1. Executive Summary
The character of modern warfare is undergoing a profound transformation driven by the rapid proliferation, integration, and continuous evolution of uncrewed aerial systems (UAS). As the United States Department of Defense (DoD) prepares for massive investments in drone technology, a critical strategic vulnerability remains under-addressed by military and defense planners: the speed at which peer and near-peer adversaries observe, adapt to, and counter technological advantages. While domestic defense discussions frequently fixate on the acquisition of exquisite platforms and the expansion of domestic drone fleets, the operational reality dictates that the platform itself is merely the most visible component of a highly complex, multidomain capability. The ongoing conflicts in Eastern Europe and the Middle East serve as real-world laboratories, demonstrating that advantage in modern combat is no longer strictly derived from possessing the most advanced technology at the onset of hostilities. Instead, military advantage is increasingly dictated by the speed of the adaptation cycle—the ability to field a capability, observe the enemy’s countermeasures, and deploy a counter-countermeasure before the adversary can institutionalize their defense.1
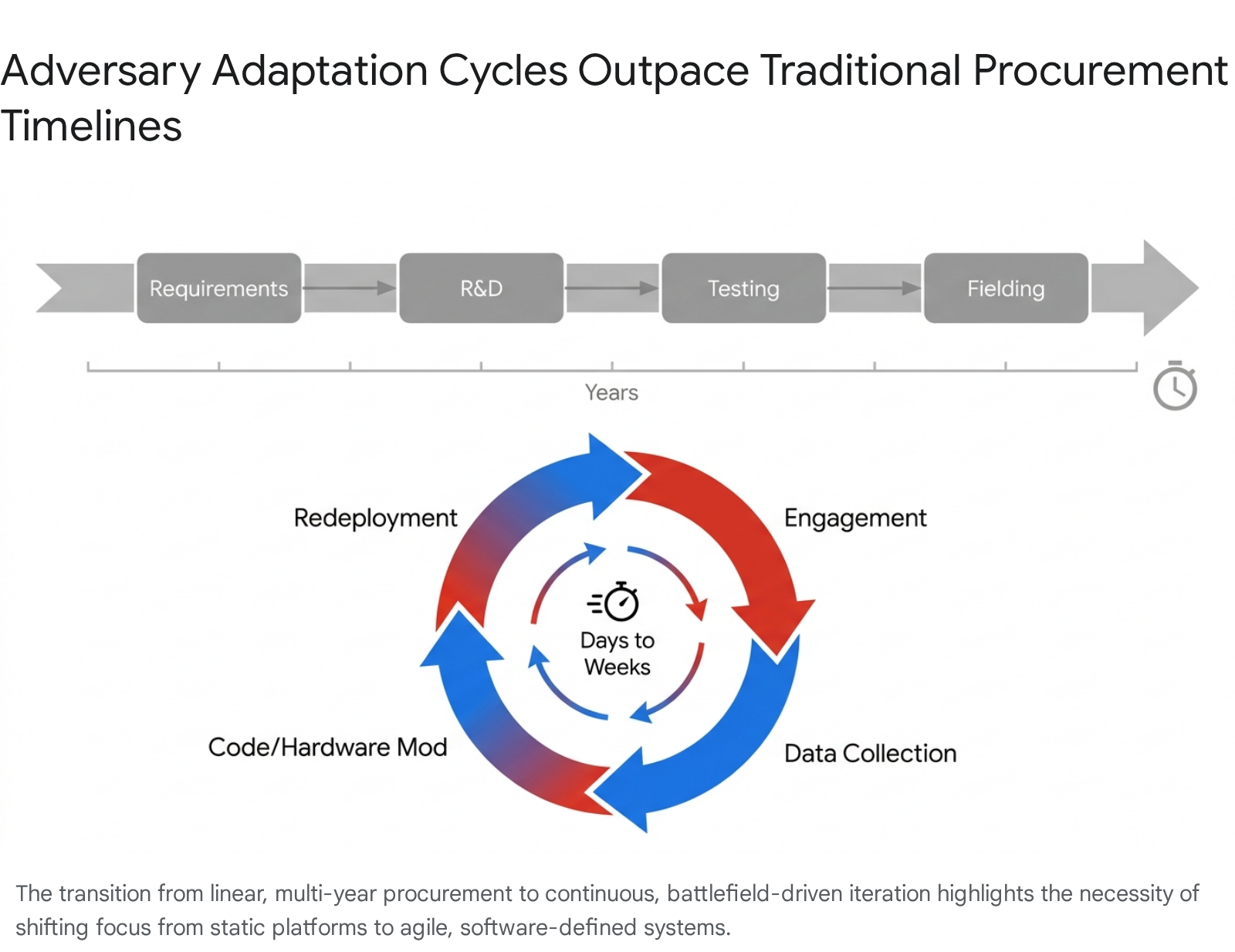
In these contemporary operational environments, the development cycle for adversary countermeasures has compressed from years to months, and in some tactical scenarios, to mere days.3 This report synthesizes national intelligence and military analysis to outline the systemic requirements necessary for the DoD to design, build, operate, and evolve UAS capabilities in a highly contested environment. It assesses the overlooked mechanisms of enemy adaptation, particularly the rapid exploitation and reverse-engineering of captured U.S. technology, and the fielding of advanced electronic warfare (EW) and directed energy (DE) countermeasures.5 Furthermore, this assessment details the organizational agility required to transition from a static, platform-centric procurement model to a dynamic, continuous capability-evolution model.
The traditional paradigm of military technological superiority relies on a linear process of research, development, testing, and fielding, often spanning a decade or more. Once a system is fielded, it is expected to provide an asymmetric advantage for years before an adversary develops a viable countermeasure. The proliferation of commercial-off-the-shelf (COTS) drone technology, combined with the democratization of digital command and control networks, has shattered this paradigm.2 To achieve decision dominance and outpace the adversary adaptation cycle, the DoD must rethink its approach to supply chain resilience, spectrum management, tactical-edge fabrication, and the integration of artificial intelligence into command and control architectures.8 The central thesis of this report is that the United States military must weaponize the learning cycle itself, transitioning to an organizational model capable of deploying updates, counter-measures, and hardware modifications at operationally relevant speeds.1
2. The Accelerating Adversary Adaptation Cycle
The operational environment has shifted definitively toward an era characterized by precise mass, where adversaries utilize large volumes of low-cost, expendable uncrewed systems to overwhelm sophisticated, legacy defense networks.2 Within this paradigm, the most significant threat is not the initial capability of the adversary’s drone swarm, but rather the speed at which the adversary organization learns, adapts, and implements changes based on operational contact with U.S. and allied forces.
