1. Executive Summary
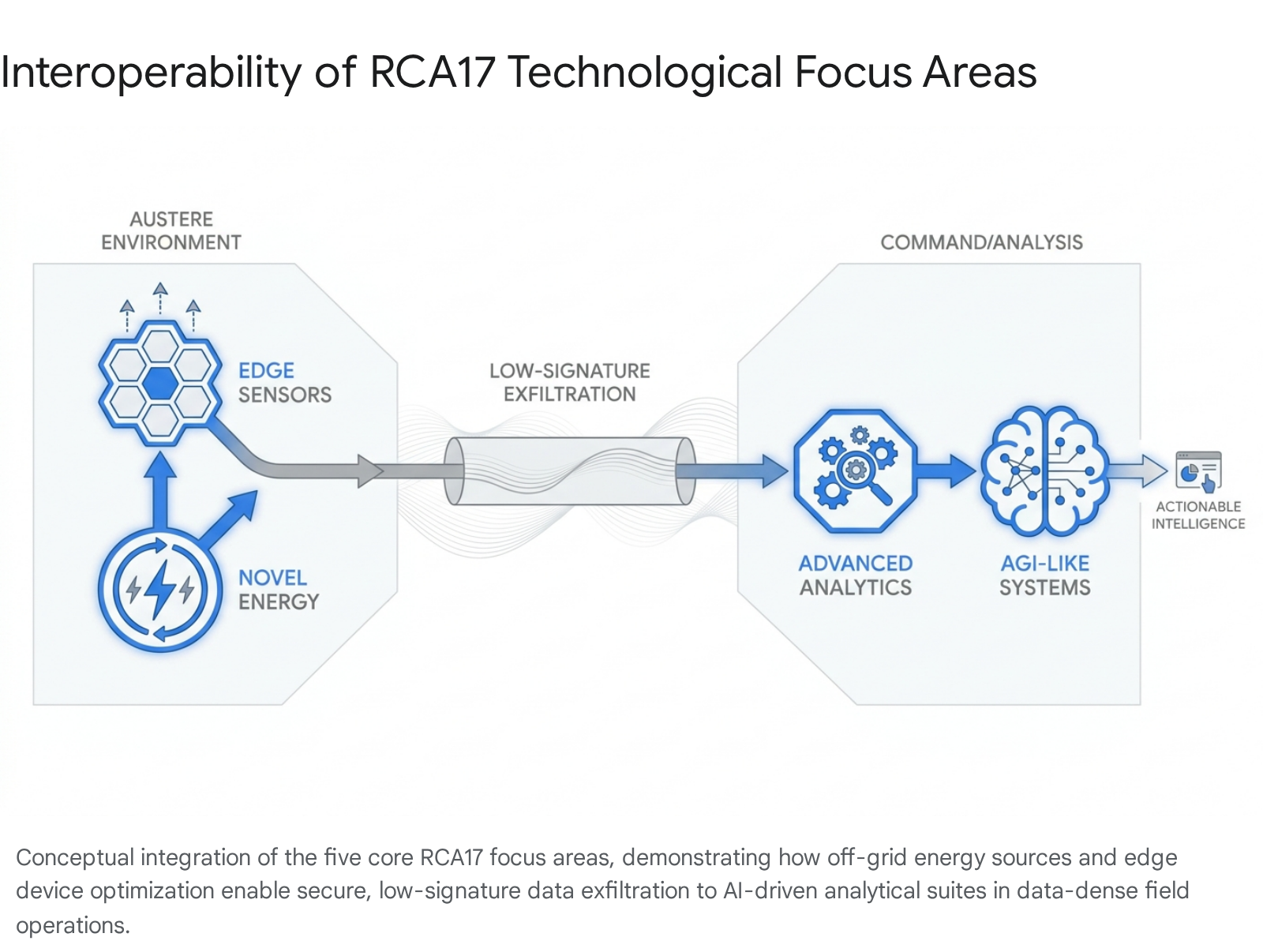
The United States Department of Defense (DoD) is undertaking a profound structural transition in force design, characterized by rapid, massive investments in scaled autonomous systems. Initiatives such as the Replicator program, which seeks to field thousands of all-domain attritable autonomous (ADA2) systems by late 2025, alongside recent executive directives intended to unleash domestic drone manufacturing, indicate a strategic pivot toward mass and numerical advantage.1 However, current strategic dialogues and procurement focuses heavily favor the acquisition of physical airframes, payloads, and autonomous navigation software, while the systemic requirements—specifically the invisible architecture of the electromagnetic spectrum (EMS)—remain critically underexamined.3
Operating thousands of uncrewed systems simultaneously generates extreme bandwidth limitations, heightens the risk of friendly electromagnetic interference (blue-on-blue EMI), and creates severe vulnerabilities to adversarial electronic warfare (EW).3 The historical reliance on clear, centralized communication lines is a fundamental vulnerability in contested environments.5 To successfully enable warfighters and employ drones effectively, DoD leadership must shift its conceptual framework from viewing the EMS as a passive, guaranteed utility to recognizing it as a highly contested, primary maneuver space.5
This strategic report provides an exhaustive overview of the systemic requirements necessary to design, build, operate, and evolve scaled drone architectures. It outlines the limitations of current bandwidth allocations, details the adversarial electronic warfare threat landscape based on recent combat observations in theaters such as Ukraine, and provides an actionable framework for operational resilience.7 The accumulated evidence suggests that operational viability in contested environments requires abandoning centralized “mothership” command structures in favor of decentralized, self-healing mesh networks.10 Furthermore, forces must push computational processing to the tactical edge to drastically reduce bandwidth dependencies and adopt software-defined, modular open systems architectures (MOSA) to enable real-time frequency agility and stealth communications.12
2. The Strategic Imperative: The Electromagnetic Spectrum as a Primary Maneuver Space
For decades, military communications architectures were conceptualized and built around the fundamental assumption that spectrum access could be predicted, allocated, and largely preserved through operational planning.5 Frequency plans, static allocations, and pre-mission deconfliction procedures functioned effectively in environments where spectrum access remained orderly and enforceable by allied forces.5 That operational context no longer exists. Contemporary military deployments unfold amid dense, unpredictable, and overlapping radio frequency (RF) emissions stemming from military, commercial, and civilian activities.5
2.1. The Shift to Electromagnetic Spectrum Operations (EMSO)
Strategic competitors and adversaries have thoroughly observed the deep reliance of United States forces on EMS-dependent capabilities and have actively structured their forces to exploit this specific vulnerability.15 Consequently, without control or resilience within the EMS, precision capabilities degrade, joint operations falter, and broader deterrence erodes.15 Recognizing this paradigm shift, the DoD formalized a new reality in its 2020 Electromagnetic Spectrum Superiority Strategy. This document marked a transition from the traditional concept of electronic warfare (EW)—often viewed as a secondary or supporting capability—into the broader, unified framework of Electromagnetic Spectrum Operations (EMSO).17
Despite this critical doctrinal shift, execution and bureaucratic alignment have historically lagged. Assessments by the Government Accountability Office (GAO) have noted that the Department risks failing to achieve its spectrum strategy goals due to a lack of clearly identified processes, reformed governance structures, and assigned leadership for strategy implementation.18 Accountability mechanisms and oversight processes required to integrate spectrum operations across the joint force must be accelerated to match the pace of physical drone acquisition.18
2.2. Domestic Spectrum Scarcity and Commercial Contention
Compounding the tactical threat is a broader, systemic issue of spectrum scarcity. Spectrum is a finite national and international resource. Treaties and international agreements govern global allocations, making it exceedingly difficult to acquire new spectrum permanently for military use.3 Domestically, significant portions of the bandwidth previously reserved for the exclusive use of the DoD have been auctioned to private entities over the past decade to form the foundation of commercial 4G and 5G cellular networks.20
This commercial sell-off restricts the DoD’s freedom of action and means that large-scale drone deployments cannot simply be assigned dedicated, pristine frequencies.17 Furthermore, many systems are acquired as Commercial Off-The-Shelf (COTS) products tested using U.S. commercial spectrum; when transitioned to military use, these systems often face priority conflicts or are prohibited from use outside the United States unless transferred to military-use spectrum.3 Future operations therefore demand dynamic spectrum sharing and cognitive technologies that allow military systems to coexist within congested commercial and contested tactical bands.20 The DoD’s Office of the Chief Information Officer and the FutureG office are actively exploring dynamic spectrum-sharing demonstrations to allow the Pentagon and private sector to simultaneously utilize the same spectrum bands without degradation.21
3. The Ambition and Reality of Scaled Autonomous Systems
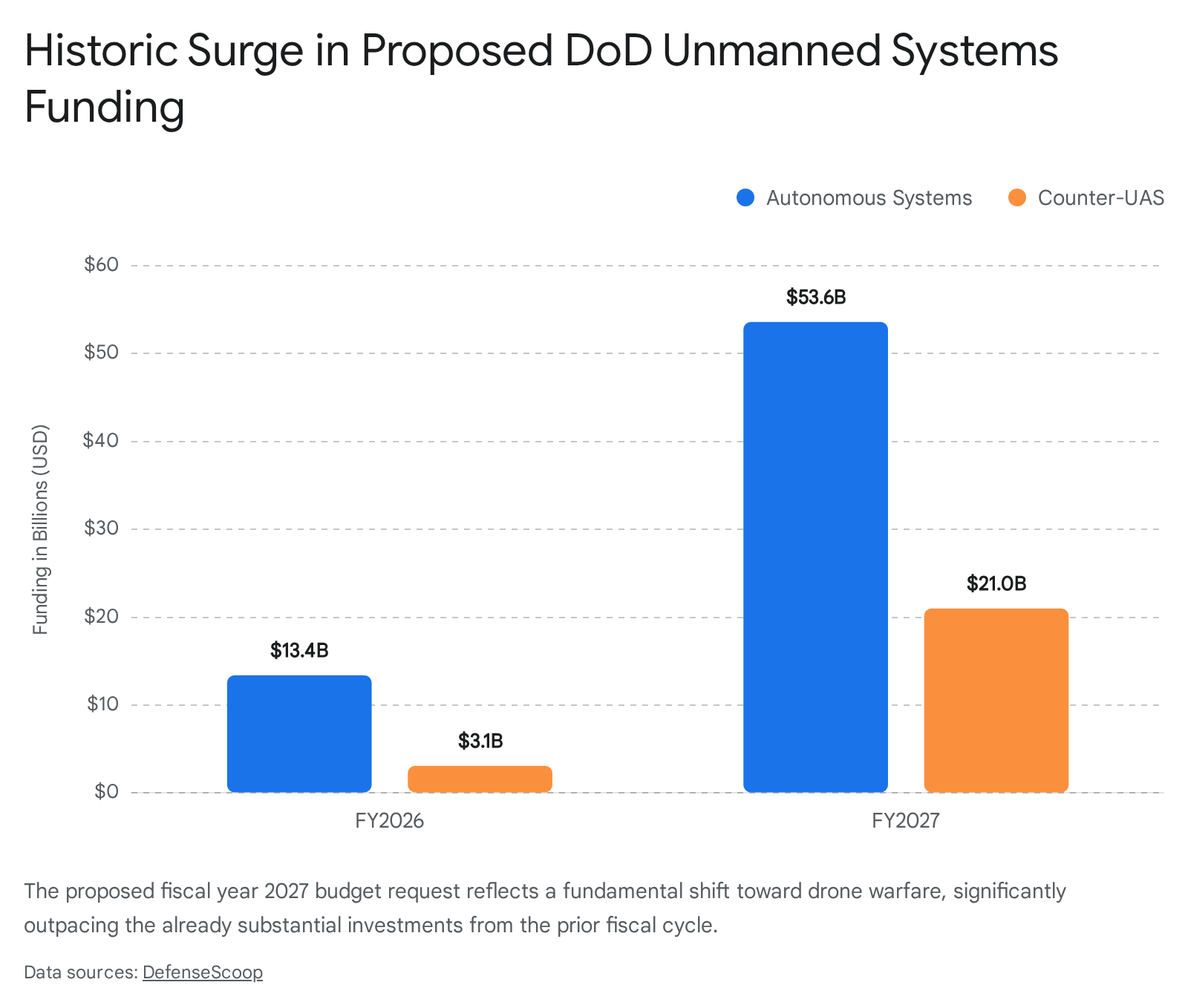
The DoD’s current acquisition trajectory reflects an urgent drive to overcome the numerical advantages of adversaries through the mass deployment of uncrewed systems. However, a significant disconnect exists between the procurement of these physical assets and the maturation of the networks required to sustain them.
