1. Executive Summary
The United States Department of Defense (DoD) is entering a transformative era of warfare characterized by the rapid deployment of uncrewed, autonomous, and attritable mass. As the DoD executes massive investments in drone technology—exemplified by high-profile efforts such as the Replicator initiative and the Army’s Project SkyFoundry—there is a critical need to evaluate the systemic and architectural requirements necessary to design, build, operate, sustain, and evolve these platforms.1 While technological capabilities such as artificial intelligence (AI) targeting, swarm logic, and advanced sensor payloads dominate public and institutional discourse, the underlying acquisition frameworks governing intellectual property (IP), technical data rights, and system architectures frequently dictate the operational success or failure of these platforms.3
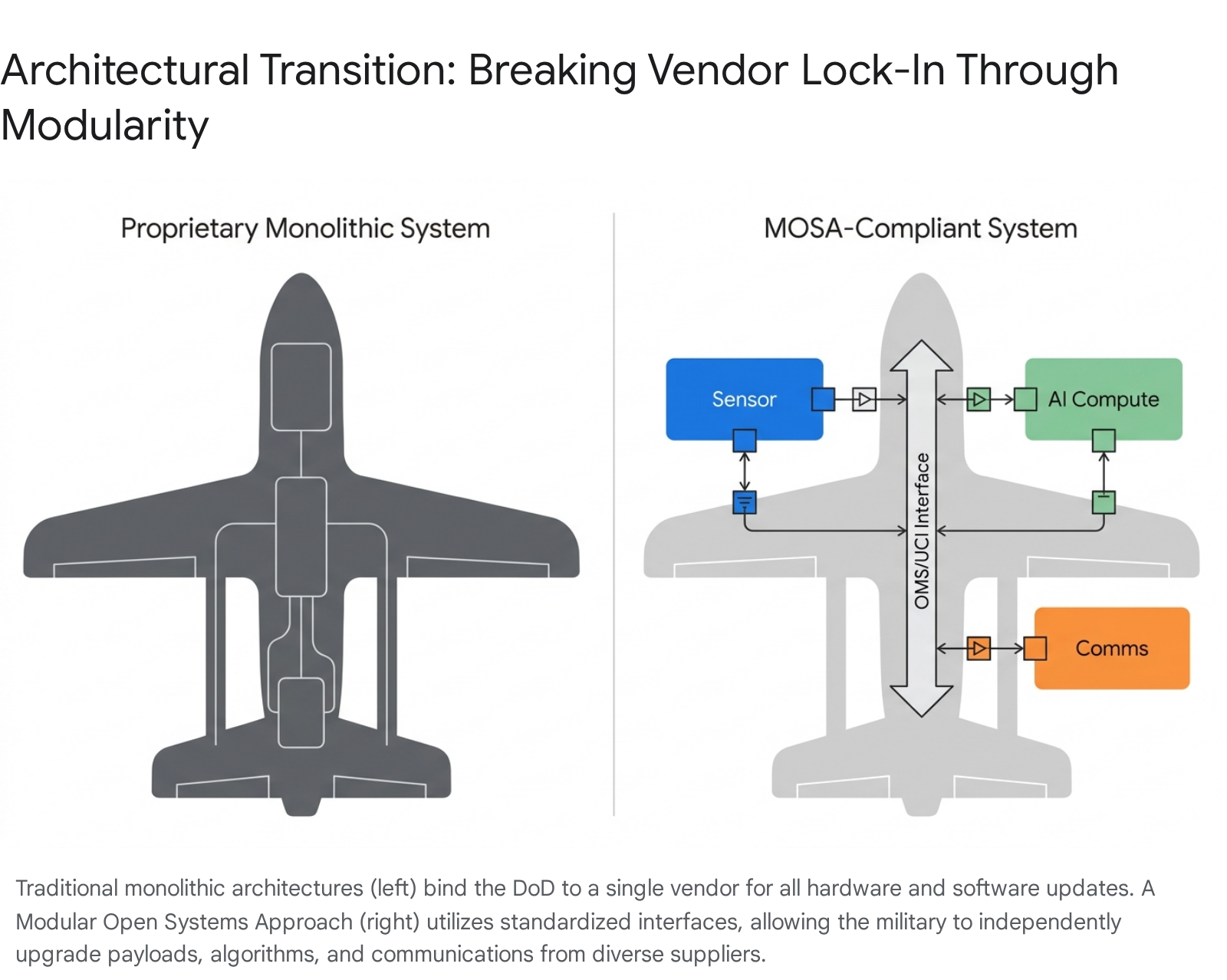
This report provides DoD leadership with a strategic analysis of vendor lock-in, proprietary data rights, closed-source software, and black-box hardware in the specific context of military drone acquisitions. The analysis indicates that without a strictly enforced Modular Open Systems Approach (MOSA), the military risks severe operational, tactical, and fiscal constraints.4 Proprietary hardware and closed software ecosystems prevent military personnel from organically repairing platforms at the forward edge, seamlessly integrating third-party payloads, or rapidly updating AI algorithms in response to emerging electronic warfare threats.6
The findings suggest that the traditional hardware-centric procurement models of the 20th century are fundamentally misaligned with the requirements of software-defined warfare.9 When vendors retain restrictive technical data rights—often leveraging the “segregability doctrine” to protect privately funded components—the DoD can become trapped in a state of vendor lock-in.10 This dynamic drives up long-term sustainment costs, extends repair timelines beyond tactical utility, and stifles the continuous innovation required to pace near-peer adversaries.12
To successfully enable warfighters and maintain operational flexibility, leadership must navigate the complex intersection of(https://www.esd.whs.mil/Portals/54/Documents/DD/issuances/dodi/501044p.pdf) (Intellectual Property Acquisition and Licensing), statutory mandates for MOSA, and the practical realities of frontline combat.11 This report outlines the current IP landscape, analyzes the operational impact of closed systems, extracts actionable lessons from contemporary high-intensity conflicts, and provides recommendations for reforming unmanned aerial systems (UAS) acquisition strategies.
2. The Operational Imperative for Systemic Reform
The transition from exquisite, low-density, human-piloted aviation assets to distributed, high-density uncrewed systems requires a fundamental shift in how the DoD conceptualizes and architectures its platforms. Drones can no longer be procured as static, monolithic end-items; they must be treated as dynamic, evolving nodes within a broader software-defined network.
2.1 The Shift to Software-Defined, Attritable Mass
The character of modern conflict is increasingly defined by the ability to generate, lose, and regenerate combat power at an industrial scale.14 This requires a departure from systems that prioritize absolute survivability at immense cost, toward “attritable” platforms—systems designed to be affordable enough to be lost in combat and rapidly replaced.14 However, producing physical airframes at scale is only the first step. The true capability of these systems resides in their software, payloads, and communication links.16
Advanced military drones rely on complex algorithms for autonomous navigation, target recognition, and electronic warfare (EW) resilience.16 In an environment where adversaries rapidly adapt their tactics, algorithmic stagnation equates to platform obsolescence. If a drone cannot be updated rapidly to counter a new GPS spoofing technique or radar frequency, its physical availability is rendered tactically irrelevant.17 Therefore, the architecture of the drone must allow for continuous, seamless capability injection.
