Executive Overview
The integration of Unmanned Aircraft Systems (UAS) into public safety has transitioned from an experimental capability to a foundational element of modern emergency response infrastructure. Specifically, the Drone as First Responder (DFR) model represents a paradigm shift in law enforcement operations. Unlike traditional drone deployments, where an aircraft is transported to a scene by a ground unit and launched reactively, the DFR model utilizes prepositioned, remote-operated drones that launch immediately upon receiving a call for service.1 These systems provide real-time, high-definition aerial intelligence to dispatchers and responding officers, frequently arriving minutes before ground units can navigate urban traffic.3
Driven by advancements in automated docking stations, robust cellular connectivity, and streamlined federal regulatory processes, the adoption of DFR programs expanded significantly between 2024 and 2026.3 By 2025, the Law Enforcement Drone Association (LEDA) reported that approximately 6,000 police drone programs were operational nationwide, a fourfold increase largely catalyzed by the “Unleashing American Drone Dominance” Executive Order and subsequent Federal Aviation Administration (FAA) policy revisions.3 With the 2025 Verizon Frontline Public Safety Communications Survey projecting that daily drone use in public safety will triple over the next five years, DFR has moved from a theoretical concept to a tactical necessity.3
This analysis provides a comprehensive, exhaustive evaluation of DFR operations in the United States. It examines the tactical advantages of integrating these platforms into Computer-Aided Dispatch (CAD) systems, the operational impact of streamlined Beyond Visual Line of Sight (BVLOS) waivers, the critical necessity of an “aviation mindset” in program management, and the strategic mitigation of cybersecurity vulnerabilities inherent in drone telemetry.
The Operational Landscape and Tactical Application of DFR
The core objective of a DFR program is to acquire an “eye in the sky” prior to the arrival of ground units, fundamentally altering how law enforcement agencies allocate resources, manage critical incidents, and assess risk.3 Data collected from established programs demonstrates profound, measurable impacts on response times, officer safety, and call resolution efficiency across various operational contexts.6
Evolution from Reactive Deployments
Historically, public safety drones were utilized reactively. A patrol officer or dedicated aviation unit would transport the UAS in a vehicle, arrive at the scene of an ongoing incident, physically unpack the equipment, establish a safe launch perimeter, and deploy the aircraft.5 This sequential process inherently introduced significant delays, often rendering the drone ineffective for highly dynamic, rapidly evolving situations such as fleeing suspects or active threats.
The DFR model reverses this operational sequence. In a DFR configuration, first responders place drones strategically within a city, typically housed in weather-proof automated docking stations installed on building rooftops.3 Upon receiving a call for service, a certified remote pilot—operating from a central command center or Real-Time Crime Center (RTCC)—launches and controls the drone to respond to the scene.3 In advanced configurations, the launch and initial flight routing can be conducted autonomously.5 This immediacy enables law enforcement agencies to adapt their strategies in real time, ensuring a faster and more precise response to civic emergencies.9
Quantitative Impact on Resource Allocation
A primary metric for evaluating the efficacy of a DFR program is its capacity to clear calls without necessitating the dispatch of a patrol unit. Drones provide immediate situational awareness that allows dispatchers and field supervisors to assess the severity of an incident instantly.3 For example, in cases of reported traffic collisions, minor disturbances, or triggered alarms, an aerial assessment can confirm that the incident is minor, unfounded, or already resolved.3 This allows the call to be cleared entirely or handled by a civilian community service officer.3
Operational data spanning multiple jurisdictions indicates that this capability reduces unnecessary patrol dispatches by 15 to 24 percent.3 The Chula Vista Police Department in California, a pioneer in the DFR model, reported responding to 15,000 calls for service with their DFR program between 2018 and May 2023.10 Of those deployments, the department was able to clear 25 percent of the calls using only the drone, negating the need for ground intervention.9 Similarly, the Lakewood Police Department in Colorado, utilizing full-time remote pilots, was completing roughly 1,800 calls for service annually by 2025, operating with a public dashboard to ensure mission transparency.3 By filtering out low-priority or resolved incidents, DFR programs ensure that sworn personnel remain available for higher-priority emergencies, thereby optimizing fleet readiness and reducing overall emergency response times for the jurisdiction.3
Key Use Cases and Incident Capabilities
DFR deployments have proven highly effective across a wide spectrum of incident types. A comprehensive 60-day study of 1,779 DFR flights conducted between September 15, 2024, and November 14, 2024, revealed that the most frequent call types supported by drones included burglaries, retail thefts, vehicle thefts, and robberies.6 In these scenarios, drones routinely arrived in less than two minutes, capturing suspect locations, tracking movements, and guiding responding officers to successful apprehensions.6
The second most common deployment category involved assaults, domestic disturbances, and reports of individuals displaying weapons in a threatening manner.6 In these high-risk calls, DFR provides persistent tactical overwatch. This allows SWAT teams or patrol officers to track suspect movements, positively identify the presence of weapons, and maintain a safe standoff distance.3 This standoff capability is directly correlated with enhanced de-escalation strategies; officers can formulate a response plan based on objective, real-time intelligence rather than ambiguous initial dispatch reports, frequently leading to de-escalation instead of physical confrontation.3
The operational applications extend beyond direct law enforcement functions to encompass broader public safety mandates.
