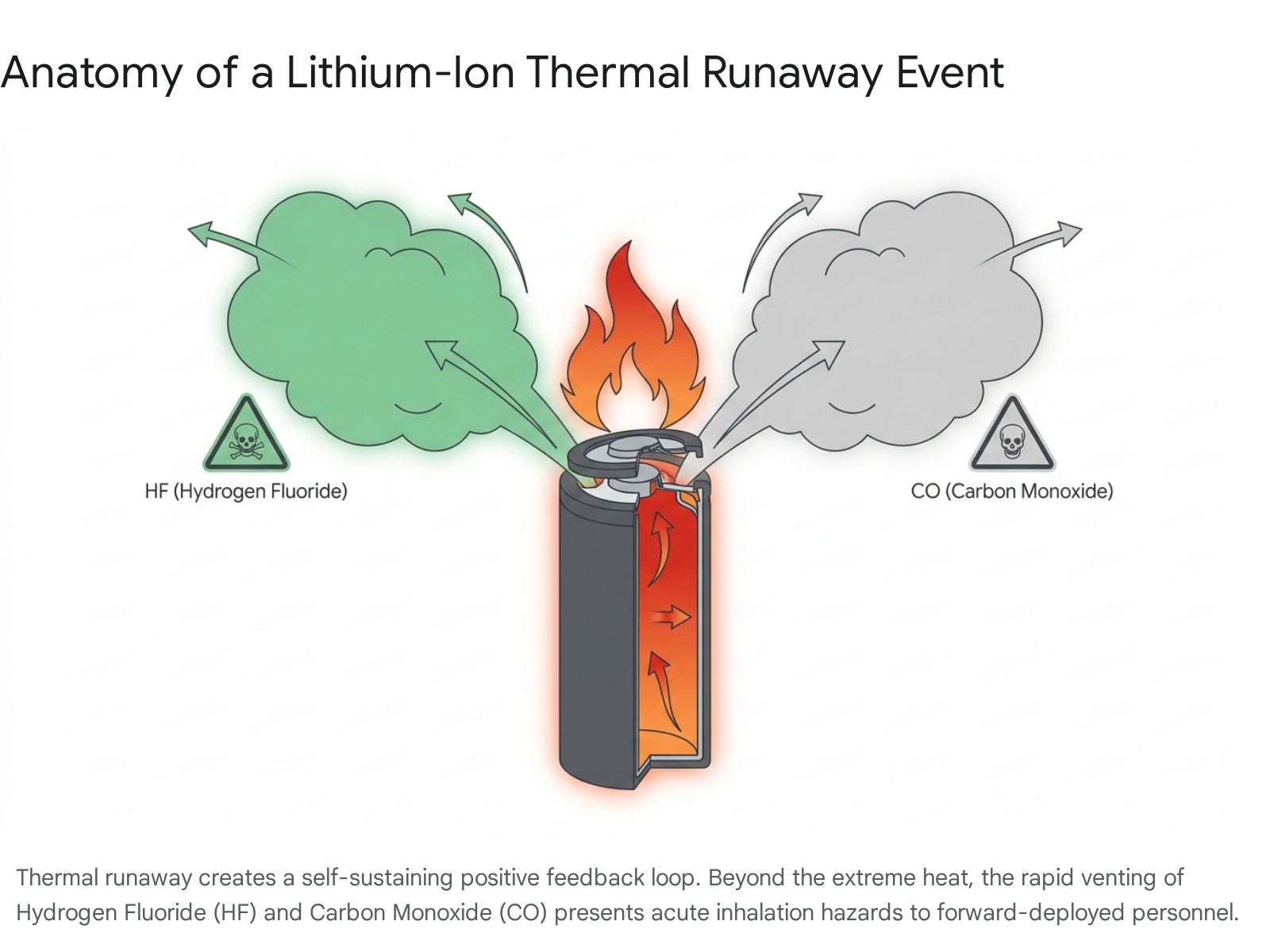
Turkey: Massive Naval Procurement and SAHA Expo Unveils Reflecting a massive, historic pivot toward asymmetric maritime warfare, the Turkish Defense Industry Executive Committee—the highest decision-making body in Turkey’s defense procurement policy—formally initiated the procurement of 100 expendable Unmanned Surface Vessels (USVs) designed explicitly for naval swarm attacks.13 These systems will be rapidly manufactured by a consortium of three domestic companies, overseen by the Secretariat of Defense Industries (SSB).13
This aggressive procurement follows the highly successful SAHA Expo 2026 in Istanbul, which generated a record business volume approaching $8 billion through 182 agreements, firmly cementing Turkey as a rising global military-tech power.46 During the expo, Turkish defense electronics giant Aselsan unveiled the TUFAN USV, a cutting-edge autonomous vessel equipped with advanced communication antennas and an electro-optics pod capable of alternating seamlessly between persistent ISR and one-way kinetic strike missions.47 Furthermore, Aselsan introduced the KILIC family of autonomous underwater strike systems (specifically highlighting the compact KILIC 10 and longer-range KILIC 200 variants).12 These highly stealthy UUVs are explicitly designed to detect, track, and unilaterally destroy high-value surface combatants and submarines without exposing crewed platforms to risk, severely complicating adversary naval defense planning in littoral chokepoints.12 Concurrently, UAV giant Baykar unveiled multiple new aerial one-way attack platforms, including the tube-launched Sivrisinek (Mosquito)—which features a 10-foot wingspan and can perform simultaneous reconnaissance and strike missions—and the next-generation K2 kamikaze drone.47
United States: Navy MUSV Prototype Selection The United States Navy formally selected seven industry submissions from its Medium Unmanned Surface Vessel (MUSV) marketplace to advance to the critical prototype evaluation phase.10 With over two dozen initial designs submitted when the marketplace launched in March, the down-selected firms (which notably include Saildrone and its new Spectre MUSV variants) must now conduct rigorous, highly scrutinized at-sea demonstrations prior to October 2026 to prove system maturity.10 The technical parameters mandated by the Navy are severe: the prototypes must be capable of carrying a 25-metric-ton load (equivalent to two 40-foot shipping containers) on the payload deck, and they must travel 2,500 nautical miles autonomously at a sustained speed of 25 knots in highly turbulent Sea State 4 conditions.10 Following successful demonstrations, the Navy plans to lease or procure these vessels in fiscal year 2027 to rapidly bolster fleet capacity and implement tailored, unmanned force packages.10
