1. Executive Summary
The Department of Defense (DoD) is actively shifting its force structure to counter near-peer adversaries through the deployment of autonomous systems at an unprecedented scale. High-profile programs, notably the Replicator initiative, aim to rapidly field thousands of attritable, multidomain platforms to overcome the massed advantages of strategic competitors, particularly in the Indo-Pacific theater.1 However, the institutional fixation on the procurement of the physical platform frequently obscures the complex, systemic requirements necessary to operate, deconflict, and sustain these systems in saturated, highly contested operational environments.3 Fielding autonomous mass introduces critical vulnerabilities regarding airspace management, command and control (C2) resilience, and the prevention of blue-on-blue engagements.
The integration of thousands of friendly unmanned aerial systems (UAS) into a theater already populated by manned aircraft, loitering munitions, ground-based air defenses, and adversary swarms creates an airspace environment that exceeds the capacity of legacy procedural control measures.4 Without scalable Identify Friend or Foe (IFF) mechanisms, a friendly attritable drone is virtually indistinguishable from an adversary threat on tactical radar displays, appearing merely as an unidentified track.7 Furthermore, the physical limitations of small UAS platforms restrict the integration of traditional cryptographic Mode 5 IFF transponders, thereby elevating the risk of fratricide to unacceptable levels.8
To successfully employ drone swarms while protecting joint forces, traditional concepts of airspace deconfliction must evolve. The DoD must transition from rigid, rules-based procedural control to intent-based, automated airspace deconfliction managed by artificial intelligence (AI).9 Concurrently, air defense architectures must be modernized through the Integrated Battle Command System (IBCS) and Joint All-Domain Command and Control (JADC2) networks to enable rapid, software-defined threat identification and engagement.11 This report provides a strategic analysis of the systemic requirements for massive drone integration, focusing on overcoming the critical barriers of fratricide prevention, scalable combat identification, automated airspace management, and joint air defense interoperability.
2. The Replicator Initiative and the Shift to Attritable Mass
2.1. Strategic Intent and the McNamara Paradigm
In August 2023, the DoD announced the Replicator initiative, a paradigm-shifting effort designed to field attritable autonomous systems across multiple domains within an 18-to-24-month timeline.1 The strategic calculus behind this initiative is to leverage low-cost, expendable mass to counter the numeric advantages of the Chinese military in ships, missiles, and forces.2 However, executing this vision requires dismantling legacy acquisition processes. Analysts note that DoD culture remains entrenched in a 1960s paradigm, originating under former Secretary of Defense Robert McNamara, which favors centrally-planned, linear, and highly predictive processes.1 These prolonged acquisition cycles are fundamentally incompatible with the rapid evolution of autonomous systems and the immediate demands of modern electronic warfare.
The Replicator initiative operates outside traditional acquisition programs, acting as a forcing function to accelerate fielding through the Defense Innovation Unit (DIU) and commercial partnerships.2 Phase one, known as Replicator 1 or all-domain attritable autonomy (ADA2), focused on offensive swarm capabilities.2 Phase two, Replicator 2, targets counter-small unmanned aerial systems (C-sUAS), reflecting urgent lessons learned from the conflict in Ukraine.2 Despite the strategic ambition, the transition from concept to combat-ready mass has proven difficult.
2.2. The Reality of Fielding Autonomous Mass
While defense officials have routinely characterized the Replicator initiative as a success, external analyses highlight significant systemic friction. The Congressional Research Service observed that only “hundreds” rather than the promised “thousands” of systems materialized by the initial mid-2025 targets.3 The rapid 18-month timeline, while necessary for operational relevance, resulted in predictable delays due to a lack of upfront vetting, with some selected systems existing only as concepts during the selection phase.3
More critically, the initiative exposed a severe deficit in software integration. The DoD struggled to procure unified C2 software capable of seamlessly commanding and deconflicting diverse fleets of drones manufactured by different vendors.3 During exercises in austere environments, such as testing grounds in Alaska, drone prototypes frequently failed to launch, missed targets, or crashed due to persistent technical glitches and integration failures with existing command structures.3 This indicates that hardware procurement is insufficient without an equally robust investment in the systemic software required to operate the fleet.
3. Typology and Economics of the Unmanned Fleet
To effectively manage airspace and logistics, leadership must categorize the unmanned fleet based on cost, survivability, and mission profile. The conflict in Ukraine has invalidated the pre-war binary of distinguishing only between expendable ammunition and highly survivable manned platforms.14 Modern military force architecture now recognizes a spectrum of unmanned assets.
The U.S. military has formally begun categorizing collaborative combat aircraft (CCA) and drones into three distinct tiers to guide acquisition and airspace integration strategies.16
| Drone Category | Estimated Cost Cap | Mission Profile | Recovery Expectation |
| Expendable | Under $3 Million | Single-use kinetic strikes, high-risk ISR. Designed to be lost after a single mission. | Assured Loss |
| Attritable | $3 Million to $10 Million | Multi-use swarming, forward reconnaissance. Expected to fly multiple missions but “may not return.” | High Risk Tolerance |
| Exquisite | Over $25 Million | Long-endurance ISR, high-altitude command relays (e.g., RQ-4 Global Hawk). | Full Recovery Required |
Data indicates that while attritable and expendable drones offer significantly lower acquisition costs and eliminate the financial burden of man-rating, their lifecycle economics are complex.17 Traditional exquisite drones, such as the MQ-9 Reaper or RQ-4 Global Hawk, boast favorable cost-per-flight-hour metrics compared to manned aircraft.18 However, attritable drones rely on single-engine configurations, rendering them vastly less reliable than manned equivalents.17 The financial viability of an attritable drone fleet is contingent upon balancing the lower unit cost against the operational requirement to continuously replace lost airframes.17
4. Systemic Logistics and Distributed Manufacturing
4.1. The Logistical Footprint of Drone Swarms
The deployment of attritable mass fundamentally alters military logistics. Traditional airpower relies on centralized hub-and-spoke supply chains, wherein large aircraft deliver munitions to secure airbases, which are then serviced by highly trained maintenance squadrons.19 In a contested environment characterized by long-range precision fires, these centralized hubs are highly vulnerable.20
Attritable drone swarms require a dispersed, localized logistical footprint. While the airframes themselves may be considered expendable, the infrastructure to launch, recover, and sustain them is not. Operating thousands of drones necessitates modular recovery systems capable of arresting varying sizes of UAVs on the flight decks of amphibious transport docks or austere forward operating bases.22 Furthermore, managing continuous flight operations requires dedicated infrastructure for payload telemetry validation, automated flight-authorization systems, and rapid battery swapping.23 Without these systemic logistical foundations, the generation of combat drone sorties will quickly culminate.