2.2 Evaluating Supply Chain and Raw Material Dependencies
The push for domestic drone dominance is occurring against a backdrop of severe supply chain vulnerabilities. The ability to sustain mass production of drones requires access to specialized composites, alloys, and semiconductors.18 Currently, the defense industrial base is deeply entangled with adversary-controlled supply chains. Critical nodes—including carbon fiber, rare-earth magnets, lithium-ion cells, and gallium-nitride chips—often originate in Chinese factories and refineries.18
China’s increased imposition of global export controls on defense-related minerals underscores how easily these dependencies can be weaponized.18 Unless the United States adapts quickly by securing domestic sources and standardizing components across platforms, warfighting capacity could be hamstrung by a shortage of the specialized materials needed to build affordable mass.18
Recent federal policy reflects an urgent recognition of this threat. The(https://www.hklaw.com/en/insights/publications/2025/12/drones-and-the-federal-government-what-contractors-need-to-know) and subsequent Office of Management and Budget (OMB) memorandums have established comprehensive requirements to counteract the effects of purchasing foreign-made drones and to reinforce the integrity and security of federal operations.19 However, enforcing these supply chain security measures is exceedingly difficult when procuring proprietary “black-box” systems, as the government cannot easily audit or verify the origins of internalized components.20 An open architecture, conversely, provides transparency into the supply chain down to the sub-component level.
3. Modular Open Systems Approach (MOSA) Mandates and Mechanics
The Modular Open Systems Approach (MOSA) is the principal mechanism through which the DoD seeks to avoid the pitfalls of proprietary, monolithic system design.5 It is a strategy designed to decouple the lifecycle of a drone’s airframe from the lifecycle of its rapidly evolving digital and sensor payloads.
3.1 Statutory Foundations and Department Directives
MOSA is not merely an acquisition best practice or a theoretical engineering preference; it is a strict statutory requirement. Under Title 10 U.S.C. 4401 (formerly 10 U.S.C. 2446a), all major defense acquisition programs (MDAPs) are mandated to be designed and developed using a MOSA.13 Furthermore, Section 804 of the National Defense Authorization Act (NDAA) for Fiscal Year 2021 expanded this requirement, directing its application to the maximum extent practicable across programs beyond just MDAPs.4
Under these statutes, programs must employ a modular design utilizing modular system interfaces between major systems and components.13 These interfaces must be subjected to verification to ensure they comply with widely supported, consensus-based standards.13 Crucially, the legislation integrates technical requirements directly with legal contracting mechanisms, specifically linking MOSA to the acquisition of technical data rights set forth in 10 U.S.C. 3771-3775.13 Contracts must now include requirements for the delivery of software-defined interface syntax and properties in machine-readable formats, ensuring that the government possesses the data necessary to integrate third-party solutions.13
3.2 The Five Core Pillars of Defense Modularity
The Office of the Under Secretary of Defense for Research and Engineering (OUSD(R&E)) has developed specific guidance to implement MOSA, structured around five foundational pillars 21:
- Establish an Enabling Environment: Program Managers (PMs) must establish supportive requirements, business practices, technology development strategies, and product support strategies that prioritize modularity from the earliest stages of the acquisition lifecycle.21
- Employ Modular Design: System architectures must separate major functions into severable components. These modules must be highly cohesive (delivering well-defined, singular functionality), encapsulated (hiding internal workings from the rest of the system), and self-contained.21
- Designate Key Interfaces: PMs must identify and define the critical boundaries between modules. A system is only as open as the interfaces that connect its parts.21
- Use Consensus-Based Open Standards: To the maximum extent possible, designated interfaces must utilize publicly available or non-proprietary standards rather than vendor-specific protocols.21
- Certify Conformance: Programs must implement rigorous testing and verification processes to ensure that delivered systems actually comply with the designated open standards, preventing vendors from introducing undocumented proprietary modifications.21
The DoD anticipates that adherence to these pillars will yield significant cost savings, enable technology refresh without platform redesign, and foster interoperability across joint domains.23
| Benefit Category | Impact of Proprietary Architecture | Impact of MOSA Implementation |
| Cost Management | Vendor monopolies dictate pricing for upgrades and sustainment. | Severable modules allow components to be openly competed among diverse suppliers. |
| Technology Refresh | Requires extensive, system-wide recertification and OEM involvement. | Targeted replacement of specific modules (e.g., upgrading an AI compute card) without altering the airframe. |
| Interoperability | Siloed platforms that cannot natively share data or coordinate effects. | System-of-systems integration enabling cross-platform swarm coordination. |
| Operational Flexibility | Fixed configurations tailored to specific environments. | Rapid reconfiguration of payloads to meet changing mission profiles at the tactical edge. |
3.3 Technical Standards Defining the Drone Ecosystem
A modular approach is ineffective if the modules speak different digital languages. To actualize MOSA, the DoD and industry consortia have developed a suite of consensus-based technical standards.
The Open Mission Systems (OMS) standard and the Universal Command and Control Interface (UCI) are critical components of this strategy for airborne systems.24 OMS establishes an industry consensus for a non-proprietary mission system architectural standard, focusing heavily on the software interfaces between services and hardware subsystems.25 It is a government-owned architecture specification designed to enable logical “Plug and Talk” functionality, allowing different sensors and algorithms to exchange data seamlessly.26 UCI complements OMS by establishing a set of XML-defined messages for machine-to-machine, mission-level command and control.25
Similarly, the Future Airborne Capability Environment (FACE) Technical Standard provides a foundation for modern, open software architectures.27 By moving away from monolithic systems toward reusable software components, FACE allows avionics software developed for one aircraft to be ported to another, provided both adhere to the standard.27 On the hardware side, the Sensor Open Systems Architecture (SOSA) Consortium develops standards and best practices for sensor system physical integration, ensuring that a radar or optical payload from one vendor can physically mount and connect to a platform built by another.28
Other critical standards include the C5ISR/EW Modular Open Suite of Standards (CMOSS) for command, control, communications, computers, cyber, intelligence, surveillance, and reconnaissance (C5ISR), and the Hardware Open Systems Technologies (HOST) framework.29
3.4 Overcoming Third-Party Payload Integration Hurdles
Unmanned aerial systems are fundamentally sensor and effector trucks; their operational value is derived entirely from the payloads they carry.30 As technology evolves, a drone airframe may remain structurally viable for a decade, but its optical sensors, electronic warfare packages, and communications relays may become technologically obsolete in months.31