United States: Space Force Advances On-Orbit Autonomous Logistics The U.S. Space Force’s Space System Command (SSC) significantly accelerated its timeline for operationalizing unmanned on-orbit logistics, officially announcing concrete plans for two major orbital demonstrations in 2027.50 These missions will focus specifically on autonomous satellite refueling and augmented maneuver capabilities.50 Operating alongside SpaceWERX (the service’s innovation unit), SSC launched the $20 million “In-Domain Orbital Logistics Challenge”.50 The military is heavily investing in exotic technologies such as orbital warehousing, robotic transfer vehicles, in-space propellant management, and mechanics for reusability.50 The stated goal is to build a highly resilient logistics enterprise that feeds the entire space domain, moving away from single-use satellites toward an ecosystem of serviceable platforms, akin to the capabilities demonstrated by the secretive X-37B Boeing spaceplane.50 This effort mirrors a growing global arms race to develop “bodyguard satellites” and military spaceplanes capable of on-orbit inspection and protection, a capability currently being pursued by France, Germany, India, and Japan.53
United States: Teledyne FLIR Unveils Rogue 1 Block 2 At the premier Special Operations Forces (SOF) Week exposition in Tampa, Florida, Teledyne FLIR introduced the Block 2 variant of its Rogue 1 lethal unmanned aerial system (loitering munition).54 Leveraging two years of direct, intense operational feedback from deployments with the US Marine Corps Organic Precision Fires-Light program and USSOCOM, the electrically propelled quadrotor has undergone major upgrades.54 The Block 2 boasts double the effective range of its predecessor, now capable of striking targets over 20 kilometers (12.4 miles) away.54 Furthermore, it incorporates a highly specialized shape charge jet anti-armor payload designed specifically to neutralize hardened and armored vehicles, alongside advanced autonomy and highly robust EW-resilient communication suites, ensuring lethality in highly jammed environments.54
4. Strategic Lessons Learned
Note: The combined list of tactical, operational, and strategic lessons learned below is sorted strictly by date (chronologically) and then alphabetically by the primary country involved.