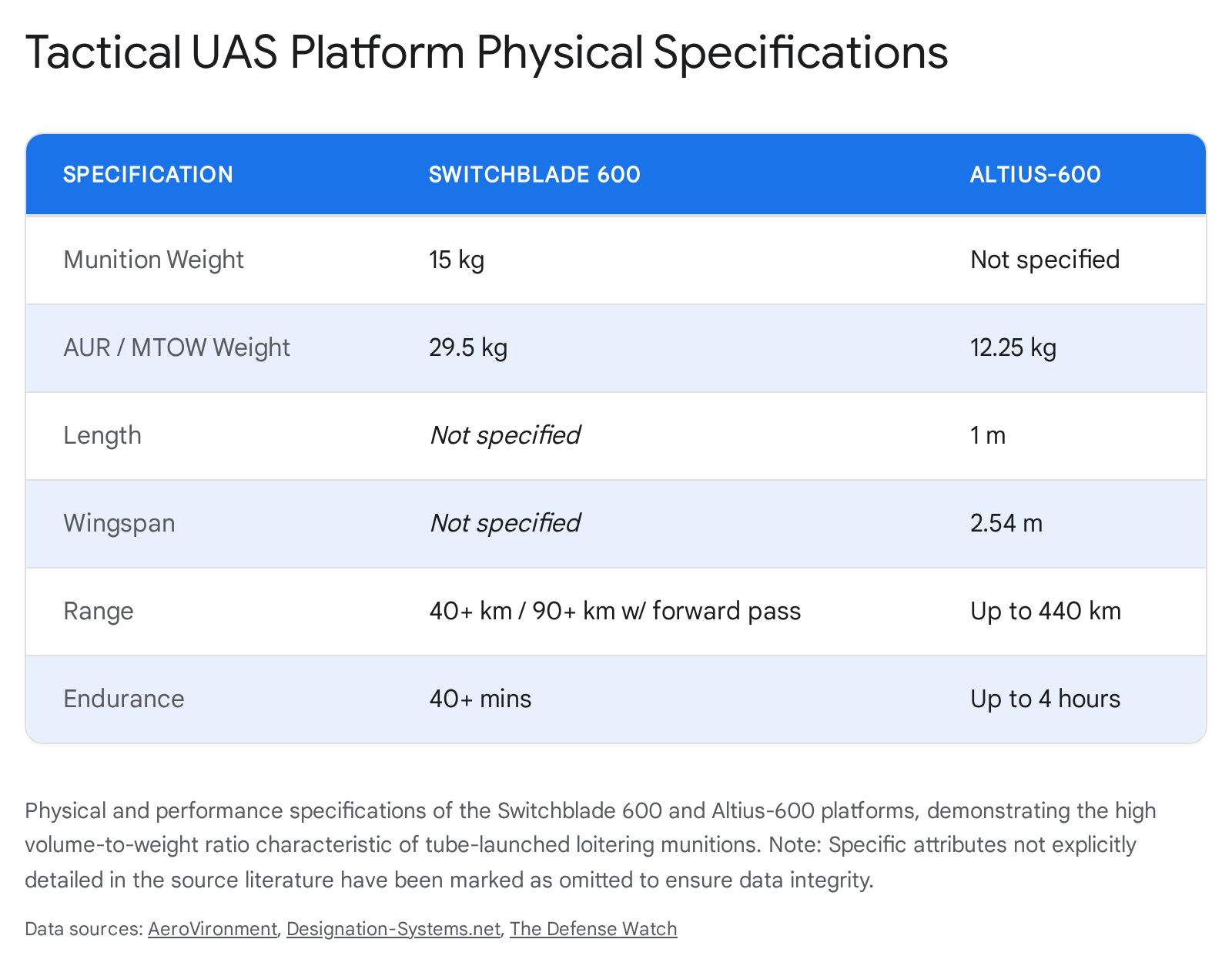
3.1. The Replicator Initiative and ADA2
Launched to counter the mass of the Chinese military, the Replicator Initiative represents a high-profile effort to rapidly field thousands of autonomous systems across multiple domains within an aggressive timeline.1 Managed by the Defense Innovation Unit (DIU), Replicator bypasses traditional acquisition programs to accelerate the fielding of all-domain attritable autonomy (ADA2).1 These are low-cost, expendable platforms designed to be lost in combat.1 Replicator 1 focuses on fielding thousands of uncrewed aerial, ground, maritime, and space-based systems by August 2025, while Replicator 2 targets counter-small unmanned aerial systems (C-sUAS).1
While the strategic intent is clear, the initiative faces scrutiny regarding technological integration. Congressional Research Service (CRS) analyses have raised oversight concerns framing Replicator as a test case for future defense innovation, warning that accelerated fielding may pose risks to system reliability, interoperability, and long-term sustainment.1 Crucially, the initiative’s success relies heavily on unnamed software vendors tasked with enabling swarming, autonomous navigation, and dynamic threat response—all of which require a robust, resilient electromagnetic backbone.1
3.2. Executive Directives and the Procurement Drive
The push for mass has been further codified by recent executive actions. Executive Order 14307, issued to support the American drone industry and arm warfighters, mandates that the DoD must be able to procure, integrate, and train using low-cost, high-performing drones manufactured domestically.2 Follow-on memorandums from DoD leadership have emphasized “Unleashing U.S. Military Drone Dominance,” rescinding restrictive policies to power a technological leapfrog.2
This directive acknowledges that adversaries collectively produce millions of cheap drones annually, and U.S. units must be outfitted with lethal small drones.2 However, as procurement scales rapidly, the systemic infrastructure must scale concurrently. Building millions of drones yields no tactical advantage if they cannot communicate, coordinate, or survive in a contested electromagnetic environment. The focus must expand from simply acquiring platforms to establishing the network architectures that make those platforms lethal and survivable.5
4. Physical and Infrastructural Vulnerabilities of Mass Operations
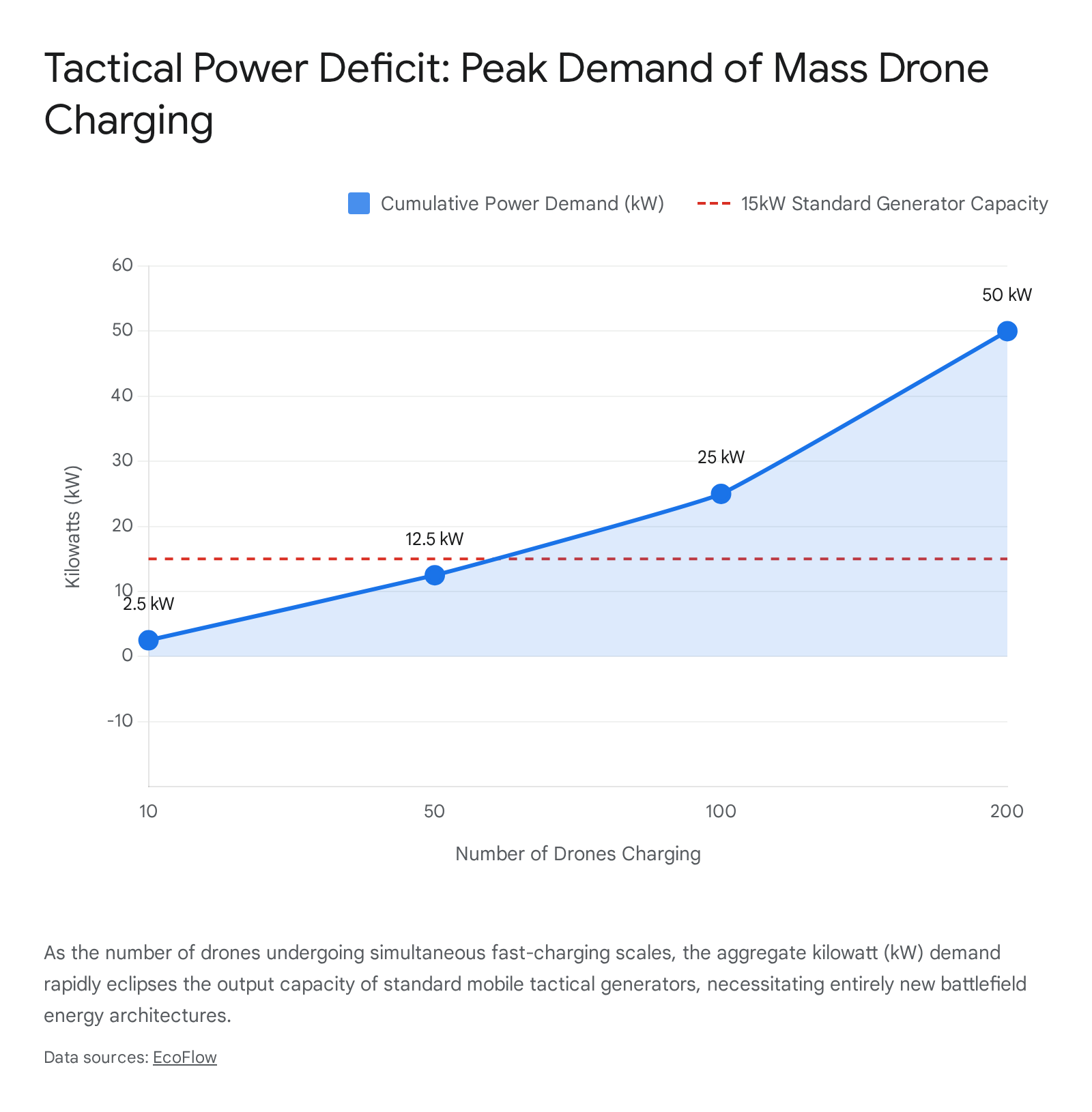
The ambition to field thousands of autonomous systems introduces immediate physical and infrastructural limitations. Leadership must recognize the nonlinear complexity that arises when scaling from single-drone operations to coordinated swarms. The primary constraints are bandwidth saturation, signal latency, and internal electromagnetic interference.
4.1. Bandwidth Saturation and Latency Constraints
Uncrewed Aircraft Systems rely heavily on datalinks for command and control (C2), telemetry, and the transmission of sensor payloads. As the density of drones increases within a given airspace, the demand for spectrum rapidly outpaces availability.3 High-fidelity sensors designed for intelligence, surveillance, and reconnaissance (ISR) or target acquisition generate massive, continuous data streams.3 In recent tactical counter-UAS exercises, such as Project Flytrap in Germany, single U.S. Army platoons found that 70 percent of their available tactical bandwidth was consumed entirely by sensor data alone.23
Beyond Visual Line of Sight (BVLOS) operations, which are essential for long-range missions and deep strikes, compound this communication challenge.24 Drones operating at extended ranges face severe signal attenuation—often exceeding 120 decibels at distances beyond 50 kilometers.25 To maintain connectivity, systems frequently rely on satellite communications (SATCOM). While SATCOM offers global coverage and bypasses local terrestrial obstacles, it introduces substantial propagation delays, with latency ranging from 500 milliseconds to over a full second.24 In the context of high-speed drone swarms, autonomous coordination, and kinetic fire control, milliseconds matter.23 High latency can cripple real-time swarm coordination and render rapid targeting impossible.