4.2. Fabrication at the Tactical Edge (FATE)
To alleviate the strain on trans-oceanic supply chains and rapidly adapt to battlefield realities, the DoD must transition toward distributed manufacturing. The paradigm of(https://ndupress.ndu.edu/Media/News/News-Article-View/Article/4366244/fabrication-at-the-tactical-edge/) (FATE) leverages additive manufacturing and artificial intelligence to colocate production with the warfighter.24
In modern conflict, the ability to adapt hardware is as critical as the initial design. Utilizing advanced engineering-grade polymers and carbon-fiber composite 3D printing, aerospace engineers can reduce the lead time for producing mission-critical UAV components from four weeks to four days, achieving structural designs that traditional CNC machining cannot match.25 By deploying expeditionary manufacturing hubs on naval vessels or heavy airlift aircraft, military units can produce customized drone mounts, repair damaged airframes, and integrate new sensors on-demand.24 This localized production capability shortens the supply line and ensures that hardware evolves synchronously with tactical requirements.
5. DevSecOps and the Software Deficit
5.1. The Necessity of Rapid Software Evolution
A drone swarm is defined not by its composite airframe, but by its underlying software architecture. The conflict in Ukraine has demonstrated that static conceptual frameworks and rigid software quickly lose operational viability. Drones that are effective one month may become entirely obsolete the next due to the rapid adaptation of adversarial electronic warfare (EW) and GPS spoofing.15 To survive, the control logic, navigation algorithms, and targeting software of the drone fleet must be updated continuously.
The DoD’s traditional approach to software development—characterized by prolonged testing cycles and point-in-time security authorizations—is dangerously inadequate for this environment.14 To achieve true operational resilience, the military must fully embrace Development, Security, and Operations (DevSecOps) methodologies.30 DevSecOps integrates security directly into the continuous integration and continuous deployment (CI/CD) pipeline, enabling software factories to push updates to drones in the field securely and instantaneously.29
5.2. Lessons from Commercial-First Innovation
The acceleration of drone warfare requires commercial-first innovation pathways. In Ukraine, the integration of commercial technology and the establishment of real-time digital interfaces between frontline operators and software engineers resulted in an innovation cycle compressed from years to mere weeks.32 Initiatives like the Brave1 platform facilitated rapid capital deployment, increasing defense tech investment one-hundred-fold between 2023 and 2025.32
By utilizing an app-based feedback loop similar to commercial software ecosystems, forces can identify EW vulnerabilities in real-time, allowing developers to patch drone firmware and deploy the update back to the front lines almost immediately.33 If the DoD is to successfully operate Replicator platforms, it must move beyond hardware procurement and cultivate an agile software ecosystem capable of delivering continuous, over-the-air updates to the swarm.35
6. The Fratricide Threat and Procedural Control Breakdown
6.1. Historical Context and the Operator’s Dilemma
Combat identification (CID) has historically been one of the most persistent challenges in joint operations. During the Persian Gulf War, studies indicated that up to 17 percent of fratricide incidents could have been prevented with the widespread implementation of IFF devices on combat vehicles.36 The proliferation of small, low-cost drones has effectively reset this baseline, drastically escalating the risk of blue-on-blue engagements.
On a tactical air defense display, small military drones without broadcasting IFF appear as generic unidentified radar tracks, commonly referred to as “dots”.7 Because attritable drones physically resemble the commercial off-the-shelf (COTS) platforms utilized by adversaries, radar cross-sections and visual profiles offer no reliable method for distinguishing friend from foe.7 When airspace becomes saturated with hundreds of these unidentified tracks, the cognitive burden on air defense operators becomes overwhelming. In these scenarios, operators face a lethal dilemma: withhold fires and risk an adversary swarm destroying critical friendly infrastructure, or engage the tracks indiscriminately, risking the destruction of friendly drone assets or adjacent ground units.38
6.2. The Failure of Legacy Procedural Control
Historically, militaries have mitigated fratricide through procedural control. Procedural control relies on the segregation of airspace through Airspace Coordinating Measures (ACMs), Fire Support Coordination Measures (FSCMs), and Restricted Operating Zones (ROZs).10 For instance, a commander might designate a specific altitude block or geographic corridor exclusively for friendly UAS operations during a set time window, prohibiting all surface-to-air fires within that volume.38
