1. Executive Summary
The rapid proliferation and unprecedented technological advancement of Unmanned Aircraft Systems, commonly referred to as drones, have initiated a profound paradigm shift in the security environment for United States federal, state, and local law enforcement agencies. What was once a highly specialized technology utilized almost exclusively by aviation hobbyists and advanced military units has rapidly democratized into a ubiquitous, low-cost, and exceptionally capable platform available to the general public. While these systems undoubtedly offer significant operational benefits for civic functions, including search and rescue missions, crime scene reconstruction, and tactical aerial overwatch, they simultaneously introduce a dynamic and multifaceted asymmetric threat vector. Hostile actors, ranging from careless recreational operators to highly sophisticated transnational criminal organizations and domestic violent extremists, are increasingly exploiting drone technology to bypass traditional ground-based security architectures and directly challenge the authority of local police departments.
This comprehensive research report delineates the top ten mechanisms by which Unmanned Aircraft Systems constitute a critical threat to the safety, security, and operational efficacy of the United States law enforcement community. The analysis synthesizes intelligence from the Department of Homeland Security 2025 Homeland Threat Assessment, the Cybersecurity and Infrastructure Security Agency, the Federal Bureau of Investigation, the Federal Aviation Administration, and leading industry security consortiums to provide a nuanced, exhaustive understanding of the modern aerial threat matrix. The identified vulnerabilities span both the physical and digital domains. These vulnerabilities encompass direct kinetic attacks against infrastructure, complex cyber network intrusions utilizing aerial access points, severe disruptions to crewed law enforcement aviation, and the systemic obstruction of justice through persistent aerial counter-surveillance.
The central finding of this expert assessment reveals a severe and growing asymmetry between the escalating sophistication of malicious drone operations and the current legal, technological, and tactical capabilities of local police departments to effectively mitigate them. While foreign battlefields currently serve as the primary testing ground for autonomous swarms and weaponized payloads, intelligence indicators confirm that these identical tactical methodologies are actively migrating to the domestic United States homeland. Furthermore, this report highlights a critical legislative failure. Current federal statutes, originally drafted decades ago to protect commercial passenger aviation, inadvertently shield malicious drone operators from local police intervention by criminalizing the physical interception or electronic disruption of their aircraft by municipal authorities. This report concludes that without immediate, comprehensive legislative reform, significantly enhanced detection funding, and unified interagency coordination, law enforcement personnel will remain structurally disadvantaged against emerging threats originating from the airspace immediately above their respective jurisdictions.
2. Weaponized Payloads and Domestic Terrorism
The most severe physical threat posed by Unmanned Aircraft Systems is their conversion into low-cost, highly precise aerial weapons delivery platforms. The adaptation of foreign drone warfare tactics for domestic deployment is no longer a theoretical concern, but an active and documented operational reality. Tactics refined in conflict zones across Eastern Europe and the Middle East provide a highly accessible blueprint for domestic violent extremists and hostile non-state actors operating within the United States. In foreign theaters, operations such as Ukraine’s Operation Spider Web have demonstrated that low-cost, commercially available drones integrated with artificial intelligence can execute strikes over thousands of kilometers, utilizing dead-reckoning navigation and civilian cellular links to completely bypass traditional Global Positioning System jamming defenses. These platforms allow threat actors to achieve unprecedented strategic depth, striking targets well beyond traditional physical perimeter defenses without risking direct confrontation with armed security personnel or law enforcement officers.
The accessibility of consumer-grade drones dictates that sophisticated delivery mechanisms can be engineered using widely available open-source schematics, three-dimensional printing, and commercial off-the-shelf components. The payload capacities of modern commercial drones, particularly heavy-lift agricultural or cinematic models, permit the transportation of significant quantities of high explosives, chemical agents, or incendiary devices. A stark illustration of this specific threat materialized in November 2024, when federal agents arrested Skyler Philippi, a twenty-four-year-old domestic violent extremist motivated by a white supremacist and accelerationist ideology. Philippi was indicted for plotting to destroy a critical electrical power substation in Nashville, Tennessee.
According to federal charging documents and statements from the Department of Justice, the suspect explicitly intended to utilize a commercially acquired drone strapped with a homemade explosive device to bypass the physical security fencing of the facility. The operational objective was to detonate the payload directly atop critical energy transformers, causing cascading power failures. This plot, while successfully disrupted by the Federal Bureau of Investigation, demonstrates the clear intent and technical capability of domestic extremists to weaponize drones for mass civic disruption. The threat profile extends significantly beyond traditional high explosives. Law enforcement intelligence indicates that commercial platforms can be easily modified to disperse hazardous chemicals, biological agents, or even carry makeshift firearms, flamethrowers, and chainsaws designed to sabotage infrastructure or harm personnel.
Furthermore, the emerging tactic of drone swarming, where multiple autonomous or semi-autonomous aircraft coordinate a simultaneous attack, threatens to entirely overwhelm point-defense systems. Traditional law enforcement tactical doctrines are fundamentally designed to counter linear, terrestrial threats. A coordinated aerial assault utilizing multiple directions of approach creates a highly complex, three-dimensional operational challenge for responding Special Weapons and Tactics teams and critical infrastructure protection units. The ease with which a single operator can terrorize a community or cripple a regional power grid using a remotely piloted munition represents a profound escalation in the potential lethality available to lone-wolf attackers.