| Tactical Application | Operational Mechanism | Documented Impact / Benefit |
| Search and Rescue (SAR) | Drones equipped with dual Electro-Optical/Infrared (EO/IR) sensors cover impassable terrain. Modern systems utilize Automated Human Detection (AHD) to flag heat signatures or specific clothing colors. | Rapid location of missing individuals in dense brush or total darkness, significantly reducing search times compared to ground-based line searches.3 |
| Firefighting Operations | DFR units act as advance scouts, utilizing thermal imaging to identify the “seat” of a structural fire, assess roof integrity, and spot hazardous materials before fire crews make entry. | Enhances situational awareness for incident commanders, provides real-time mapping for brush fires, and protects property and personnel lives.3 |
| Active Shooter & Overwatch | DFR provides constant aerial overwatch, tracking suspect movements on rooftops or behind physical barriers such as fences. | Allows tactical teams to maintain distance and adapt strategies in real time, prioritizing information gathering without compromising human safety.3 |
| Traffic Collision Reconstruction | Drones capture high-definition aerial photography and video of accident sites to facilitate detailed accident reconstruction and analysis. | Reduces the time roadways are closed for investigation, improving traffic flow and safety for responding personnel.7 |
| Medical Payload Delivery | Advanced DFR systems utilize integrated winch systems to drop critical medical supplies directly to the scene of an emergency. | Delivery of automated external defibrillators (AEDs), Narcan, EpiPens, and tourniquets. Early intervention with AEDs via drone has led to a 46.2% survival rate.3 |
Case Study: Pearland Police Department
The operational evolution of DFR is clearly demonstrated by the Pearland Police Department in Texas. Serving a rapidly growing city of 129,600 residents across 49 square miles, the agency operates with 179 sworn police officers.12 Facing personnel shortages that impact first responders nationwide, Pearland PD utilized DFR to circumvent urban traffic and offer advanced incident scene assessments.12
Operating near Houston Hobby Airport, the program faced stringent airspace regulations.14 However, by establishing a robust DFR program, Pearland allowed its first responders to be “on scene” virtually.12 This early observation relays critical information to police, fire, or paramedics, which has proven to be the difference between life and death in medical emergencies and has drastically reduced the over-deployment of municipal resources.12 Their operations highlight that highly automated drones, centrally managed by a small number of personnel, can exponentially improve the scale and efficiency of emergency response.12
Tactical Advantages of Direct CAD Integration
The efficacy of a DFR program is heavily dependent on the speed and precision of its deployment. Consequently, the integration of DFR software platforms directly into Computer-Aided Dispatch (CAD) systems and Real-Time Crime Centers (RTCC) is a critical operational requirement.3 CAD systems serve as the central nervous system for public safety communications, processing emergency calls, pinpointing origins (via E911 and Next Generation 911), managing automatic vehicle location (AVL), and coordinating multi-agency responses.17
The Mechanics of Automated Dispatch
When DFR operations are siloed from CAD infrastructure, dispatchers or dedicated drone pilots must manually monitor call screens, extract address data, input GPS coordinates into a separate flight application, and initiate launch sequences. This manual data entry introduces critical latency, delaying the deployment of the aircraft.
Direct integration allows specialized DFR platforms, such as Skydio DFR Command or Motorola Solutions’ CAPE software, to read CAD data via Application Programming Interfaces (APIs) in real-time.3 Features such as automated call handling and event creation enable the system to automatically assign and recommend the nearest prepositioned drone for deployment based on the incident type and geographic proximity.18 A call for service (CFS) can originate from multiple points: E911 systems, direct 10-digit numbers, alarm systems, or CAD-to-CAD interfaces, all of which seamlessly feed into the DFR software.19
Advanced integrations utilize artificial intelligence to parse live 9-1-1 audio and dispatch data. For example, Motorola’s Assist AI Suite can actively monitor live calls and automatically flag specific keywords such as “gun,” “robbery,” or “heart attack”.3 Upon detecting these triggers, the system suggests an immediate autonomous launch to the remote pilot.3 With this level of integration, a single click by an operator launches the nearest drone to a call for service, transitioning the aircraft from a docked state to airborne in just 20 seconds.16