Integrating a custom or third-party payload into a commercial or proprietary military drone is notoriously difficult. If a drone’s computational system is closed-source, the software Application Programming Interface (API) acts as an impenetrable black box.7 Manufacturers expose only limited functionality and documentation to the public, primarily because supporting third-party integration reduces their control over the platform’s ecosystem and is rarely profitable for the prime contractor.7
For researchers, warfighters, and non-traditional defense vendors, this creates a prohibitively high barrier to entry. To integrate a new LiDAR sensor or an automated precision-landing module, engineers are often forced to bypass the drone’s internal computational system entirely, strapping redundant power supplies and separate processors onto the exterior of the airframe.7 This drastically degrades the drone’s flight time, aerodynamics, and overall payload capacity.7
To resolve this, the DoD requires enforced, standardized hardware and software boundaries. Initiatives like the DoD’s Modular Payload Design Standard (Mod Payload), developed by the Johns Hopkins Applied Physics Laboratory, outline a uniform architecture for both payloads and host platforms.32 By defining specific physical connections, power draws, and radio frequency (RF) cabling standards, Mod Payload allows a single drone to rapidly swap between an EW jammer, a signals intelligence (SIGINT) collector, or a kinetic effector without requiring complex factory recertification.32
When hardware and software interfaces are fixed and clearly defined, the DoD can foster a “software-defined architecture” akin to a commercial app store.30 The prime contractor builds the airframe and flight controller, while a diverse ecosystem of specialized vendors competes to build the best AI algorithms and advanced sensors to plug into that airframe.35
4. The Intellectual Property Landscape and Vendor Lock-In
The acquisition of physical drone hardware represents only a fraction of total procurement complexity; the acquisition of the intellectual property (IP) and technical data rights required to operate, sustain, and upgrade that hardware is equally critical. For decades, the DoD’s approach to IP has oscillated unproductively between demanding total data rights—which stifles commercial participation—and accepting commercial terms that leave the government with insufficient access to maintain its own systems.11
4.1 The Role of the DoD IP Cadre and DoDI 5010.44
In an effort to unify and standardize IP acquisition, the DoD published(https://www.esd.whs.mil/Portals/54/Documents/DD/issuances/dodi/501044p.pdf), “Intellectual Property Acquisition and Licensing,” in October 2019.11 This instruction established the DoD IP Cadre, a cross-functional team of legal and technical experts designed to advise program managers on customizing IP strategies.36 The instruction emphasizes early lifecycle planning, competitive acquisition of technical data, and the use of specially negotiated license rights.11
DoDI 5010.44 mandates that every program develop an IP strategy that aligns with the system’s product support and modernization goals.38 The objective is to strike a delicate balance: the DoD must acquire enough technical data to enable organic sustainment and avoid vendor lock-in, while contractors must retain enough IP protection to incentivize private investment in defense technologies.11 A 2018 report by the Government-Industry Advisory Panel on Technical Data Rights (the “813 Panel”) highlighted that ambiguous contract terms and a government tendency to overreach for “general government purpose rights” regardless of actual need were primary drivers of industry reluctance to partner with the DoD.40
4.2 Evaluating Technical Data Rights: OMIT Versus DMPD
A central tension in drone acquisition revolves around the legal classification of technical data. Under standard Defense Federal Acquisition Regulation Supplement (DFARS) clauses, the government is statutorily entitled to unlimited rights for Operation, Maintenance, Installation, and Training (OMIT) data, regardless of whether the system was developed at private or government expense.10 OMIT data serves as the essential “user manual” required to keep the system functional in the field.12
However, statutory frameworks explicitly exclude Detailed Manufacturing or Process Data (DMPD) from this unlimited OMIT allowance.12 DMPD includes proprietary manufacturing techniques, source codes, material compositions, and the precise engineering tolerances that constitute a contractor’s core trade secrets.
This distinction creates significant friction during the sustainment phase of a drone’s lifecycle. A recent Government Accountability Office (GAO) report (GAO-25-107468) highlighted that government acquisition professionals and industry representatives frequently dispute what constitutes OMIT data versus DMPD.12 When a drone experiences a complex failure, military logisticians may claim the necessary repair schematics fall under OMIT, while the contractor asserts the data is proprietary DMPD. These interpretive disputes result in critical data gaps that prevent military maintainers from executing repairs, forcing the system back into the Original Equipment Manufacturer (OEM) repair pipeline.12
4.3 The Segregability Doctrine and the Black-Box Hardware Problem
The allocation of data rights in DoD contracts is traditionally tied to the source of funding used to develop the technology.42 If the government fully funds development, it typically receives Unlimited Rights. If the technology is developed exclusively at private expense, the government receives Limited Rights (for technical data) or Restricted Rights (for software).43 If funding is mixed, the government generally receives Government Purpose Rights, allowing it to use the IP for defense purposes and share it with third-party contractors for government work.42
This funding-based test is applied at the lowest practicable segregable level—a concept known as the “segregability doctrine”.10 In the context of a drone, the government might hold Unlimited Rights to the airframe (which it funded) but only Limited Rights to a privately funded electro-optical sensor or an AI targeting algorithm.10
While segregability protects commercial innovation, it is frequently manipulated to generate vendor lock-in. A vendor may self-fund a small but highly critical component—such as an encryption module or an algorithmic interface—and assert proprietary rights over it. If that component is structurally integrated into the broader platform without open interfaces, the vendor effectively locks the government into its proprietary ecosystem. This results in “Swiss cheese data rights,” where the government owns the majority of the system but lacks the specific data rights necessary to independently upgrade, integrate, or sustain the platform as a cohesive whole.42
To protect their “crown jewel” technologies, defense contractors and commercial tech startups frequently deliver hardware as proprietary “black boxes”—sealed systems where the internal mechanics, firmware, and processing architectures are legally and physically inaccessible to the end-user.8 Furthermore, under the Bayh-Dole Act, contractors are permitted to retain patent rights for inventions developed even with federal funding, provided they grant the government a non-exclusive license.39 While this encourages dual-use commercial technology development, it solidifies the contractor’s leverage over the specific application of that technology.39
4.4 Deferred Delivery Versus Deferred Ordering of Technical Data
To mitigate the risk of acquiring vast amounts of technical data prematurely, the DoD utilizes mechanisms like Deferred Delivery and Deferred Ordering.
Under Deferred Delivery (DFARS 227.7103-8 and 252.227-7026), the government identifies specific technical data during contract formation that it knows it will need, but defers the actual physical delivery until up to two years after the acceptance of all other items.44 This allows the contractor to finalize the data without delaying hardware delivery.