The Shift to Adaptation in Contact
The concept of Adaptation in Contact describes a closed-loop learning cycle where operational engagement generates immediate technical data, which is then used to rapidly update tactics, software, electromagnetic signatures, and hardware configurations.1 Validated changes are deployed back to the tactical edge before the adversary can fully react. By applying this infrastructure for adaptation, a military force can turn deterrence into a measurable control problem, running calibrated moves to observe adversary responses and learning which changes reliably create uncertainty without waiting for a systemic crisis.1
In the Russo-Ukrainian conflict, tactical adaptation occurs at an unprecedented velocity. Russian forces are observed altering their drone flight routes, antenna configurations, and guidance methods every few weeks to bypass Ukrainian electronic warfare bubbles.2 When traditional radio-frequency (RF) links are successfully jammed, adversaries quickly transition to fiber-optic tethers or autonomous terminal guidance driven by machine vision, rendering sophisticated RF jammers obsolete.6 This iterative process means that a brilliant tactical innovation or a new highly capable drone model provides only a fleeting advantage. A capability fielded on Monday may be neutralized by Friday if the organization lacks the infrastructure to push software updates or modular hardware changes continuously.3
This compression of the innovation cycle challenges the foundational assumptions of the U.S. defense acquisition process. The Joint Capabilities Integration and Development System (JCIDS), optimized for acquiring exquisite, highly survivable platforms over multi-year timelines, is structurally incapable of matching the pace of Adaptation in Contact.13 Consequently, the DoD frequently fields systems that are technologically advanced but tactically outdated upon deployment, as adversaries have already observed prototypes, mapped electromagnetic signatures, and developed appropriate countermeasures.
The Adversary Entente and Collaborative Knowledge Sharing
The speed of adaptation is heavily compounded by the emergence of a collaborative adversary learning bloc—primarily comprising the Russian Federation, the People’s Republic of China (PRC), the Islamic Republic of Iran, and North Korea.2 This network functions as a connected knowledge market where strategic and tactical lessons derived from contact with Western systems are rapidly disseminated, creating a compounding effect on military innovation.
The relationships between these nations have evolved past transactional arms sales into deeply integrated technical cooperation. For instance, the battlefield data gathered by Russian forces regarding the vulnerabilities of U.S. precision-guided munitions and drones to specific EW frequencies is almost certainly analyzed in conjunction with Chinese technical experts.16 China, possessing the world’s most extensive commercial drone manufacturing base, provides the component supply chain—including mesh networking modems, navigation sensors, and specialized microelectronics—that allows Russia and Iran to modify their systems to bypass newly discovered Western defenses.18
This two-way partnership ensures that when the U.S. military deploys a new platform or countermeasure in one theater, the defensive solutions developed against it will quickly proliferate to adversaries in entirely different geographic commands.2Iranian operational concepts, such as launching mixed salvos of inexpensive drones and ballistic missiles to saturate air defenses, are refined based on Russian combat experience and enabled by Chinese industrial capacity.20Consequently, U.S. forces must anticipate that any operational deployment of a new UAS capability will instantly trigger a distributed, multinational effort to identify its vulnerabilities and reverse-engineer its strengths.
3. Technical Exploitation and the Speed of Reverse Engineering
A frequent oversight in U.S. strategic planning is the underestimation of the timeline required for peer adversaries to capture, reverse-engineer, and operationalize advanced uncrewed systems. The U.S. military has historically relied on the complexity of its systems to serve as a barrier to exploitation. However, the modular nature of modern drone technology, combined with the adversary’s willingness to integrate COTS components into military airframes, has drastically reduced the friction of reverse engineering.
Historical Precedents and the Compression of Exploitation Time
The operational history of U.S. drone deployments reveals a consistent pattern of adversary technical exploitation. The most prominent example occurred in December 2011, when an American Lockheed Martin RQ-170 Sentinel stealth drone was captured largely intact by Iranian forces utilizing electronic spoofing and cyberwarfare techniques.22 Despite initial Western assessments that Iran lacked the industrial base to fully exploit the technology, Iranian aerospace organizations successfully decoded the data and reverse-engineered the platform.23 This effort directly resulted in the production of the Shahed 171 Simorgh and Shahed Saeqeh—jet-powered, flying-wing combat drones that incorporate the radar-evading geometry of the original U.S. platform while utilizing Iranian and Chinese internal components.24
Similarly, the capture of U.S. ScanEagle drones led to Iranian domestic production lines that subsequently supplied proxy forces across the Middle East, effectively turning U.S. surveillance assets into adversary strike capabilities.23 China has exhibited similar capabilities over decades, having previously reverse-engineered Israeli Harpy loitering munitions to produce the ASN-301 26, and having utilized components of downed U.S. target drones to jumpstart its early UAV programs, such as the Chang Kong-1 and WZ-5.5
The success of these reverse-engineering efforts relies on a strategy of pragmatic integration. Adversaries do not attempt to perfectly replicate every U.S. microchip or proprietary software algorithm. Instead, they clone the aerodynamic properties and structural designs, and then populate the airframe with commercially available, unregulated components.29 The Iranian Shahed-136, for example, utilizes a delta-wing design paired with a reverse-engineered German Limbach L 550 engine, navigated by Chinese GNSS modules.29 This modular approach bypasses complex manufacturing bottlenecks and accelerates the time from capture to deployment.
| Captured Western Asset | Adversary Derivative | Mechanism of Exploitation | Strategic Impact on U.S. Operations |
| RQ-170 Sentinel (U.S.) | Shahed 171 Simorgh / Saeqeh (Iran) | Cyber-spoofing forced landing; aerodynamic cloning. | Proliferation of stealth-geometry combat drones to state and non-state proxies. |
| ScanEagle (U.S.) | Yasir (Iran) | EW interception; component reverse engineering. | Erosion of U.S. tactical ISR dominance in the maritime domain. |
| Harpy (Israel) | ASN-301 (China) | Direct acquisition and technical analysis. | Development of indigenous anti-radiation loitering munitions to target air defenses. |
| Various Commercial UAS | Geran-2 (Russia) | Technology transfer from Iran; integration of Russian mesh modems. | Massive saturation attacks on critical infrastructure; exhaustion of kinetic interceptor stockpiles. |
The Modern Formalized Exploitation Pipeline
Today, the exploitation pipeline is highly formalized and significantly faster. Adversaries have established dedicated intelligence and engineering task forces whose sole purpose is to recover downed Western UAS, extract the encrypted firmware, analyze the communication protocols, and identify hardware supply chain origins.31
The implications are severe for programs that aim to mass-produce attritable drones. If the U.S. deploys thousands of autonomous systems into contested airspace, a statistically significant number will inevitably fall into enemy hands intact—either through kinetic disablement, EW forced-landings, or mechanical failure.33 Once captured, adversaries do not necessarily need to replicate the entire system to defeat it. By analyzing the drone’s logic boards, sensor suites, and navigation algorithms, adversary engineers can identify the exact frequency hopping patterns, optical recognition parameters, and autonomous decision trees the drone relies upon.35
This technical intelligence allows the adversary to calibrate their EW jammers and directed energy weapons specifically to the vulnerabilities of the U.S. swarm within weeks of the platform’s initial deployment. Furthermore, the integration of advanced artificial intelligence into cyber operations has dramatically reduced the time required to find and exploit software vulnerabilities. As demonstrated by recent developments in frontier AI models capable of autonomously discovering zero-day vulnerabilities and generating working exploits without human guidance, the timeline for software exploitation has shifted from months to days.37 If an adversary captures an uncrewed system with vulnerable firmware, the associated attack paths can be mapped and disseminated across the adversary entente almost instantaneously, rendering entire fleets of U.S. drones susceptible to hijacking or disruption.