May 17, 2026
Israel: The Obsolescence of RF Counter-UAS and Shift to Kinetic Solutions The persistent and deadly success of Hezbollah’s fiber-optic FPV drone campaign has forced a rapid, highly public, and profoundly necessary strategic recalibration within the highest levels of the Israeli defense establishment.1 The primary, undeniable lesson learned from the recent casualties along the Lebanese border is that state-of-the-art Electronic Warfare (EW) is fundamentally impotent against physically tethered systems.1 A $300 commercial-off-the-shelf drone sourced cheaply from civilian internet marketplaces, when equipped with a 10-to-20-kilometer spool of fiber-optic cable, can securely transmit high-bandwidth video feeds and receive flight commands without any vulnerability whatsoever to signal jamming or spoofing.1
This stark physical reality has rendered multi-million-dollar defense systems insufficient and obsolete against this specific threat vector.1 Front-line IDF soldiers, lacking technological solutions, have been forced to rely on desperate, rudimentary interim measures, such as attempting to physically snag the fast-moving cables with scrap metal or deploying hundreds of thousands of square meters of physical chicken wire mesh over installations to entangle the drones before they detonate.1 Recognizing this severe, fatal capability gap, Prime Minister Benjamin Netanyahu formally authorized the creation of a specialized, fast-track task force armed with an “unlimited budget” to rapidly prototype and field localized kinetic and technological countermeasures.2 The strategic takeaway for global militaries is clear: software and signal dominance are insufficient; defensive networks must once again be backed by abundant, cheap physical hard-kill capabilities.
May 19, 2026
Estonia / NATO: The Escalation Trap of “EW Spillover” The unprecedented airspace incursions into NATO territory (specifically Estonia, Latvia, and Lithuania) yield a profound, highly concerning strategic lesson regarding the unintentional, chaotic ripple effects of modern, wide-area electronic warfare.7 Radar data and intelligence assessments definitively indicate that Ukraine is not intentionally targeting NATO airspace; rather, exceptionally powerful Russian EW installations, attempting to protect military targets, are successfully blinding the GPS and GLONASS navigation systems of long-range Ukrainian attack drones.7 Once blinded and disconnected from satellite guidance, these autonomous systems default to dead-reckoning inertial navigation or wander erratically, drifting unpredictably across international borders into sovereign NATO airspace.7
The paramount lesson learned is that indiscriminate EW creates an uncontrollable, physical escalation trap with severe geopolitical consequences. The spillover effect has already exacted a heavy political toll; most notably, Latvian Prime Minister Evika Siliņa was forced to formally resign after her coalition government collapsed entirely due to massive public anger over the military’s failure to swiftly intercept stray drones that eventually crashed into a domestic oil storage facility.7 The subsequent triggering of bunker protocols in Vilnius and the kinetic shoot-down of a drone by a Romanian F-16 over Estonia demonstrate that NATO can no longer rely solely on traditional anti-aircraft doctrines meant for manned bombers.7 Alliance members must rapidly develop and deploy highly localized, rapid-response air policing protocols specifically tailored for detecting, tracking, and safely neutralizing stray, erratic autonomous threats before they impact civilian infrastructure or trigger Article 5 level miscalculations.7
May 21, 2026
United States: Legislative Recognition of the Autonomous Paradigm Shift The formal introduction of the Unmanned Autonomous Systems Strategy Act by U.S. Senators Dave McCormick and John Fetterman reflects a crucial, bipartisan legislative realization that the current, legacy defense procurement model is dangerously slow and overly reliant on expensive, highly vulnerable crewed platforms.17 The strategic lesson driving this landmark legislation is the stark recognition that the United States cannot effectively maintain deterrence in the Indo-Pacific—nor can it secure the maritime corridors of the Western Hemisphere against transnational criminal organizations—against adversaries capable of mass-producing millions of autonomous systems annually.17