While procedural control is effective for managing a limited number of manned sorties, it collapses under the weight of massive drone integration. Procedural deconfliction is inherently rigid; it requires extensive pre-planning, continuous voice communications, and strict adherence to a daily Airspace Control Order (ACO).4 Drone swarms, however, derive their tactical advantage from dynamic maneuverability, adapting their formations autonomously to optimize sensor coverage and exploit enemy vulnerabilities.43 Confining a swarm to a predetermined, rigid geographic box negates its utility. Furthermore, when the airspace is saturated, the manual clearance of fires through a Joint Air-Ground Integration Center (JAGIC) introduces fatal latency into the kill chain, preventing timely responses to pop-up adversary threats.13
7. Scalable Combat Identification: Reimagining IFF
7.1. The SWaP Challenge of Mode 5 Micro-IFF
The established standard for secure combat identification in the U.S. military and NATO is the Mark XIIB Mode 5 IFF transponder.44 Mode 5 utilizes spread-spectrum radio transmissions that are highly resistant to adversarial jamming and interception. It encrypts data with keys that rotate every few seconds, positively distinguishing friendly aircraft and responding to both lethal and non-lethal interrogations.46
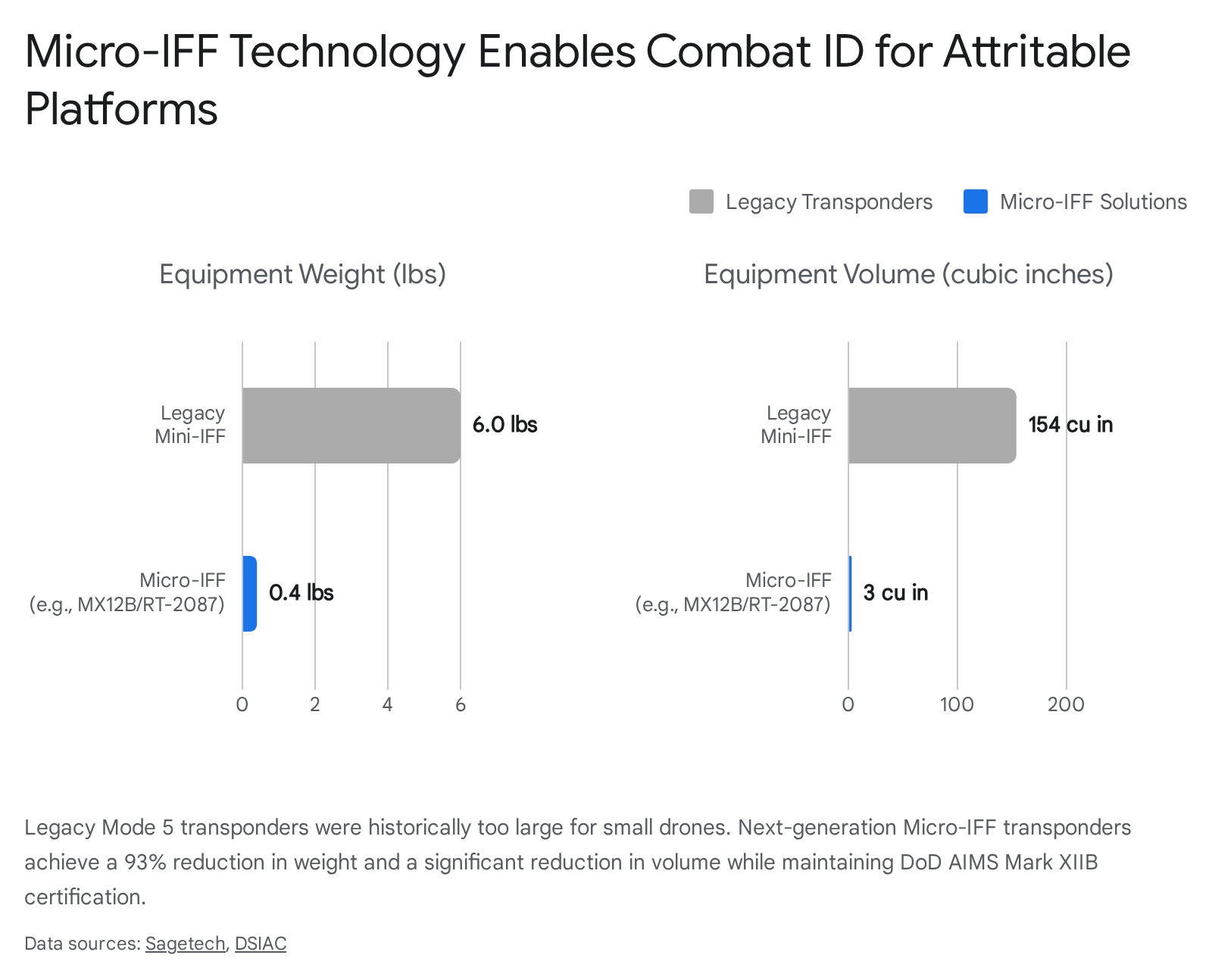
The primary barrier to implementing Mode 5 IFF on attritable drone swarms has been Size, Weight, and Power (SWaP) constraints. Legacy military Mode 5 transponders are excessively large for small UAVs, frequently weighing over six pounds and occupying vital payload space that could otherwise be utilized for sensors or munitions.8
However, recent engineering breakthroughs have successfully miniaturized this technology. Defense contractors have developed Micro-IFF transponders, such as the Sagetech MX12B and the uAvionix RT-2087/ZPX, which maintain full DoD AIMS Mark XIIB certification while drastically reducing their physical footprint.8 These modern transponders weigh less than a pound and consume a fraction of the power required by legacy systems, making encrypted combat identification viable for Group 1 and Group 2 drones.8
7.2. Cryptographic Key Management and Spectrum Congestion
While Micro-IFF solves the physical SWaP limitations, it does not resolve the security and spectrum challenges associated with scaling Mode 5 to thousands of platforms. Mode 5 functionality requires an external cryptographic computer, such as the KIV-77 or KIV-78, or an internal crypto module.44 Deploying highly classified cryptographic keys on attritable platforms designed to operate forward and potentially crash in enemy territory introduces a severe security vulnerability.
If an adversary recovers an intact attritable drone, they could theoretically extract cryptographic material or analyze the control logic.50 To mitigate this, systems employ “zeroize” functions that wipe the cryptographic keys upon loss of power or unauthorized tampering.51 However, continuously authenticating, synchronizing, and rotating keys across a rapidly maneuvering swarm of thousands of drones creates immense computational overhead and requires advanced group key management protocols that legacy C2 networks struggle to support.52
Furthermore, widespread adoption of Mode 5 creates an RF spectrum bottleneck. Mode 5 replies broadcast on the 1090 MHz frequency, while interrogations occur on 1030 MHz.45 In a congested theater where thousands of friendly and allied drones are simultaneously queried by air defense radars, the sheer volume of RF traffic can cause signal collisions and latency, effectively blinding the combat identification network.55
8. Alternative Identification Modalities
Given the limitations of scaling Mode 5 IFF, the DoD must invest in complementary identification technologies that operate outside the congested 1030/1090 MHz spectrum and reduce reliance on highly classified cryptographic keys.
8.1. Optical and Laser Interrogation
A highly promising alternative to RF-based IFF is the use of cryptographically encoded optical lasers. Systems currently under development allow counter-UAS platforms to emit a non-visible laser toward an unidentified drone.56 If the drone is friendly, its onboard sensor verifies the laser’s cryptographic signature and immediately transmits a radio-silent, modulated near-infrared (NIR) or short-wave infrared (SWIR) light sequence confirming its identity.56 This optical handshake occurs in less than 200 milliseconds, allowing defensive effectors to swiftly disengage from friendly assets and target hostile tracks.56 Because this process relies on light rather than radio waves, it is immune to RF jamming and does not contribute to spectrum congestion.
8.2. Artificial Intelligence and Behavioral Tracking
Modern air defense networks increasingly incorporate optical sensors paired with AI to track and classify drones based on visual signatures and flight behavior.57 High-resolution cameras and thermal imaging can detect specific drone models, while sensor fusion engines analyze the platform’s speed, trajectory, and swarming characteristics.57 By continuously monitoring the airspace, these AI systems can autonomously identify the predictable, pre-programmed flight behaviors of friendly logistics drones, distinguishing them from the aggressive maneuver patterns of adversary attack swarms.