3. Obstruction of Law Enforcement Operations and Counter-Surveillance
Organized criminal enterprises and sophisticated transnational cartels are increasingly utilizing drone technology to actively obstruct justice and compromise the operational security of law enforcement agencies during active deployments. This threat manifests primarily through the practice of aerial counter-surveillance. Criminals actively deploy drones to monitor the staging areas, movement patterns, and tactical formations of police units in real time. By maintaining a persistent, high-altitude vantage point, criminal organizations can anticipate incoming police raids, orchestrate the rapid destruction of illicit evidence, and facilitate the physical escape of high-value targets long before tactical teams can ever breach a target perimeter.
A defining incident illuminating this specific capability occurred during a Federal Bureau of Investigation hostage rescue operation on the outskirts of a major United States city. As federal agents established a concealed, elevated observation post to assess the target location and gather pre-raid intelligence, a coordinated swarm of small consumer drones descended upon their position. The criminal operators, who had backpacked the drones into the area in anticipation of the federal raid, executed high-speed, low-altitude passes directly at the agents in a deliberate attempt to flush them from their concealed vantage point. The suspects effectively blinded the federal team, stripping them of critical situational awareness during a highly volatile, life-or-death deployment.
Compounding the technological sophistication of the operation, the suspects live-streamed the drone video footage to the public video-sharing platform YouTube. This allowed geographically distributed members of the criminal organization to access the real-time tactical feed via standard cellular networks on their mobile devices, granting them continuous updates on the movements of the Federal Bureau of Investigation personnel. This specific application of technology fundamentally shifts the balance of power during tactical encounters.
Transnational criminal organizations operating near the southern United States border routinely utilize similar drone networks to map the patrol routes of United States Customs and Border Protection personnel. By maintaining persistent aerial observation, these cartels identify temporary gaps in radar and patrol coverage to smuggle highly profitable narcotics and human cargo with virtual impunity. In urban environments, organized crime syndicates frequently deploy drones to monitor local police precincts. They utilize high-resolution cameras to catalog the license plates of unmarked undercover vehicles and identify confidential informants who physically enter the facilities. This persistent aerial espionage completely neutralizes the element of tactical surprise, which is often the single most critical asset possessed by law enforcement during high-risk warrant executions, hostage rescues, and fugitive apprehension missions.
4. Interference with Crewed Aviation and First Responder Air Support
The unauthorized intrusion of drones into controlled civilian airspace constitutes a direct, immediate, and potentially lethal threat to crewed law enforcement aviation, emergency medical air ambulances, and aerial firefighting operations. Even a relatively small consumer micro-drone, weighing less than two pounds, possesses the necessary kinetic energy to shatter a helicopter windshield, critically damage an exposed tail rotor, or cause a catastrophic engine failure if ingested into an intake mechanism. Unlike high-altitude commercial passenger airliners, police and rescue helicopters operate extensively at low altitudes in dense urban canyons or treacherous rural environments. This operational necessity forces them to share the exact stratum of airspace highly favored by recreational and malicious drone operators.
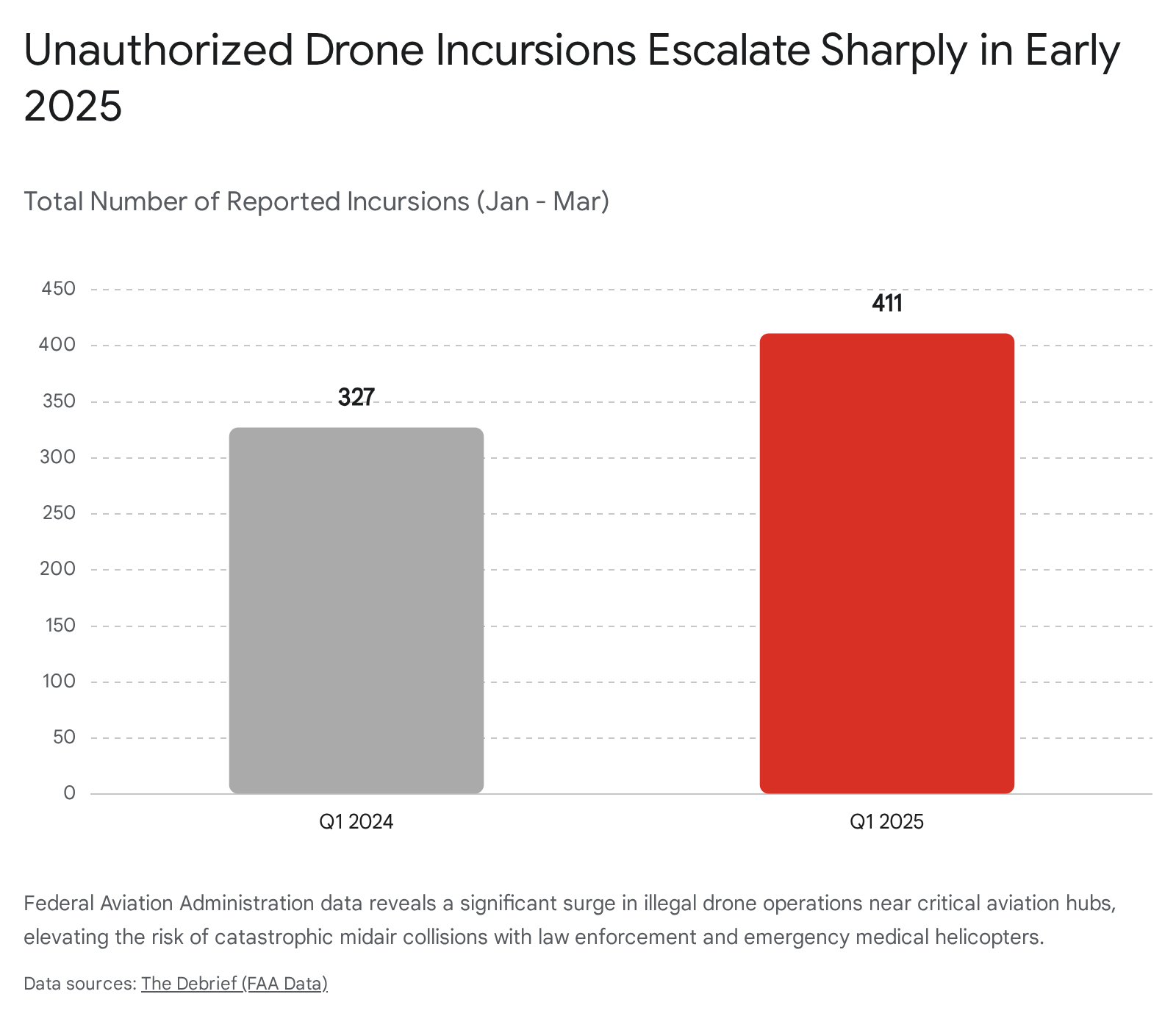
Recent data compiled by federal authorities underscores a significant and highly concerning acceleration in this specific threat vector. According to internal records reviewed by the Federal Aviation Administration and incident reports filed with the NASA Aviation Safety Reporting System, there were four hundred and eleven official reports of illegal drone incursions near United States airports from January to March of 2025. This figure represents a substantial 25.6 percent increase compared to the three hundred and twenty-seven reports recorded during the exact same period in the previous year.