4. Overlooked Adversary Countermeasures: Electronic Warfare
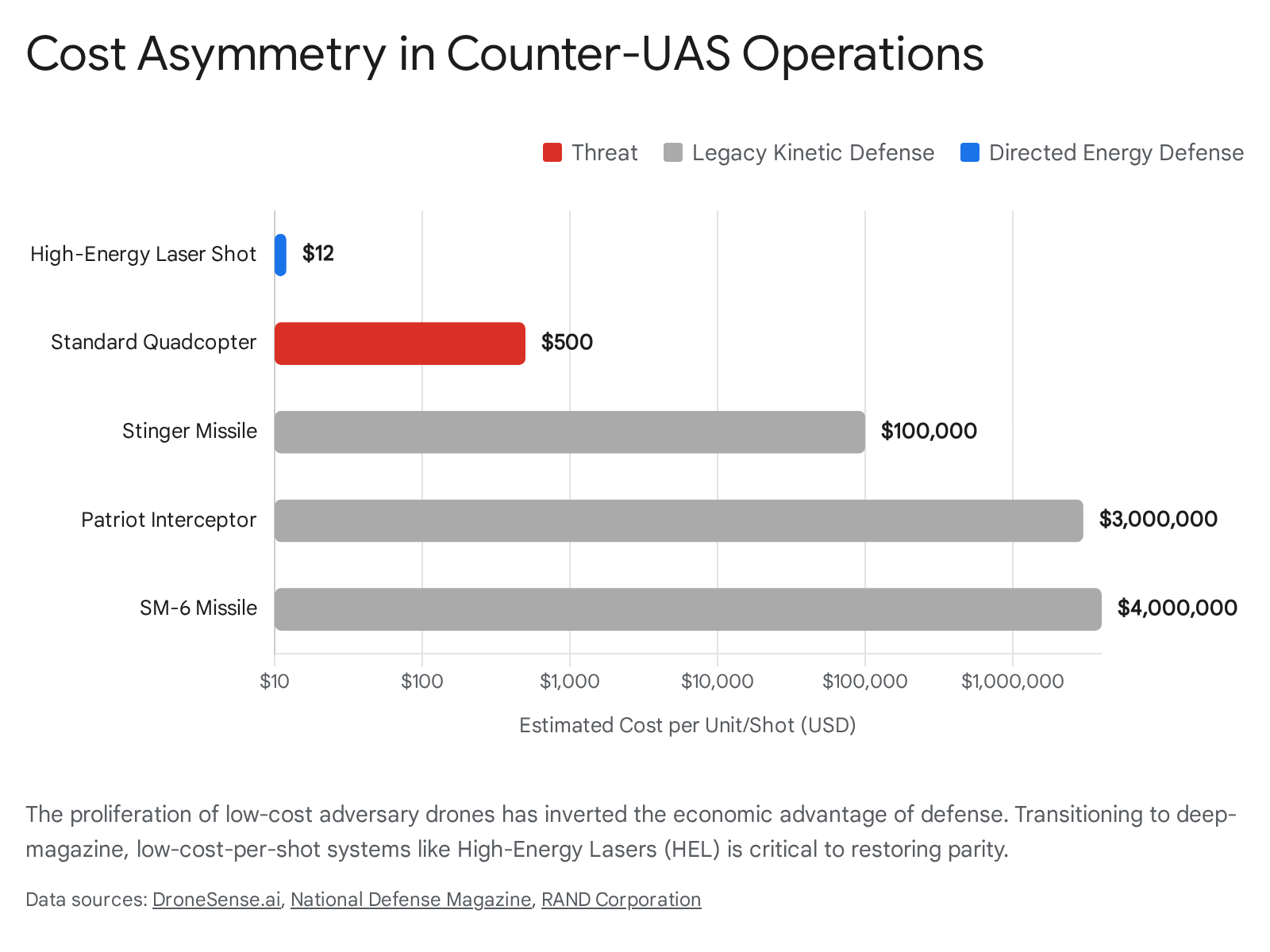
The proliferation of cheap, autonomous UAS has fundamentally altered the economics of air defense. The U.S. has historically relied on highly capable, exquisite kinetic interceptors to defeat aerial threats. However, when a defender is forced to expend a $3 million Patriot missile or a $100,000 Stinger missile to destroy a $30,000 Shahed-136 or a $500 commercial quadcopter, the attacker wins the economic exchange ratio regardless of the tactical outcome.10 Adversaries acutely understand this cost asymmetry and are deliberately fielding drone swarms to bankrupt defender magazines and exhaust logistical supply lines.
While the U.S. military has recognized this challenge and initiated the development of cost-effective countermeasures, there remains a systemic failure to appreciate how rapidly peer adversaries—specifically China and Russia—are deploying their own non-kinetic defenses, particularly electronic warfare, to neutralize incoming U.S. uncrewed systems.