8.3. Military Adaptations of Civil Remote ID
The Federal Aviation Administration (FAA) has mandated Remote ID for commercial and civilian drones to manage domestic airspace. Standard Remote ID broadcasts the drone’s unique serial number, latitude, longitude, altitude, velocity, and the pilot’s control station location via Wi-Fi or Bluetooth.59
While broadcasting the location of a pilot’s control station is unacceptable in a combat theater due to the immediate risk of counter-battery fire, the underlying concept of a localized, continuous broadcast can be adapted.61 The DoD could implement an encrypted, military-specific variant of Direct Remote ID that transmits authenticated telemetry over tactical mesh networks. This would provide localized identification for drone swarms within specific sectors, supplementing high-level Mode 5 radar tracks and providing necessary situational awareness to dismounted ground units without broadcasting their exact positions to the adversary.60
| Identification Modality | Primary Mechanism | Advantages | Vulnerabilities |
| Mode 5 Micro-IFF | Encrypted RF Interrogation (1030/1090 MHz) 45 | AIMS-certified, highly secure, integrates with legacy radars.46 | Spectrum congestion, requires complex crypto key management.52 |
| Optical/Laser ID | Modulated SWIR/NIR light sequences 56 | Radio-silent, immune to RF jamming, sub-200ms response time.56 | Requires line-of-sight, performance degraded by severe weather. |
| Military Remote ID | Encrypted localized broadcast (Bluetooth/Wi-Fi) 59 | Low SWaP, provides continuous telemetry without active interrogation.62 | Range limited to localized tactical networks, risk of signal interception. |
| Behavioral AI | Sensor fusion analyzing flight trajectories 57 | Passive detection, no transponder required on the drone.57 | Computationally intensive, potential for adversary spoofing of friendly behavior. |
9. Transitioning to Automated, Intent-Based Airspace Deconfliction
To safely manage the sheer volume of drone traffic and prevent fratricide without stalling operational momentum, airspace management must evolve from rigid procedural rules to dynamic, intent-based automation.
9.1. ASTARTE and Intent-Based Routing
The Defense Advanced Research Projects Agency (DARPA), in collaboration with the Army and Air Force, has pioneered automated airspace deconfliction through the Air Space Total Awareness for Rapid Tactical Execution (ASTARTE) program.5 ASTARTE provides an accurate, real-time common operational picture of the airspace, integrating seamlessly with the Army’s Integrated Mission Planning and Airspace Control Tools (IMPACT) software.9
Unlike procedural control, which closes entire blocks of airspace for extended periods, ASTARTE utilizes an intent-based model. By continuously analyzing the telemetry, mission parameters, and intended flight paths of all friendly assets, the software can generate complex route alternatives in seconds.9 This enables automated flight-path planning that successfully deconflicts manned aircraft, unmanned swarms, and the trajectories of outgoing artillery fire within the same airspace.9 By automating these deconfliction tasks, ASTARTE drastically reduces the procedural burden on commanders and mitigates the human error that often leads to fratricide.9
9.2. Dynamic Geofencing and Collaborative Autonomy
To further manage spatial separation at the tactical edge, automated systems employ dynamic geofencing. Dynamic geofencing envelops a UAS or an entire swarm within a virtual, three-dimensional keep-in or keep-out volume.63 Rather than remaining static, these geofenced volumes adjust in real-time based on the drone’s velocity, altitude, and surrounding traffic.63
When combined with multi-agent reinforcement learning, dynamic geofencing allows drone swarms to exhibit collaborative autonomy.65 If a swarm detects incoming adversary fire or an unexpected friendly aircraft entering its sector, the swarm’s internal logic recalculates the route for the entire formation.65 The swarm behaves as a single, flexible organism, dynamically shifting its geofenced boundaries to avoid collisions while maintaining mission continuity, all without requiring manual intervention from a ground operator.66
10. Air Defense Integration and the JADC2 Architecture
10.1. The Integrated Battle Command System (IBCS)
Automated airspace deconfliction must be intrinsically linked to air defense fire control to effectively prevent fratricide. The materiel solution driving this integration is the Army’s Integrated Battle Command System (IBCS).11 For decades, air and missile defense systems operated in isolated silos; a Patriot battery could not utilize target data generated by a Sentinel radar. IBCS shatters these silos by networking disparate sensors and effectors across a unified Integrated Fire Control Network (IFCN).11
Operating under the doctrine of “any sensor, best shooter,” IBCS aggregates data from ground radars, aerial nodes, and satellite feeds to create a Single Integrated Air Picture.11 When a saturated drone threat emerges, IBCS utilizes AI platforms, such as Anduril’s Lattice software, to rapidly process the incoming data.13 Selected for the IBCS Maneuver (IBCS-M) program, Lattice acts as a next-generation fire control platform that fuses sensor data, evaluates IFF returns, and automates target prioritization.13 This capability compresses the decision loop, allowing a single operator to manage multiple autonomous threats simultaneously while ensuring that friendly swarms—identified and tracked by the network—are strictly avoided by defensive effectors.13
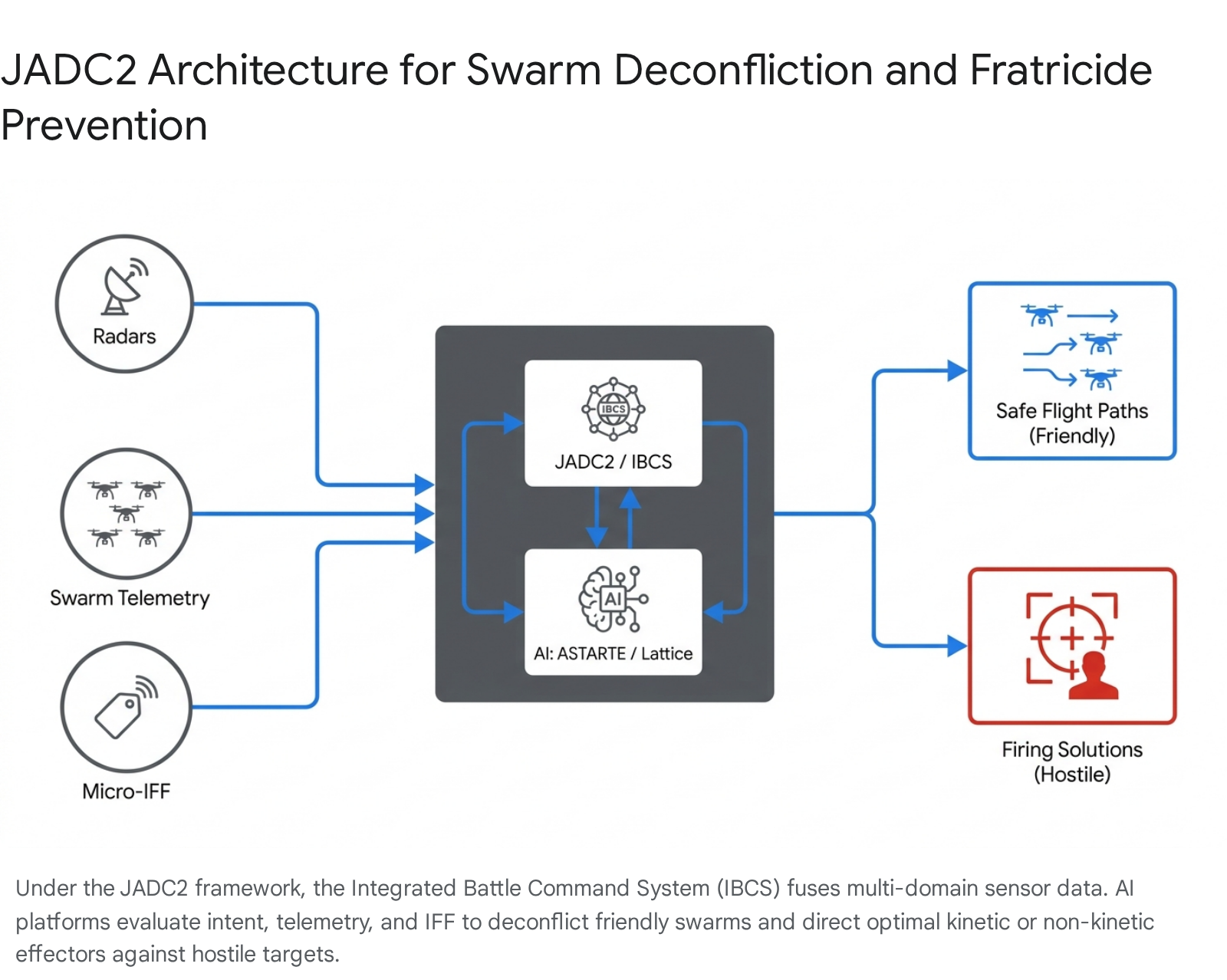
10.2. Joint All-Domain Command and Control (JADC2)
The integration capabilities of IBCS form the foundation for the broader Joint All-Domain Command and Control (JADC2) initiative. JADC2 seeks to connect the distributed sensors, shooters, and C2 nodes of all U.S. military branches and allied partners into a single, cohesive network.69