A geographic analysis of the first quarter 2025 data reveals that specific major urban centers are experiencing acute surges in unauthorized activity. Chicago led the nation with twenty-nine unauthorized sightings, more than doubling its tally from the prior year. Houston and New York followed with nineteen and eighteen sightings respectively, while Orlando recorded eighteen and San Diego logged fourteen. At the state level, Florida reported seventy-three total incidents, California reported fifty-six, and Texas reported forty.
The incident reports from early 2025 outline harrowing near-midair collisions. In February 2025, an emergency air ambulance helicopter crew operating with night vision goggles reported a terrifying near-miss where an unidentified drone passed less than ten feet from their aircraft in flight. Such high-speed encounters force pilots into violent evasive maneuvers that can induce spatial disorientation, damage the airframe, or cause a total loss of control, particularly during the critical, low-altitude phases of takeoff and landing.
The secondary consequence of these incursions is the profound disruption of emergency services across multiple jurisdictions. When an unauthorized drone is detected in the operational theater of a major wildfire or a complex traffic collision, incident commanders are routinely forced by safety protocols to ground all crewed aviation assets to prevent a midair collision. This mandatory grounding halts the delivery of vital aerial fire retardant, terminates the aerial pursuit of fleeing felony suspects, and critically delays the evacuation of severely injured trauma patients. By merely flying a commercial drone in the general vicinity of an emergency scene, a careless hobbyist or a deliberate provocateur can effectively neutralize millions of dollars of public safety aviation assets, severely degrading the emergency response capability of the entire surrounding jurisdiction.
5. Cyber Exploitation and Secured Network Infiltration
While the physical and kinetic risks of drones dominate public security discourse, their emerging capability as highly mobile vectors for sophisticated cyberattacks presents an equally critical, yet often overlooked, threat to law enforcement infrastructure. Modern police departments rely entirely on secure, interconnected digital networks to dispatch officers, transmit sensitive Criminal Justice Information Services data, and manage secure radio communications. Drones provide malicious cyber actors with a novel, three-dimensional method to completely bypass fortified physical perimeters and attack these sensitive networks directly from the sky, exploiting the growing convergence of physical and digital security vulnerabilities.
The technical mechanics of this specific threat are best exemplified by the “Dual-Drone Hack” incident. This was a highly sophisticated corporate espionage case targeted at an unnamed financial institution that perfectly illustrates the severe vulnerability of secured government facilities to aerial network incursions. In this complex operation, the attackers deployed a small reconnaissance drone equipped with a specialized device known as a WiFi Pineapple to hover near the secure facility. The device acted as a rogue wireless access point, intercepting internal network traffic and successfully harvesting the secure credentials and Media Access Control addresses of legitimate employees working deep inside the building.
Several days later, the attackers executed the second phase of the operation. A heavier payload drone landed directly on the facility’s roof, carrying a custom suite of hacking equipment including a Raspberry Pi microcomputer, a 4G cellular modem, and additional power supplies. Utilizing the credentials stolen during the initial reconnaissance flight, this airborne hacking terminal successfully breached the internal corporate network, effectively bridging the secure, isolated intranet to the public internet.