The Maturation of Adversary Electromagnetic Warfare
Russia and China view the electromagnetic spectrum (EMS) not merely as an enabling environment, but as a primary maneuver space and warfighting domain, and have invested heavily in EW capabilities to deny U.S. forces access to it.39 The Russian deployment of EW in Ukraine has been characterized as the densest electromagnetic environment in modern military history, exposing the vulnerabilities of systems reliant on persistent connectivity.11
Adversary EW strategies focus on disrupting the crucial links that uncrewed systems rely upon: GPS/GNSS navigation signals, satellite communications, and operator command-and-control (C2) data links. By projecting high-powered interference, Russian systems have successfully blinded the navigation suites of highly sophisticated Western precision-guided munitions—such as Excalibur artillery shells and HIMARS rockets—rendering them tactically ineffective and forcing a rapid reevaluation of their utility.11
Against drone swarms, adversary EW aims to sever the connection between the drones and their operators, or between the drones themselves. Without resilient mesh networking and autonomous fallback protocols, a drone swarm subjected to severe broadband jamming will lose cohesion, drift off course, or trigger automatic landing protocols, effectively neutralizing the threat without the adversary firing a single kinetic shot.42 The sheer volume of EW activity also creates a secondary problem: the degradation of Identity Friend or Foe (IFF) systems. In a saturated airspace, defenders struggle to distinguish between incoming adversary attack drones and returning friendly autonomous assets. This “duck test” ambiguity reduces response times and has directly contributed to fatal incidents where U.S. forces failed to engage hostile drones due to confusion with friendly signatures.43
The Cat-and-Mouse Game of Spectrum Dominance
The struggle for electromagnetic dominance is not static; it is a continuous cycle of measure and countermeasure. When Ukrainian forces successfully employed portable EW systems to spoof the navigation of Russian Shahed drones, Russian engineers quickly adapted.44 To counteract localized jamming, Russian forces began integrating Chinese-made mesh modems for resilient radio links, installing controlled reception pattern antennas (CRPA) to filter out interference, and utilizing mothership drones to relay signals to first-person-view (FPV) attack drones operating deep in the rear.18
The most significant adaptation has been the shift away from the electromagnetic spectrum entirely. To bypass the densest EW bubbles, adversaries are increasingly deploying drones guided by physical fiber-optic tethers, which are completely immune to RF jamming and spoofing.6 Alternatively, they are integrating autonomous terminal guidance driven by machine vision and artificial intelligence, allowing the drone to navigate to the target using terrain recognition and optical matching even when GPS and C2 links are severed.12
If the DoD fields thousands of attritable drones relying on standard RF communications and GPS navigation, they will be swiftly neutralized by peer adversary EW complexes. To survive, U.S. systems must be designed from inception with cognitive EW capabilities—AI-driven radios capable of sensing spectrum interference and seamlessly hopping frequencies, or transitioning to alternative navigation aids when the primary spectrum is denied.42
5. Overlooked Adversary Countermeasures: Directed Energy Weapons
Perhaps the most significant overlooked threat to U.S. drone deployments is the adversary’s rapid advancement and operationalization of Directed Energy Weapons (DEW). For decades, DEWs were viewed as experimental technology relegated to laboratories and controlled test ranges. Today, driven by the urgent need to counter the precise mass of drone swarms, these systems are transitioning into deployable, operational assets on the battlefield.40
Both China and Russia are actively fielding DEW systems designed specifically for the counter-UAS (C-UAS) mission, recognizing that directed energy is the only defense capable of inverting the unsustainable cost-exchange ratio of drone warfare.6 These weapons fall primarily into two functional categories: High-Energy Lasers and High-Power Microwaves.
High-Energy Lasers (HEL)
HEL systems utilize focused light to physically burn through the optical sensors, control surfaces, or battery compartments of an incoming drone. By delivering destructive energy at the speed of light, lasers eliminate the need for complex target-leading calculations required by kinetic anti-aircraft artillery. Furthermore, with a stable power source, lasers offer an effectively infinite magazine, allowing for continuous engagement without the logistical burden of physical reloading.50
China has prioritized the development of HEL systems to protect critical infrastructure and ground forces. They have demonstrated multiple ground-based and vehicle-mounted laser systems, such as the Silent Hunter, which boasts a power output of 30 to 100 kilowatts. This is sufficient to destroy the structural components of small to medium uncrewed aerial vehicles at ranges of up to 4 kilometers.49 Russia has similarly deployed the Peresvet system, a ground-based laser complex specifically designed to blind the electro-optical sensors of surveillance satellites and shoot down tactical UAVs.49 While lasers are susceptible to atmospheric attenuation and thermal blooming, they remain a highly lethal, low-cost-per-shot countermeasure against unshielded drones.50
High-Power Microwaves (HPM)
While lasers must track and dwell on a single target to destroy it, HPM systems emit a wide cone of electromagnetic energy designed to instantaneously disrupt or permanently destroy the unshielded microelectronics within a drone.6 HPM is widely considered the ultimate counter-swarm weapon, as a single pulse can simultaneously disable dozens of drones flying in tight formation without requiring precise individual tracking.51
Chinese defense contractors are aggressively advancing HPM technology for deployable use. Systems such as NORINCO’s Hurricane-3000 are designed to create localized zones of electromagnetic denial, providing close-in protection against multi-axis swarm attacks.52 Because HPM systems induce catastrophic voltage spikes in flight controllers and navigation modules, they bypass the aerodynamic and kinetic evasive maneuvers that adversary drones might employ to dodge traditional interceptors.
Implications for U.S. Drone Design
The proliferation of adversary DEWs necessitates a complete reevaluation of U.S. drone design and employment doctrine. The smaller, attritable drones currently planned for mass deployment typically lack the size, weight, and power (SWaP) capacity to carry adequate defenses against directed energy. Installing thermal shielding, reflective coatings, or Bragg mirrors to mitigate laser damage significantly increases the weight and manufacturing complexity of the drone.49 Similarly, hardening internal electronics with Faraday cages to survive HPM attacks drives up the cost per unit, eroding the core advantage of attritable mass.53
If the DoD fixates solely on producing millions of unprotected, unshielded drones, it risks fielding a massive force that can be efficiently neutralized by a handful of strategically placed adversary directed-energy batteries. The systemic requirement is therefore to develop swarming tactics that incorporate deception, mass dispersal, and active countermeasures—such as integrating sacrificial decoy drones or deploying laser-jamming payload modules within the swarm to confuse enemy DEW tracking systems before the drones enter lethal range.49
6. Systemic Vulnerabilities in U.S. Drone Operations
A persistent vulnerability in U.S. defense planning is the cultural tendency to fixate on the end-product—the drone platform itself—while neglecting the vast, complex systemic architecture required to sustain it in a high-intensity conflict. The United States has a history of optimizing acquisition for exquisite, highly survivable systems, a model that breaks down entirely when confronted with the necessity of fielding thousands of expendable drones.54 An effective uncrewed capability is not merely an airframe; it is an integrated ecosystem comprising raw material supply chains, spectrum management protocols, maintenance logistics, and decentralized data infrastructure.