In a congested theater, a localized air defense network is insufficient. Threat data must be shared seamlessly across domains. For example, during JADC2 exercises over the Baltic Sea, allied forces successfully utilized a Dutch F-35 as an aerial sensor node, feeding real-time targeting data down to the 10th Army Air Missile Defense Command at Ramstein Air Base.71 By networking platforms across domains, JADC2 creates a multi-layered defense web that reduces sensor-to-shooter timelines and ensures that a unified air picture is maintained across the theater, significantly lowering the probability of an isolated unit engaging a friendly asset.71
11. Telemetry, Bandwidth, and the Electromagnetic Spectrum
The realization of the JADC2 vision relies entirely on the resilience of the underlying communication networks. Historically, the Link 16 tactical data link has been the primary conduit for sharing critical battlefield information and IFF tracks among U.S. and NATO forces.72 However, Link 16 was originally architected for a limited number of high-value platforms, operating in a less congested electromagnetic spectrum.72
The integration of thousands of attritable drones, all continuously broadcasting telemetry and receiving automated routing instructions, places unsustainable strain on legacy RF networks.72 Furthermore, traditional RF communications are highly susceptible to adversary jamming, spoofing, and interception, making them unreliable in a highly contested Anti-Access/Area Denial (A2/AD) environment.74
To overcome these bandwidth constraints and enhance security, the DoD is transitioning toward advanced data transport mechanisms. Innovations such as Concurrent Multiple Reception (CMR) allow Link 16 radios to receive multiple messages simultaneously, easing network congestion.72 More significantly, the Space Development Agency (SDA) is constructing an optical communications network utilizing Proliferated Low Earth Orbit (p-LEO) satellite constellations.74 This network relies on lasers to transmit data between satellites and terrestrial platforms, offering massively increased data throughput, lower latency, and an inherent resistance to RF jamming and interception.74 Shifting swarm C2 and telemetry to optical networks ensures that critical identification and deconfliction data remains uninterrupted, even when the tactical RF spectrum is severely degraded.
12. Interoperability via Modular Open Systems Approach (MOSA)
The sheer diversity of platforms intended for integration—ranging from commercial quadcopters to advanced attritable strike drones—demands strict adherence to standardization. To ensure that systems can seamlessly communicate and share IFF data within the JADC2 architecture, the DoD has mandated the Modular Open Systems Approach (MOSA).77
MOSA is an acquisition and design strategy that abandons proprietary, closed-architecture software in favor of open standards.77 By separating a system into major functional elements that communicate via consensus-based interfaces, MOSA prevents vendor lock-in.77 Standards such as Open Mission Systems (OMS) and the Universal Command and Control Interface (UCI) allow the DoD to rapidly upgrade specific components of a system without undertaking a complete redesign.79
In the context of drone swarms, MOSA guarantees that a new sensor developed by an agile startup can be instantly integrated into the Army’s IBCS network, or that a software patch addressing a novel EW threat can be pushed to drones manufactured by multiple different defense contractors.79 Furthermore, initiatives like the Defense Innovation Unit’s Blue UAS Framework maintain a roster of interoperable, NDAA-compliant drone components and secure datalinks, streamlining the procurement process and ensuring that all newly acquired attritable platforms are natively compatible with joint C2 and deconfliction networks from the moment they are deployed.83
13. Lessons from Joint Experimentation: Project Convergence
The theoretical frameworks of JADC2 and automated airspace management are continuously evaluated through Project Convergence, the Army’s campaign of persistent joint and multinational experimentation.84 Exercises such as Capstone 5 at Fort Irwin and Capstone 6 at Kirtland Air Force Base bring together thousands of participants from the Air Force, Space Force, Army, Navy, and coalition partners to stress-test emerging technologies in realistic, contested environments.85
These exercises consistently underscore that airspace deconfliction remains a primary friction point. When operators are introduced to massive influxes of small UAS—both simulated friendly swarms and opposition force drones—the saturation rapidly overwhelms traditional command posts.87 However, the experiments also validate the necessity of intent-based tools and AI-driven battle management systems. By utilizing platforms like the Tactical Operations Center-Light (TOC-L) and integrating data directly into the Army’s Next-Generation Command and Control systems, units are learning to manage the cognitive load of a drone-dominant battlefield.84 The critical takeaway from Project Convergence is that the technology to prevent fratricide exists, but it requires continuous, cross-domain rehearsal to refine the human-machine interfaces that commanders will rely upon in combat.
14. Strategic Recommendations for DoD Leadership
The successful integration of attritable mass requires systemic overhauls that extend far beyond the procurement of the physical vehicles. To mitigate the severe risks of blue-on-blue engagements and effectively manage saturated airspace, DoD leadership should prioritize the following strategic initiatives:
- Accelerate the Fielding of Intent-Based Airspace Management: The DoD must officially transition airspace doctrine away from strictly procedural control. Programs like ASTARTE and IMPACT should be scaled and integrated across all combatant commands to provide automated, AI-enabled routing that accommodates the dynamic maneuvers of autonomous swarms while safely deconflicting joint fires.
- Mandate SWaP-Optimized, Multi-Modal Combat Identification: Relying solely on legacy RF-based Mode 5 IFF is unsustainable for massive drone fleets. Leadership must enforce the integration of AIMS-certified Micro-IFF systems on larger attritable platforms, while concurrently accelerating the commercialization of alternative modalities, such as optical/laser identification and encrypted military Remote ID, to operate outside the congested RF spectrum.