4.2. Blue-on-Blue Electromagnetic Interference (EMI)
When thousands of electronic devices operate in close proximity, they generate significant RF noise, leading to internal or “blue-on-blue” electromagnetic interference.26 Failure to properly shield and coordinate drones can result in disrupted flight controls, severed communication links, and mid-mission platform failure without any enemy action.28
Internal EMI in swarms stems from multiple sources. Propulsion system electrical noise, the physical overlap of wireless modules, and the proximity of unshielded cables all contribute to a chaotic internal electromagnetic environment.4 As the swarm scales, coordination complexity increases non-linearly. Field tests demonstrate that communication latency between drones can spike, and positioning errors can accumulate rapidly—at rates of 2 to 5 centimeters per minute—especially in GPS-denied scenarios.30
To mitigate these physical vulnerabilities, system designs must incorporate rigorous electromagnetic compatibility (EMC) standards and active coordination techniques.
| EMI Mitigation Category | Techniques and Implementation Strategies | Source Applications |
| Passive Shielding | Exterior shielded enclosures, ferrite beads, EMI filters, and advanced cable shielding to protect vulnerable internal components and reduce emissions. | Baseline hardware resilience and power system protection.4 |
| Active Coordination | Spatial multiplexing, adaptive channel access, and multi-level path planning architectures (e.g., adaptive ant colony algorithms) to prevent signal collision. | Swarm internal networking and trajectory prediction.30 |
| Frequency Agility | Distributed spectrum allocation utilizing higher frequency bands (e.g., millimeter waves at 77 GHz) and dynamic frequency shifting to lower interference probabilities. | Co-channel mitigation and high-resolution swarm detection.32 |
5. The Adversarial Threat Landscape: Electronic Warfare and Contested Environments
The operating environment defined by current near-peer competitors is actively hostile to traditional RF communications. Insights derived from ongoing conflicts, particularly in Ukraine, demonstrate that numerical mass alone does not guarantee tactical success if the overarching network is highly susceptible to adversarial electronic warfare.35 In modern combat, the drone will only get through if its communication architecture survives.37
5.1. The Russian Electronic Warfare Architecture
Russian military doctrine heavily integrates non-kinetic spectrum operations across all service branches.38 Since 2009, the vertical integration of domestic defense industry companies into entities like the Radio-Electronic Technologies Concern (KRET) has driven intensive lobbying and promotion of EW interests within the Russian military.38 Consequently, the Russian Armed Forces deploy sophisticated, layered EW systems designed specifically to suppress satellite navigation, disrupt tactical communications, and neutralize drone operations.7
Key adversarial systems observed in current theaters include:
| Adversarial EW System | Primary Function and Target Profile | Operational Impact |
| Borisoglebsk-2 (R-330B/R-934B) | A multi-functional, ground-vehicle-mounted system that acts as a core command post, controlling various jamming units from a single point. | Targets both communications and GPS systems, severely degrading airborne coordination and command links.7 |
| Pole-21 (R-340RP) | Explicitly engineered to suppress satellite navigation signals (GNSS/GPS) over wide areas. | Neutralizes high-precision guided munitions and disrupts autonomous drone navigation.39 |
| Zhitel (R-330Zh) | An automated jammer targeting satellite communication networks (e.g., INMARSAT, IRIDIUM) and cellular bands (GSM). | Cuts off long-range telemetry and severs beyond-visual-line-of-sight (BVLOS) communication links.38 |
The lethality of these systems is evident in the severe attrition rates of tactical drones. In highly contested zones, 60 to 80 percent of all first-person view (FPV) drones operated have been neutralized by RF and GNSS signal jamming.9 To circumvent this overwhelming electromagnetic pressure, forces have occasionally been forced to revert to physical workarounds. For example, innovations have included deploying FPV drones tethered by kilometers of physical fiber-optic cables, allowing them to penetrate areas of heavy jamming and strike targets without relying on the electromagnetic spectrum at all.9 While effective in niche tactical scenarios, tethered systems cannot scale to meet the strategic requirements of ADA2 or broad swarm operations.
5.2. Advanced Adversarial Swarm Capabilities
Strategic competitors are concurrently developing their own uncrewed capabilities and counter-swarm technologies. The People’s Liberation Army (PLA) has heavily prioritized the “intelligentization” of its forces, accelerating drone warfare research for potential multi-domain conflicts, including specific testing for scenarios involving an invasion of Taiwan.42 Analysis indicates that Chinese development in artificial intelligence for drone swarms is rapidly advancing, focusing on utilizing uncrewed systems to overwhelm adversary air defenses.42
However, intelligence assessments also note vulnerabilities in adversary AI development, such as the risk of “model collapse.” As Chinese leaders deploy AI systems trained on strictly controlled domestic information ecosystems, the models become detached from ground truth, functioning merely as mirrors of the state’s information control apparatus rather than objective intelligence processors.43