Deferred Ordering (DFARS 252.227-7027) provides a broader safety net, allowing the government to order any technical data or computer software that was generated in the performance of the contract at any time up to three years after the acceptance of all items.46 While these tools provide flexibility, the 813 Panel noted that the government’s deferred ordering imposes significant administrative burdens on industry, while the rigid time limits restrict the government’s ability to carry out long-term sustainment plans that extend decades beyond the three-year window.47
4.5 Software Rights, Closed-Source Architectures, and AI Model Retraining
The risks of vendor lock-in are magnified exponentially in software-defined systems. If a drone’s software architecture is closed-source, the DoD is entirely dependent on the prime contractor for software updates, cybersecurity patches, and algorithmic retraining.7
For example, if an AI computer vision model deployed on an autonomous drone begins experiencing “model drift” or encounters a novel adversary camouflage technique, the model must be retrained with new datasets.8 If the acquisition contract does not clearly delineate who has the right to retrain the model—the original developer, the DoD, or a third-party contractor—the military may be legally barred from updating the system.8 The AI developer may refuse to grant a license for retraining or charge a significant premium to do so, creating a project-impeding dispute.8
This scenario poses a severe operational risk. The definitional layer of warfare—the ontological programming that determines how a drone identifies a “threat” versus a “civilian,” or assesses “readiness”—is ceded to vendors as proprietary IP.3 Once a closed-source platform flags a threat based on its hidden algorithms, these categorizations influence command decisions, effectively turning commercial vendor choices into de facto military doctrine.3 Even if a platform is fully MOSA compliant at the hardware and API boundary, running vendor-proprietary, black-box ontologies that no program office owns remains a significant liability.3
5. Analyzing the True Costs of Proprietary Sustainment
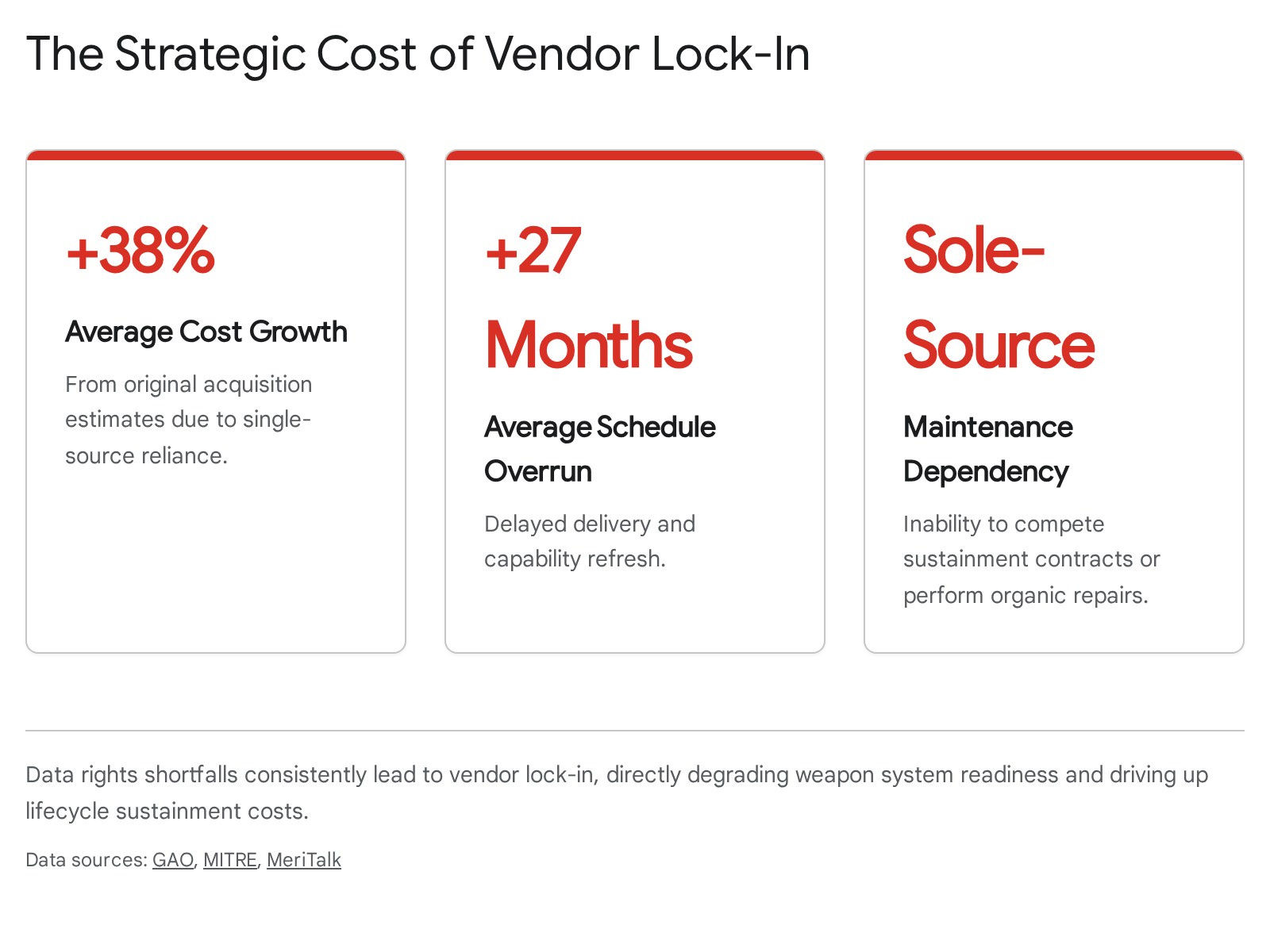
Vendor lock-in occurs when the DoD becomes so dependent on a single supplier that it cannot transition to an alternative vendor without incurring prohibitive costs or unacceptable operational delays.48 The theoretical risks of this dependency are starkly illustrated by historical sustainment data.
5.1 Historical Precedents of Vendor Lock-In (GAO Findings)
A comprehensive review of major weapon systems in sustainment by the Government Accountability Office (GAO-25-107468) found that the DoD consistently struggles to secure the data rights necessary for independent maintenance.12 The report highlighted that programs receive thousands of individual data deliverables, which under-resourced personnel struggle to review for accuracy and completeness.12
The consequences of failing to secure these rights are severe. Maintainers of the F/A-18 have been unable to procure data rights for specific radio frequency cables for over a decade, forcing them to rely entirely on the vendor’s schedule or resort to cannibalizing grounded aircraft for parts.12 F-35 maintainers cannot repair significant corrosion issues without direct contractor support due to a lack of technical data, extending repair timeframes dramatically.12 In the Littoral Combat Ship (LCS) program, a prime contractor refused to repair a broken hydraulic motor without the OEM physically present, resulting in a multi-week wait for a routine fix.12
While these examples pertain to legacy crewed platforms, the implications for drone fleets are profound. According to MITRE analysis, the average major defense acquisition program experiencing vendor lock-in suffers a 38% cost growth from original estimates and a 27-month schedule overrun.49 If the DoD attempts to scale a fleet of thousands of attritable drones but applies the same flawed, proprietary IP strategies, the resulting sustainment backlog will paralyze operational readiness and negate the primary advantage of low-cost mass.
5.2 Comparing OEM Depot Repair with Organic Field Capabilities
The financial model of defense sustainment is heavily skewed toward Contractor Logistics Support (CLS) and OEM depot repair. OEMs affiliated with in-house depots control the majority of revenue by leveraging their exclusive access to proprietary data and parts.51 For contractors, the profit incentive is strong; they maintain a monopoly on spare parts, specialized tooling, and the cleared personnel required to service highly classified drone capabilities.52
However, this reliance on CLS introduces dangerous inflexibility. Government funding is rigidly siloed into specific Element of Expense Investment Codes (EEIC). If a program manager lacks funding in one area but has a surplus in another, bureaucratic processes delay the conversion of funds, whereas a contractor has total fiscal flexibility to reallocate resources to maximize profit.52 By failing to secure the data rights necessary to perform organic repair—or to open maintenance contracts to third-party independent MROs (Maintenance, Repair, and Overhaul facilities)—the DoD sacrifices readiness for perceived short-term acquisition ease.51
5.3 Cyber Security, Forensics, and Software Vulnerabilities
Closed-source, black-box systems also present profound cybersecurity vulnerabilities. While proprietary systems are often touted as more secure through obscurity, the inability of independent military cyber-teams to audit the code leaves platforms exposed.