The legislation explicitly mandates that the Department of War develop a comprehensive, all-domain strategy to vastly accelerate the fielding of affordable, AI-enabled drones.17 It formally acknowledges at the highest levels of government that the era of relying solely on exquisite, multi-billion dollar platforms (such as aircraft carriers and advanced destroyers) to project power is ending.17 Future military force design must intimately incorporate persistent surveillance and long-range strike capabilities delivered at a fraction of the cost, aggressively utilizing a scalable commercial manufacturing base to offset adversary advantages in mass and localized area denial.17
May 22, 2026
Taiwan: The Cost-Attrition Paradox in Island Air Defense Deep strategic assessments regarding Taiwan’s current air defense posture highlight a crippling, mathematically unsolvable cost-attrition paradox when facing potential massed autonomous swarms from the People’s Liberation Army (PLA).14 Taiwan’s meticulously planned multilayered air-defense network, colloquially known as “T-Dome,” is entirely financially unviable against a dedicated, sustained drone assault utilizing cheap commercial technology.14
The lesson is purely mathematical and highly concerning for island defense planners: Taiwan’s most cost-effective interceptor, the domestically produced Sky Bow (Tien Kung-3), costs approximately $600,000 per unit, while the highly advanced U.S.-supplied Patriot PAC-3 missiles cost over $3.7 million each.14 In stark contrast, China is demonstrating the immediate capability to launch massive autonomous swarms, including incredibly inexpensive Shahed-style loitering munitions (costing roughly $20,000 each) and highly creative J-6W drones—which are legacy J-6 fighter jets stripped of life support and converted into uncrewed, heavily armed cruise missiles designed to absorb interceptors.14 Utilizing advanced command systems like the Atlas (Swarm-2) operations vehicle, China could rapidly and efficiently overwhelm Taiwanese interceptor stockpiles in a matter of days.14 The ultimate lesson learned is that firing a $3 million interceptor at a $20,000 drone results in an unsustainable 150:1 cost exchange ratio, virtually guaranteeing fiscal and material exhaustion long before the adversary runs out of cheap munitions. To survive, Taiwan must rapidly pivot away from high-end missiles toward developing its own massive domestic, low-cost drone manufacturing base and scalable kinetic interceptors (conceptually akin to the U.S. Army’s IonStrike) to balance the equation.14
United States: Re-Purposing Legacy Aviation as Airborne Command Nodes In a vivid, highly successful demonstration of tactical adaptation and ingenuity, the U.S. Marine Corps recently tested a novel operational concept by actively utilizing a legacy UH-1Y Venom utility helicopter as an airborne command and control node for launching and directing low-cost Neros Archer FPV strike drones.14
The operational lesson learned from this exercise is that to survive against modern, highly integrated air defense systems, human operators and expensive, vulnerable crewed platforms must remain far outside the enemy’s maximum weapons engagement zone (WEZ).58 By launching the modular FPV drones safely from the ground and instantly transferring control to operators orbiting miles away in a helicopter acting as a high-altitude signal relay, the Marine Corps effectively and cheaply extends the reach, situational awareness, and lethality of expendable munitions.18 This tactic seamlessly integrates the harsh lessons learned from the brutal trench warfare in Ukraine into conventional, highly mobile, distributed maritime operations.57 It conclusively proves that minor software upgrades and aggressive tactical creativity can dramatically extend the relevance, survivability, and lethality of older manned platforms in a drone-dominated airspace.57
Table 2: Cost-Attrition Threat Matrix (Air Defense Interceptor vs. Autonomous Threat)
This matrix details the unsustainable economic disparities driving the urgent need for low-cost kinetic interceptors across global theaters.