Concurrently, foreign militaries are closely studying western doctrine to develop automated, AI-driven counter-drone architectures. In response, the U.S. Army is accelerating initiatives like Project Golden Shields, designed to automate the response chain against high-volume aerial threats and drone swarms.44 These automated defense systems will undoubtedly become high-priority targets for adversaries, further emphasizing the need for resilient EMS operations.
6. Decentralized Command and Control: Transitioning to Leaderless Swarms
The DoD’s historical reliance on centralized command-and-control (C2) models presents a critical vulnerability in the modern electromagnetic environment. Legacy drone operations typically utilize a “mothership” model or a single ground control station, routing all telemetry, commands, and video feeds through a central node.11
Centralized architectures rely on a single ‘mothership’ or ground station; neutralizing this node incapacitates the entire swarm. In a decentralized mesh network, every drone acts as a router, allowing the swarm to self-heal and maintain operational coherence even if multiple units are jammed or destroyed.11 If an adversary successfully jams, deceives, or physically destroys the mothership, the entire fleet of dependent uncrewed systems is rendered inert, creating an unacceptable single point of failure.47
6.1. The Transition to Mesh Networking
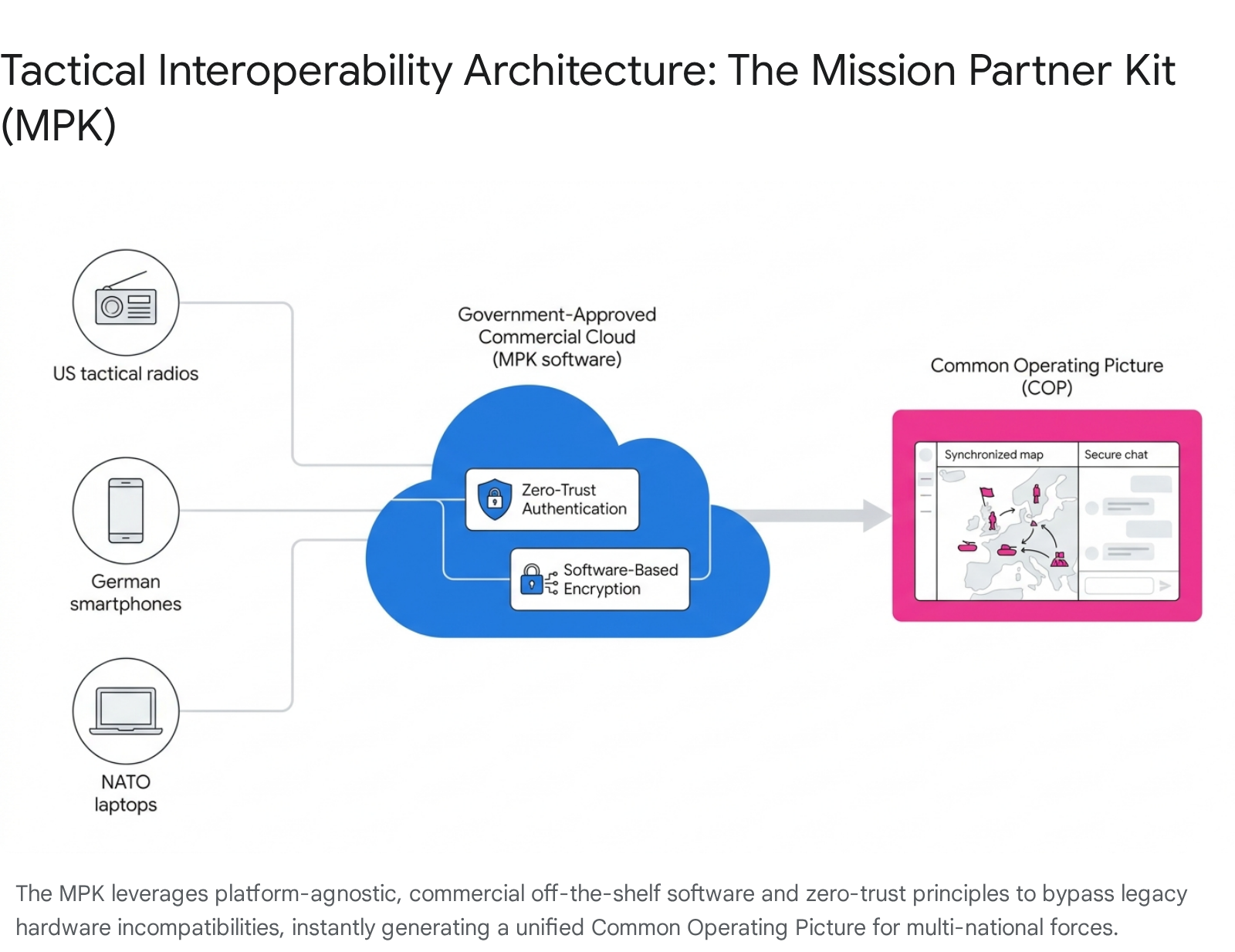
To achieve the requisite resilience, communications architectures must shift fundamentally to decentralized, ad-hoc mesh networks.10 In a true mesh network topology, every drone (or node) functions simultaneously as a transmitter, receiver, and router.46 Data packets are not forced through a central hub; instead, they dynamically hop between nodes, automatically evaluating and seeking the most efficient and clear path to their destination based on rules-based criteria.46
This architecture provides inherent “self-healing” capabilities. If a drone is shot down, encounters localized jamming, or moves behind physical terrain that blocks line-of-sight, the network instantly re-routes traffic through surviving adjacent nodes.46 Technologies such as Kinetic Mesh networking evaluate communication paths in real-time without relying on fixed infrastructure, ensuring that secure communications persist even as platforms move rapidly through highly degraded and dynamic environments.49 This is vital for maintaining situational awareness and tracking partner force operations in austere conditions without traditional cellular or SATCOM availability.52
6.2. Leaderless Swarm Autonomy
Software platforms are evolving to manage thousands of assets simultaneously without the need for centralized human control or a single mothership. Systems such as L3Harris’s AMORPHOUS (Autonomous Multi-domain Operations Resiliency Platform for Heterogeneous Unmanned Swarms) are actively demonstrating “leaderless swarm” capabilities.11
In a leaderless swarm, an operator assigns a high-level objective—for example, conducting a search over a specific coordinate grid or executing a coordinated strike. The software distributes the command across the entire fleet.11 The drones intelligently delegate tasks among themselves, deconflict routing to avoid collision and internal EMI, and execute the mission collaboratively.11 This decentralized decision-making allows individual uncrewed assets to perform tasks autonomously inside the network, stripping away the vulnerability of a single, targetable C2 node and enabling rapid scaling across multi-domain operations.53
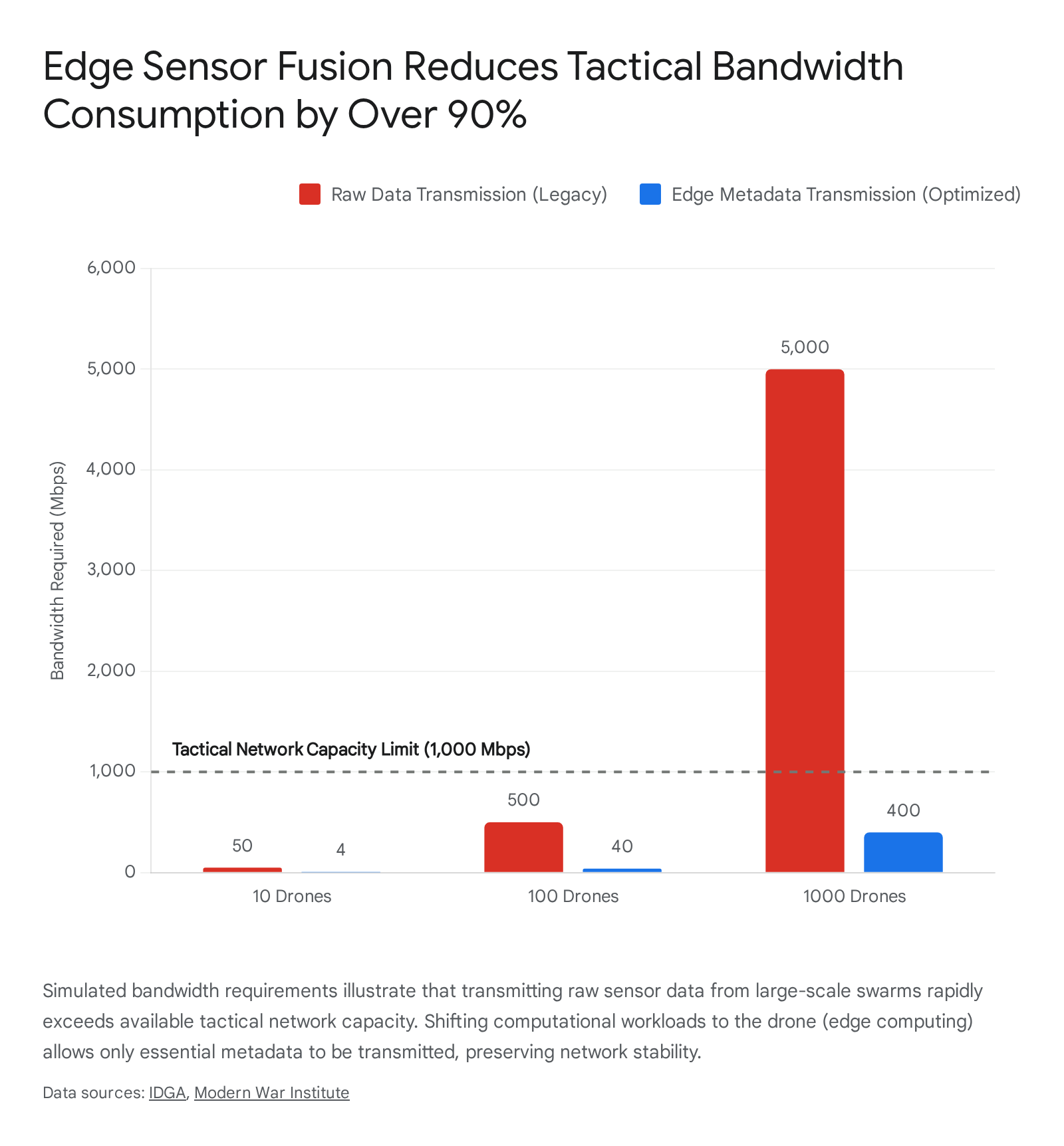
7. Bandwidth Mitigation through Edge Computing and Sensor Fusion
Solving the bandwidth crisis requires altering not just how data is transmitted, but fundamentally changing what data is transmitted. Traditional architectures stream continuous, raw data—such as high-definition video feeds or unfiltered radar returns—from the drone back to an enterprise cloud or ground station for processing and human analysis. In Denied, Disconnected, Intermittent, and Limited (D-DIL) environments, this reliance on reach-back communications is a fatal flaw.55
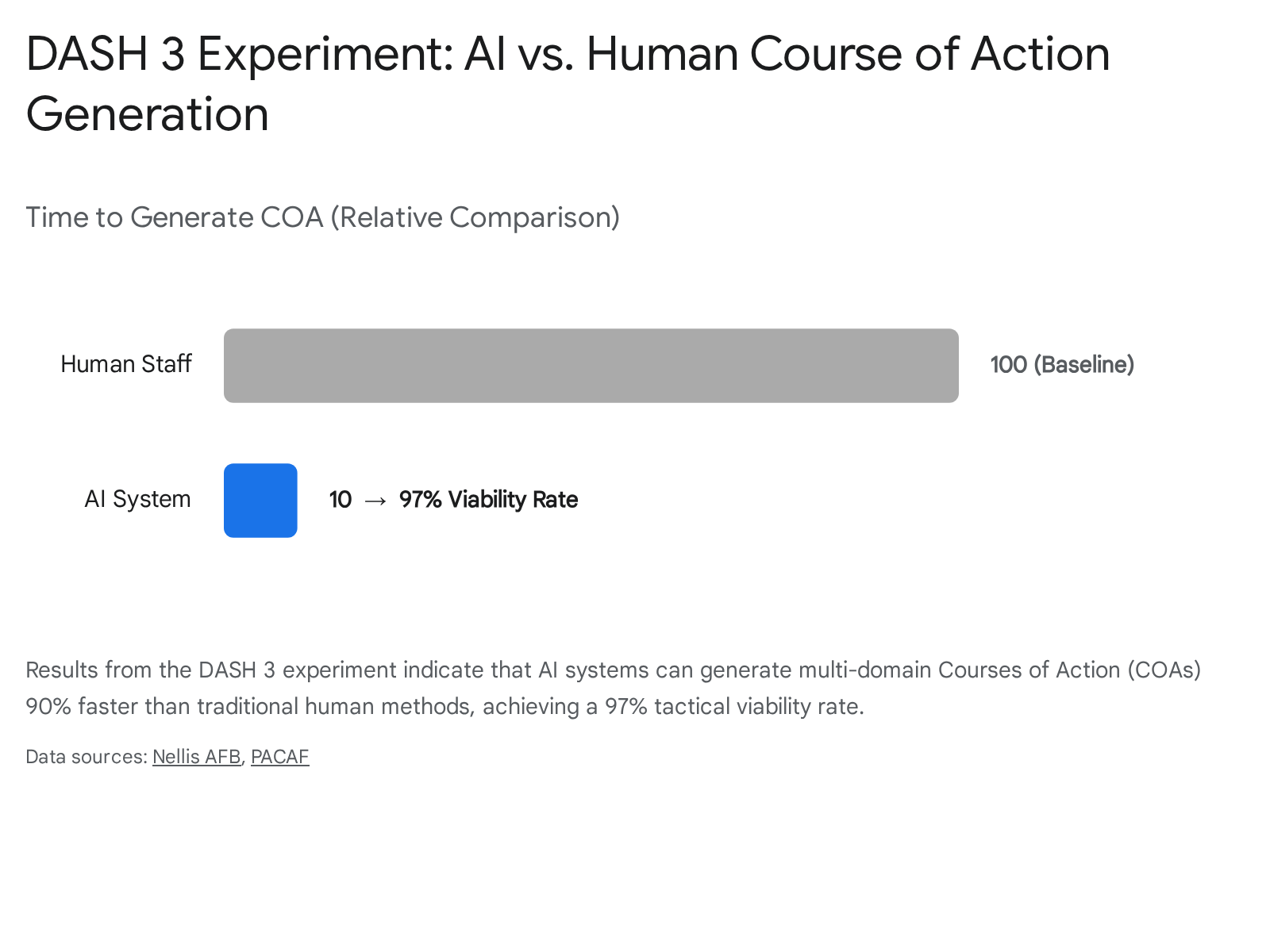
7.1. Edge Artificial Intelligence
The integration of ruggedized hardware processors—such as Tensor Processing Units (TPUs), Neural Processing Units (NPUs), and Field-Programmable Gate Arrays (FPGAs)—directly onto the drone platform allows for Edge AI.55 Edge computing forces the processing of information to occur at the point of collection, far beyond the traditional IT enterprise.56
Instead of transmitting gigabytes of high-definition video over a saturated RF link, the drone’s onboard AI processes the video locally. It identifies the target, calculates trajectories, and generates essential metadata.12 Only this metadata—such as target classification, exact coordinates, and velocity—is transmitted back to the operator or shared with the swarm.12 This transition from raw data streaming to selective metadata transmission drastically reduces bandwidth requirements, preventing network overload and operator cognitive fatigue.12
7.2. Tactical Sensor Fusion
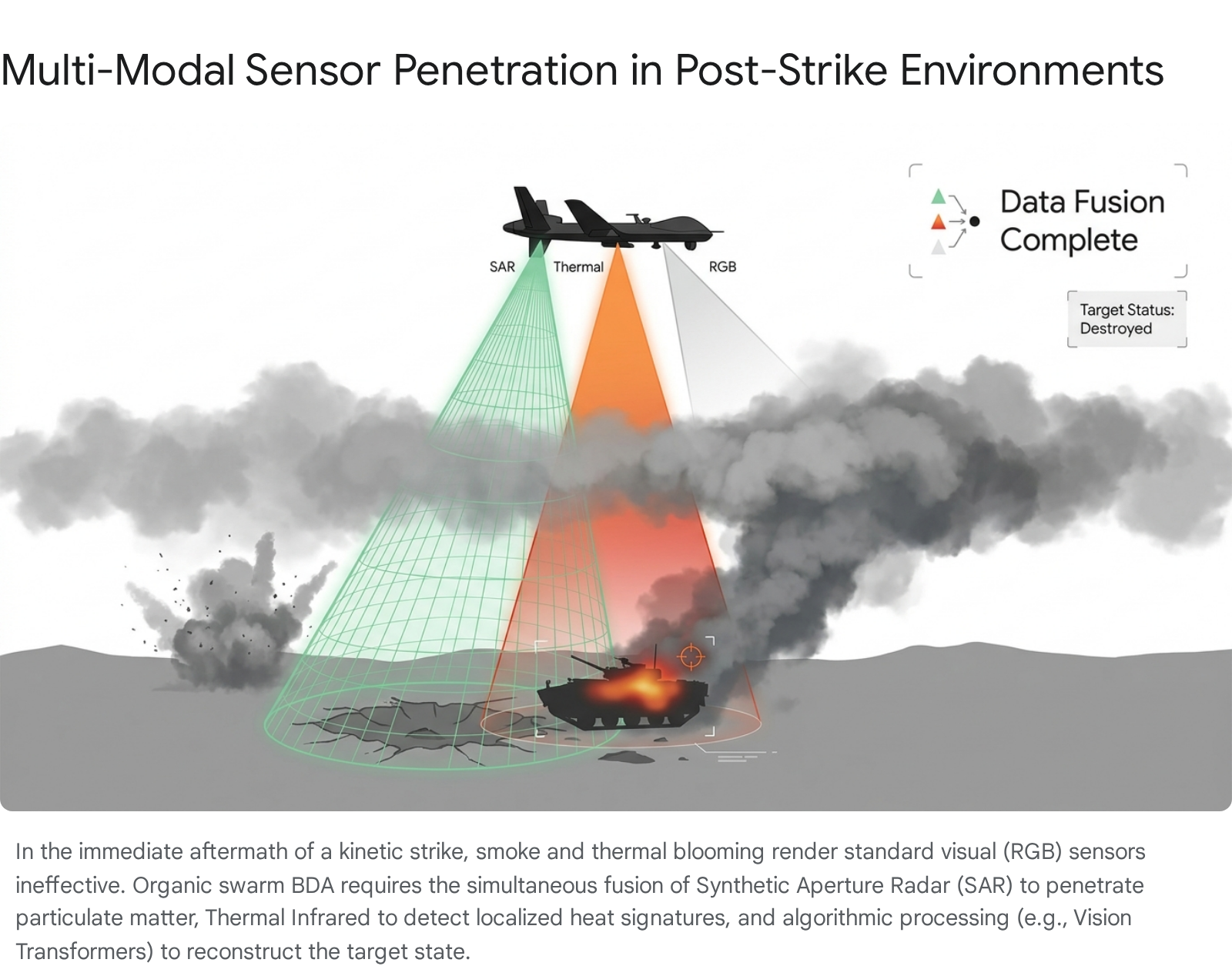
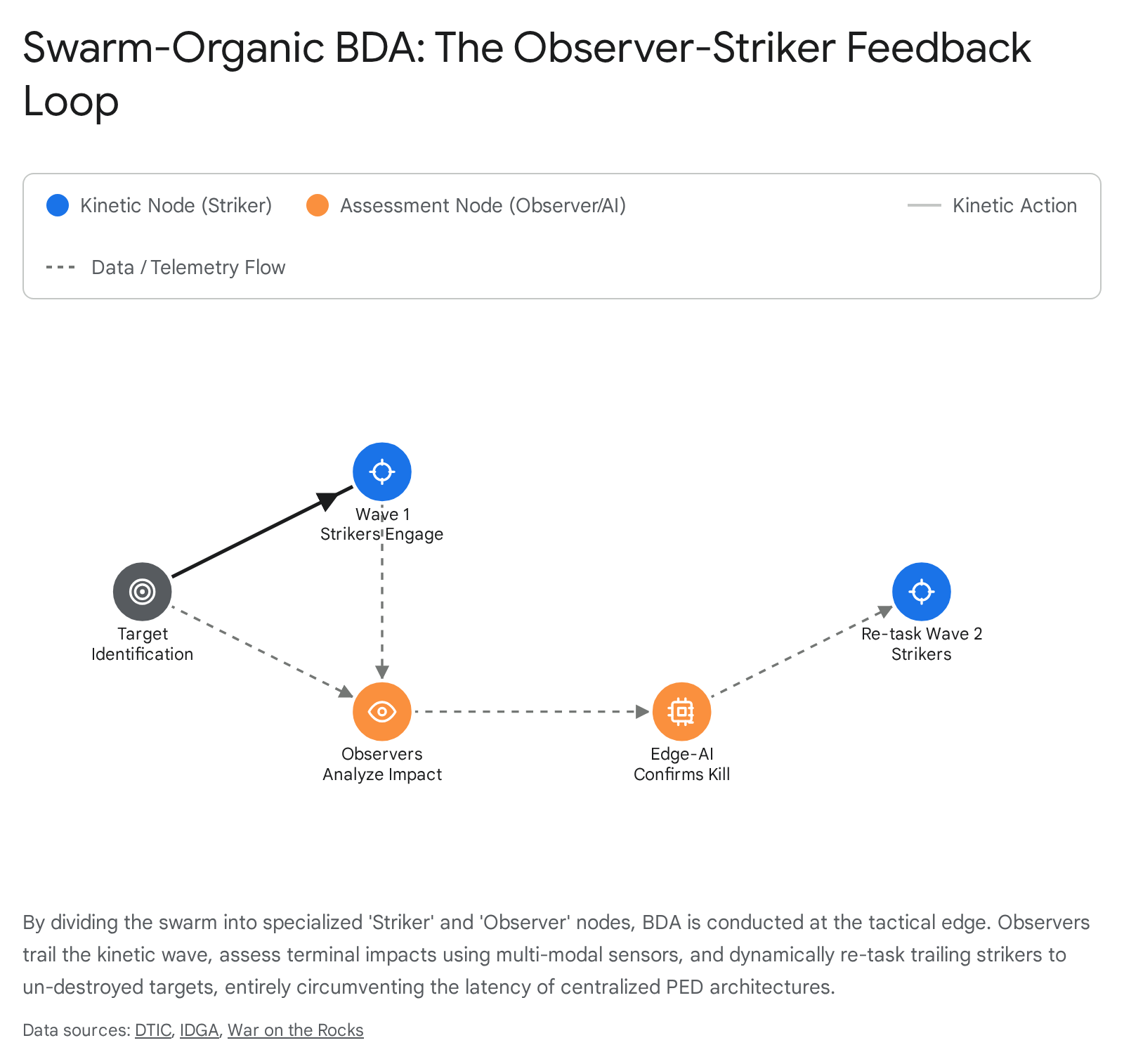
Further network optimization and operational clarity are achieved through advanced sensor fusion. When multiple drones in a swarm detect the same target, legacy systems often transmit separate tracks, clogging the network with redundant data and confusing C2 displays with multiple icons for a single entity.23