- Modernize Cryptographic Key Management for Expendable Assets: Establish new protocols for managing encrypted IFF on platforms expected to be lost in combat. This requires implementing highly autonomous zeroize functions, localized key generation protocols, and dynamic key rotation frameworks that secure the network without crippling the swarm if individual nodes are disconnected.
- Enforce MOSA Across All Autonomous Initiatives: Ensure that all drones, sensors, and effectors acquired under programs like Replicator strictly comply with Open Mission Systems (OMS) standards. The ability to utilize DevSecOps software factories to push over-the-air updates directly to the tactical edge is the only proven method to outpace adversary electronic warfare and maintain accurate combat identification.
- Expand the IBCS Architecture to the Tactical Edge: Ensure that the “any sensor, best shooter” capabilities of the Integrated Battle Command System (IBCS) and AI fire-control software like Lattice are pushed down to the platoon and company echelons. Air defense and airspace deconfliction cannot remain siloed at the division level; forward-deployed units require localized, automated threat processing to survive and maneuver in a saturated drone environment.
- Invest in Distributed Manufacturing and Optical Logistics: To sustain operations in contested theaters, the DoD must invest in Fabrication at the Tactical Edge (FATE) by deploying expeditionary 3D printing hubs. Furthermore, to support the massive data requirements of JADC2 and swarm telemetry, transition critical C2 networks toward Space Development Agency (SDA) optical laser communications, ensuring resilience against adversarial RF jamming.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Sources Used
- DOD’s Replicator Program:, accessed April 24, 2026, https://docs.house.gov/meetings/AS/AS35/20231019/116484/HHRG-118-AS35-Wstate-GreenwaltW-20231019.pdf
- Deep Dive: Pentagon’s Replicator Initiative Raises Questions | Inkstick, accessed April 24, 2026, https://inkstickmedia.com/deep-dive-pentagons-replicator-initiative-raises-questions/
- DoD promised a ‘swarm’ of attack drones. We’re still waiting …, accessed April 24, 2026, https://responsiblestatecraft.org/replicator/
- AFDP 3-52, Airspace Control – Air Force Doctrine, accessed April 24, 2026, https://www.doctrine.af.mil/Portals/61/documents/AFDP_3-52/3-52-AFDP-AIRSPACE-CONTROL.pdf
- Real-time Airspace Awareness and De-confliction for Future Battles – DARPA, accessed April 24, 2026, https://www.darpa.mil/news/2020/airspace-awareness-deconfliction
- Toward Automating Airspace Management – SoarTech, accessed April 24, 2026, https://soartech.com/wp-content/uploads/2021/11/AutoATC-Paper-CISDA-vSUBMIT-final-tag.pdf
- Is That Our “DOT”? – Inside Unmanned Systems, accessed April 24, 2026, https://insideunmannedsystems.com/is-that-our-dot/
- Implementing Mode 5 IFF Transponders on UAS: What to Consider – Sagetech Avionics, accessed April 24, 2026, https://sagetech.com/wp-content/uploads/2025/01/Implementing-Mode-5-IFF-Transponders-On-UAS-What-To-Know.pdf
- DARPA, Services Demonstrate Battlefield Airspace Deconfliction Software, accessed April 24, 2026, https://www.darpa.mil/news/2023/battlefield-airspace-deconfliction-software
- Airspace as a Weapon | Article | The United States Army, accessed April 24, 2026, https://www.army.mil/article/280151/airspace_as_a_weapon
- IBCS And The Future Of Offensive And Defensive Integrated Fires | Article – U.S. Army, accessed April 24, 2026, https://www.army.mil/article/291023/ibcs_and_the_future_of_offensive_and_defensive_integrated_fires
- How The Army Will Use Its Super Integrated Air Defense System – The War Zone, accessed April 24, 2026, https://www.twz.com/sponsored-content/how-the-army-will-use-its-super-integrated-air-defense-system
- Anduril Selected for U.S. Army’s Integrated Battle Command System Maneuver Program, accessed April 24, 2026, https://www.anduril.com/news/anduril-selected-for-u-s-army-s-integrated-battle-command-system-maneuver-program
- Lessons from the Ukraine Conflict: Modern Warfare in the Age of Autonomy, Information, and Resilience – CSIS, accessed April 24, 2026, https://www.csis.org/analysis/lessons-ukraine-conflict-modern-warfare-age-autonomy-information-and-resilience
- Drone Warfare in Ukraine: From Myths to Operational Reality – Part 1, accessed April 24, 2026, https://researchcentre.army.gov.au/library/land-power-forum/drone-warfare-ukraine-myths-operational-reality-part-1
- Artificial Intelligence (AI) for Weapons Systems – DSIAC, accessed April 24, 2026, https://dsiac.dtic.mil/wp-content/uploads/2024/11/SOAR_DSIAC_Attritable-Unmanned-Aircraft-Systems-Conceptualization-and-Key-Players_11252024.pdf
- Is it known how much ”CCA” type drones cost per hour to run compared to 4th and 5th gen aircraft? – Reddit, accessed April 24, 2026, https://www.reddit.com/r/WarCollege/comments/1qai8b6/is_it_known_how_much_cca_type_drones_cost_per/
- The US and its UAVs: A Cost-Benefit Analysis – American Security Project, accessed April 24, 2026, https://www.americansecurityproject.org/the-us-and-its-uavs-a-cost-benefit-analysis/
- The Last Mile Problem: Re-Thinking Modern Aerial Logistics – ParaZero Technologies, accessed April 24, 2026, https://parazero.com/2025/11/11/the-last-mile-problem-re-thinking-modern-aerial-logistics/
- Achtung Swarm – Marine Corps University, accessed April 24, 2026, https://www.usmcu.edu/Outreach/Marine-Corps-University-Press/MCU-Journal/JAMS-vol-16-no-2/Achtung-Swarm/
- Logistics While Under Attack: Key to a CCA Force Design, accessed April 24, 2026, https://www.mitchellaerospacepower.org/app/uploads/2025/03/Logistics-While-Under-Attack-Key-to-a-CCA-Force-Design-WEB.pdf
- 24.2 SBIR – Recovery System for Group 3–5 UAVs for Sea-Based Operations – Navy, accessed April 24, 2026, https://www.navysbir.com/n24_2/N242-083.htm
- Drone‐Assisted Organ Transport: A Scoping Review of Clinical, Regulatory, and System Readiness – PMC, accessed April 24, 2026, https://pmc.ncbi.nlm.nih.gov/articles/PMC12699177/