Aviation cybersecurity firm CYVIATION recently uncovered a critical vulnerability within the PX4 drone operating system—a widely adopted open-source foundation used in many commercial and military systems—that could allow malicious actors to remotely seize control of drones mid-flight.53 While this flaw was discovered and patched due to the open nature of the codebase, similar flaws buried deep within proprietary, closed-source military flight controllers may go undetected until exploited by an adversary.53
Furthermore, many drones utilize unencrypted or proprietary datalinks for communication. Protocols like MAVLink, commonly used to connect ground control stations to uncrewed vehicles, can be intercepted or manipulated if not properly secured.54 Mainstream drones often rely on unencrypted radio frequencies, allowing adversaries to launch man-in-the-middle attacks, hijack flight controllers, or siphon biometric and visual data stored on the drone.55 If a drone’s communication architecture is proprietary and closed, the military cannot organically upgrade the encryption standards or integrate modern, zero-trust network protocols without relying entirely on the OEM’s development timeline.56
6. Forward-Edge Operations and Lessons from High-Intensity Conflict
The ultimate test of any acquisition strategy is its efficacy in a contested operational environment. As the character of war shifts toward distributed lethality, the ability to maintain, repair, and adapt equipment at the “forward edge”—the front lines of combat—has become a critical determinant of tactical success.
6.1 Decentralized Maintenance in the Ukraine Paradigm
In traditional operations over the past two decades, the U.S. military relied heavily on centralized, contractor-supported depots. Damaged equipment was packed up, shipped out of the theater to a secure facility, repaired by civilians, and eventually returned.57
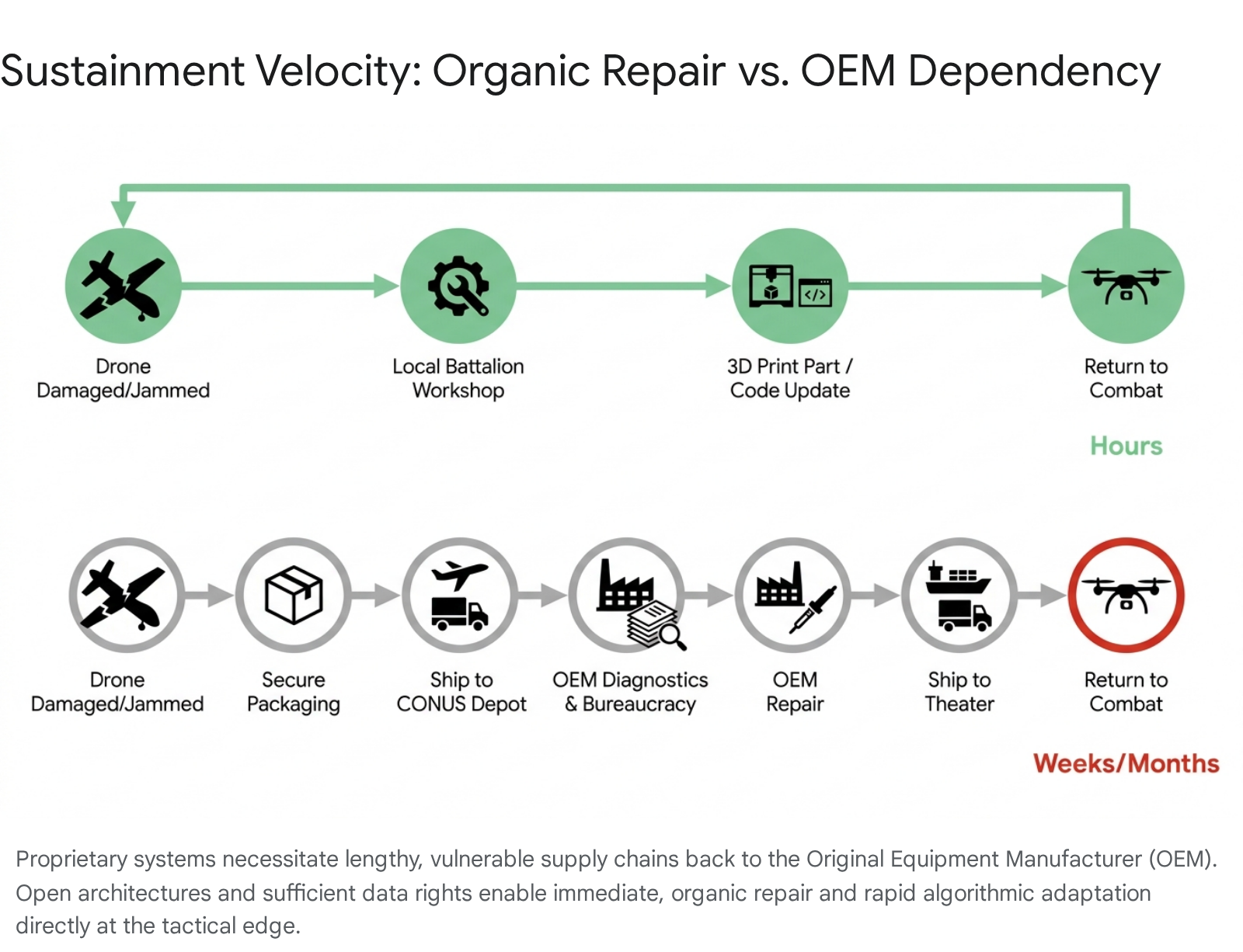
In a high-intensity, large-scale combat operation against a peer adversary, this centralized sustainment model is unviable. Logistics nodes will be targeted, supply lines will be contested, and the sheer volume of drone attrition will overwhelm traditional repair pipelines.6 The ongoing conflict in Ukraine offers a stark preview of this reality.
Ukrainian forces have successfully decentralized their drone support systems, integrating specialized engineering workshops directly into the organizational structure of frontline battalions.6 These highly mobile, 10- to 12-person teams consist of skilled technicians who diagnose, repair, and upgrade UAV platforms on demand.6 Because they operate at the forward edge, they benefit from an immediate, continuous feedback loop with drone pilots.