Sensor fusion is the alignment and merging of detections from multiple distributed sensors into a single, highly accurate object track.23 To achieve this across a swarm, precise temporal alignment is mandatory. All sensors, effectors, and C2 nodes must operate on a strictly synchronized, shared clock.23 By correlating data at the tactical edge before transmission, the swarm operates as a unified, overcomplete sensory architecture.23 This ensures that decision-making fidelity is maintained without relying on any single data source and without overwhelming the available tactical spectrum.23 Precedents for this approach exist in advanced crewed platforms; the F-35, for instance, utilizes a multifunction advanced data link (MADL) to automatically fuse environmental data and distribute a single, unified operational picture across a squadron.56
8. Hardware Agility and Stealth Communications
To outmaneuver adversaries in the EMS, the physical hardware of the swarm must be as agile and adaptable as its software. Rigid, single-purpose radio modules are incompatible with the demands of modern electronic warfare.
8.1. Software-Defined Radios (SDR)
Legacy radio modules operate on predetermined frequencies and fixed modulations.60 Confronting a new EW threat or adapting to a different spectrum regulatory environment previously required physical hardware replacement, causing severe logistical delays. Software-Defined Radios (SDR) resolve this limitation by shifting the heavy lifting of modulation, demodulation, encoding, and frequency selection from hardware into software.60
Cognitive SDRs represent a further leap. These radios can autonomously assess their RF environment, detect interference or jamming, and dynamically adjust frequencies in real-time to optimize performance.60 Instead of rigid hardware limitations, SDRs utilize advanced algorithms to instruct the system to hop between frequencies and find innovative pathways to maintain the link.62 This flexibility allows a single SDR datalink to support multiple mission profiles, platforms, or even coalition partner networks simply by loading a new software profile, vastly reducing procurement overhead and increasing tactical adaptability.60
8.2. Modular Open Systems Approach (MOSA)
To integrate technologies like SDRs and Edge AI rapidly, the DoD is enforcing a Modular Open Systems Approach (MOSA).14 The implementation of MOSA is not merely a best practice; it is a statutory requirement codified under Title 10 U.S.C. 4401(b).14 This legislation mandates that all major defense acquisition programs employ modular designs featuring standardized, machine-readable interfaces that allow major components to be incrementally added, removed, or upgraded.14
By decoupling the radio hardware and sensor payloads from the proprietary flight control software of the airframe, the DoD can continuously field upgraded algorithms from varied commercial vendors to counter evolving EW threats, without having to replace the entire drone fleet.13 This open business model permits sharing risk, maximizing asset reuse, and spurring competition among defense and intelligence community partners.13
| Key MOSA Standard | Domain and Application Focus | Function |
| OMS (Open Mission Systems) | Military aviation weapons systems, services, and subsystems. | Ensures interoperability of mission payloads across different aircraft platforms.13 |
| FACE (Future Airborne Capability Environment) | Aircraft systems software. | Standardizes software environments to allow applications to be portable across different avionics systems.13 |
| MORA (Modular Open RF Architecture) | Radio frequency capabilities. | Maximizes RF flexibility, essential for integrating advanced SDRs and dynamic spectrum management.13 |
| CMOSS (C5ISR/EW Modular Open Suite of Standards) | Comprehensive suite integrating FACE, VPX, MORA, VICTORY, and Redhawk. | Serves as the overarching framework for networked communications, electronic warfare, and sensor integration.13 |
8.3. Low Probability of Intercept and Detection (LPI/LPD)
Survival in a contested spectrum requires operating beneath the adversary’s detection threshold. Traditional omnidirectional radios broadcast signals that are easily detected, pinpointed, and jammed by systems like the Russian Borisoglebsk-2.64 Advanced autonomous swarms must utilize Low Probability of Detection (LPD) and Low Probability of Intercept (LPI) communications to remain covert.64
- LPD (Low Probability of Detection): Focuses on minimizing the chance an adversary detects the signal’s presence at all. This is achieved utilizing directional transmission, low-power emissions, and noise-like waveforms that blend seamlessly into the background electromagnetic radiation.64
- LPI (Low Probability of Intercept): Ensures that even if a signal is detected, it is exceedingly difficult to decode, exploit, or jam. LPI techniques include rapid frequency hopping, complex spread-spectrum modulation, and AI-driven adaptive beamforming.64
Implementing advanced LPI/LPD protocols, such as those demonstrated in naval exercises like “Silent Swarm,” within autonomous mesh networks ensures that drones can coordinate tasks, route data, and execute complex maneuvers without broadcasting their position to adversary signals intelligence (SIGINT) operators.64
9. Doctrinal, Regulatory, and Organizational Realignments
Technological acquisition must be matched by profound doctrinal and organizational shifts. Procurement of advanced drones is insufficient if the force is not structurally organized, trained, and legally authorized to manage the spectrum those platforms rely upon.