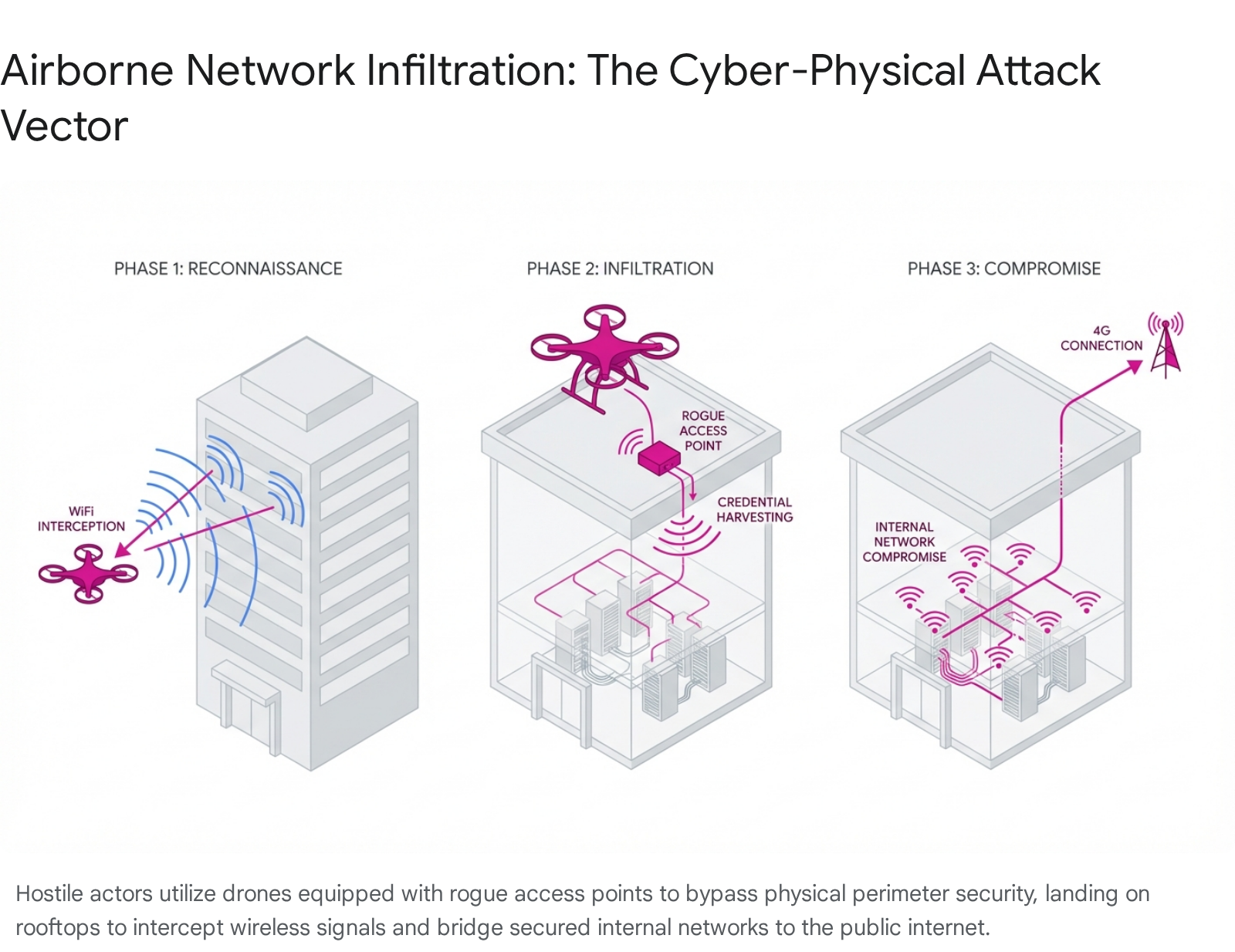
Municipal law enforcement facilities, secure evidence storage warehouses, and emergency operations centers are acutely vulnerable to this precise airborne cyber-physical attack vector. Drones can land undetected on the flat roofs of police headquarters, establishing persistent rogue access points that trick officer smartphones, automated license plate readers, and squad car mobile data terminals into connecting to a hostile network. Once connected, attackers can execute severe man-in-the-middle attacks, intercepting unencrypted tactical radio communications, altering vital dispatch data, or deploying crippling ransomware directly into the municipal server infrastructure.
Furthermore, as local governments increasingly adopt automated drone detection technologies to protect their airspace, the detection networks themselves become prime targets for cyber exploitation. As the Cybersecurity and Infrastructure Security Agency explicitly warns, malicious executables can be hidden within routine software or firmware updates required for detection systems. Additionally, the agency advises extreme caution regarding the widespread use of foreign-manufactured drones by local agencies. These platforms may contain fundamental software vulnerabilities or opaque data storage protocols that allow hostile foreign intelligence services to access sensitive law enforcement telemetry, operational imagery, and geographic routing data.
6. Contraband Delivery to Correctional Facilities
The continuous introduction of illicit materials into federal, state, and county correctional facilities remains a persistent, highly dangerous challenge for law enforcement agencies and prison administration. Drones have fundamentally revolutionized the illicit prison supply chain, providing a highly efficient, remarkably low-risk mechanism for transnational gangs and local criminal networks to entirely bypass external perimeter fencing, armed watchtowers, and thorough vehicular checkpoints. By hovering over open recreation yards at night or flying directly to specific, pre-coordinated cell windows, drones execute precise, remote-controlled airdrops of highly lucrative contraband directly into the hands of incarcerated individuals.
Comprehensive data published by the United States Sentencing Commission underscores the escalating severity of this specific crisis. A detailed review of federal prison contraband offenses prosecuted under Section 2P1.2 of the Guidelines Manual between fiscal years 2019 and 2023 reveals distinct patterns regarding the methods and materials of institutional smuggling. During this five-year period, a total of eight hundred and fifty-two individuals were federally sentenced for providing or possessing contraband in prison.
Table 1: United States Sentencing Commission Prison Contraband Data (FY 2019 – 2023)
The following data outlines the demographic characteristics and primary contraband types recovered during the Sentencing Commission’s review period, highlighting the extensive nature of the smuggling economy.
| Contraband Category | Percentage of Total Cases | Average Age of Offender | Percentage Non-U.S. Citizen | Primary Methods of Introduction |
| Cellular Telephones | 45.7% | 39 Years | 6.7% | Corrupt Staff (38.6%), Over Fence (21.4%), Mail (7.1%), Drone (7.1%) |
| Illicit Narcotics | ~33.0% | 37 Years | 4.1% | Visitation (38.3%), Mail (23.3%), Corrupt Staff (18.4%), Over Fence (4.4%) |
| Weapons | ~25.0% | 34 Years | 7.1% | Homemade internally (97.4%), Possess at Booking (1.0%) |
Source data derived from the United States Sentencing Commission Special Edition QuickFacts on Prison Contraband.