- Fabrication at the Tactical Edge – NDU Press – National Defense University, accessed April 24, 2026, https://ndupress.ndu.edu/Media/News/News-Article-View/Article/4366244/fabrication-at-the-tactical-edge/
- Aerospace 3D Printing: Building Field-Ready Drones in Hours, accessed April 24, 2026, https://www.phillipscorp.com/india/aerospace-3d-printing-for-drone-manufacturing/
- Additive Manufacturing and 3D Printing for Drone Manufacturers, accessed April 24, 2026, https://www.unmannedsystemstechnology.com/expo/additive-manufacturing-3d-printing/
- Moving Toward Defense as a Service – War on the Rocks, accessed April 24, 2026, https://warontherocks.com/2024/11/moving-toward-defense-as-a-service/
- The End of GPS Reliability Is Reshaping Modern Combat Strategy | Markets Insider, accessed April 24, 2026, https://markets.businessinsider.com/news/stocks/the-end-of-gps-reliability-is-reshaping-modern-combat-strategy-1036048386
- Pentagon Revamps Tech Strategies to Advance DevSecOps | GovCIO Media & Research, accessed April 24, 2026, https://govciomedia.com/pentagon-revamps-devsecops-updates-for-software-delivery/
- The State of DevSecOps – DoD CIO, accessed April 24, 2026, https://dodcio.defense.gov/Portals/0/Documents/Library/DevSecOpsStateOf.pdf
- Navigating the Drone Threat: Technology, Policy, and the Path Ahead (Part 2) | Amentum, accessed April 24, 2026, https://www.amentum.com/news/navigating-the-drone-threat-technology-policy-and-the-path-ahead-part-2/
- Securing Ukraine’s Future in Europe: Ukraine’s Defense Industrial Base—An Anchor for Economic Renewal and European Security | Council on Foreign Relations, accessed April 24, 2026, https://www.cfr.org/articles/securing-ukraines-future-in-europe-ukraines-defense-industrial-base-an-anchor-for-economic-renewal-and-european-security
- Unleashing U.S. Military Drone Dominance: What the United States Can Learn from Ukraine, accessed April 24, 2026, https://www.csis.org/analysis/unleashing-us-military-drone-dominance-what-united-states-can-learn-ukraine
- Technological Evolution on the Battlefield – CSIS, accessed April 24, 2026, https://www.csis.org/analysis/chapter-9-technological-evolution-battlefield
- Defense Software for a Contested Future: Agility, Assurance, and Incentives (2025), accessed April 24, 2026, https://www.nationalacademies.org/read/29129/chapter/4
- Integrating Technology to Reduce Fratricide – DTIC, accessed April 24, 2026, https://apps.dtic.mil/sti/tr/pdf/ADA487939.pdf
- FRATRICIDE: REDUCING THE FRICTION THROUGH TECHNOLOGY, accessed April 24, 2026, https://cgsc.contentdm.oclc.org/digital/api/collection/p4013coll3/id/1159/download
- The Evolution of Air Defense: Adapting to Emerging Threats – Army University Press, accessed April 24, 2026, https://www.armyupress.army.mil/Journals/Military-Review/English-Edition-Archives/September-October-2025/Air-Defense/
- Let Them Fly: To Generate Drone Combat Readiness, Army Installations Must Step Up, accessed April 24, 2026, https://mwi.westpoint.edu/let-them-fly-to-generate-drone-combat-readiness-army-installations-must-step-up/
- Joint Airspace Control, Doctrine Update 10-06 – DTIC, accessed April 24, 2026, https://apps.dtic.mil/sti/tr/pdf/ADA526037.pdf
- Army Airspace Management During Large-Scale Combat Operations – ALSSA, accessed April 24, 2026, https://www.alssa.mil/News/Article/2989031/army-airspace-management-during-large-scale-combat-operations/
- Airspace Control In The Combat Zone – GovInfo, accessed April 24, 2026, https://www.govinfo.gov/content/pkg/GOVPUB-D301-PURL-LPS96218/pdf/GOVPUB-D301-PURL-LPS96218.pdf
- Designing for Doctrine: Decentralized Execution in Unmanned Swarms – Air University, accessed April 24, 2026, https://www.airuniversity.af.edu/Wild-Blue-Yonder/Articles/Article-Display/Article/2703656/designing-for-doctrine-decentralized-execution-in-unmanned-swarms/
- Key Considerations for Mode 5 IFF Micro Transponder UAS Implementation, accessed April 24, 2026, https://www.unmannedsystemstechnology.com/feature/key-considerations-for-mode-5-iff-micro-transponder-uas-implementation/
- IFF Transponders for Drones, UAVs & UAS – Unmanned Systems Technology, accessed April 24, 2026, https://www.unmannedsystemstechnology.com/expo/iff-transponders/
- Mode 5 Micro-IFF For Small Drones Takes Off – Sagetech Avionics, accessed April 24, 2026, https://sagetech.com/news-and-events/mode-5-micro-iff-for-small-drones-takes-off/
- Micro IFF for Secure Airspace Awareness Across Domains – uAvionix, accessed April 24, 2026, https://uavionix.com/defense/
- Small/Micro Identification Friend or Foe (IFF) Transponder Survey – DSIAC, accessed April 24, 2026, https://dsiac.dtic.mil/technical-inquiries/notable/small-micro-iff-transponder-survey/
- Overcoming the Mode 5 SWaP Challenge in the RQ-21A STUAS – uAvionix, accessed April 24, 2026, https://uavionix.com/blog/overcoming-the-mode-5-swap-challenge-in-the-rq-21a-stuas/
- A Survey of Security Challenges and Solutions for UAS Traffic Management (UTM) and small Unmanned Aerial Systems (sUAS) – arXiv, accessed April 24, 2026, https://arxiv.org/pdf/2601.08229
- Securing Unmanned Devices in Critical Infrastructure: A Survey of Hardware, Network, and Swarm Intelligence – MDPI, accessed April 24, 2026, https://www.mdpi.com/2079-9292/15/6/1204
- Secure Communication in Drone Networks: A Comprehensive Survey of Lightweight Encryption and Key Management Techniques – MDPI, accessed April 24, 2026, https://www.mdpi.com/2504-446X/9/8/583
- Enhancing Drone Security: Advanced IFF Code Management and Rotation Strategies, accessed April 24, 2026, https://decentcybersecurity.eu/enhancing-drone-security-advanced-iff-code-management-and-rotation-strategies/
- Scalable Key Management for Tactical Swarms Hunter C. Gatewood – DSpace@MIT, accessed April 24, 2026, https://dspace.mit.edu/bitstream/handle/1721.1/123141/1128823189-MIT.pdf?sequence=1&isAllowed=y
- A Comprehensive Approach to Countering Unmanned Aircraft Systems – Joint Air Power Competence Centre, accessed April 24, 2026, https://www.japcc.org/wp-content/uploads/A-Comprehensive-Approach-to-Countering-Unmanned-Aircraft-Systems.pdf
- Allen Control Systems Releases New Drone ID Technology – Tectonic Defense, accessed April 24, 2026, https://www.tectonicdefense.com/allen-control-systems-releases-new-drone-id-technology/