| Defense Platform / Interceptor | Approx. Unit Cost (USD) | Primary Target / Autonomous Threat | Approx. Target Cost (USD) | Cost Exchange Ratio | Operational Implication |
| Patriot PAC-3 Missile (Taiwan/US) | $3,700,000 | Converted J-6W / Large Strike Drone | $100,000 | 37:1 | High risk of rapid interceptor depletion; financially unsustainable against mass swarms. |
| Tien Kung-3 Missile (Taiwan) | $600,000 | Shahed-136 / Geran-2 Loitering Munition | $20,000 | 30:1 | Guaranteed exhaustion of domestic stockpiles within days of a sustained swarm assault. |
| IonStrike Interceptor (US Army) | Classified (Sub-$20k) | Group 1-3 One-Way Attack Drones | $5,000 – $20,000 | < 1:1 | Highly favorable. Preserves high-end effectors; allows for scalable, deep magazine defense. |
| Iron Dome Tamir Interceptor (Israel) | $50,000 | Hezbollah Fiber-Optic FPV Drone | $300 | 166:1 | Catastrophic cost ratio. Physical fiber tether renders EW useless, forcing highly inefficient kinetic intercepts. |
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Works cited
- Israeli gov’t allocates NIS 2b. to combat Hezbollah drones, accessed May 23, 2026, https://www.jpost.com/defense-and-tech/article-896628
- ‘Unjammable’ Drones Pioneered In Ukraine Emerge In Middle East War, accessed May 23, 2026, https://www.rferl.org/a/israel-iran-fiber-optic-drones-russia-ukraine-war/33761841.html
- Lebanon-Israel talks: diplomacy under bombs, accessed May 23, 2026, https://en.majalla.com/node/331161/politics/lebanon-israel-talks-diplomacy-under-bombs
- Iran’s Drone Strategy (Part 2): Preventing Postwar Rebuilding and Advancements, accessed May 23, 2026, https://www.washingtoninstitute.org/policy-analysis/irans-drone-strategy-part-2-preventing-postwar-rebuilding-and-advancements
- Why Hezbollah’s Use of FPV Drones Against Israel Will Backfire – FDD, accessed May 23, 2026, https://www.fdd.org/analysis/2026/05/18/why-hezbollahs-use-of-fpv-drones-against-israel-will-backfire/
- Defense Ministry presented with solutions for fiber optic explosive drones | The Jerusalem Post, accessed May 23, 2026, https://www.jpost.com/israel-news/defense-news/article-896927
- Lithuanian leaders rushed to bunkers as drone violates country’s …, accessed May 23, 2026, https://www.theguardian.com/world/2026/may/20/lithuania-vilnius-drone-alert-leaders-bunkers
- NATO jets scrambled, Lithuanian leaders moved to safe location after Ukraine war drone detected, accessed May 23, 2026, https://www.cbc.ca/news/world/lithuania-ukraine-russia-war-drone-incident-9.7205544
- NATO jet shoots down Ukrainian drone over Estonia in escalation of airspace violations, accessed May 23, 2026, https://www.defensenews.com/global/europe/2026/05/19/nato-jet-shoots-down-ukrainian-drone-over-estonia-in-escalation-of-airspace-violations/
- Navy green lights seven MUSV marketplace submissions to …, accessed May 23, 2026, https://breakingdefense.com/2026/05/navy-green-lights-seven-musv-marketplace-submissions-to-advance-to-prototype-phase/
- The Navy Needs Precise Mass and Here Is How to Get There, accessed May 23, 2026, https://warontherocks.com/the-navy-needs-precise-mass-and-here-is-how-to-get-there/