Once airborne, integrated routing software automatically charts the most efficient and safe flight path.16 Systems like Skydio Pathfinder account for local terrain elevation, natural and man-made obstacles, geofences, and dynamic airspace rules.16 By automating the navigation phase, the remote operator is freed from the cognitive burden of navigating complex urban geography and can focus entirely on the call for service, camera operation, and incident assessment.16
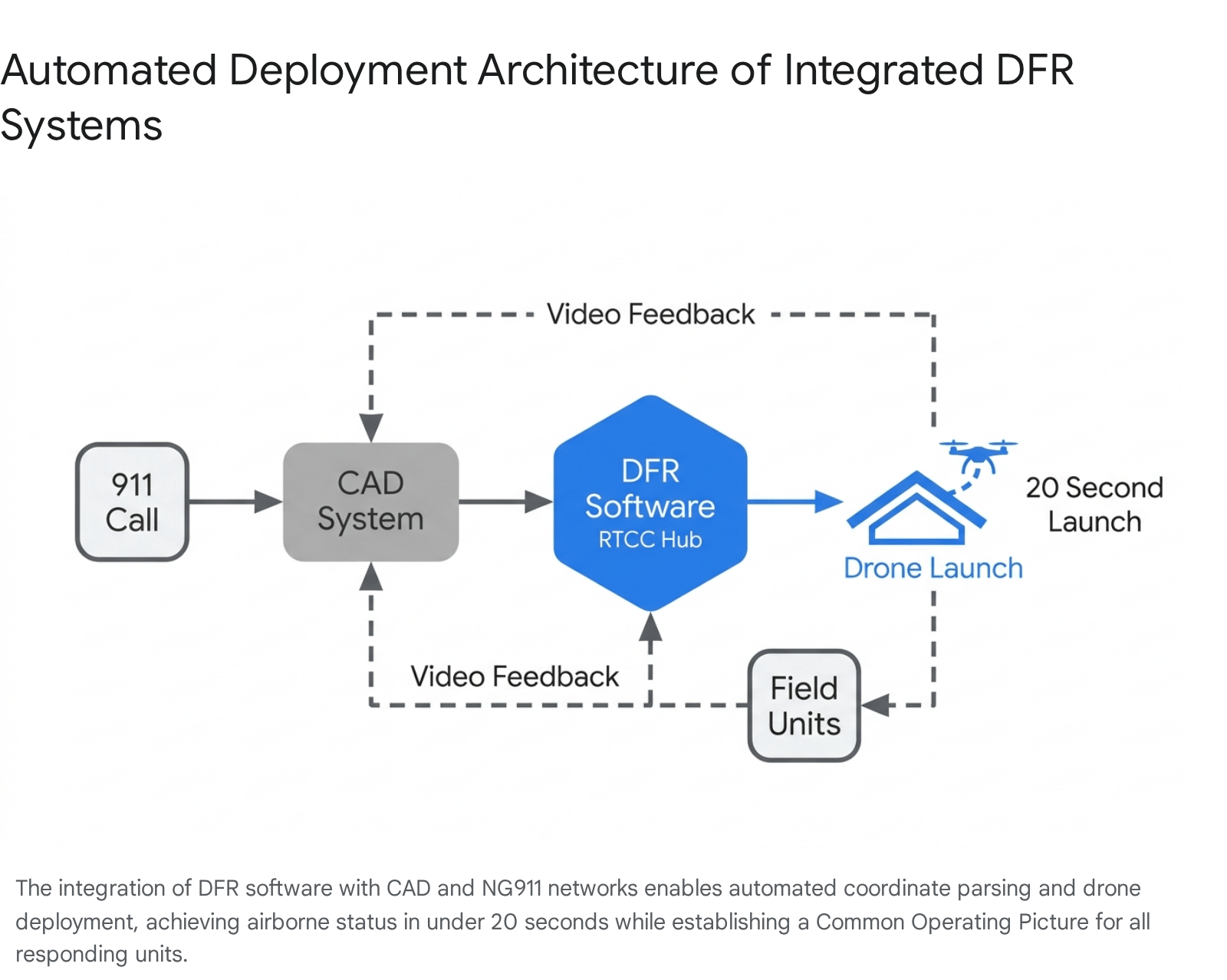
Real-Time Data Access and Common Operating Picture
CAD integration ensures that the telemetry and live video feeds generated by the drone are disseminated seamlessly across the public safety network. This creates a Common Operating Picture (COP) accessible simultaneously to dispatchers in the communications center, supervisors in the RTCC, and officers responding in the field via Mobile Data Terminals (MDTs).16
Tactical mapping within the CAD interface displays the drone’s geographic location, altitude, and camera field of view overlaid on multi-layer maps (such as Google or Bing Maps).18 This immediate display and centering functions alongside the real-time AVL tracking of ground units, allowing commanders to coordinate movements visually.18 Furthermore, layer filtering permits dispatchers to overlay critical infrastructure data on the same map, including fire hydrants, flow rates, and evacuation routes, enriching the situational awareness provided by the drone feed.18
The interconnected environment also extends to airspace security and interagency coordination. Integrations with systems like SkySafe provide dispatchers with airspace domain awareness, allowing them to detect the flight paths and controller locations of unauthorized drones, thereby helping dispatchers distinguish between friendly agency UAVs and potential threats in the incident area.3 Additionally, timely sharing of this CAD data with transportation agencies, such as State Departments of Transportation (DOTs) via automated data transfers, enhances the coordination of resources to clear roadways and relieve congestion during major traffic incidents.20
Communication Networks and Routing Algorithms
For remote operations to function reliably, the communication link must be robust. Connectivity solutions, such as Skydio Connect Fusion, combine point-to-point radio transmissions with commercial 5G/LTE networks to ensure uninterrupted coverage across the operational area.16 This redundant connectivity ensures that drones remain connected from launch to landing, maintaining speed and reliability on every mission, while enabling one operator to control multiple drones independently from a single browser window to set perimeters and provide multi-angle overwatch.16
Regulatory Pathways: The Evolution of BVLOS Waivers
The primary bottleneck for scaling DFR programs historically resided in federal aviation regulations, not hardware limitations. Under the standard 14 CFR Part 107 (Small UAS Rule), which governs the majority of commercial drone operations in the United States, operators are strictly required to maintain visual line-of-sight (VLOS) with the aircraft at all times.21
Early iterations of DFR bypassed this limitation by utilizing Visual Observers (VOs)—dedicated personnel stationed on rooftops or elevated platforms to physically watch the airspace and verbally deconflict flight paths with the remote pilot.5 However, the requirement to deploy dedicated personnel strictly for airspace deconfliction created costly, non-scalable personnel infrastructures that proved difficult to preposition and maintain, particularly during extreme weather conditions or 24/7 operations.4 From 2018 to 2024, the FAA approved just over 50 DFR waivers due to the complexity of the process, which often took eleven or more months to adjudicate.4
The operational viability of DFR is therefore inextricably linked to Beyond Visual Line of Sight (BVLOS) capabilities. Operating BVLOS completely removes the requirement for a co-located human visual observer, significantly increasing the ratio of drones to operators and exponentially improving the scalability and efficiency of the program.12
The Part 91 Public Aircraft Operator Exemption
To alleviate regulatory gridlock and respond to the specific needs of law enforcement, the FAA instituted a streamlined waiver process designed exclusively for public safety entities. Organizations that legally qualify as both a Public Aircraft Operator (PAO) and a Public Safety Organization (PSO) can bypass standard Part 107 restrictions by operating under statutory requirements for public aircraft (49 U.S.C. §40102(a) and § 40125), governed operationally by 14 CFR Part 91.21