When a drone experiences a technical failure or combat damage, these workshops provide emergency repairs in hours rather than the weeks required by traditional logistics.6 This extreme agility is only possible because Ukrainian forces utilize commercial, open-source, or highly modifiable systems.14 If they were forced to operate under the restrictive proprietary frameworks standard in U.S. defense procurement—where repairing a circuit board violates an end-user license agreement or requires OEM cryptographic authentication—their operational tempo would collapse.6
6.2 Additive Manufacturing and Rapid Iteration at the Tactical Edge
A key enabler of organic repair at the forward edge is additive manufacturing (3D printing). Ukrainian workshops heavily utilize 3D printing to fabricate critical drone components, spare parts, and bespoke munitions adapters on demand.6 By modeling and fabricating parts locally, these teams significantly reduce reliance on vulnerable external supply chains and ensure rapid restoration of combat power.6
For the U.S. military to replicate this capability, it must possess the legal right and technical data to print replacement parts. If the dimensions, material specifications, and digital models of a drone’s structural components are classified as proprietary DMPD, soldiers are legally and technically prohibited from printing replacements.12
The debate surrounding the “Right to Repair” highlights this tension. Secretary of the Army Dan Driscoll recently highlighted an instance where an Army team reverse-engineered and 3D-printed a replacement part for a UH-60 Black Hawk fuel tank for $3,000 in 43 days, whereas the vendor charged $14,000 with significantly longer lead times.62 While industry representatives warn that compelling the transfer of sensitive manufacturing techniques risks exposing trade secrets and deterring commercial investment, the inability to organically manufacture critical components at the edge remains a glaring operational vulnerability.61
6.3 Overcoming Electronic Warfare via Algorithmic Agility
The electromagnetic spectrum is the most fiercely contested domain in modern drone warfare. Adversaries continuously deploy sophisticated Electronic Warfare (EW) systems to jam command links, spoof GPS signals, and disrupt video feeds.17
When Russian EW actively jams a particular frequency along the front line, Ukrainian engineering workshops do not submit a request to a prime contractor and wait weeks for a software patch. Instead, they mitigate the problem in-house, altering tactics, swapping antennas, or modifying frequency-hopping algorithms within hours.6 They execute localized software updates to alter flight profiles or remove features that transmit identification data, minimizing the risk of enemy interception.6
If a U.S. drone operates on closed-source software, forward-edge operators are locked out of the flight controller.7 They cannot rewrite the navigation logic to rely on optical flow when GPS is denied, nor can they rapidly integrate a new third-party anti-jamming module.63 Bypassing bureaucratic OEM repair cycles is not a matter of convenience; it is a prerequisite for survival on the modern battlefield.
7. Current DoD Initiatives Driving Open Architecture Adoption
Recognizing the urgent need to field attritable mass and break free from slow, proprietary acquisition cycles, the DoD has launched several high-profile initiatives centered heavily on open systems and rapid scaling.
7.1 The Replicator Initiative and Attritable Autonomy
Announced in August 2023 by Deputy Secretary of Defense Kathleen Hicks, the Replicator initiative aims to accelerate the delivery of thousands of All-Domain Attritable Autonomous (ADA2) systems to warfighters within an 18-to-24-month window, specifically to counter the pacing threat of China’s military mass.1
Replicator explicitly targets the “valley of death” in defense acquisition by leveraging existing authorities to scale commercial technology rapidly.65 The initiative spans multiple domains and has successfully awarded contracts to over 30 hardware and software companies, of which 75% are non-traditional defense contractors.1
The second tranche of the first phase, Replicator 1.2, includes the Army’s Company-Level Small UAS effort—selecting Anduril Industries’ Ghost-X and Performance Drone Works’ C-100—and the Air Force’s Enterprise Test Vehicle (ETV).1 The success of Replicator relies entirely on avoiding vendor lock-in. As General James Slife, Vice Chief of Staff of the Air Force, noted regarding the ETV, its “modular design and open system architecture make it an ideal platform for program offices to test out new capabilities at the sub-system level, reducing risk, and demonstrating various options for weapon employment”.1
Recognizing that autonomy relies on software, the Defense Innovation Unit (DIU) awarded specific software contracts under Replicator to support resilient command and control (C2) and collaborative autonomy. The ORIENT program focuses on improving C2 resilience, while the ACT program focuses on the automated coordination of drone swarms.66 These efforts establish a baseline reference architecture informed by both government and industry, ensuring future opportunities for competing and scaling best-of-breed solutions.67
7.2 Counter-sUAS Expansion Under Replicator 2
In late 2024, the DoD announced that the next phase, Replicator 2, will pivot to tackle the warfighter priority of countering the threat posed by small uncrewed aerial systems (C-sUAS) to critical installations and force concentrations.68 Secretary of Defense Lloyd J. Austin III explicitly noted that Replicator 2 will assist with overcoming challenges in “production capacity, technology innovation, authorities, policies, open system architecture and system integration”.68
Counter-drone operations require the seamless fusion of disparate sensors (radar, acoustics, optical) and effectors (kinetic interceptors, EW jammers).69 If each sensor operates on a bespoke, proprietary network, they provide little beyond siloed point-defense.69 Replicator 2’s emphasis on open architecture ensures that third-party solutions can plug into a unified defensive net, allowing a single command interface to coordinate multi-domain responses.71
7.3 Project SkyFoundry and Organic Industrial Base Modernization
Parallel to Replicator, the U.S. Army is pursuing a massive ramp-up in organic drone production. The Army Materiel Command’s “SkyFoundry” pilot program aims to rapidly develop, test, and manufacture small drones using innovative manufacturing methods at government-owned facilities.72 Supported by legislative efforts like the SkyFoundry Act of 2025, the program’s ambitious goal is to reach a production capacity of tens of thousands to one million small drones annually.2
By pulling manufacturing into the Organic Industrial Base (OIB)—specifically utilizing facilities like the Red River Army Depot and the Rock Island Arsenal-Joint Manufacturing and Technology Center—the Army aims to cut adversaries out of the supply chain, bypass traditional contracting red tape, and maintain direct control over intellectual property.2
SkyFoundry represents a radical departure from traditional procurement. By producing drones in-house, the government inherently sidesteps many proprietary IP constraints associated with prime contractors. However, to maintain technological superiority, SkyFoundry drones must still be built upon a strict MOSA framework. This open approach ensures the Army can seamlessly integrate the latest commercial AI software, advanced optical payloads, and secure data links developed by private industry into its organically manufactured airframes without triggering vendor lock-in.75
| Initiative | Primary Objective | Key Technologies / Systems | Role of MOSA & Data Rights |
| Replicator 1 (Tranches 1.1 & 1.2) | Field thousands of ADA2 systems to counter adversary mass within 18-24 months. | ETV, Ghost-X, C-100, ACT (Swarm logic), ORIENT (Resilient C2). | Relies on modularity to rapidly integrate non-traditional vendor software into standard airframes. |
| Replicator 2 | Rapidly deploy comprehensive Counter-sUAS defenses to protect critical installations. | DroneHunter F700, integrated multi-modal sensor networks, EW effectors. | Demands open architecture to fuse disparate, multi-vendor sensors into a unified C2 network. |
| Project SkyFoundry | Leverage the Organic Industrial Base to domestically mass-produce 1M drones annually. | In-house manufactured small UAS, 3D printed components, integrated commercial AI. | Government retains IP of the core platform; uses open interfaces to plug in specialized commercial payloads. |
8. Strategic Guidance for Acquisition Leadership
To fully leverage massive investments in drone technology and prevent the paralyzing effects of vendor lock-in, DoD leadership and acquisition professionals must align their contracting strategies with the realities of software-defined warfare. The following actions provide a strategic framework for navigating intellectual property constraints and enforcing open architectures.