The geographic distribution of these offenses is highly concentrated. Over forty percent of all federal contraband cases were concentrated within the Eighth Circuit. This statistical anomaly is directly attributed to widespread smuggling activities at the Federal Correctional Complex at Forrest City, located in the Eastern District of Arkansas, which accounted for thirty-eight percent of all prison contraband cases where a sentence was imposed.
The specific materials delivered via these aerial incursions fundamentally destabilize the security environment of the prison. As the data indicates, almost half of the cases involved cellular telephones. The introduction of smartphones is particularly devastating to external law enforcement efforts. An unmonitored, secure cellular connection allows incarcerated gang leaders to continue orchestrating major criminal enterprises on the outside. They utilize these devices to order retaliatory violence against cooperating witnesses, coordinate regional drug trafficking operations, and manage illicit financial transactions directly from within their maximum-security cells.
Furthermore, the aerial delivery of highly potent, compact narcotics, such as synthetic fentanyl and concentrated synthetic cannabinoids, fuels a violently competitive internal black market. The resulting turf wars among rival inmate factions over the control of the drone-delivered contraband lead to severe assaults against inmates and extensive injuries to responding correctional officers. Despite widespread national awareness of the problem, local jail administrators remain severely restricted by archaic federal communications laws that strictly prohibit the use of radio frequency signal jamming technology. This prevents them from legally severing the command and control links of incoming drones, leaving their facilities acutely and continuously vulnerable to aerial resupply.
7. Disruption of Major Public Events and Mass Gatherings
Large-scale public events, including professional sporting championships, national political conventions, and sprawling outdoor music festivals, present highly concentrated, target-rich environments for both malicious drone operators and exceptionally reckless hobbyists. The immense density of the crowds and the open-air nature of these massive venues create an environment where even a minor aerial incident or mechanical failure can trigger catastrophic secondary consequences. Local law enforcement agencies tasked with securing these high-profile events must now look upward constantly, dedicating immense financial resources to monitor the airspace over stadiums that were fundamentally designed to manage ground-based crowd flow.
The threat profile at these major events is heavily skewed toward the “careless and clueless” demographic. Recreational pilots, eager to capture unique aerial footage of a stadium or a concert stage for social media broadcasting, routinely violate temporary flight restrictions implemented by the Federal Aviation Administration. A prominent example occurred during the Seattle Seahawks’ Super Bowl championship parade, where a joint state and federal defense team documented over thirty unauthorized drones operating simultaneously in the restricted airspace, with one pilot flying directly into the packed stadium environment despite explicit warnings.
During Super Bowl LIX in New Orleans in February 2025, the Federal Aviation Administration was forced to declare the airspace within a strict three-nautical-mile radius of the Caesars Superdome as a severe “No Drone Zone,” threatening violators with immediate confiscation of their aircraft, civil fines up to seventy-five thousand dollars, and potential federal criminal prosecution. While these rogue operators typically lack explicit malicious intent, the kinetic danger remains profound. A standard consumer drone weighing three to five pounds, if it suffers a mechanical rotor failure, experiences severe signal interference, or simply depletes its battery, will plummet into the densely packed crowd below. It acts as an unguided, high-velocity projectile capable of causing severe blunt force trauma or deep lacerations.
Beyond the direct, kinetic impact hazard, the sudden presence of an unauthorized drone can induce widespread, uncontrollable panic. In an era hyper-vigilant to the threat of domestic terrorism, the sudden appearance of a buzzing, unidentified aircraft hovering over a grandstand can trigger an immediate stampede as thousands of spectators attempt to flee a perceived chemical or explosive attack. This mass exodus can easily result in severe crush injuries and trampling fatalities, rapidly turning a nuisance flight into a mass casualty incident.
The logistical challenge for police commanders is acute. Identifying a single operator holding a small controller in a crowd of tens of thousands is akin to finding a needle in a haystack. Furthermore, executing a kinetic takedown of the drone over a crowd introduces an unacceptable risk of collateral damage from falling debris. As the United States prepares to host massive international events, including the 2026 FIFA World Cup and the 2028 Summer Olympics, federal agencies are aggressively attempting to bolster local defenses. The Federal Emergency Management Agency recently awarded two hundred and fifty million dollars through a specialized grant program to the eleven World Cup host states specifically to enhance their capabilities to detect and monitor these aerial threats.
8. Surveillance of Critical Infrastructure
The robust protection of critical infrastructure is a core, foundational mandate of homeland security, requiring extensive, daily coordination between private sector utility operators and local law enforcement. Drones provide hostile nation-states, organized terrorist organizations, and domestic saboteurs with an unparalleled, highly evasive tool for conducting covert reconnaissance of these vital societal lifelines. By utilizing high-resolution optical zoom cameras, advanced thermal imaging sensors, and light detection and ranging payloads, adversaries can meticulously map the physical vulnerabilities of regional power grids, water purification plants, telecommunications hubs, and volatile energy pipelines from a completely safe standoff distance.