The Material Supply Chain Chokepoint
The DoD’s ambition to field tens of thousands of attritable autonomous systems is severely constrained by an industrial base that is fragmented, expensive, and deeply entangled with adversary-controlled supply chains.54 The true vulnerability of the U.S. drone program is found not in software algorithms, but in the domains of metallurgy and chemistry.
The “drone supply chain war” revolves around access to specialized composites, alloys, and semiconductors necessary for mass production. Nearly every modern drone relies on carbon fiber reinforced polymers for the airframe, lithium-ion cells for high-density power storage, and neodymium-iron-boron magnets to convert electrical current into torque for propulsion motors.56 China maintains a near-monopoly on the processing and refinement of these critical materials. Currently, China processes roughly two-thirds of the world’s lithium, over 70 percent of graphite anode material, and approximately 90 percent of global sintered-magnet output.56 Furthermore, the advanced sensors and AI-processing edge computers required for autonomous flight depend on specialty semiconductors, such as gallium-nitride (GaN) power amplifiers and infrared detectors, whose production is bottlenecked in a limited number of facilities.56
If the DoD treats drones as true consumables—expecting high attrition rates and demanding rapid replenishment—a single export restriction from Beijing on rare-earth magnets or graphite could paralyze U.S. production lines within weeks.56 True organizational agility requires upstream strategic stockpiling of raw materials, rather than just finished weapons. To secure production, the DoD must rapidly establish redundant, allied-shored refining and manufacturing capacities (e.g., through coproduction with partners in Australia, Japan, and Canada) to ensure the industrial base remains operational during a prolonged conflict.56
Spectrum Management and Command Link Logistics
Operating a handful of surveillance drones in uncontested airspace via satellite links is a relatively simple communications task. Operating swarms of thousands of collaborative, autonomous drones in a dense, highly contested electromagnetic environment represents a monumental systemic hurdle.47
Drones require spectrum to communicate with operators, share targeting data among the swarm, and relay high-resolution intelligence. In a peer conflict, the electromagnetic spectrum will be severely degraded by adversary jamming, and any active RF emission from a U.S. drone or ground control station will serve as a highly visible beacon for adversary anti-radiation missiles and counter-battery artillery fire.5 The traditional model of relying on continuous reach-back to central command posts via persistent data links is a fatal vulnerability.
The systemic requirement is the development of dynamic spectrum management and decentralized data architectures. Drones must be capable of processing intelligence at the tactical edge, sharing only minimal, highly compressed burst transmissions via localized, low-probability-of-intercept mesh networks.4 The U.S. military must shift its operational philosophy from ensuring perfect, continuous connectivity to ensuring that systems can execute complex commander’s intents autonomously when communications are completely severed.58
Maintenance, Logistics, and Attritable Fleet Management
The deployment of massive drone fleets introduces entirely new logistical burdens that tactical units are currently unequipped to handle. While attritable drones are intended to be low-cost and expendable, they still require significant support infrastructure, including secure storage, transportation, high-capacity battery charging stations, firmware update terminals, and pre-flight diagnostic tools.60
The failure rate of commercial-grade and attritable UAS is significantly higher than that of crewed aircraft, requiring a continuous pipeline of spare parts—propellers, motors, optical modules, and communication relays.62 U.S. tactical units currently lack the specialized training and equipment necessary to manage the lifecycle of hundreds of autonomous systems in austere, forward-deployed environments.64
Building organizational agility requires completely redesigning sustainment. The DoD must mandate Modular Open Systems Architectures (MOSA) across all drone procurement. Open architectures ensure that components are plug-and-play across different drone variants, allowing soldiers to cannibalize damaged systems to repair others without requiring proprietary contractor support or waiting for highly specific replacement parts to travel across vulnerable trans-oceanic supply lines.3
7. Building Organizational Agility and Decision Dominance
To successfully employ drone technology long-term and survive in a rapidly adapting threat landscape, the DoD must fundamentally restructure how it designs, procures, and updates uncrewed systems. The objective is not merely to construct a more technologically advanced drone, but to build an organizational machine capable of learning, iterating, and evolving faster than the adversary.2 This requires a paradigm shift across acquisition, tactical fabrication, and artificial intelligence integration.
Rethinking Acquisition: From Platforms to Capabilities as a Service
The traditional acquisition models, such as JCIDS, mandate years of requirements generation, testing, and evaluation, ultimately resulting in highly integrated, proprietary platforms that are exceedingly difficult to upgrade once fielded.13 By the time a rigid platform navigates the bureaucratic pipeline and reaches the warfighter, the adversary has already witnessed its prototypes, mapped its signatures, and deployed targeted countermeasures.14
To outpace this cycle, DoD leadership must transition toward a model of purchasing “Capabilities as a Service” and utilizing rapid, iterative pilot programs.8 Rather than locking the military into a decade-long contract for a specific airframe, the DoD should procure modular systems governed by open digital architectures. This software-defined approach allows the military to continuously swap out payloads, radios, and optical sensors from various commercial vendors as the threat environment changes, breaking vendor lock and accelerating deployment.3
The U.S. Navy’s Task Force 59 provides a successful blueprint for this necessary agility. By integrating commercial uncrewed surface vessels with artificial intelligence and mesh networks, and utilizing a workforce comprising reservists and tech industry experts, Task Force 59 demonstrated the ability to rapidly iterate capabilities directly in the operational environment of the Middle East, bypassing traditional bureaucratic chokepoints and fielding viable systems in months rather than years.66