Under the definitions established by the 2024 FAA Reauthorization Act, a PAO must be a government entity (State, District of Columbia, US territory, or political subdivision) using the aircraft for non-commercial purposes.23 A PSO is defined as an entity primarily engaged in activities related to the safety and well-being of the general public, encompassing law enforcement, fire departments, and emergency medical services.22 Crucially, volunteer organizations or 501(c)(3) entities typically do not qualify for this specific pathway and must utilize Part 107 waivers instead.22
Operating under Part 91 allows the qualifying agency to self-certify its UAS and operators for flights performing governmental functions.21 The expedited Part 91 BVLOS waiver process—initiated by submitting FAA Form 7711-2 and a Concept of Operation (ConOp) to the FAA—cuts approval times from nearly a year down to approximately one week.22 This expedited waiver outright replaces older, more restrictive authorizations like the Tactical BVLOS (TBVLOS) and First Responder BVLOS (FR-BVLOS) Certificates of Authorization (COAs).22 Furthermore, the new VLOS/BVLOS 91.113 CoW/As remain valid for a duration of 48 months and eliminate the substantial administrative burden of filing Notices to Airmen (NOTAMs) or submitting monthly operational reports.22
Operational Altitudes: Evaluating Shielded vs. Non-Shielded Operations
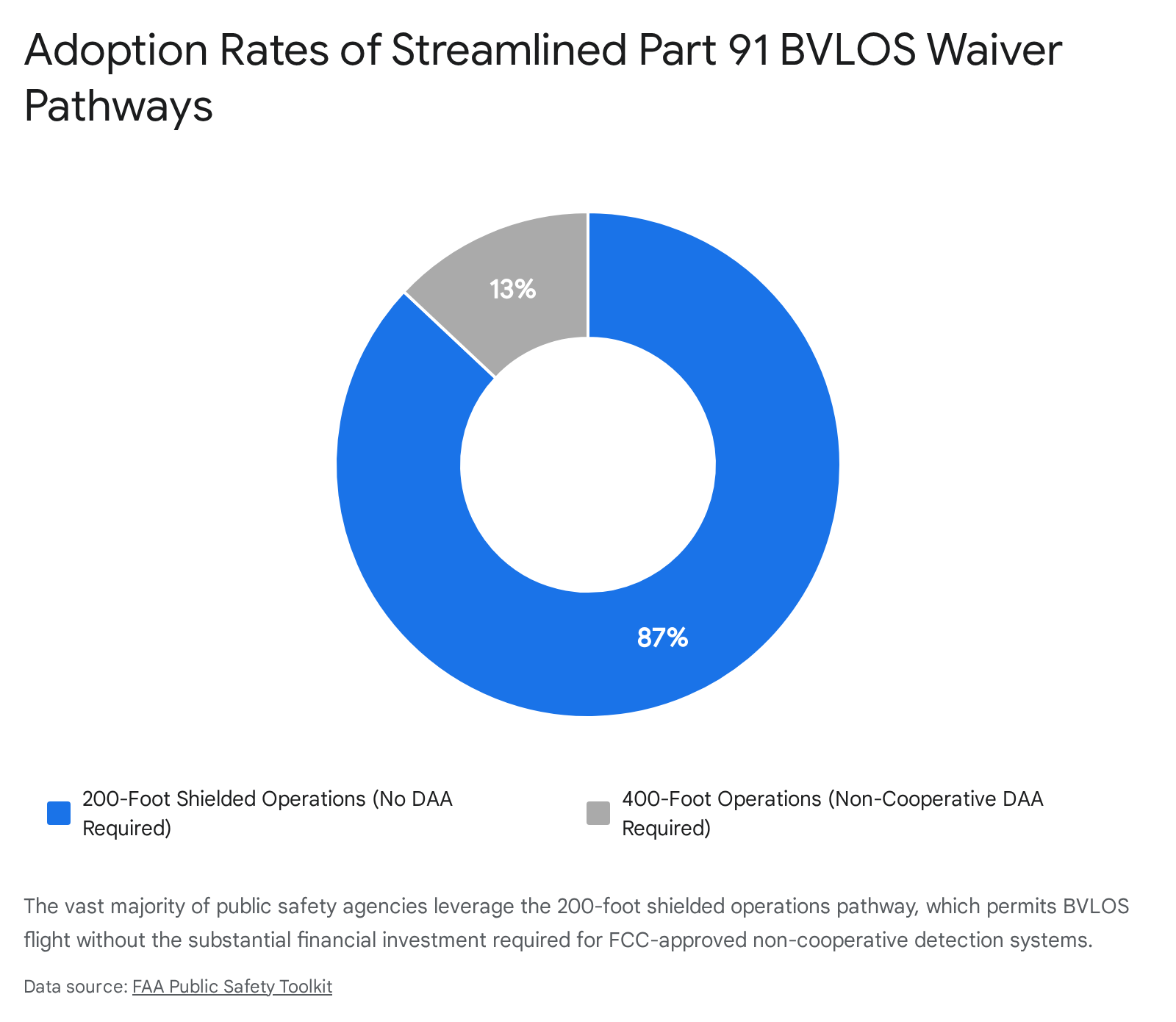
The streamlined Part 91 BVLOS waiver process offers two distinct pathways based on the airspace deconfliction technology utilized by the agency. These pathways dictate the operational ceiling of the DFR program.
1. The 200-Foot Shielded Operations Pathway The most widely adopted pathway—utilized by approximately 87 percent of participating public safety departments—is the 200-Foot Shielded Operations Waiver.22 This pathway relies on the principle of obstruction shielding to mitigate the risk of mid-air collisions. Drones are permitted to operate up to 200 feet Above Ground Level (AGL), or up to 100 feet above the height of a natural or man-made obstruction, provided the drone remains within a 100-foot lateral radius of that obstruction (not to exceed 400 feet AGL total).22
Because low-altitude urban infrastructure (buildings, cellular towers, trees) provides a physical barrier against manned aircraft entering the operational area, this pathway does not require the agency to procure expensive ground-based radar systems.22 It only requires the drone to be equipped with standard ADS-B In technology to detect cooperative manned aircraft broadcasting their positions.22 Many modern tactical drones, such as the Skydio X10, feature built-in ADS-B receivers capable of detecting aircraft on both 879 MHz and 1090 MHz frequencies without requiring additional external hardware.23
2. The 400-Foot Non-Shielded Operations Pathway (DAA) Conversely, approximately 13 percent of departments pursue the 400-Foot Non-Shielded Operations Waiver.22 This pathway allows drones to operate up to the standard 400 feet AGL ceiling but strictly requires the implementation of an FCC-approved Detect and Avoid (DAA) system capable of identifying non-cooperative aircraft (aircraft that are not transmitting ADS-B signals, such as older general aviation planes or gliders).22 Agencies utilizing this pathway must submit a specific “Criteria for Making Decision-Detect And Avoid (CMD-DAA)” worksheet detailing their system’s components, capabilities, and limitations.22
The Pearland Police Department successfully demonstrated this advanced capability by becoming the first law enforcement agency in the nation to be awarded a COA for BVLOS operations without human visual observers under the non-shielded framework.12 To achieve this, they implemented the Iris Automation Casia G ground-based air surveillance system.12 Installed on various city buildings, this system provides a 360-degree field of regard, detecting, alerting, and enabling remote operators to avoid both local and commercial aircraft.15 This ground-based optical network functions as an approved alternative means of compliance to the traditional “see-and-avoid” requirement mandated by 14 CFR 91.113.13
Advanced Airspace Authorizations and Waivers
While the Part 91 BVLOS waiver provides substantial operational freedom in uncontrolled Class G airspace, operations extending into controlled airspace or exceeding specific altitude thresholds require secondary authorizations.