This persistent aerial surveillance is the absolutely necessary precursor to executing devastating physical or cyber attacks. Adversaries utilize drones to identify the precise geographic locations of critical, hard-to-replace transformers, map the routine patrol routes of private security guards, and locate the operational blind spots in perimeter camera networks. Particularly alarming are the persistent, highly coordinated reports of drone incursions over the nation’s most sensitive nuclear power infrastructure. Comprehensive security investigations have documented multiple, highly suspicious drone flights over facilities such as the Palo Verde Nuclear Generation Station in Arizona. These specific flights, occurring frequently at night and often utilizing coordinated multi-drone formations, exhibit a level of technical sophistication that strongly suggests organized intelligence gathering by capable actors, rather than amateur curiosity.
Recognizing the severity of this intelligence gathering threat, the Nuclear Regulatory Commission updated its federal regulations in 2024 to strictly require all nuclear power plant licensees to immediately report any sightings of drones over their facilities to the Commission, the Federal Aviation Administration, the Federal Bureau of Investigation, and local law enforcement agencies. Similar massive intelligence gathering efforts have been observed near vital military installations. In late 2024, widespread reports of drone swarms emerged across New Jersey and Pennsylvania, with highly concerning sightings verified over the Picatinny Arsenal and Naval Weapons Station Earle.
When facility managers or military personnel detect these incursions, the immediate, heavy burden of the physical response falls directly upon local and county law enforcement agencies. Municipal officers and county deputies are dispatched to rapidly scour the surrounding rural or industrial landscapes in a usually futile attempt to locate the pilot hiding in the darkness. This dynamic forces local police into a highly reactionary posture, expending valuable patrol resources and manpower to chase shadows. The intelligence gathered by these hostile drone flights is invariably used to optimize future attacks, ensuring that when an adversary ultimately decides to strike a critical node of the American economy, they will do so with intimate, real-time knowledge of the facility’s specific physical vulnerabilities and the exact expected response times of local law enforcement.
9. Targeted Harassment and Privacy Violations Against Personnel
The psychological well-being, personal safety, and operational security of law enforcement personnel are under novel, persistent attack through the deliberate weaponization of drones for targeted harassment and extreme privacy invasion. The unique ability of a consumer drone to hover silently outside a second-story bedroom window, peer effortlessly over high backyard privacy fences, and continuously track a personal vehicle from the sky transforms the technology into a profound instrument for organized stalking and severe intimidation. Sophisticated criminal organizations, retaliatory gang members, and anti-government extremists are increasingly leveraging this aerial capability to surveil the private residences of police officers, federal judges, prosecuting attorneys, and highly vulnerable confidential informants.
This targeted, deeply personal aerial harassment serves multiple malicious purposes. First, it is utilized as a sophisticated form of witness intimidation and psychological warfare. By continuously flying drones over an officer’s private home, criminal syndicates send a clear, chilling message that the officer and their family are entirely vulnerable and constantly being monitored. This significantly degrades the morale of the police force and can influence the aggressive pursuit of justice in local courts. Second, the surveillance is actively used to gather actionable intelligence for planned retaliatory violence. Drones can silently track an officer’s daily routine, identifying the exact times they depart for their patrol shift, the personal vehicles they drive, and the highly vulnerable periods when their spouses or children are left alone.
The use of drones to intimidate personnel and the public was heavily scrutinized during immigration enforcement surges in Minnesota. During periods of heightened operations by Immigration and Customs Enforcement, local residents and civic activists reported numerous incidents of drones hovering outside their residential windows at night, creating a severe climate of fear and perceived government or vigilante intimidation.
The complex legal frameworks governing constitutional protections and reasonable expectations of privacy are currently struggling immensely to adapt to this new technology. Transparency advocates and citizens are increasingly challenging how law enforcement utilizes drone video. A recent, highly publicized lawsuit in Chula Vista, California, which reached the state Supreme Court in 2024, highlighted extreme community concerns regarding police drones flying over private residences and the public’s subsequent right to access that surveillance footage.
Conversely, protecting private citizens and off-duty police officers from civilian drone harassment is immensely complex. In cases such as Long Lake Township v. Todd Maxon and the Williamson Supreme Court petition, courts are grappling with whether the continuous, targeted aerial observation of a fenced backyard constitutes an illegal search or a fundamental invasion of privacy. Existing municipal stalking and voyeurism statutes are often incredibly difficult to apply in these scenarios because the drone operator remains geographically detached and hidden from the aircraft. This makes it exceptionally challenging for responding patrol officers to prove criminal intent or definitively link the harassing aircraft hovering overhead to a specific suspect standing several blocks away holding a controller. This creates a persistent climate of vulnerability, where law enforcement personnel find their sanctuaries violated by an unblinking, remote-controlled eye.
10. Public Safety Hazards from Malfunctioning or Reckless Operations
While highly sophisticated criminal usage appropriately captures the most attention from intelligence analysts, the sheer, overwhelming volume of recreational drones operating daily introduces a pervasive and persistent public safety hazard that chronically drains vital law enforcement resources. The Federal Aviation Administration estimates that millions of drones currently operate within the national airspace system, with well over a million formally registered to users. The vast majority of these flights are conducted by enthusiastic hobbyists possessing minimal to zero formal training in aviation safety, airspace regulations, or aeronautical navigation. This rapid democratization of the low-altitude airspace results in a continuous, daily stream of incidents involving reckless operation, sudden mechanical failures, and highly disruptive mid-flight collisions with civic infrastructure.
Local municipal police departments and county sheriffs are the default first responders for all such incidents. Patrol officers are routinely dispatched to investigate reports of drones crashing violently into residential rooftops, becoming dangerously entangled in high-voltage municipal power lines, or interfering with local vehicular traffic on busy highways. Each seemingly minor incident requires a thorough, time-consuming investigation by officers to ensure no property damage occurred, to safely retrieve the potentially hazardous, fire-prone lithium-ion batteries, and to attempt to identify and cite the negligent operator.