- New Turkish Autonomous Underwater Strike Systems Could Challenge Traditional Naval Defenses, accessed May 23, 2026, https://www.armyrecognition.com/news/navy-news/2026/new-turkish-autonomous-underwater-strike-systems-could-challenge-traditional-naval-defenses
- Turkey to buy 100 one-way explosive naval drones for swarm attacks, accessed May 23, 2026, https://www.defensenews.com/global/europe/2026/05/21/turkey-to-buy-100-one-way-explosive-naval-drones-for-swarm-attacks/
- A Cost Too High to Protect the Sky? Lessons for Taiwan from the …, accessed May 23, 2026, https://globaltaiwan.org/2026/05/a-cost-too-high-to-protect-the-sky/
- News – Army Air Defenders assess IonStrike interceptors to … – DVIDS, accessed May 23, 2026, https://www.dvidshub.net/news/566032/army-air-defenders-assess-ionstrike-interceptors-support-eastern-flank-deterrence-initiative
- 52d ADA BDE assesses IonStrike interceptors to support EFDI, accessed May 23, 2026, https://www.army.mil/article/292769/52d_ada_bde_assesses_ionstrike_interceptors_to_support_efdi
- PENNSYLVANIA SENATORS MCCORMICK AND FETTERMAN INTRODUCE BILL TO ACCELERATEU.S. MILITARY DRONE AND AUTONOMOUS SYSTEMS STRATEGY, accessed May 23, 2026, https://www.mccormick.senate.gov/news/press-releases/pennsylvania-senators-mccormick-and-fetterman-introduce-bill-to-accelerateu-s-military-drone-and-autonomous-systems-strategy/
- US Marine Corps tests using helicopter as mobile drone command …, accessed May 23, 2026, https://www.marinecorpstimes.com/news/your-marine-corps/2026/05/22/us-marine-corps-tests-using-helicopter-as-mobile-drone-command-center/
- Drone attack starts fire at UAE nuclear power plant | PBS News, accessed May 23, 2026, https://www.pbs.org/newshour/world/drone-attack-starts-fire-at-uae-nuclear-power-plant
- Drone strike causes fire at UAE’s Barakah nuclear power plant in Abu Dhabi, accessed May 23, 2026, https://www.hindustantimes.com/world-news/drone-strike-causes-fire-at-uae-barakah-nuclear-power-plant-in-abu-dhabi-us-iran-war-101779013182458.html
- UAE investigates source of drones after ‘treacherous terrorist attack’ on Barakah plant, accessed May 23, 2026, https://www.thenationalnews.com/news/uae/2026/05/17/uae-launches-investigation-into-source-of-drone-strike-on-barakah-nuclear-plant/
- UAE says drone strike caused fire at nuclear plant, accessed May 23, 2026, https://www.ft.com/content/c4b786a6-55d4-4689-b19e-48a48f7946e6?syn-25a6b1a6=1
- Drone strike sparks fire near UAE nuclear plant, no radiation leak reported, accessed May 23, 2026, https://www.indiatoday.in/world/story/uae-barakah-nuclear-plant-drone-strike-fire-iran-conflict-talks-stall-2913093-2026-05-17
- Drone Hits UAE Nuclear Power Plant | Barakah Attack Explained | Who’s Behind It? | N18S, accessed May 23, 2026, https://www.youtube.com/shorts/SvJF9lUm0WI
- Drone strikes UAE nuclear plant as US and Iran signal they are prepared to resume war, accessed May 23, 2026, https://apnews.com/article/iran-us-uae-nuclear-drones-71e7e58f45193b7dee3df28740532a7b
- Russia labels Ukraine attack in occupied Luhansk ‘monstrous crime’ – Al Jazeera, accessed May 23, 2026, https://www.aljazeera.com/news/2026/5/22/russia-labels-ukraine-attack-in-occupied-luhansk-monstrous-crime