For routine operations requiring altitudes above the established UAS Facility Map (UASFM) grid heights at LAANC-enabled airports, or for operations in E3/E4 controlled airspace, operators must apply for a separate Air Traffic Organization (ATO) COA via the FAA’s CAPS (COA Application Processing System) portal.22 Accessing the CAPS system requires agencies to obtain a Public Declaration Letter signed by outside legal counsel.23
Furthermore, during severe crises where immediate life-safety operations necessitate exceeding standard limitations, waiver holders must request a Special Governmental Interest (SGI) COA or waiver directly from the FAA’s Systems Operations Support Center (SOSC).22
Regarding general operational requirements embedded in these waivers, night operations are permitted 24/7 provided the drone is equipped with anti-collision lighting visible for three statute miles.22 Weather minimums mandate a minimum visibility of three statute miles, with the aircraft remaining 500 feet below and 2,000 feet horizontally from clouds.22 Operations over people for routine policing (non-life-safety emergencies) require the drone to meet Part 107 Subpart D category compliance, be equipped with propeller guards (for aircraft weighing 0.88 lbs or less), or utilize a Parachute Recovery System (PRS) conforming to the ASTM F3322-18 standard (for aircraft weighing more than 0.88 lbs).22 Standard Remote ID compliance per 14 CFR Part 89 is universally required for all BVLOS operations unless explicitly authorized otherwise by the FAA.22
Establishing an “Aviation Mindset” in Police Drone Management
As DFR programs rapidly scale across the nation, operational capability risks outpacing safety if law enforcement agencies treat drones merely as advanced consumer electronics. Industry experts strongly advocate for a structural transition toward an “aviation mindset”—a disciplined, highly structured approach imported directly from commercial manned aviation that focuses heavily on risk management, standardized operating procedures, and human factors.24
Building a drone program upon these foundations is essential to maintaining community trust, minimizing agency liability, and preventing hardware failure in densely populated urban environments.24
Safety Management Systems (SMS) and Risk Mitigation
The cornerstone of an aviation mindset is the formal implementation of a Safety Management System (SMS). An SMS is a comprehensive, top-down, organization-wide approach to managing safety risk and assuring the effectiveness of safety controls.25 It encompasses systematic procedures, practices, and policies designed to proactively identify hazards, assess operational risks, and implement mitigations before accidents or catastrophic failures occur.25
Although historically mandated only for critical commercial aviation segments (such as charter airlines and Part 145 repair stations), integrating SMS principles into public safety drone operations aligns departments with emerging global aviation regulations and standardizes operational efficiency.25 Integral to the SMS framework is the establishment of rigorous Standard Operating Procedures (SOPs) and checklists, mirroring the Crew Resource Management (CRM) practices utilized by manned airline crews.22
SOPs strip away ambiguity during high-stress law enforcement deployments by clearly defining deployment protocols. Effective policies must explicitly dictate who possesses the authority to launch a drone, under what specific circumstances they may be used (e.g., distinguishing between search warrants and exigent circumstances), the precise geographic and temporal limits of the operation, and operational thresholds regarding weather and visibility.29 By defining these protocols proactively, agencies reduce the risk of rash decision-making during active crises and ensure operational consistency.29
Hardware Standards and Program Pillars
A scalable, aviation-grade DFR program relies on the procurement and maintenance of specialized hardware. A modern DFR ecosystem generally rests on five core pillars:
- NDAA-compliant UAVs: Small, multirotor aircraft designed to hover and maneuver in urban environments, equipped with 5G-enabled redundant communication links.3
- Sensor Payloads: High-definition dual Electro-Optical/Infrared (EO/IR) sensors capable of reading license plates at a distance or tracking heat signatures in low visibility.3
- Automated Docking Stations: Weather-proof hubs installed on rooftops that manage battery charging and maintain the aircraft in a constant state of readiness for remote launch.3
- Tactical Software: The aforementioned CAD integration platforms that facilitate automated launches and unified mapping.3
- Sense and Avoid Technology: AI-powered obstacle avoidance and built-in ADS-B receivers critical for safe BVLOS operations.3
Comprehensive Maintenance Protocols
Disciplined maintenance protocols are mandatory to sustain an aviation-grade fleet. Uncrewed systems degrade over time due to the rigors of flight, environmental exposure (mud, dirt, moisture), and the significant thermal stress placed on lithium-ion batteries.31 Departments must institute scheduled maintenance regimens, typically categorized into pre-flight/post-flight field inspections and comprehensive structural inspections executed after defined intervals, such as 25 and 100 flights.31
A full structural inspection requires granular attention to detail across all hardware components:
| Component Category | Required Inspection Protocol |
| Chassis & Structure | Clean exterior of mud/dirt. Inspect chassis for hairline cracks. Visually and physically check that all screws are in place, tight, and not vibrating loose. Inspect all exterior stickers to ensure none are loose and capable of obstructing sensors.32 |
| Propulsion System | Check propellers for broken pieces, bent blades, or micro-cracks. Manually rotate to ensure they are free-spinning without resistance. Check motors for debris, obstructions, unusual vibrations, or wobble.32 |
| Electronics & Antennas | Check for exposed or frayed wiring and inspect internal solder joints. Verify that antennas are in good condition and properly screwed into the unit.32 |
| Battery Management | Inspect battery packs for bulges, swelling, cracks, leakage, or corrosion. Clean gold battery plates inside the aircraft and check metal data sockets for damage. Conduct a full discharge (down to 10%) and full recharge cycle. Ensure docking station voltage is compliant and maintains charge between 30% and 90% to prevent chemical degradation.32 |
| Software & Firmware | Regularly update drone and controller firmware to patch vulnerabilities, optimize flight algorithms, and ensure the system is working properly.32 |
Professionalizing Remote Pilot Training Standards
Operating a drone under the Part 91 public aircraft framework places the ultimate burden of self-certification on the public safety agency itself.23 While obtaining an FAA Part 107 Remote Pilot Certificate provides a baseline understanding of airspace classifications and weather, it does not adequately prepare a police officer for the kinetic, high-stress reality of tactical DFR flight.7 Research indicates that the proficiency of many public safety remote pilots remains inconsistent, often hampered by limited flight hours, the demands of collateral duty requirements, and a historical lack of formalized, sector-wide training standards.36
Implementing Position Task Books (PTBs)
To bridge this training gap, organizations such as DRONERESPONDERS urge agencies to rapidly adopt Position Task Books (PTBs).36 PTBs are structured tracking tools used to verify performance qualification testing and document accumulated skill sets before assigning flight crews to active operational duties.36 Despite being a low-cost, highly proven solution for standardizing remote pilot training, data collected in late 2019 indicated that fewer than 40 percent of public safety UAS operations were utilizing any form of PTB to qualify their pilots.36 Implementing these tools is viewed as a critical stop-gap measure to improve safety and certify key personnel while formal sector standards continue to evolve.36
The NIST Aerial Test Methods
For quantitative evaluation of pilot proficiency, the industry standard has shifted toward the National Institute of Standards and Technology (NIST) Aerial Test Methods for Small Unmanned Aircraft Systems.37 Developed in conjunction with the Science and Technology Directorate of the U.S. Department of Homeland Security, the NIST course is considered one of the most scientifically validated UAS training methods available.36 It quantitatively measures both the mechanical capabilities of the drone system and the competence of the remote pilot in executing precise flight maneuvers.36
The NIST test methods are categorized into progressively difficult operational scenarios:
- Level 1 (Basic Proficiency) & Level 2 (Maneuvering): Focuses on foundational flight control and orientation.37
- Level 3 (Open) & Level 4 (Obstructed): Requires pilots to navigate specific lanes and obstacles, often integrated into standard recurrent pilot training (e.g., 16-hour maintenance courses) to ensure competency for Part 107 or COA operations.37
- Level 5 (Confined): Evaluates skills necessary for interior operations and GPS-denied environments.37
Agencies are increasingly relying on certified proctors to administer these NIST scenarios natively within their departments.37 Furthermore, advanced tactical courses teach officers to operate effectively in First Person View (FPV), utilize infrared and self-illumination views, and pilot drones alongside ground robots during complex indoor operations or SWAT support missions.37
Strategic Methodologies for Mitigating Cybersecurity Vulnerabilities
Drones are advanced Information and Communication Technology System (ICTS) devices.39 A DFR unit constantly transmits highly sensitive telemetry (GPS coordinates, altitude, battery status), control commands, and high-definition optical video data between the aircraft and the Ground Control Station (GCS).39 Because these transmissions utilize wireless protocols over the internet or radio frequency bands, every point of connection represents a potential target for malicious actors.39
If a law enforcement drone is compromised, adversaries could intercept sensitive operational data, hijack control of the aircraft, spoof GPS signals to misdirect the drone, or exploit the connection to inject malware into the broader police enterprise network.40 Consequently, establishing robust cybersecurity protocols is a critical operational mandate for any modern DFR program.
Legislative Compliance and Supply Chain Security
The first layer of cybersecurity defense involves securing the hardware supply chain. The widespread use of foreign-manufactured drones in public safety fleets has raised severe national security and data privacy concerns, leading to sweeping federal legislation. The National Defense Authorization Act (NDAA) and the subsequent American Security Drone Act (ASDA) explicitly prohibit federal agencies, as well as state and local organizations utilizing federal grant money, from procuring or operating drones manufactured by specific foreign entities.43
The enforcement of ASDA’s procurement prohibitions became fully active on December 22, 2025.43 This transformed NDAA compliance from a defense-centric requirement into a baseline expectation for municipal law enforcement programs nationwide.43 To be considered compliant, an aircraft and its critical subsystems—including flight controllers, cameras, data links, storage, and ground control stations—must be manufactured without any components from restricted suppliers.43 Agencies must rigorously audit their existing fleets against these standards or exclusively select hardware cleared by the United States Department of Defense through its Blue UAS Program, thereby eliminating potential backdoors embedded in proprietary foreign firmware.45
Securing the Data Link: MAVLink 2.0 and Encryption
The wireless data link connecting the GCS to the drone is highly susceptible to eavesdropping, interception, and signal jamming.46 The most ubiquitous telemetry protocol used in the UAS industry is MAVLink (Micro Air Vehicle Link), which facilitates efficient data exchange over low-bandwidth connections.48 However, legacy versions of MAVLink (version 1) transmit data in plaintext, exposing critical control commands and flight parameters to anyone actively monitoring the frequency.49
To mitigate this fundamental vulnerability, law enforcement agencies must implement systems utilizing MAVLink 2.0, which introduces critical security enhancements, primarily cryptographic message signing.42 While message signing does not encrypt the payload itself, it appends a cryptographic signature—generated via a secure secret key—to each data packet.49 This allows the drone’s onboard flight controller to cryptographically verify that incoming commands originated from a trusted, authorized GCS.49 By enforcing message signing on all communication links, agencies prevent spoofing and command replay attacks; an attacker cannot force the drone into an unauthorized state because the flight controller will automatically reject any unsigned commands.42 Additionally, MAVLink utilizes CRC-16 (Cyclic Redundancy Check) checksums to ensure that data packets are not corrupted or altered during transmission.51
Beyond authentication, complete end-to-end encryption is required to protect the confidentiality of the actual data payload. State guidelines and industry standards mandate that all video feeds, GPS coordinates, and telemetry must be encrypted in transit using advanced protocols such as AES-256 (Advanced Encryption Standard), Transport Layer Security (TLS/DTLS), or Virtual Private Networks (VPNs).40 To counteract physical-layer eavesdropping and signal jamming, transmission hardware should utilize spread-spectrum techniques and frequency hopping, which rapidly shift the transmission frequency in a pseudorandom sequence known only to the authorized transmitter and receiver, maintaining stable communication in contested environments.46
Network Architecture, Zero Trust, and Data-at-Rest
Cybersecurity must extend beyond the airborne radio link to encompass the broader IT infrastructure. Law enforcement drones must operate within an isolated environment or a segmented network.39 Ground Control Stations, laptops, and smartphones used for drone operations should never connect directly to the primary enterprise network of the police department.39 Implementing a Zero Trust Architecture (ZTA)—which assumes all network traffic is hostile and requires continuous verification and authentication for every access request—minimizes the attack surface and prevents malware injected via a compromised drone from moving laterally into sensitive police databases or CAD systems.39
Protecting data-at-rest is equally critical. A single 30-minute flight can generate gigabytes of data containing sensitive metadata, timestamps, and geospatial coordinates.40 Best practices dictate the enforcement of end-to-end AES-256 encryption on all local storage mediums (such as SD cards) and cloud servers.45 For agencies utilizing commercial platforms that may attempt to “phone home” to external manufacturer servers, enabling features like “Local Data Mode” (LDM) prevents the drone from transmitting flight logs or imagery over the internet.40 Furthermore, stringent data sanitization policies must be enforced, requiring the deletion of all flight telemetry and imagery from the drone’s internal memory immediately upon secure transfer to CJIS-compliant storage facilities.39
Forensic Readiness and the NIST Cybersecurity Framework
Finally, the overarching cybersecurity strategy of a DFR program should be mapped to the National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF) 2.0.53 This framework provides a structured vocabulary and proven methodology for identifying risks, protecting assets, detecting anomalies, responding to breaches, and recovering operations.55 By aligning DFR cybersecurity policies with NIST guidelines, organizations establish a defensible, proactive posture capable of addressing the rapidly evolving threat landscape of uncrewed aerial systems.53
In the event of a breach or hostile action, law enforcement agencies must be prepared for digital forensics. Anti-forensic techniques employed by adversaries—such as wiping telemetry logs, encrypting flight data post-compromise, or falsifying timestamps—must be countered aggressively.56 To ensure investigative reliability, DFR systems should implement tamper-resistant designs, including immutable storage (such as WORM drives or blockchain technology), redundant log backups, machine learning-based behavioral profiling, and real-time intrusion detection systems (IDS) on the dedicated drone network to detect and block malicious traffic immediately.41
Conclusion
The expansion of Drone as First Responder programs has fundamentally transformed the tactical architecture of United States law enforcement. By transitioning from a reactive, manual deployment model to a proactive, highly integrated system, agencies have demonstrated measurable, quantitative success in optimizing resource allocation, significantly reducing response times, and enhancing officer safety during high-risk encounters. The strategic integration of DFR platforms into Computer-Aided Dispatch networks has proven essential to this success, removing human latency and enabling autonomous, twenty-second launch sequences that provide immediate, high-fidelity aerial intelligence to a unified Common Operating Picture.