9.1. Decentralized Training and Field Integration
The DoD is currently overhauling its operational doctrine to integrate lessons learned from recent conflicts, shifting aggressively toward a “learn-by-doing” approach.67 Initiatives like the Army’s Transformation in Contact (TiC) prioritize deploying new systems directly to operational units rather than waiting years for perfect technological maturity.67 This iterative fielding allows real-world user feedback to drive rapid updates to tactics, techniques, and procedures (TTPs).67 For instance, recent updates to Field Manual 3-0 include new operational imperatives specifically designed to address persistent drone threats and the necessity of making contact with the smallest element possible.67
Furthermore, training regimens must evolve. Operating within the spectrum requires specialized, highly technical knowledge.6 Expanding the presence and training of Spectrum Management Officers (SMO) at lower tactical echelons is critical.69 These officers are required to deconflict frequencies, navigate highly restrictive Federal Aviation Administration (FAA) and Federal Communications Commission (FCC) regulations, and ensure operational compliance without stifling combat agility.69 For example, recent FCC orders enabling limited access to the 5030-5091 MHz band for drone operations require complex registration and deconfliction processes that tactical units must be trained to navigate seamlessly.70
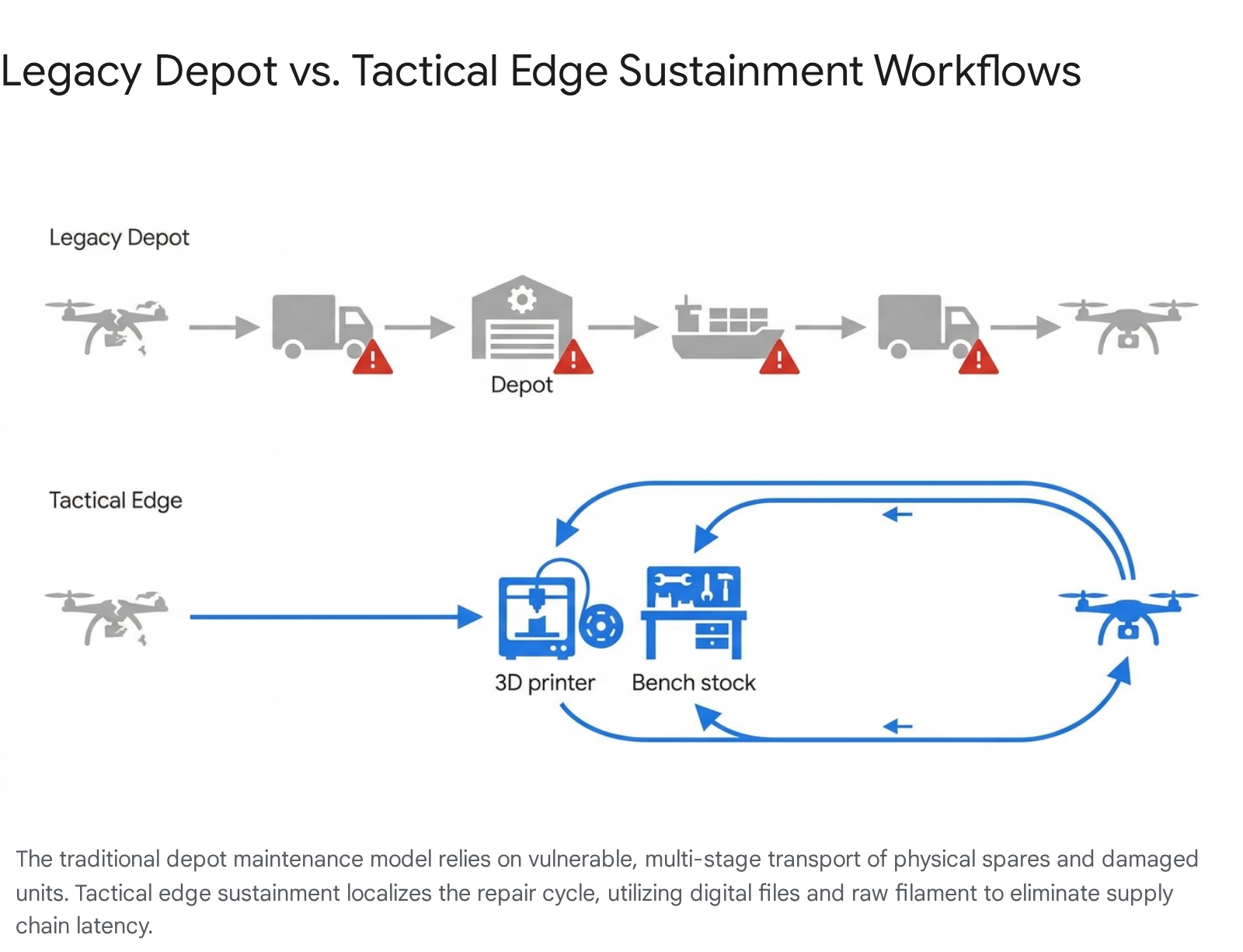
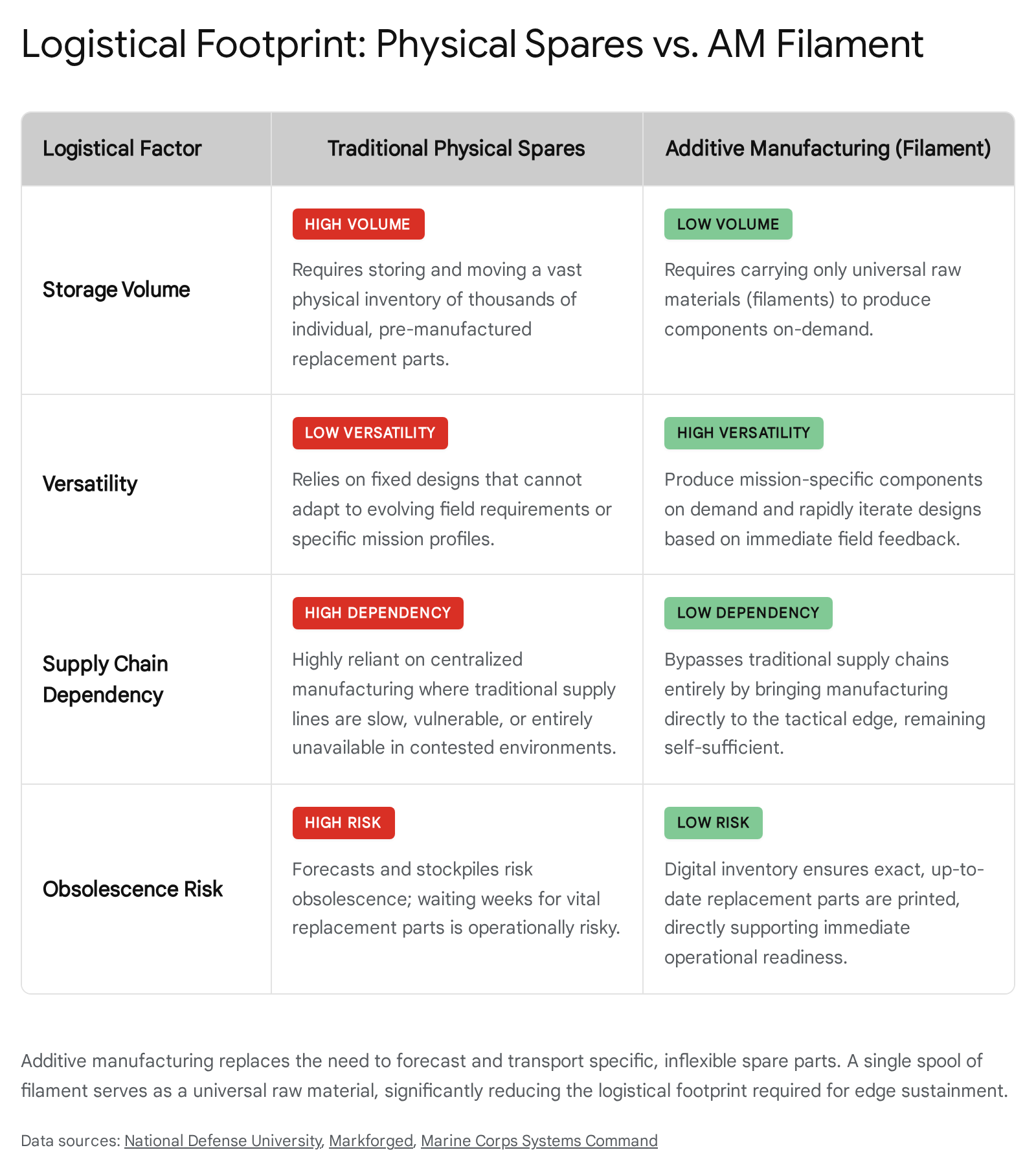
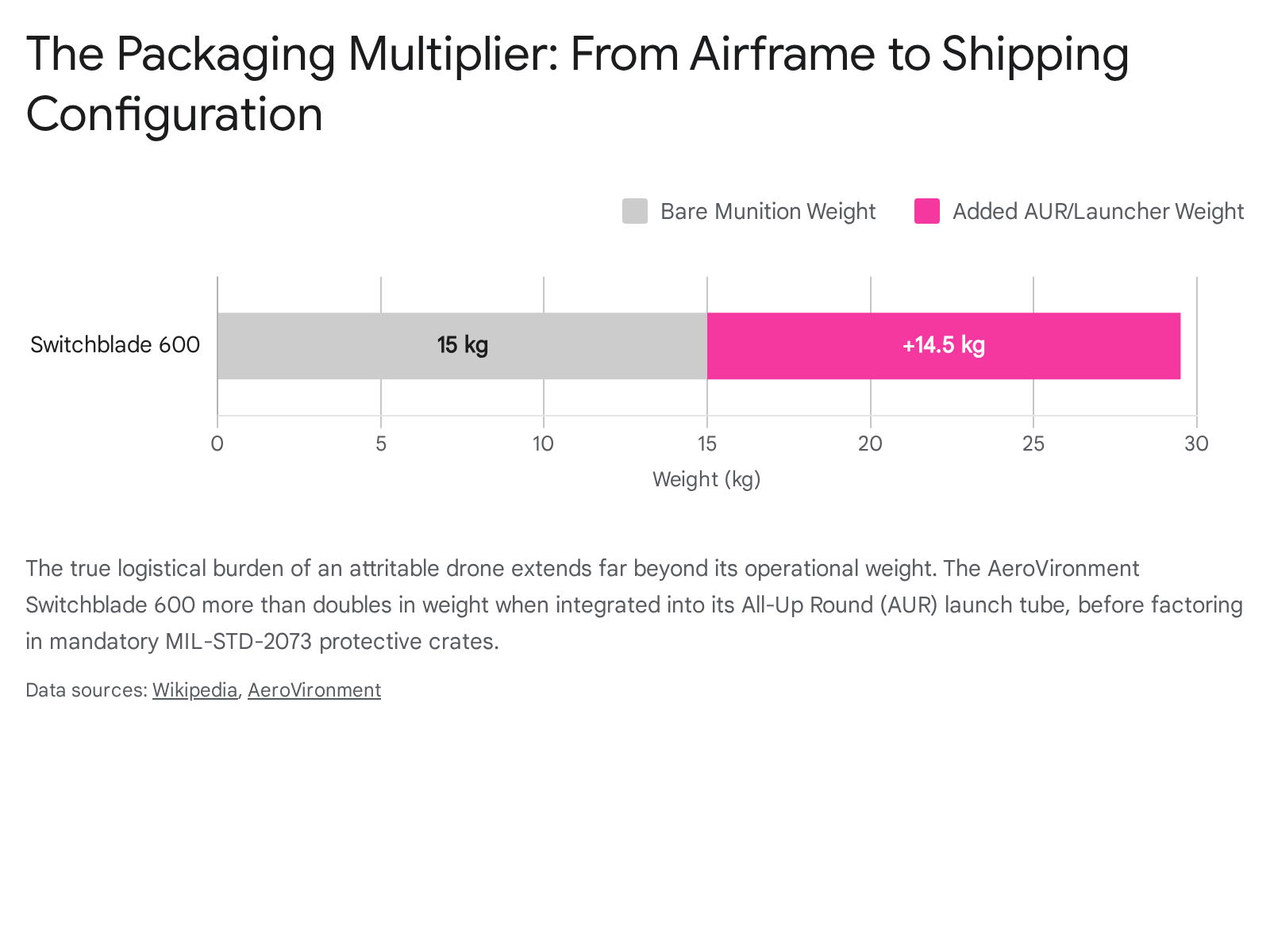
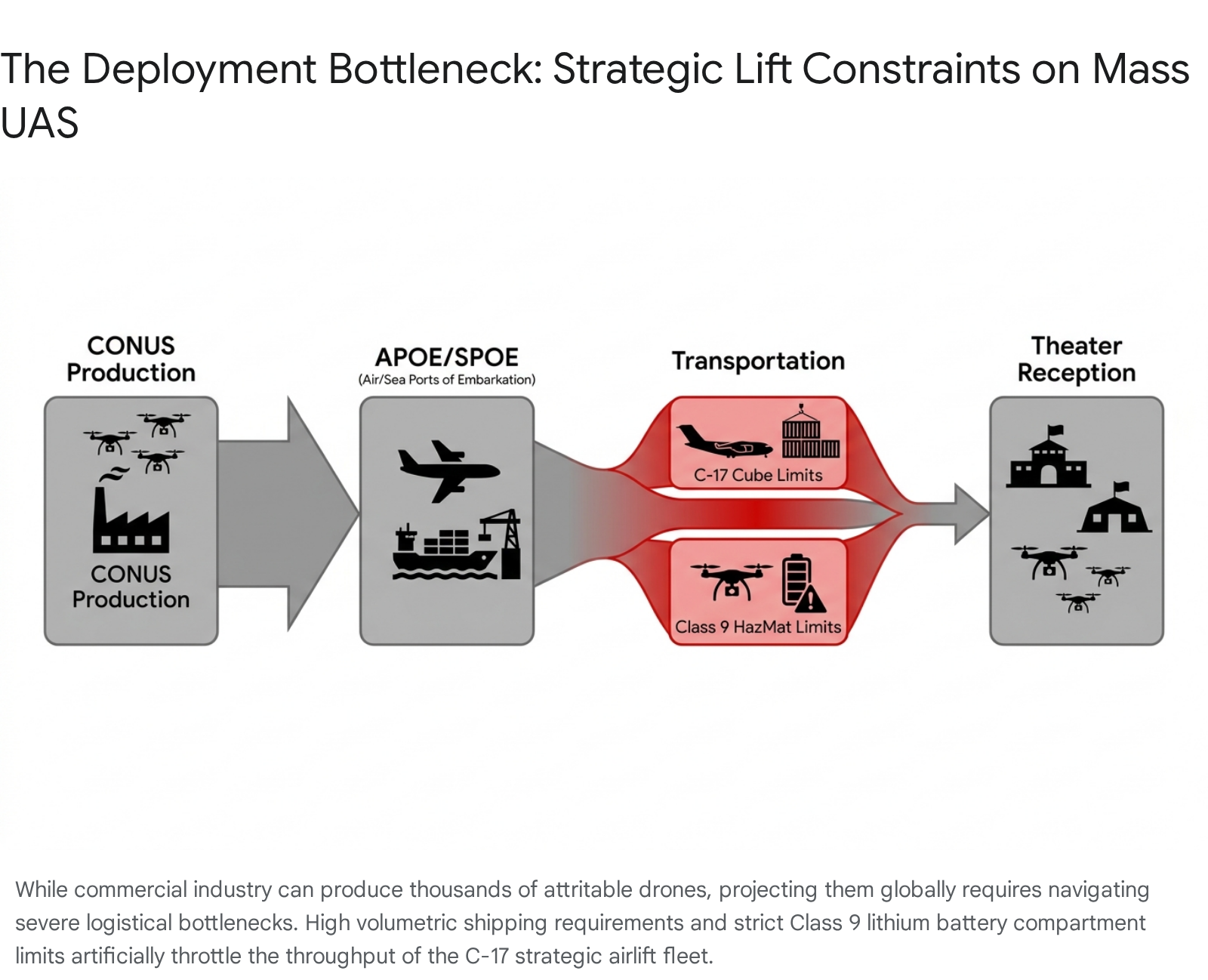
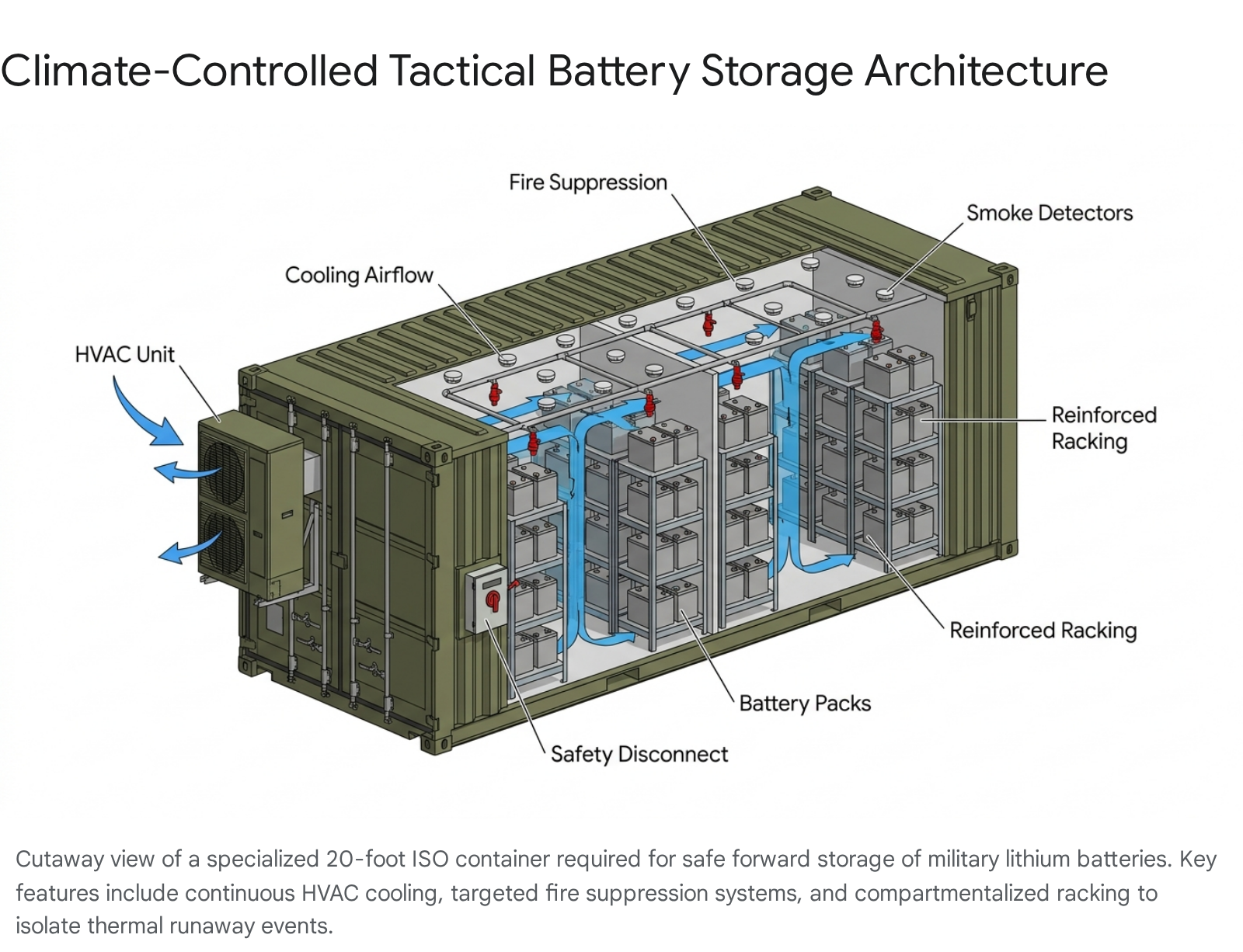
9.2. Operationalizing Production at the Tactical Edge
The demands of rapid-reaction warfare expose the inherent limitations of centralized, bureaucratic procurement models. The ability to innovate inside the adversary’s decision cycle requires Fabrication at the Tactical Edge (FATE).72 By leveraging additive manufacturing (3D printing) and AI directly in the field, joint forces can design, produce, and modify expendable drone components—such as specific antenna mounts, aerodynamic modifications, or shielding adaptations—in response to immediate EW threats.72 This paradigm decentralizes production, effectively allowing forces to execute an acquisition and deployment cycle within 24 hours, rapidly countering localized adversarial spectrum tactics.72
9.3. The Collaborative Combat Aircraft (CCA) Paradigm
The lessons of spectrum resilience being learned in small drone swarms are actively scaling to the highest tiers of air dominance. The U.S. Air Force’s Collaborative Combat Aircraft (CCA) program represents the maturation of these concepts.73 Designed to fly alongside crewed fighters as autonomous wingmen, the CCA relies heavily on secure, semi-autonomous communication architectures.73 Recent successful flights utilizing integrated third-party mission autonomy software (such as Sidekick) integrated via the Autonomy Government Reference Architecture (A-GRA) underscore the viability of decentralized decision-making at higher speeds and larger scales.75 However, the ultimate success of programs like the CCA, which may scale to thousands of aircraft, hinges entirely on the exact same principles of EMS resilience, MOSA adherence, and LPI/LPD stealth networking discussed throughout this report.74
10. Strategic Conclusions
The Department of Defense’s intense focus on massive drone acquisition signals a necessary and urgent adaptation to the realities of modern warfare. However, the physical hardware of these platforms represents only the visible surface of the capability. The true center of gravity for scaled autonomous operations is the electromagnetic spectrum.
Adversaries are actively fielding sophisticated electronic warfare systems designed specifically to sever the critical links upon which uncrewed systems depend. To secure the operational viability of initiatives like Replicator and broader drone dominance strategies, DoD leadership must prioritize investments in the unseen architecture of the swarm.
This requires an immediate and sustained commitment to moving away from fragile, centralized command structures and embracing self-healing, leaderless mesh networks. It demands the integration of edge computing and sensor fusion to drastically reduce bandwidth dependency and prevent network collapse. Furthermore, the mandatory adoption of software-defined radios and open systems architectures is essential to ensure that U.S. forces can dynamically maneuver within the spectrum faster than adversaries can jam it. Ultimately, success in future conflicts will not be measured solely by the sheer number of drones procured, but by the resilience, agility, and covertness of the networks that connect them.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Sources Used
- Deep Dive: Pentagon’s Replicator Initiative Raises Questions | Inkstick, accessed April 24, 2026, https://inkstickmedia.com/deep-dive-pentagons-replicator-initiative-raises-questions/
- Unleashing U.S. Military Drone Dominance – Department of War, accessed April 24, 2026, https://media.defense.gov/2025/Jul/10/2003752117/-1/-1/1/UNLEASHING-U.S.-MILITARY-DRONE-DOMINANCE.PDF
- Spectrum Management: Key to the Future of Unmanned … – dtic.mil, accessed April 24, 2026, https://apps.dtic.mil/sti/tr/pdf/ADA484444.pdf
- Strong Electromagnetic Interference and Protection in UAVs – MDPI, accessed April 24, 2026, https://www.mdpi.com/2079-9292/13/2/393
- From single-band fragility to adaptive spectrum control – Military Embedded Systems, accessed April 24, 2026, https://militaryembedded.com/unmanned/sensors/from-single-band-fragility-to-adaptive-spectrum-control
- Countering Swarms: Strategic Considerations and Opportunities in Drone Warfare, accessed April 24, 2026, https://ndupress.ndu.edu/Media/News/News-Article-View/Article/3197193/countering-swarms-strategic-considerations-and-opportunities-in-drone-warfare/
- Borisoglebsk-2 – Wikipedia, accessed April 24, 2026, https://en.wikipedia.org/wiki/Borisoglebsk-2
- Mapping the MilTech War: Eight Lessons from Ukraine’s Battlefield – Ifri, accessed April 24, 2026, https://www.ifri.org/en/studies/mapping-miltech-war-eight-lessons-ukraines-battlefield
- Russia’s Changes in the Conduct of War Based on Lessons from Ukraine – Army University Press, accessed April 24, 2026, https://www.armyupress.army.mil/Journals/Military-Review/English-Edition-Archives/September-October-2025/Lessons-from-Ukraine/