Fostering Innovation and Fabrication at the Tactical Edge
The most critical adaptations in drone warfare do not originate in pristine defense laboratories; they are born in trenches and forward operating bases out of operational necessity. Ukrainian forces achieve rapid adaptation precisely because the end-users (the soldiers) are directly integrated with the engineers modifying the software and hardware.8 When a new Russian EW frequency is encountered, Ukrainian teams write software patches, 3D-print modified antenna housings, and deploy the updated drone the following day.8
The DoD must build an infrastructure that supports this bottom-up innovation, applying the principles of the lean startup model directly to tactical units.8 Soldiers must be granted the authority, budget, and tools to modify systems in the field without awaiting top-down approval. Initiatives such as “Fabrication at the Tactical Edge” (FATE)—which involves equipping forward units with ruggedized 3D printers, software coding terminals, and modular COTS components—allow operators to invent, manufacture, and test physical drone modifications and payload adaptations within hours of encountering a new enemy countermeasure.69
Furthermore, leadership must cultivate a culture that tolerates acceptable failure at the tactical level. Innovation requires iteration. If a squad attempts a new drone modification and it fails, the organization must rapidly capture that telemetry data, share it across the network, and facilitate a second attempt, rather than subjecting the failure to punitive bureaucratic reviews that stifle future experimentation.2
Implementing Agentic AI for Decision Dominance
As the volume of drones on the battlefield scales into the thousands, human operators will be fundamentally incapable of processing the sheer influx of sensor data, threat warnings, and EW anomalies. Managing this complexity requires a transition from basic automation to “Agentic AI” to achieve true decision dominance.9
Unlike traditional AI—which functions primarily as an analytical tool, a predictive model, or a generative summarizer—Agentic AI acts as an autonomous, goal-oriented entity embedded within the command-and-control workflow.9 In a drone swarm context, Agentic AI does not simply alert a human commander that the swarm is being jammed. Instead, it actively senses the EW interference, reasons through alternative navigation options, dynamically re-routes the unaffected drones to form a new mesh network, assigns specific drones to act as sacrificial decoys, and generates an optimized course of action for the commander to approve—all in milliseconds.9
To realize this, the DoD must invest heavily in the software infrastructure required to host Agentic AI at the edge. The true competitive advantage in uncrewed warfare lies in the sophisticated algorithms that govern collaborative swarm behavior, automated target recognition, and dynamic spectrum evasion, rather than the aerodynamic efficiency or kinetic payload of the drone hardware itself.9
8. Strategic Recommendations for DoD Leadership
The Department of Defense is entering an era of precise mass, where low-cost, highly intelligent systems will increasingly dominate the multidomain battlespace.2 To ensure long-term viability, maintain operational overmatch, and survive against the rapid adaptation of peer adversaries, DoD leadership must operationalize the following strategic imperatives:
| Strategic Imperative | Operational Execution | Intended Outcome |
| Institutionalize ‘Adaptation in Contact’ | Shift programmatic metrics from “compliance with initial requirements” to “speed of iteration.” Establish digital pipelines to push software updates and EW evasion protocols directly to the tactical edge in hours. | Replaces static vulnerability with dynamic resilience, forcing adversaries into a continuous, reactive posture.1 |
| Decouple the Sub-Tier Supply Chain | Build allied-shored refining capacity for critical drone components (NdFeB magnets, GaN chips). Shift strategic stockpiles from finished munitions to raw material inputs. | Secures the “factory floor” during prolonged conflicts, mitigating the impact of adversary export restrictions.56 |
| Prioritize Directed Energy and Cognitive EW | Accelerate fielding of High-Power Microwave (HPM) and High-Energy Laser (HEL) systems. Mandate AI-driven, frequency-hopping radios for all future UAS procurements. | Inverts the unsustainable cost-exchange ratio of defending against drone swarms and ensures navigation in GPS-denied environments.38 |
| Mandate Modular Open Systems Architectures (MOSA) | Require open software/hardware architectures for all uncrewed systems to prevent proprietary vendor lock and enable rapid field cannibalization/repair. | Allows the rapid integration of commercial upgrades and alternate payloads when existing systems are compromised.3 |
| Elevate Data Integrity and Counter-Exploitation | Incorporate self-wiping firmware protocols, hardware tamper-resistance, and rigorous adversarial AI training to defend against data poisoning and rapid reverse engineering. | Slows the adversary’s technical exploitation pipeline and maintains the integrity of U.S. targeting algorithms.35 |
The nation that first masters the systemic integration of uncrewed systems—securing the underlying supply chain, fielding deeply integrated non-kinetic defenses, and weaponizing the learning cycle to adapt faster than the enemy—will dictate the terms of future military competition.1 Drones are not the terminal end-state of military innovation; they are the catalyst for an entirely new organizational paradigm of warfare. The DoD must look beyond the platform to build an agile, software-defined, and deeply resilient defense enterprise.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Sources Used
- The Quick and the Dead: How Adaptation in Contact Drives Military Advantage, accessed April 24, 2026, https://www.hudson.org/defense-strategy/quick-dead-how-adaptation-contact-drives-military-advantage-bryan-clark-dan-patt-ian-crone
- The requirement that a force must adapt while it is in combat is built into the inherent nature of war. – SCSP, accessed April 24, 2026, https://www.scsp.ai/wp-content/uploads/2025/11/Adaptation_War_SCSP.pdf
- The Drone War’s Real Problem Isn’t Technology — It’s Speed, accessed April 24, 2026, https://www.thecipherbrief.com/drone-wars
- How are Drones Changing Modern Warfare? | Australian Army Research Centre (AARC), accessed April 24, 2026, https://researchcentre.army.gov.au/library/land-power-forum/how-are-drones-changing-modern-warfare