This operational scaling has been heavily facilitated by critical regulatory evolutions, specifically the FAA’s streamlined Part 91 BVLOS waiver process. By recognizing the unique operational environment and statutory authority of Public Aircraft Operators, the FAA has enabled agencies to bypass the restrictive and costly requirement for human visual observers. This is achieved primarily through the utilization of low-altitude shielded operations or the deployment of advanced, FCC-approved ground-based radar systems.
However, the proliferation of these automated aerial assets necessitates a stringent shift in departmental culture. Law enforcement agencies must adopt a rigorous aviation mindset, prioritizing Safety Management Systems, comprehensive structural maintenance protocols, and formalized remote pilot training validated by NIST testing methodologies. Simultaneously, the profound cybersecurity risks associated with continuous drone telemetry and data transmission demand uncompromising adherence to federal supply chain mandates (NDAA/ASDA) and the implementation of robust cryptographic defenses. Only through the holistic integration of tactical CAD software, regulatory compliance, aviation discipline, and hardened cybersecurity networks—such as MAVLink message signing, AES-256 encryption, and Zero Trust architectures—can DFR programs safely and effectively serve the modern public safety mission without compromising the data integrity or security of the communities they protect.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Sources Used
- Drone as First Responder: Practical Insights into Law Enforcement Implementation, accessed May 10, 2026, https://www.ojp.gov/library/publications/drone-first-responder-practical-insights-law-enforcement-implementation
- Drone as First Responder: Practical Insights into Law Enforcement …, accessed May 10, 2026, https://cjttec.org/drone-as-first-responder-practical-insights-into-law-enforcement-implementation/
- Drone as First Responder (DFR): Key Uses & Implementation – Motorola Solutions, accessed May 10, 2026, https://www.motorolasolutions.com/en_us/blog/drone-first-responder
- 2025: The year drone as first responder programs went mainstream – Police1, accessed May 10, 2026, https://www.police1.com/drones/2025-the-year-drone-as-first-responder-programs-went-mainstream
- Drone as First Responder Programs: 2025 in Review – Electronic Frontier Foundation, accessed May 10, 2026, https://www.eff.org/deeplinks/2025/12/drone-first-responder-programs-2025-review
- The modern DFR deployment: insights from nearly 2,000 DFR flights – Skydio, accessed May 10, 2026, https://www.skydio.com/blog/insights-from-nearly-2-000-dfr-flights
- Public Safety Drones: A Comprehensive Guide for First Responders, accessed May 10, 2026, https://www.dronepilotgroundschool.com/public-safety-drone/
- Drones as First Responders – CNA.org., accessed May 10, 2026, https://www.cna.org/reports/2025/09/Drones-as-First-Responders.pdf
- All the Buzz About Drones as First Responders – Police Chief Magazine, accessed May 10, 2026, https://www.policechiefmagazine.org/all-the-buzz-dfr/
- Pearland Police Department Makes History: The Future of Incident Response for All First Responders – Issuu, accessed May 10, 2026, https://issuu.com/theedrmagazine/docs/edr_july_2023_final_draft_for_pab_/s/29211918
- Drones for First Responders (DFR) Pilot Program | DriveOhio – Ohio.gov, accessed May 10, 2026, https://drive.ohio.gov/programs/advanced-aviation/drones-for-first-responders-pilot-program
- First in the Nation – Pearland PD expands DFR operations to include BVLOS without Visual Observers, accessed May 10, 2026, https://www.commercialdronealliance.org/news/pearlandpd
- Pearland Police expands drone as first responder operations without visual observers, accessed May 10, 2026, https://evtolinsights.com/pearland-police-expands-drone-as-first-responder-operations-without-visual-observers/
- Enhancing Emergency Response in Pearland With ThousandEyes, accessed May 10, 2026, https://www.thousandeyes.com/resources/pearland-case-study
- First in the Nation Pearland Police Department expands DFR o, accessed May 10, 2026, https://www.pearland.com/msg/first-nation-pearland-police.php?p=1610634
- Skydio DFR Command: operating system for DFR Programs, accessed May 10, 2026, https://www.skydio.com/software/dfr-command
- Computer-Aided Dispatch (CAD): Definition, Benefits & Rugged Solutions – Getac, accessed May 10, 2026, https://www.getac.com/us/industries/public-safety/computer-aided-dispatch/
- Computer Aided Dispatch (CAD) – CSI Technology Group, accessed May 10, 2026, https://www.csitech.com/public-safety/cad/
- Standard Functional Specifications for Law Enforcement Computer Aided Dispatch (CAD) Systems – Bureau of Justice Assistance, accessed May 10, 2026, https://bja.ojp.gov/sites/g/files/xyckuh186/files/media/document/leitsc_law_enforcement_cad_systems.pdf
- Computer-Aided Dispatch Integration Factsheet – FHWA Office of Operations, accessed May 10, 2026, https://ops.fhwa.dot.gov/tim/docs/EDC-6_Factsheet_TIM_CAD_v2_508.pdf
- Operate a Drone, Start a Drone Program | Federal Aviation Administration, accessed May 10, 2026, https://www.faa.gov/uas/public_safety_gov/drone_program
- Public Safety Toolkit | Federal Aviation Administration, accessed May 10, 2026, https://www.faa.gov/uas/public_safety_gov/public_safety_toolkit