During heightened periods of public anxiety, the strain on emergency dispatch centers becomes overwhelming. During the mass drone sighting panic in the northeastern United States in late 2024 and early 2025, federal investigators and local 911 centers were inundated with over five thousand reports from highly concerned citizens reporting mysterious lights and formations in the sky. While the vast majority of these sightings were eventually determined by the Federal Bureau of Investigation to be lawful commercial drones, misidentified conventional aircraft, or simple atmospheric phenomena, the operational response required immense resources.
This phenomenon creates a severe and highly dangerous “cry wolf” dynamic within dispatch centers. The overwhelming noise of benign, albeit highly reckless, drone operations masks the faint signal of genuine, malicious threats targeting critical infrastructure. Law enforcement agencies suffer from severe alarm fatigue, expending massive amounts of patrol hours investigating petty neighborhood disputes over hovering drones or teenagers crashing toys in public parks. This constant diversion of patrol resources degrades the rapid response capability of the police department for acute emergencies, effectively forcing municipalities to utilize local public safety funds to manage a chaotic and largely unregulated low-altitude federal airspace.
11. The Exploitation of Legislative and Mitigation Authority Gaps
The overarching, systemic vulnerability that magnifies and exacerbates all preceding ten threats is the severe legal and technological restriction currently placed upon local law enforcement regarding the active mitigation of malicious drones. The United States currently faces a profound national security paradox. While local municipal police officers and county deputies are invariably the first to arrive at the scene of a drone incident, they are strictly, legally prohibited from utilizing the technology required to stop it. The national airspace is governed exclusively by the federal government, and drones are legally classified as “aircraft” under federal aviation law.
Consequently, any attempt by a local sheriff’s deputy or municipal police officer to utilize electronic warfare to jam the radio frequency of a drone, spoof its navigation system, or kinetically shoot it down constitutes a severe federal felony. These actions violate federal statutes codified in Title 18 and Title 49 of the United States Code, which were originally designed decades ago to protect commercial airliners from sabotage and to prevent the unauthorized disruption of critical telecommunications networks. The legal authority to actively mitigate a threatening drone is strictly reserved for a highly limited number of federal agencies, primarily specialized units within the Department of Homeland Security and the Department of Justice.
However, federal agents cannot be omnipresent. The federal government simply lacks the massive personnel required to simultaneously protect every local sports stadium, every county jail, and every municipal power substation across the country. The federal government acknowledges that it can respond to only a tiny fraction of the thousands of counter-drone assistance requests generated by local jurisdictions annually.
Table 2: Drone Threat Vectors and Law Enforcement Impact Taxonomy
The following taxonomy categorizes the primary threat profiles and their downstream operational impact on local police departments.
| Threat Category | Primary Threat Actor | Mechanism of Action | Impact on Law Enforcement |
| Kinetic / Terrorism | Violent Extremists, Lone Wolves | Explosive payload delivery, chemical dispersal, infrastructure sabotage. | Mass casualty response, complex explosive ordnance disposal, catastrophic infrastructure failure. |
| Obstruction / Counter-Surveillance | Transnational Criminal Organizations, Cartels | Live-streaming tactical movements, monitoring border patrol gaps, counter-SWAT observation. | Loss of tactical surprise, increased risk of officer ambush, destruction of evidence. |
| Aviation Interference | Reckless Hobbyists, Hostile Actors | Flying in restricted flight paths, buzzing low-altitude helicopters. | Grounding of life-saving air ambulances and police air support, risk of fatal midair collisions. |
| Cyber Exploitation | Advanced Cyber Criminals, Espionage Actors | Deploying rogue access points (WiFi Pineapples) onto secure facility roofs. | Compromise of sensitive criminal databases, interception of secure communications, network ransomware. |
| Contraband Smuggling | Prison Gangs, Outside Criminal Associates | Bypassing perimeter fencing to drop narcotics, phones, and weapons. | Increased institutional violence, continued orchestration of outside crimes from within maximum security. |
Legislative efforts are currently underway to address this fatal gap. Bills such as the Safeguarding the Homeland from the Threats Posed by Unmanned Aircraft Systems Act (S. 4687) and the Counter-UAS Authority Security, Safety, and Reauthorization Act (H.R. 5061) attempt to expand vital mitigation authorities to specially trained state, local, tribal, and territorial law enforcement agencies through pilot programs. These bills aim to provide local authorities with the approved technology needed to safely interdict drones threatening major events or critical infrastructure. However, until such comprehensive legislation is fully enacted, standardized, and funded, local police remain in a purely observational role. They can watch a drone hover over a crowded stadium, they can watch it drop lethal fentanyl into a prison yard, and they can watch it systematically survey a vulnerable power plant, but they lack the legal authority to press the button that severs the drone’s connection to its pilot. This severe legislative paralysis is aggressively exploited by malicious actors who operate with the full, highly calculated knowledge that local police are virtually powerless to stop them in the air.
12. Conclusion
Unmanned Aircraft Systems have irreversibly altered the fundamental security architecture of the United States. The proliferation of this technology has effectively collapsed the immense distance between foreign battlefields and domestic cities, placing the highly sophisticated capabilities of persistent aerial reconnaissance and precision kinetic strike directly into the hands of anyone with a credit card and malicious intent. The ten distinct threat vectors exhaustively analyzed in this report illustrate a comprehensive, multi-domain assault on the traditional methodologies and physical structures of civilian law enforcement. From blinding federal tactical teams during hostage rescues and grounding vital medical helicopters, to breaching highly secure cyber networks and terrorizing patrol officers at their private residences, drones represent a profound asymmetric advantage currently held by the adversary.