- PRC Concepts for UAV Swarms in Future Warfare | CNA.org., accessed April 24, 2026, https://www.cna.org/reports/2025/07/PRC-Concepts-for-UAV-Swarms-in-Future-Warfare.pdf
- Counter-UAS Mission Seen as Killer App for Directed Energy – National Defense Magazine, accessed April 24, 2026, https://www.nationaldefensemagazine.org/articles/2026/1/20/counterdrone-mission-seen-as-killer-app-for-directed-energy
- Fact Sheet: DoD Strategy for Countering Unmanned Systems – Department of War, accessed April 24, 2026, https://media.defense.gov/2024/Dec/05/2003599149/-1/-1/0/FACT-SHEET-STRATEGY-FOR-COUNTERING-UNMANNED-SYSTEMS.PDF
- Want Drone Dominance? Let the Squad Fail – Modern War Institute -, accessed April 24, 2026, https://mwi.westpoint.edu/want-drone-dominance-let-the-squad-fail/
- Decision Dominance in the Age of Agentic AI – Small Wars Journal, accessed April 24, 2026, https://smallwarsjournal.com/2025/10/03/agentic-ai-decision-dominance/
- Electronic Warfare vs. Directed Energy: Which C-UAS Approach Wins the Scaling War?, accessed April 24, 2026, https://www.dronesense.ai/electronic-warfare-vs-directed-energy-which-c-uas-approach-wins-the-scaling-war-2/
- How Russia’s Electronic Warfare Blinded Ukrainian Drones — and How Ukraine Fought Back | Military Machine, accessed April 24, 2026, https://militarymachine.com/russia-electronic-warfare-ukraine-drones
- Drone Warfare in Ukraine: From Myths to Operational Reality – Part 1, accessed April 24, 2026, https://researchcentre.army.gov.au/library/land-power-forum/drone-warfare-ukraine-myths-operational-reality-part-1
- Why the Army Needs Units Driving Drone Development and How to Do It, accessed April 24, 2026, https://www.armyupress.army.mil/journals/military-review/online-exclusive/2025-ole/drone-development/
- Achieving Adaptable Scale: Fielding Military Capabilities as a Service | Hudson Institute, accessed April 24, 2026, https://www.hudson.org/events/achieving-adaptable-scale-fielding-military-capabilities-service
- Adversary Entente Task Force Update, July 9, 2025 | ISW, accessed April 24, 2026, https://understandingwar.org/research/adversary-entente/adversary-entente-task-force-update-july-9-2025/
- Russian Drone Innovations are Likely Achieving Effects of Battlefield Air Interdiction in Ukraine – Institute for the Study of War, accessed April 24, 2026, https://understandingwar.org/research/russia-ukraine/russian-drone-innovations-are-likely-achieving-effects-of-battlefield-air-interdiction-in-ukraine/
- Collaboration for a Price: Russian Military-Technical Cooperation with China, Iran, and North Korea – CSIS, accessed April 24, 2026, https://www.csis.org/analysis/collaboration-price-russian-military-technical-cooperation-china-iran-and-north-korea
- Countering Iran’s UAS swarms ‘requires compressing the kill chain’ – RUSI, accessed April 24, 2026, https://www.rusi.org/news-and-comment/in-the-news/countering-irans-uas-swarms-requires-compressing-kill-chain
- What Are Iranian Shahed Drones Capable of? From Ukraine to Dubai and US Bases in the Gulf – UNITED24 Media, accessed April 24, 2026, https://united24media.com/war-in-ukraine/what-are-iranian-shahed-drones-capable-of-from-ukraine-to-dubai-and-us-bases-in-the-gulf-16497
- The new economics of warfare – European Policy Centre (EPC), accessed April 24, 2026, https://www.epc.eu/publication/the-new-economics-of-warfare/
- Monthly Drone Report – March 2026 – SOF News, accessed April 24, 2026, https://sof.news/drones/march-2026/
- Iran–U.S. RQ-170 incident – Wikipedia, accessed April 24, 2026, https://en.wikipedia.org/wiki/Iran%E2%80%93U.S._RQ-170_incident
- Iran claims it decoded all data from captured CIA drone – The Times of Israel, accessed April 24, 2026, https://www.timesofisrael.com/iran-claims-it-decoded-all-data-from-captured-cia-drone/
- Captured US Stealth Drone, Reversed-Engineered By Iran, Could Help Russia In Gaining Air Superiority Over Ukraine – EurAsian Times, accessed April 24, 2026, https://www.eurasiantimes.com/us-stealth-drone-reversed-engineered-by-iran-to-help/
- Iran gives Russia copy of US ScanEagle drone as proof of mass production – The Guardian, accessed April 24, 2026, https://www.theguardian.com/world/2013/oct/21/iran-russia-us-scaneagle-spy-drone-production-capture
- China Takes Control of Indian In-Service Drone: A Wake-Up Call for Indigenous Development – AlphaDefense.in, accessed April 24, 2026, https://alphadefense.in/index.php/2025/03/25/china-control-indian-drone-security-flaw/
- The PLA’s Unmanned Aerial Systems – Air University, accessed April 24, 2026, https://www.airuniversity.af.edu/Portals/10/CASI/documents/Research/PLAAF/2018-08-29%20PLAs_Unmanned_Aerial_Systems.pdf
- China’s Military Unmanned Aerial Vehicle Industry, accessed April 24, 2026, https://www.uscc.gov/sites/default/files/Research/China’s%20Military%20UAV%20Industry_14%20June%202013.pdf
- Russia’s Iranian-Made UAVs: A Technical Profile | Royal United Services Institute – RUSI, accessed April 24, 2026, https://www.rusi.org/explore-our-research/publications/commentary/russias-iranian-made-uavs-technical-profile
- A U.S. Spy Drone Reverse-Engineered By Both Russia & China: The Untold Story Of Lockheed Martin’s D-21 – EurAsian Times, accessed April 24, 2026, https://www.eurasiantimes.com/u-s-spy-drone-reverse-engineered-by-both-russia-china-the-untold-story-of-lockheed-martins-3-d-21/
- Uncovering an Adversary UAS Unit and Shadow Pipeline – DroneSec, accessed April 24, 2026, https://dronesec.com/resources/7643d3e0-3358-11f1-ad69-c3
- How the U.S. Army ‘Replicates’ Enemy Drones to Destroy Them – The National Interest, accessed April 24, 2026, https://nationalinterest.org/blog/buzz/how-us-army-replicates-enemy-drones-destroy-them-79601
- Security analysis of drones systems: Attacks, limitations, and recommendations – PMC – NIH, accessed April 24, 2026, https://pmc.ncbi.nlm.nih.gov/articles/PMC7206421/
- UAV Exploitation: A New Domain for Cyber Power | CCDCOE, accessed April 24, 2026, https://ccdcoe.org/uploads/2018/10/Art-14-Assessing-the-Impact-of-Aviation-Security-on-Cyber-Power.pdf
- Cyber threat in drone systems: bridging real-time security, legal admissibility, and digital forensic solution readiness – Frontiers, accessed April 24, 2026, https://www.frontiersin.org/journals/communications-and-networks/articles/10.3389/frcmn.2025.1661928/full
- A Comprehensive Approach to Countering Unmanned Aircraft Systems – Joint Air Power Competence Centre, accessed April 24, 2026, https://www.japcc.org/wp-content/uploads/A-Comprehensive-Approach-to-Countering-Unmanned-Aircraft-Systems.pdf
- The Vulnerability Management Race Is Over. It’s Time to Focus on Exposure., accessed April 24, 2026, https://securityboulevard.com/2026/04/the-vulnerability-management-race-is-over-its-time-to-focus-on-exposure/