- DedroneTracker.AI is the world’s leading drone detection software, accessed April 24, 2026, https://www.dedrone.com/products/drone-detection-software
- 10 Types of Counter-drone Technology to Detect and Stop Drones Today – Robin Radar, accessed April 24, 2026, https://www.robinradar.com/resources/10-counter-drone-technologies-to-detect-and-stop-drones-today
- Remote ID Requirements – Drone Law and Drone Attorney Assistance – Rupprecht Law, accessed April 24, 2026, https://jrupprechtlaw.com/remote-id-requirements/
- (PDF) Efficient Remote Identification for Drone Swarms – ResearchGate, accessed April 24, 2026, https://www.researchgate.net/publication/374549560_Efficient_Remote_Identification_for_Drone_Swarms
- Understanding Remote ID: A Comprehensive Guide – Drone Pilot Ground School, accessed April 24, 2026, https://www.dronepilotgroundschool.com/remote-id/
- Remote Identification of Drones | Federal Aviation Administration, accessed April 24, 2026, https://www.faa.gov/uas/getting_started/remote_id
- Airspace Geofencing and Flight Planning for Low-Altitude, Urban, Small Unmanned Aircraft Systems – MDPI, accessed April 24, 2026, https://www.mdpi.com/2076-3417/12/2/576
- A New Approach to Complex Dynamic Geofencing for Unmanned Aerial Vehicles, accessed April 24, 2026, https://www.researchgate.net/publication/355391217_A_New_Approach_to_Complex_Dynamic_Geofencing_for_Unmanned_Aerial_Vehicles
- Using Drone Swarms as a Countermeasure of Radar Detection | Journal of Aerospace Information Systems, accessed April 24, 2026, https://arc.aiaa.org/doi/10.2514/1.I011131
- AI-Powered Airspace Management: How Automated Data Service Providers (ADSPs) Will Shape the Future of UAS Integration and BVLOS Operations – Autonomy Global, accessed April 24, 2026, https://www.autonomyglobal.co/ai-powered-airspace-management-how-automated-data-service-providers-adsps-will-shape-the-future-of-uas-integration-and-bvlos-operations/
- Connecting sensors and effectors into one command and control system with IBCS, accessed April 24, 2026, https://breakingdefense.com/2023/10/ibcs-to-battleone-modernizing-air-and-missile-defense/
- Army picks Anduril to provide next-gen fire control platform for IBCS-M program, accessed April 24, 2026, https://defensescoop.com/2025/11/11/army-ibcs-maneuver-anduril-lattice-counter-uas/
- Joint All-Domain Command and Control (JADC2) – Missile Defense Advocacy Alliance, accessed April 24, 2026, https://www.missiledefenseadvocacy.org/defense-systems/joint-all-domain-command-and-control-jadc2/
- Joint Force Coordination for Full Scale Operations – Booz Allen, accessed April 24, 2026, https://www.boozallen.com/insights/defense/c2-command-and-control/joint-force-coordination-for-full-scale-operations.html
- JADC2: NATO’s Answer to the Threat of Drone Swarm Attacks – The National Interest, accessed April 24, 2026, https://nationalinterest.org/blog/reboot/jadc2-natos-answer-threat-drone-swarm-attacks-197128
- Expanding Link 16’s Reach Through Concurrent Multiple Reception (Sponsored Content), accessed April 24, 2026, https://www.afcea.org/signal-media/expanding-link-16s-reach-through-concurrent-multiple-reception-sponsored-content
- Tactical Data Links, Air Traffic Management, and Software Programmable Radios – Mitre, accessed April 24, 2026, https://www.mitre.org/sites/default/files/publications/white_tactical_data_links.pdf
- Pentagon contemplating eventual sunsetting of Link 16 as enthusiasm grows for optical communications | DefenseScoop, accessed April 24, 2026, https://defensescoop.com/2025/09/25/link-16-sda-optical-communications/
- https://comptroller.war.gov/Portals/45/Documents/defbudget/FY2026/budget_justification/pdfs/03_RDT_and_E/RDTE_Vol1_DARPA_MasterJustificationBook_PB_2026.xml, accessed April 24, 2026, https://comptroller.war.gov/Portals/45/Documents/defbudget/FY2026/budget_justification/pdfs/03_RDT_and_E/RDTE_Vol1_DARPA_MasterJustificationBook_PB_2026.xml
- Link 16 tactical data link communication via space: ‘A ground-breaking development’, accessed April 24, 2026, https://www.sda.mil/link-16-tactical-data-link-communication-via-space-a-ground-breaking-development/
- MOSA | NAVAIR, accessed April 24, 2026, https://www.navair.navy.mil/MOSA
- What is MOSA? – BAE Systems, accessed April 24, 2026, https://www.baesystems.com/en-us/definition/what-is-mosa
- Open Mission Systems (OMS) in a Nutshell – VDL, accessed April 24, 2026, https://www.vdl.afrl.af.mil/programs/oam/OMS_Marketing.pdf
- Open System Standards and Agile Acquisition – Defense Standardization Program, accessed April 24, 2026, https://www.dsp.dla.mil/portals/26/documents/publications/conferences/2018/dsp%20workshop%20july2018/dspworkshop-day4-180712/dspworkshop-4garrett-180712.pdf?ver=2018-08-01-150711-913
- Open Mission Systems (OMS) Overview and Update – Global Product Data Interoperability Summit, accessed April 24, 2026, https://gpdisonline.com/wp-content/uploads/2024/10/Chris-Garrett-Presentation-Sep-2024.pdf
- Open Mission Systems: The Standard Driving Defense Innovation, accessed April 24, 2026, https://www.lynx.com/blog/open-mission-systems-the-standard-driving-defense-innovation
- Blue UAS Framework: Comprehensive Overview for Defense Drone Manufacturers, accessed April 24, 2026, https://mobilicom.com/insight/blue_uas_framework/
- Project Convergence | U.S. Department of War, accessed April 24, 2026, https://www.war.gov/Spotlights/Project-Convergence/
- Training Tomorrow’s Fight: Project Convergence at Kirtland, accessed April 24, 2026, https://www.kirtland.af.mil/News/Article-Display/Article/4409854/training-tomorrows-fight-project-convergence-at-kirtland/
- Air Force, Army shaping the future of C2, together, accessed April 24, 2026, https://www.af.mil/News/Article-Display/Article/4155743/air-force-army-shaping-the-future-of-c2-together/
- Army summit presents lessons learned, identifies hurdles of the drone dominant future, accessed April 24, 2026, https://www.army.mil/article-amp/290518/army_summit_presents_lessons_learned_identifies_hurdles_of_the_drone_dominant_future