8.1 Assert MOSA Compliance as a Mandatory Evaluation Factor
Program managers must move beyond treating MOSA as a theoretical design preference or a buzzword. Open architectures must be integrated into the Request for Proposal (RFP) and scored aggressively during source selection.21
Solicitations must require vendors to deliver machine-readable documentation and functional descriptions of all software-defined interfaces, conveying the semantic meaning of interface elements to guarantee third-party interoperability.13 Leadership must empower the DoD IP Cadre to review these proposals and disqualify vendors whose architectures rely on closed, proprietary standards that deliberately limit interoperability.77
8.2 Leverage Specially Negotiated License Rights and OTAs
Rather than defaulting to standard DFARS clauses that incentivize vendors to hide behind the “segregability doctrine,” contracting officers should utilize Specially Negotiated License Rights (SNLRs) and Other Transaction Authorities (OTAs).11 Because OTAs are not subject to the strictures of the Federal Acquisition Regulation (FAR), they provide the flexibility to negotiate tailored data rights that reflect the actual funding contributions and operational needs of both parties.78
Additionally, the DoD should explore innovative models such as “Data-as-a-Service” (DaaS) for sustainment. Under this model, the government pays for continuous, subscription-based access to a contractor’s technical data library to support maintenance and repair, rather than attempting to forcibly extract proprietary source code up front.61 Exploring mechanisms like the Finstad Amendment—which proposes a comprehensive inventory of existing technical data to identify specific gaps—allows for targeted, cost-effective negotiations rather than damaging, one-size-fits-all mandates.61
8.3 Structure Solicitations to Isolate Proprietary Subsystems
When a vendor utilizes private internal research and development (IRAD) funding to create a highly advanced, proprietary component, the DoD should not engage in protracted legal battles to own the internal IP. Instead, the DoD must demand that the component acts as a discrete “black box” that interacts with the rest of the system only through government-owned or consensus-based open interfaces (e.g., OMS, UCI, FACE).10
This modular licensing approach allows the government to treat the proprietary technology as a cleanly swappable module.10 It preserves the vendor’s IP and trade secrets—maintaining their incentive to innovate—while ensuring the government is never locked into that specific vendor when a superior or cheaper alternative becomes available.10
8.4 Secure Rights for AI Model Retraining
In the procurement of autonomous systems, conventional definitions of maintenance and repair are insufficient. Contracts must explicitly define who holds the intellectual property rights to retrain AI models.8
If a drone’s computer vision algorithm fails to detect a new class of adversary armor, or its autonomous navigation system is continually thwarted by novel GPS spoofing, the model is functionally broken. The DoD must have the legal right and technical capability to feed new training datasets into the model without returning to the OEM for renegotiation.8 Clarifying the boundaries between operational retraining data and the core proprietary algorithm is essential to maintaining the tactical relevance of AI-enabled drone fleets.
9. Conclusion
The future of unmanned aerial warfare will not be dominated by the military that fields the most exquisite, proprietary hardware, but by the military that can iterate, repair, and adapt its systems fastest at the forward edge. The Department of Defense’s massive investments in drone technology risk generating a fragile, unmaintainable fleet if acquisition strategies fail to address the systemic constraints of intellectual property and system architecture.
By strictly enforcing a Modular Open Systems Approach, utilizing the specialized expertise of the IP Cadre to craft nuanced data rights strategies, and fostering an ecosystem where hardware and software are cleanly decoupled, the DoD can break the historical cycle of vendor lock-in. Embracing open interfaces, transparent technical data standards, and decentralized organic repair will ensure that U.S. warfighters retain the operational agility required to deter and defeat pacing threats in an era defined by rapid technological disruption.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Sources Used
- Deputy Secretary of Defense Kathleen Hicks Announces Additional Replicator All-Domain Attritable Autonomous Capabilities – Department of War, accessed April 24, 2026, https://www.war.gov/News/Releases/Release/Article/3963289/deputy-secretary-of-defense-kathleen-hicks-announces-additional-replicator-all/
- Congressman Pat Harrigan Introduces SkyFoundry Act to Restore America’s Drone Dominance, accessed April 24, 2026, https://harrigan.house.gov/media/press-releases/congressman-pat-harrigan-introduces-skyfoundry-act-restore-americas-drone
- The U.S. Military Risks Letting Contractors Define How It Sees the Battlefield – War on the Rocks, accessed April 24, 2026, https://warontherocks.com/cogs-of-war/the-u-s-military-risks-letting-contractors-define-how-it-sees-the-battlefield/
- MOSA | NAVAIR, accessed April 24, 2026, https://www.navair.navy.mil/MOSA
- What is MOSA? – BAE Systems, accessed April 24, 2026, https://www.baesystems.com/en-us/definition/what-is-mosa
- Innovating Under Fire: Lessons from Ukraine’s Frontline Drone Workshops, accessed April 24, 2026, https://mwi.westpoint.edu/innovating-under-fire-lessons-from-ukraines-frontline-drone-workshops/
- Lowering Barriers to Entry for Fully-Integrated Custom Payloads on a DJI Matrice – arXiv, accessed April 24, 2026, https://arxiv.org/html/2405.06176v1
- When Deft Hands Are Needed: DoD’s Conflicted Strategies for Acquiring IP Rights in AI Systems – Business Law Today from ABA, accessed April 24, 2026, https://businesslawtoday.org/2026/04/dod-conflicted-strategies-acquiring-ip-rights-ai-systems/
- How Data Rights Stifle Innovation in the DoD (and How to Fix Them) – Future, accessed April 24, 2026, https://future.com/data-rights-stifle-innovation-in-the-dod/
- DOD Releases Intellectual Property Guidebook: Key Insights for Defense Contractors, Part 3 | PilieroMazza, Law Firm, Government Contracts Attorney, accessed April 24, 2026, https://www.pilieromazza.com/dod-releases-intellectual-property-guidebook-key-insights-for-defense-contractors-part-3/
- Intellectual Property Guidebook for DoD Acquisition – acq.osd.mil, accessed April 24, 2026, https://www.acq.osd.mil/asda/dpc/api/docs/intellectual%20property%20guidebook%20for%20dod%20acquisition%20signed.pdf
- GAO-25-107468, WEAPON SYSTEM SUSTAINMENT: DOD Can …, accessed April 24, 2026, https://files.gao.gov/reports/GAO-25-107468/index.html
- Modular Open Systems Approach (MOSA) – Defense Standardization Program, accessed April 24, 2026, https://www.dsp.dla.mil/Programs/MOSA/
- The Pentagon’s Replicator Initiatives’ Real Challenge Is Cultural, Not Technical, accessed April 24, 2026, https://www.gotechinsights.com/blog/replicator
- Airborne attritable systems and open systems – Military Embedded Systems, accessed April 24, 2026, https://militaryembedded.com/unmanned/payloads/airborne-attritable-systems-and-open-systems