- GOVERNMENT PERSPECTIVE: Directed Energy in Air Base Defense Can Save the Arsenal, accessed April 24, 2026, https://www.nationaldefensemagazine.org/articles/2025/8/11/government-perspective-directed-energy-in-air-base-defense-can-save-the-arsenal
- Electronic warfare – Wikipedia, accessed April 24, 2026, https://en.wikipedia.org/wiki/Electronic_warfare
- Visions for the next 40 years of U.S. Department of Defense Directed Energy technologies – Air Force Research Laboratory, accessed April 24, 2026, https://www.afrl.af.mil/Portals/90/Documents/RD/Directed_Energy_Futures_2060_Final29June21_with_clearance_number.pdf
- Lessons from the War in Ukraine for Space: Challenges and Opportunities for Future Conflicts – RAND, accessed April 24, 2026, https://www.rand.org/content/dam/rand/pubs/research_reports/RRA2900/RRA2950-1/RAND_RRA2950-1.pdf
- Drone Swarm Navigation in GNSS-Challenged and Cluttered Environments – Medium, accessed April 24, 2026, https://medium.com/@gwrx2005/drone-swarm-navigation-in-gnss-challenged-and-cluttered-environments-d50388bc31b3
- COUNTERING THE SWARM – Amazon S3, accessed April 24, 2026, https://s3.us-east-1.amazonaws.com/files.cnas.org/documents/Report_CUAS_Defense_Sep-2025_final.pdf
- Electronic Warfare: Mastering the Invisible Battlefield | by S-Ag3 – Medium, accessed April 24, 2026, https://medium.com/@ingartsq2/electronic-warfare-mastering-the-invisible-battlefield-191b0b92d3ef
- Russian Force Generation & Technological Adaptations Update, October 9, 2025, accessed April 24, 2026, https://understandingwar.org/research/russia-ukraine/russian-force-generation-technological-adaptations-update-october-9-2025/
- Exploiting Offensive Use of Small Unmanned Aerial Systems (sUAS): Learning from Our Adversaries > Air University (AU) > Wild Blue Yonder, accessed April 24, 2026, https://www.airuniversity.af.edu/Wild-Blue-Yonder/Articles/Article-Display/Article/3836715/exploiting-offensive-use-of-small-unmanned-aerial-systems-suas-learning-from-ou/
- UAV swarm algorithm boosts spectrum resilience in contested airspace – SpaceWar.com, accessed April 24, 2026, https://www.spacewar.com/reports/UAV_swarm_algorithm_boosts_spectrum_resilience_in_contested_airspace_999.html
- Directed Energy Weapons Market Report, Industry and Market Size & Revenue, Share, Forecast 2024–2030, accessed April 24, 2026, https://www.strategicmarketresearch.com/market-report/directed-energy-weapons-market
- Counter Directed Energy Weapons and the Defense of Naval Unmanned Aerial Vehicles, accessed April 24, 2026, https://nps.edu/documents/10180/142489929/JDE_7-2_Johnson.pdf
- War at the speed of light: the emerging role of directed-energy weapons | The Strategist, accessed April 24, 2026, https://www.aspistrategist.org.au/war-at-the-speed-of-light-the-emerging-role-of-directed-energy-weapons/
- Countering the Swarm – CNAS, accessed April 24, 2026, https://www.cnas.org/publications/reports/countering-the-swarm
- China Pushes Forward with UAV and Counter-UAV Technology – Datenna, accessed April 24, 2026, https://www.datenna.com/resources/china-pushes-forward-with-uav-and-counter-uav-technology/
- Ghosts of the Road: What the Failed War on IEDs Means for Drones, accessed April 24, 2026, https://warontherocks.com/ghosts-of-the-road-what-the-failed-war-on-ieds-means-for-drones/
- The Drone Gap: Why the U.S. Industrial Base Continues to Fall …, accessed April 24, 2026, https://www.icitech.org/post/the-drone-gap-why-the-u-s-industrial-base-continues-to-fall-behind-in-a-world-at-war-by-drone
- Swarms over the Strait – CNAS, accessed April 24, 2026, https://www.cnas.org/publications/reports/swarms-over-the-strait
- The Drone Supply Chain War: Identifying the Chokepoints to Making …, accessed April 24, 2026, https://www.csis.org/analysis/drone-supply-chain-war-identifying-chokepoints-making-drone
- Spectrum Contested Environments – Marine Corps Association, accessed April 24, 2026, https://www.mca-marines.org/gazette/spectrum-contested-environments/
- How Communications Technology Enables DoW’s Drone Scaling – Elsight, accessed April 24, 2026, https://www.elsight.com/blog/how-communications-technology-enables-dows-drone-scaling/
- AGILE COMBAT EMPLOYMENT – USAF, accessed April 24, 2026, https://www.af.mil/Portals/1/documents/Force%20Management/AFDN_1-21_ACE.pdf
- Operating Low-Cost, Reusable Unmanned Aerial Vehicles in Contested Environments – RAND, accessed April 24, 2026, https://www.rand.org/content/dam/rand/pubs/research_reports/RR4400/RR4407/RAND_RR4407.pdf
- Why is Maintenance Important for Large Drone Fleets’ Management? | AirHub, accessed April 24, 2026, https://www.airhub.app/resources/news/large-drone-fleets-maintenance
- (PDF) Maintenance of a drone fleet – ResearchGate, accessed April 24, 2026, https://www.researchgate.net/publication/329690289_Maintenance_of_a_drone_fleet
- Maintenance of a Drone Fleet – BQR, accessed April 24, 2026, https://www.bqr.com/post/maintenance-of-a-drone-fleet
- Small Uncrewed Aircraft Systems in Divisional Brigades: Requirements and Findings – RAND, accessed April 24, 2026, https://www.rand.org/content/dam/rand/pubs/research_reports/RRA2600/RRA2642-1/RAND_RRA2642-1.pdf
- KSE_Institute_Report_Harnessin, accessed April 24, 2026, https://kse.ua/wp-content/uploads/2025/11/KSE_Institute_Report_Harnessing_Ukraines_Drone_Innovations_to_Advance.pdf
- Integrating USVs & AI into an Operational Maritime Environment – Saildrone, accessed April 24, 2026, https://www.saildrone.com/missions/task-force-59-unmanned-integration
- Task Force 59: The future of the Navy’s unmanned systems or a one-off win?, accessed April 24, 2026, https://defensescoop.com/2022/02/08/task-force-59-the-future-of-the-navys-unmanned-systems-or-a-one-off-win/
- How are Drones Changing War? The Future of the Battlefield – CEPA, accessed April 24, 2026, https://cepa.org/article/how-are-drones-changing-war-the-future-of-the-battlefield/
- Fabrication at the Tactical Edge – National Defense University, accessed April 24, 2026, https://www.ndu.edu/News/Article-View/Article/4445402/fabrication-at-the-tactical-edge/
- Beyond Linear Planning – Marine Corps University, accessed April 24, 2026, https://www.usmcu.edu/Outreach/Marine-Corps-University-Press/MCU-Journal/JAMS-vol-16-no-2/Beyond-Linear-Planning/
- Air Force Future Operating Concept, accessed April 24, 2026, https://www.af.mil/Portals/1/images/airpower/AFFOC.pdf
- Adapting to Win | Hudson Institute, accessed April 24, 2026, https://www.hudson.org/defense-strategy/adapting-win-us-navy-rapid-capabilities-office-nrco-new-approach-military-acquisition-bryan-clark-dan-patt
- Data Poisoning as a Covert Weapon: Securing U.S. Military Superiority in AI-Driven Warfare, accessed April 24, 2026, https://lieber.westpoint.edu/data-poisoning-covert-weapon-securing-us-military-superiority-ai-driven-warfare/