- Guide: How to Obtain a Public Safety Part 91 BVLOS Waiver | Skydio, accessed May 10, 2026, https://www.skydio.com/resources/guides/part91-bvlos-waiver-process
- How an aviation mindset can strengthen drone as first responder programs – Police1, accessed May 10, 2026, https://www.police1.com/drones/how-an-aviation-mindset-can-strengthen-drone-as-first-responder-programs
- Safety Management System (SMS) | Federal Aviation Administration, accessed May 10, 2026, https://www.faa.gov/about/initiatives/sms
- Do You Need a Safety Management System (SMS) for UAS/Drone OPS – Vector-safety, accessed May 10, 2026, https://vector-safety.com/f/do-you-need-a-safety-management-system-sms-for-uasdrone-ops
- Safety Management Systems (SMS) | NBAA – National Business Aviation Association, accessed May 10, 2026, https://nbaa.org/flight-department-administration/sms/
- Safety Management Systems – Federal Register, accessed May 10, 2026, https://www.federalregister.gov/documents/2024/04/26/2024-08669/safety-management-systems
- Law Enforcement Drone Policy: Building Programs the Community Can Trust – Flock Safety, accessed May 10, 2026, https://www.flocksafety.com/blog/law-enforcement-drone-policy
- 5 Steps For Starting a Public Safety Drone Program – Axon.com, accessed May 10, 2026, https://www.axon.com/resources/drone-program
- SUAS MAINTENANCE GUIDE – Sundance Media Group, accessed May 10, 2026, https://sundancemediagroup.com/wp-content/uploads/2020/04/Maintenance-Checklist2020.pdf
- Routine Drone Maintenance Checklist – Regulations.gov, accessed May 10, 2026, https://downloads.regulations.gov/FAA-2021-0745-0001/attachment_3.pdf
- Example Maintenance Procedures – DroneSense Support, accessed May 10, 2026, https://support.dronesense.com/hc/en-us/articles/4404450145805-Example-Maintenance-Procedures
- Guide to Drone Maintenance | Duncan-Parnell, accessed May 10, 2026, https://www.duncan-parnell.com/blog/88/guide-to-drone-maintenance
- Routine Drone Maintenance Checklist, accessed May 10, 2026, https://coastaldrone.co/routine-drone-maintenance-checklist/
- DRONERESPONDERS Releases New Guidance for Public Safety …, accessed May 10, 2026, https://www.droneresponders.org/post/droneresponders-releases-new-guidance-for-public-safety-uas-flight-training-and-operations
- Public Safety Drone Training – The Regional Training Center, accessed May 10, 2026, https://thertc.org/public-safety-drone-training/
- Public Safety UAS | Home, accessed May 10, 2026, https://www.publicsafetyuas.net/
- UAS Cybersecurity – CISA, accessed May 10, 2026, https://www.cisa.gov/topics/physical-security/be-air-aware/uas-cybersecurity
- Secure Your Drone: Privacy and Data Protection Guidance – CISA, accessed May 10, 2026, https://www.cisa.gov/sites/default/files/2023-01/FINAL_508%20Compliant_Secure%20Your%20Drone_Privacy%20and%20Data%20Protection%20Guidance_24JAN2023.pdf
- Cyber security considerations for drone use (ITSAP.00.143), accessed May 10, 2026, https://www.cyber.gc.ca/en/guidance/cyber-security-considerations-drone-use-itsap00143
- Drone Security – OWASP Cheat Sheet Series, accessed May 10, 2026, https://cheatsheetseries.owasp.org/cheatsheets/Drone_Security_Cheat_Sheet.html
- What Makes a Drone NDAA Compliant? (2026 Guide), accessed May 10, 2026, https://www.thedroneu.com/blog/ndaa-compliant-drones-guide/
- Ultimate Guide to NDAA-Compliant Drones – Duncan-Parnell, accessed May 10, 2026, https://www.duncan-parnell.com/blog/343/ultimate-guide-to-ndaa-compliant-drones-duncan-parnell
- 73-1005, accessed May 10, 2026, https://nebraskalegislature.gov/laws/statutes.php?statute=73-1005
- Secure Communication in Drone Networks: A Comprehensive Survey of Lightweight Encryption and Key Management Techniques – MDPI, accessed May 10, 2026, https://www.mdpi.com/2504-446X/9/8/583
- Ultimate Guide to Drone Wireless Protocols – Anvil Labs, accessed May 10, 2026, https://anvil.so/post/ultimate-guide-drone-wireless-protocols
- Securing Drone Communications: A Vulnerability Analysis of MAVLink – SciUp.org, accessed May 10, 2026, https://sciup.org/securing-drone-communicationsa-vulnerability-analysis-of-mavlink-15020080
- MAVLink Message Signing | PX4 Guide (main), accessed May 10, 2026, https://docs.px4.io/main/en/mavlink/message_signing
- MAVLink2 Signing — Copter documentation – ArduPilot, accessed May 10, 2026, https://ardupilot.org/copter/docs/common-MAVLink2-signing.html
- Protocol Overview – MAVLink Guide, accessed May 10, 2026, https://mavlink.io/en/about/overview.html
- Best Practices For Drone Data Analysis In Security Contexts | AAI-Drones, accessed May 10, 2026, https://aai-drones.com/best-practices-for-drone-data-analysis-in-security-contexts/
- Cybersecurity Framework | NIST – National Institute of Standards and Technology, accessed May 10, 2026, https://www.nist.gov/cyberframework
- autonomous aerial drones connecting public safety: opportunities – National Institute of Standards and Technology, accessed May 10, 2026, https://www.nist.gov/document/autonomous-aerial-drones-connecting-public-safety-opportunities-and-challenges-future
- NIST Cybersecurity Framework Examples and Best Practices – Armis, accessed May 10, 2026, https://www.armis.com/blog/nist-cybersecurity-framework-examples-and-best-practices/
- Cyber threat in drone systems: bridging real-time security, legal admissibility, and digital forensic solution readiness – Frontiers, accessed May 10, 2026, https://www.frontiersin.org/journals/communications-and-networks/articles/10.3389/frcmn.2025.1661928/full