- Drone Strike Destroys FSB Headquarters with Dozens of Invaders on the Arabat Spit, accessed May 23, 2026, https://militarnyi.com/en/news/drone-strike-destroys-fsb-hq-arabat-spit/
- U.S. Navy Launches High-Tech Unmanned Systems During Bilateral Exercise with Norway, accessed May 23, 2026, https://www.navy.mil/Press-Office/News-Stories/display-news/Article/4494567/us-navy-launches-high-tech-unmanned-systems-during-bilateral-exercise-with-norw/
- US Navy tests high-tech maritime drones off northern Norway, accessed May 23, 2026, https://www.arctictoday.com/u-s-navy-tests-high-tech-maritime-drones-off-northern-norway/
- Yemen’s Houthis Attack Trump’s Surveillance Reaper Drone, Report Says | Vantage on Firstpost | 4K – YouTube, accessed May 23, 2026, https://www.youtube.com/watch?v=iBnK02zJmuc
- U.S. MQ-9 Reaper drone downed in Yemen: Iranian media – Xinhua, accessed May 23, 2026, https://english.news.cn/20260518/7ff643531e3a4e09817e9e962b79748c/c.html
- Monday 18 May 2026: USAF MQ-9A Reaper drone shot down, post-crash piccies…. – Scramble Messageboard, accessed May 23, 2026, http://scramble.nl/forum/viewtopic.php?p=1140533&sid=638cf794f0b6f699b4833dd04f941124
- U.S. Loses 51st MQ-9 Drone in Clashes with Yemeni and Iranian Forces, accessed May 23, 2026, https://militarywatchmagazine.com/article/us-loses-51st-mq9-drone-yemen
- NATO Says Ready for All Scenarios After Drone Incursions in Baltic Region, accessed May 23, 2026, https://www.youtube.com/watch?v=aVi6B-fuDAI
- Russian Offensive Campaign Assessment, May 21, 2026, accessed May 23, 2026, https://understandingwar.org/research/russia-ukraine/russian-offensive-campaign-assessment-may-21-2026/
- Drone incursions in Baltic states: how to respond?, accessed May 23, 2026, https://www.eurotopics.net/en/358111/drone-incursions-in-baltic-states-how-to-respond
- Russian Offensive Campaign Assessment, May 22, 2026 | ISW, accessed May 23, 2026, https://understandingwar.org/research/russia-ukraine/russian-offensive-campaign-assessment-may-22-2026/
- Ukraine war briefing: Oil plant strikes all going to plan, says Zelenskyy, accessed May 23, 2026, https://www.theguardian.com/world/2026/may/22/ukraine-war-briefing-oil-plant-strikes-all-going-to-plan-says-zelenskyy
- Ukraine Downs 102 of 124 Russian Drones in Overnight Attack, accessed May 23, 2026, https://odessa-journal.com/ukraine-neutralizes-102-of-124-russian-drones-in-overnight-attack
- U.S. Marines at Camp Lejeune Field Test UGV Technology [Image 8 of 8] – DVIDS, accessed May 23, 2026, https://www.dvidshub.net/image/9702685/us-marines-camp-lejeune-field-test-ugv-technology
- AM General is Driving Innovation at AUSA Global Force 2026 with Unmanned Ground Vehicle Debut, accessed May 23, 2026, https://www.amgeneral.com/am-general-is-driving-innovation-at-ausa-global-force-2026-with-unmanned-ground-vehicle-debut/
- The Race to Keep Military Drones Powered Just Took a Major Step Forward, accessed May 23, 2026, https://www.streetwisereports.com/article/2026/05/22/the-race-to-keep-military-drones-powered-just-took-a-major-step-forward.html
- 52d ADA BDE assesses IonStrike interceptors to support EFDI – U.S. Army, accessed May 23, 2026, https://www.army.mil/article-amp/292769/52d_ada_bde_assesses_ionstrike_interceptors_to_support_efdi