Effectively addressing this complex, rapidly evolving threat requires a massive paradigm shift in homeland security strategy. It necessitates completely abandoning the outdated premise that the lower airspace is the exclusive, highly regulated domain of federal agencies. State and local law enforcement officers, who are invariably the first responders to any aerial crisis, must be legally empowered, adequately funded, and rigorously trained to deploy advanced radio-frequency detection networks and active, safe mitigation technologies. Without bridging the critical, dangerous gap between exclusive federal authority and highly restricted local response capabilities, the United States law enforcement community will remain fundamentally unequipped to protect the public from the escalating threats descending from the sky.
13. Appendix: Analytical Approach
The synthesis and structured analysis contained within this research report rely upon a comprehensive qualitative review of primary intelligence bulletins, verified congressional testimony, and federal agency datasets generated between the years 2018 and early 2026. The conceptual foundation of the threat matrix was systematically constructed utilizing the Department of Homeland Security’s 2025 Homeland Threat Assessment, the Cybersecurity and Infrastructure Security Agency’s Unmanned Aircraft System Detection Technology Guidance, and joint public safety advisories issued collaboratively by the Federal Bureau of Investigation, the Department of Defense, and the Federal Aviation Administration.
To ensure an exhaustive and highly nuanced scope, the analysis critically evaluated three distinct operational domains impacting law enforcement: physical security, cybersecurity, and aviation safety. Quantitative data concerning aviation incursions was drawn directly from Federal Aviation Administration sighting reports and NASA Aviation Safety Reporting System logs. Statistics regarding correctional facility vulnerabilities and smuggling methodologies were sourced directly from the United States Sentencing Commission’s Special Edition QuickFacts on Prison Contraband. Critical case studies, such as the November 2024 Nashville power substation explosive plot and the Denver FBI counter-surveillance incident, were integrated to provide vital empirical validation of the identified theoretical threats. The culmination of these primary sources facilitated the precise identification of the top ten distinct threat vectors currently challenging the operational integrity and physical safety of the United States law enforcement community.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Works Cited
- https://portal.cops.usdoj.gov/resourcecenter/content.ashx/cops-w0894-pub.pdf
- https://www.dhs.gov/sites/default/files/2024-10/24_0930_ia_24-320-ia-publication-2025-hta-final-30sep24-508.pdf
- https://www.fbi.gov/news/press-releases/dhs-fbi-faa-and-dod-joint-statement-on-ongoing-response-to-reported-drone-sightings
- https://www.justice.gov/opa/pr/man-pleads-guilty-attempting-use-weapon-mass-destruction-and-attempting-destroy-energy
- https://www.theguardian.com/us-news/2024/nov/05/white-supremacist-drone-plot-nashville-power-plant
- https://www.justice.gov/archives/opa/pr/man-arrested-and-charged-attempting-use-weapon-mass-destruction-and-destroy-energy-facility
- https://www.defenseone.com/technology/2018/05/criminal-gang-used-drone-swarm-obstruct-fbi-raid/147956/
- https://www.airsight.com/en/news/criminals-used-a-drone-swarm-to-obstruct-surveil-an-fbi-hostage-raid
- https://thedebrief.org/we-are-going-to-have-a-catastrophic-event-drone-incursions-in-restricted-airspace-are-surging-in-2025/
- https://www.policechiefmagazine.org/new-realities-drone-proliferation/
- https://d-fendsolutions.com/blog/unauthorized-drone-operations-in-critical-areas-lessons-from-the-norwich-incident/
- https://www.portnox.com/blog/cyber-attacks/cybercrime-takes-flight-the-case-of-the-dual-drone-hack/
- https://www.cisa.gov/topics/physical-security/be-air-aware/uas-cybersecurity
- https://www.ussc.gov/sites/default/files/pdf/research-and-publications/data-briefings/transcript_2025-Prison-Contraband.pdf
- https://www.unmannedairspace.info/counter-uas-systems-and-policies/lack-of-drone-detection-equipment-contributes-to-rise-in-prison-drug-deliveries/
- https://dronelife.com/2025/02/05/super-bowl-security-the-growing-challenge-of-unauthorized-drones-over-stadiums/
- https://www.cbsnews.com/news/super-bowl-drones-flights-banned-big-game/
- https://www.fema.gov/fact-sheet/notice-funding-opportunity-nofo-counter-unmanned-aircraft-systems-c-uas-grant-program
- https://www.flyingmag.com/world-cup-security-ondascounter-drone-uas/
- https://www.dedrone.com/blog/the-importance-of-anti-drone-systems-in-power-plants
- https://www.nrc.gov/reading-rm/doc-collections/fact-sheets/fs-drone-pwr-plant-security
- https://www.mprnews.org/story/2026/03/13/minnesota-drone-sightings-drove-surveillance-fears-as-ice-surged
- https://www.aclu.org/news/privacy-technology/drones-for-intimidation
- https://calmatters.org/commentary/2024/06/chula-vista-police-drone-lawsuit/
- https://problemsolverscaucus.house.gov/media/press-releases/problem-solvers-caucus-endorses-bill-to-protect-communities-from-threats-posed-by-drones
- https://www.hsgac.senate.gov/media/dems/on-senate-floor-senator-peters-urges-colleagues-to-pass-his-bipartisan-bill-to-address-threats-from-drones/