- Military & Defense Networks – Secure Tactical Wireless – Rajant, accessed April 24, 2026, https://rajant.com/defense/
- L3Harris unveils Amorphous autonomy software to manage drone swarms – Defense News, accessed April 24, 2026, https://www.defensenews.com/unmanned/2025/02/10/l3harris-unveils-amorphous-autonomy-software-to-manage-drone-swarms/
- Embedded AI in Military Drones Is Redefining Autonomy and Operations – IDGA, accessed April 24, 2026, https://www.idga.org/government-defense-it-communications/articles/embedded-ai-in-military-drones-is-redefining-autonomy-and-operations
- What is MOSA? – BAE Systems, accessed April 24, 2026, https://www.baesystems.com/en-us/definition/what-is-mosa
- Modular Open Systems Approach (MOSA) – Defense Standardization Program, accessed April 24, 2026, https://www.dsp.dla.mil/Programs/MOSA/
- AY 2024-2025 SPRING 2025 INDUSTRY STUDY REPORT: ELECTROMAGNETIC WARFARE 15 MAY 2025 Word Count – Eisenhower School for National Security and Resource Strategy, accessed April 24, 2026, https://es.ndu.edu/Portals/75/Documents/Industry%20Study%20Reports/reports/2025/AY25%20Electromagnetic%20Warfare-Cleared.pdf?ver=U_f9M9RL9ySMAMko8L40-w%3D%3D
- DOD Electromagnetic Spectrum Superiority Strategy – Defense Management Institute, accessed April 24, 2026, https://www.dmi-ida.org/knowledge-base-detail/DOD-Electromagnetic-Spectrum-Superiority-Strategy
- DoD Electromagnetic Spectrum Superiority Strategy 2020 – Department of War, accessed April 24, 2026, https://media.defense.gov/2020/Oct/29/2002525927/-1/-1/0/electromagnetic_spectrum_superiority_strategy.pdf
- Electromagnetic Spectrum Operations: DOD Needs to Take Action to Help Ensure Superiority | U.S. GAO, accessed April 24, 2026, https://www.gao.gov/products/gao-21-440t
- 10 USC 500d: Electromagnetic spectrum superiority implementation plan – OLRC Home, accessed April 24, 2026, https://uscode.house.gov/view.xhtml?req=granuleid:USC-prelim-title10-section500d&num=0&edition=prelim
- Electromagnetic Simulation Makes Connections with the US DoD’s JADC2 Implementation – Electro Magnetic Applications, Inc. – EMA3D, accessed April 24, 2026, https://www.ema3d.com/blog/electromagnetic-simulation-makes-connections-with-the-us-dods-jadc2-implementation/
- DOD preparing for first large-scale demonstration of spectrum-sharing tech in 2025, accessed April 24, 2026, https://rt.cto.mil/dod-preparing-for-first-large-scale-demonstration-of-spectrum-sharing-tech-in-2025/
- What Trump’s order on ‘unleashing American drone dominance’ means for the U.S. military, accessed April 24, 2026, https://defensescoop.com/2025/07/08/trump-executive-order-unleashing-american-drone-dominance-military-implications/
- Frontline Fusion: The Network Architecture Needed to Counter Drones, accessed April 24, 2026, https://mwi.westpoint.edu/frontline-fusion-the-network-architecture-needed-to-counter-drones/
- Data Transmission Between a Drone Swarm and a Ground Base: Modern Methods and Technologies—A Narrative Review, accessed April 24, 2026, https://premierscience.com/pjs-25-1302/
- Reliable Communication Systems for Long-Range Drone Operations, accessed April 24, 2026, https://xray.greyb.com/drones/communication-protocols-long-range-drone-networks
- How to Reduce EMI in Drone Testing – Mitigation Techniques – Tyto Robotics, accessed April 24, 2026, https://www.tytorobotics.com/blogs/articles/how-to-reduce-emi-in-drone-testing-emi-mitigation-techniques
- Co-Channel Interference Mitigation Using Deep Learning for Drone-Based Large-Scale Antenna Measurements – arXiv, accessed April 24, 2026, https://arxiv.org/html/2601.13205v1
- The Rising Importance of EMI Shielding for Drone Protection – Titan Electronics, accessed April 24, 2026, https://titanelectronics.com/blog/the-rising-importance-of-emi-shielding-for-drone-protection/
- Mitigation of Major Electromagnetic Interference problems for Drones and Robotics Systems, accessed April 24, 2026, https://www.odenserobotics.dk/mitigation-of-major-electromagnetic-interference-problems-for-drones-and-robotics-systems/
- Innovations in Drone Swarm Technology – GreyB, accessed April 24, 2026, https://xray.greyb.com/drones/coordination-of-multiple-drones
- Agent-Based Anti-Jamming Techniques for UAV Communications in Adversarial Environments: A Comprehensive Survey – arXiv, accessed April 24, 2026, https://arxiv.org/html/2508.11687v1
- Exploring Techniques to Mitigate Interference in Drone Communication Systems – ALife Robotics, accessed April 24, 2026, https://alife-robotics.co.jp/members2025/icarob/data/html/data/OS/OS25/OS25-1.pdf
- “ISAR imaging of drone swarms at 77 GHz” by REMZİYE BÜŞRA ÇORUK, ALİ KARA et al., accessed April 24, 2026, https://journals.tubitak.gov.tr/elektrik/vol33/iss4/3/
- Key Enabling Technologies for 6G: The Role of UAVs, Terahertz Communication, and Intelligent Reconfigurable Surfaces in Shaping the Future of Wireless Networks – MDPI, accessed April 24, 2026, https://www.mdpi.com/2224-2708/14/2/30
- Lessons from the Ukraine Conflict: Modern Warfare in the Age of Autonomy, Information, and Resilience – CSIS, accessed April 24, 2026, https://www.csis.org/analysis/lessons-ukraine-conflict-modern-warfare-age-autonomy-information-and-resilience
- The Impact of Drones on the Battlefield: Lessons of the Russia-Ukraine War from a French Perspective | Hudson Institute, accessed April 24, 2026, https://www.hudson.org/missile-defense/impact-drones-battlefield-lessons-russian-ukraine-war-french-perspective-tsiporah-fried
- The Vulnerabilities of the Drone Age Established Threats and Emerging Issues out to 2035 – CSS ETH Zürich, accessed April 24, 2026, https://css.ethz.ch/content/dam/ethz/special-interest/gess/cis/center-for-securities-studies/pdfs/NATO_VDA_Policy_Report.pdf
- Russia’s Electronic Warfare Capabilities to 2025 – International Centre for Defence and Security, accessed April 24, 2026, https://icds.ee/wp-content/uploads/2018/ICDS_Report_Russias_Electronic_Warfare_to_2025.pdf
- Analysis: Russia’s Electronic Warfare Equipment – Kyiv Post, accessed April 24, 2026, https://www.kyivpost.com/analysis/32435
- Ukrainian Bomber Drones Destroy Two Stations of Borisoglebsk-2 EW System, accessed April 24, 2026, https://militarnyi.com/en/news/ukrainian-bomber-drones-destroy-two-stations-of-borisoglebsk-2-ew-system/
- How Can Ukraine Counter Russia’s Electronic Warfare? | VOANews – YouTube, accessed April 24, 2026, https://www.youtube.com/watch?v=aWy9QPovFm8
- China Readies Drone Swarms for Future War – CNA Corporation, accessed April 24, 2026, https://www.cna.org/our-media/indepth/2025/09/china-readies-drone-swarms-for-future-war