- The U.S. Army Integrates AEVEX Disruptor During Exercise Arcane Thunder 26, accessed May 23, 2026, https://www.army.mil/article/292698/the_u_s_army_integrates_aevex_disruptor_during_exercise_arcane_thunder_26
- Turkey to buy 100 one-way explosive naval drones for swarm attacks – OODAloop, accessed May 23, 2026, https://oodaloop.com/briefs/arms-trade/turkey-to-buy-100-one-way-explosive-naval-drones-for-swarm-attacks/
- From drones to underwater warfare: Inside SAHA 2026; Türkiye’s $8B defense surge, accessed May 23, 2026, https://www.muslimnetwork.tv/from-drones-to-underwater-warfare-inside-saha-2026-turkiyes-8b-defense-surge/
- One-way attack drones under the spotlight at SAHA 2026 – Breaking Defense, accessed May 23, 2026, https://breakingdefense.com/2026/05/one-way-attack-drones-under-the-spotlight-at-saha-2026/
- Baykar unveils K2, Mizrak and Sivrisinek kamikaze swarm systems at SAHA 2026, accessed May 23, 2026, https://www.turkiyetoday.com/nation/drone-giant-baykar-unveils-k2-mizrak-and-sivrisinek-at-saha-2026-3219547
- Türkiye’s Baykar unveils next-gen drones – TRT World, accessed May 23, 2026, https://www.trtworld.com/article/0e85c26ddf80
- Space Force accelerating work to operationalize on-orbit logistics tech | DefenseScoop, accessed May 23, 2026, https://defensescoop.com/2026/05/22/space-force-accelerating-work-to-operationalize-on-orbit-logistics-tech/
- X-37B – Boeing, accessed May 23, 2026, https://www.boeing.com/space/x37b
- Boeing X-37 – Wikipedia, accessed May 23, 2026, https://en.wikipedia.org/wiki/Boeing_X-37
- ‘Everyone wants a spaceplane’: More countries eye on-orbit protection for satellites – Defense One, accessed May 23, 2026, https://www.defenseone.com/defense-systems/2026/04/everyone-wants-spaceplane-more-countries-eye-orbit-protection-satellites/412773/
- Loitering munitions, launched effects had strong presence at SOF Week 2026, accessed May 23, 2026, https://breakingdefense.com/2026/05/loitering-munitions-launched-effects-had-strong-presence-at-sof-week-2026/
- At least four people killed in Russia as Ukraine launches retaliatory strikes, accessed May 23, 2026, https://www.theguardian.com/world/2026/may/17/people-killed-in-russia-ukraine-retaliatory-strikes-moscow
- China & Taiwan Update, May 22, 2026 | ISW, accessed May 23, 2026, https://understandingwar.org/research/china-taiwan/china-taiwan-update-may-22-2026/
- Marines Turn UH-1Y Venom Into an Airborne Drone Command Post, accessed May 23, 2026, https://www.sofx.com/marines-turn-uh-1y-venom-into-an-airborne-drone-command-post/
- US Marines’ UH-1Y Venom helicopter takes control of Neros Archer FPV drones in breakthrough test : r/WorldDefenseNews – Reddit, accessed May 23, 2026, https://www.reddit.com/r/WorldDefenseNews/comments/1tje659/us_marines_uh1y_venom_helicopter_takes_control_of/
- U.S. Marines Turn UH-1 Helicopter Into a Flying Drone Command Post | RealClearDefense, accessed May 23, 2026, https://www.realcleardefense.com/2026/05/22/us_marines_turn_uh-1_helicopter_into_a_flying_drone_command_post_1184214.html
- H-1s Become Drone Control Platforms – DVIDS, accessed May 23, 2026, https://www.dvidshub.net/news/565824/h-1s-become-drone-control-platforms