- Inside China, artificial intelligence is a snake eating its own tail – Defense News, accessed April 24, 2026, https://www.defensenews.com/opinion/2026/04/23/inside-china-artificial-intelligence-is-a-snake-eating-its-own-tail/
- US starting to respond to challenge of massive drone incursions – Asia Times, accessed April 24, 2026, https://asiatimes.com/2026/04/us-starting-to-respond-to-challenge-of-massive-drone-incursions/
- C2 and AI Integration In Drone Warfare – Impacts On TTPs & Military Strategy, accessed April 24, 2026, https://www.strategycentral.io/post/c2-and-ai-integration-in-drone-warfare-impacts-on-ttps-military-strategy
- Mesh Network Topologies and Architectures Explained – Mobilicom, accessed April 24, 2026, https://mobilicom.com/insight/mesh-network-topologies/
- L3Harris unveils command, control software envisioned for 1000s of drones, accessed April 24, 2026, https://breakingdefense.com/2025/02/l3harris-unveils-command-control-software-envisioned-for-1000s-of-drones/
- Drone Swarm Technology | Swarm Communications | UAV Swarm Control – Unmanned Systems Technology, accessed April 24, 2026, https://www.unmannedsystemstechnology.com/expo/drone-swarm-technology/
- Network-Centric Warfare and Wireless Communications – Meshdynamics, accessed April 24, 2026, https://www.meshdynamics.com/documents/MD_MILITARY_MESH.pdf
- Military Mesh Networking Technology – Rajant, accessed April 24, 2026, https://rajant.com/defense/military-technology/
- The Greatest Mesh Network – Marine Corps Association, accessed April 24, 2026, https://www.mca-marines.org/wp-content/uploads/18-The-Greatest-Mesh-Network.pdf
- Transforming the ‘ARSOF Advantage’ Lines of Effort with Enhanced Mesh Network Technology – U.S. Army, accessed April 24, 2026, https://innovation.army.mil/News/Article-View/Article/4348802/transforming-the-arsof-advantage-lines-of-effort-with-enhanced-mesh-network-tec/
- L3Harris Launches New Technology to Control Autonomous Swarms, accessed April 24, 2026, https://www.l3harris.com/newsroom/press-release/2025/02/l3harris-launches-new-technology-control-autonomous-swarms
- L3Harris Selected to Develop Autonomous Swarms Prototype, accessed April 24, 2026, https://www.l3harris.com/newsroom/editorial/2024/11/l3harris-selected-develop-autonomous-swarms-prototype
- Operationalizing AI at the Tactical Edge – Line of Departure – U.S. Army, accessed April 24, 2026, https://www.lineofdeparture.army.mil/Journals/Warrant-Officer-Journal/Archive/March-2026/Operationalizing-AI-at-the-Tactical/
- How the U.S. Military Is Using Edge Computing – Booz Allen, accessed April 24, 2026, https://www.boozallen.com/s/insight/blog/how-the-us-military-is-using-edge-computing.html
- Military and Public Sector Edge Computing Solutions – ESL, accessed April 24, 2026, https://eslua.com/military-public-safety-edge-computing/
- Drone Swarms as Networked Control Systems by Integration of Networking and Computing, accessed April 24, 2026, https://www.mdpi.com/1424-8220/21/8/2642
- Tactical Multi-Sensor Fusion Techniques – Deca Defense, accessed April 24, 2026, https://decadefense.ai/sensor-integration-data-fusion/tactical-multi-sensor-fusion-techniques/
- Software Defined Radios (SDRs) for Tactical UAV and Robotics Communications, accessed April 24, 2026, https://mobilicom.com/insight/software-defined-radios-sdrs-for-tactical-uav-and-robotics-communications/
- 5 benefits of software defined radios (SDRs) over legacy RF systems – CRFS, accessed April 24, 2026, https://www.crfs.com/blog/5-reasons-why-militaries-need-sdr-sensors-at-the-edge
- DOD at risk of not meeting its own electromagnetic spectrum goals, experts tell Congress, accessed April 24, 2026, https://fedscoop.com/dod-at-risk-of-not-meeting-its-own-electromagnetic-spectrum-goals/
- Modular Open Systems Approach – DoW Research & Engineering, OUSW(R&E), accessed April 24, 2026, https://www.cto.mil/sea/mosa/
- What Is LPD/LPI? Stealth Communications in Tactical Defense Networks – Blu Wireless, accessed April 24, 2026, https://www.bluwireless.com/insight/lpd-lpi-stealth-tactical-communications/
- Phase I/II SBIR NAVAIR – Low Probability of Detection/Low Probability of Interception (Smart Beam-QRC) | Forward Edge Ai, Inc. Help Center, accessed April 24, 2026, https://support.forwardedge.ai/en/articles/8781279-phase-i-ii-sbir-navair-low-probability-of-detection-low-probability-of-interception-smart-beam-qrc
- Advanced Low Probability of Intercept/Low Probability of Detection Radar (LPI/LPD) Techniques Using Artificial Intelligence Driven Methods – Navy SBIR/STTR, accessed April 24, 2026, https://www.navysbir.com/n21_2/N212-114.htm
- Army adapts doctrine force-wide, integrating drone lessons to achieve ‘drone dominance, accessed April 24, 2026, https://www.army.mil/article/291361/army_adapts_doctrine_force_wide_integrating_drone_lessons_to_achieve_drone_dominance
- FY2026 – CPE ISW – U.S. Army, accessed April 24, 2026, https://cpeisw.army.mil/wp-content/uploads/2025/11/APPROVED-PRAS-00293-FY26-PM-EWC-Strategic-Planning-Guide_21-NOV-2025.pdf
- BY ORDER OF THE SECRETARY OF THE AIR FORCE DEPARTMENT OF THE AIR FORCE MANUAL 11-501 10 JANUARY 2025 Flying Operations SMALL UN, accessed April 24, 2026, https://static.e-publishing.af.mil/production/1/af_a3/publication/dafman11-501/dafman11-501_.pdf
- FCC Adopts Long-Awaited Order Enabling Limited Access to Dedicated Spectrum for Uncrewed Aircraft Systems – Wiley Rein, accessed April 24, 2026, https://www.wiley.law/alert-FCC-Adopts-Long-Awaited-Order-Enabling-Limited-Access-to-Dedicated-Spectrum-for-Uncrewed-Aircraft-Systems
- SMALL UNMANNED AIRCRAFT SYSTEM ELECTROMAGNETIC SPECTRUM PROCEDURES > United States Marine Corps Flagship > Messages Display, accessed April 24, 2026, https://www.marines.mil/News/Messages/Messages-Display/Article/4320798/small-unmanned-aircraft-system-electromagnetic-spectrum-procedures/
- Fabrication at the Tactical Edge – National Defense University, accessed April 24, 2026, https://www.ndu.edu/News/Article-View/Article/4445402/fabrication-at-the-tactical-edge/
- One Year On: How the Armed Force’s CCA Programs Have Matured – IDGA, accessed April 24, 2026, https://www.idga.org/aviation/articles/how-armed-forces-cca-matured-in-2025
- Air Force Revisiting Production Goals for CCA with Eye on ‘Scale’, accessed April 24, 2026, https://www.airandspaceforces.com/air-force-revisiting-production-goals-cca-increment-2/
- GA-ASI Achieves New Milestone With Semi-Autonomous CCA Flight, accessed April 24, 2026, https://www.ga-asi.com/ga-asi-achieves-new-milestone-with-semi-autonomous-cca-flight