- Military Drone Software Development: How to Build a Drone Control App? – Patternica, accessed April 24, 2026, https://patternica.com/blog/military-drone-software-development
- The Autonomous Arsenal in Defense of Taiwan: Technology, Law, and Policy of the Replicator Initiative | The Belfer Center for Science and International Affairs, accessed April 24, 2026, https://www.belfercenter.org/replicator-autonomous-weapons-taiwan
- The Drone Supply Chain War: Identifying the Chokepoints to Making a Drone – CSIS, accessed April 24, 2026, https://www.csis.org/analysis/drone-supply-chain-war-identifying-chokepoints-making-drone
- Drones and the Federal Government: What Contractors Need to Know About the Latest OMB Guidance | Insights | Holland & Knight, accessed April 24, 2026, https://www.hklaw.com/en/insights/publications/2025/12/drones-and-the-federal-government-what-contractors-need-to-know
- Manufacturing at the Tactical Edge: The Future of Military Drone Operations, accessed April 24, 2026, https://automationalley.com/2026/02/18/manufacturing-at-the-tactical-edge-the-future-of-military-drone-operations/
- Implementing a Modular Open Systems Approach in Department of …, accessed April 24, 2026, https://www.cto.mil/wp-content/uploads/2025/03/MOSA-Implementation-Guidebook-27Feb2025-Cleared.pdf
- Taking a Modular Open Systems Approach (MOSA) to Next-Gen Military Systems – RTI, accessed April 24, 2026, https://www.rti.com/blog/taking-a-modular-open-systems-approach
- Modular Open Systems Approach – DoW Research & Engineering, OUSW(R&E), accessed April 24, 2026, https://www.cto.mil/sea/mosa/
- Use of Open Mission Systems/Universal Command and Control Interface, accessed April 24, 2026, https://www.afacpo.com/AQDocs/AQMemos/20181009%20-%20OMS%20UCI%20Memo.pdf
- Open Mission Systems – VDL, accessed April 24, 2026, https://www.vdl.afrl.af.mil/programs/oam/files/oam-brochure.pdf
- Open Mission Systems (OMS) in a Nutshell – VDL, accessed April 24, 2026, https://www.vdl.afrl.af.mil/programs/oam/OMS_Marketing.pdf
- The FACE Technical Standard: Enabling modular, open, and future-proof avionics systems, accessed April 24, 2026, https://militaryembedded.com/avionics/software/the-face-technical-standard-enabling-modular-open-and-future-proof-avionics-systems
- Pentagon ‘On the Cusp’ of Open Systems Breakthrough – National Defense Magazine, accessed April 24, 2026, https://www.nationaldefensemagazine.org/articles/2025/12/4/pentagon-on-the-cusp-of–open-systems-breakthrough
- What Is Mosa Sosa Cmoss – Curtiss-Wright Defense Solutions, accessed April 24, 2026, https://defense-solutions.curtisswright.com/resources/white-papers/what-is-mosa-sosa-cmoss
- Guide to Drone Payloads: Types and Use Cases – Voliro, accessed April 24, 2026, https://voliro.com/blog/drone-payloads/
- Why autonomy upgrades stall at integration – and how MOSA fixes it, accessed April 24, 2026, https://militaryembedded.com/unmanned/payloads/why-autonomy-upgrades-stall-at-integration-and-how-mosa-fixes-it
- Design Standard Update Improves Modular Architecture for Unmanned Platforms, accessed April 24, 2026, https://www.jhuapl.edu/news/news-releases/250805-mod-payload
- MOD PAYLOAD – DTIC, accessed April 24, 2026, https://apps.dtic.mil/sti/pdfs/AD1167779.pdf
- App for DJI Drone: Custom Flight Control and Mapping Solutions – A-bots, accessed April 24, 2026, https://a-bots.com/blog/App-for-DJI-Drone
- Air Force validates open architecture, expands Collaborative Combat Aircraft ecosystem, accessed April 24, 2026, https://www.af.mil/News/Article-Display/Article/4405471/air-force-validates-open-architecture-expands-collaborative-combat-aircraft-eco/
- IP, Technical Data Rights Continue to Spark Debate – National Defense Magazine, accessed April 24, 2026, https://www.nationaldefensemagazine.org/articles/2025/10/1/ip-technical-data-rights-continue-to-spark-debate
- Intellectual Property Guidebook for DoD Acquisition 30 April 2025 Office of the Under Secretary of Defense for Acquisition and S – ARPA-H, accessed April 24, 2026, https://arpa-h.gov/sites/default/files/2025-05/DoD%20_IP_Guidebook_Apr2025.pdf
- IP Strategy – Adaptive Acquisition Framework, accessed April 24, 2026, https://aaf.dau.edu/aaf/software/ip-strategy/
- Protecting Defense Technology Innovations | Sterne Kessler, accessed April 24, 2026, https://www.sternekessler.com/news-insights/insights/protecting-defense-technology-innovations/
- Intellectual Property and Data Rights Considerations: Contracting with Small Business Owners — Strategic Planning, accessed April 24, 2026, https://business.defense.gov/Portals/57/MARC%20Presentation.pdf?ver=2019-11-06-084251-993
- GAO: Vendor Lock-In and Lack of Data Rights are Delaying Navy Maintenance, accessed April 24, 2026, https://maritime-executive.com/article/gao-vendor-lock-in-and-lack-of-data-rights-are-delaying-navy-maintenance
- The DoD Should Pilot a New Category of Software Data Rights | Anduril, accessed April 24, 2026, https://www.anduril.com/news/the-dod-should-pilot-a-new-category-of-software-data-rights
- DOD Releases Intellectual Property Guidebook: Key Insights for Defense Contractors, Part 2 | PilieroMazza, Law Firm, Government Contracts Attorney, accessed April 24, 2026, https://www.pilieromazza.com/dod-releases-intellectual-property-guidebook-key-insights-for-defense-contractors-part-2/
- 227.7103-8 Deferred delivery and deferred ordering of technical data. – Acquisition.GOV, accessed April 24, 2026, https://www.acquisition.gov/dfars/227.7103-8-deferred-delivery-and-deferred-ordering-technical-data.
- SUBPART 227.71 TECHNICAL DATA AND ASSOCIATED RIGHTS – acq.osd.mil, accessed April 24, 2026, https://www.acq.osd.mil/dpap/dars/dfars/html/current/227_71.htm
- 252.227-7027 Deferred Ordering of Technical Data or Computer Software. | Acquisition.GOV, accessed April 24, 2026, https://www.acquisition.gov/dfars/252.227-7027-deferred-ordering-technical-data-or-computer-software.
- SUMMARY OF THE SECTION 813 PANEL’S 2018 REPORT – National Defense Industrial Association, accessed April 24, 2026, https://www.ndia.org/-/media/sites/ndia/policy/documents/813-panel-report-summary_3.ashx
- What is Vendor Lock-in? Costs, Risks, and Prevention Strategies – DataCore Software, accessed April 24, 2026, https://www.datacore.com/glossary/vendor-lock-in/
- Gaining Leverage over Vendor Lock to Improve Acquisition Performance and Cost Efficiencies – Mitre, accessed April 24, 2026, https://www.mitre.org/sites/default/files/publications/gaining-leverage-over-vendor-lock-14-1262.pdf
- GAO: DOD Struggles to Manage Weapon System IP – MeriTalk, accessed April 24, 2026, https://www.meritalk.com/articles/gao-dod-struggles-to-manage-weapon-system-ip/
- Military MRO Market – Aircraft Maintenance, Repair and Overhaul – Forecast & Size, accessed April 24, 2026, https://www.mordorintelligence.com/industry-reports/military-aviation-maintenance-repair-and-overhaul-market
- ORGANIC VERSUS CONTRACTOR LOGISTICS SUPPORT FOR DEPOT-LEVEL REPAIR: FACTORS THAT DRIVE SUB-OPTIMAL DECISIONS – DTIC, accessed April 24, 2026, https://apps.dtic.mil/sti/pdfs/AD1037198.pdf
- Aviation Cybersecurity Firm Identifies Critical Drone Software Vulnerability – ePlaneAI, accessed April 24, 2026, https://www.eplaneai.com/news/aviation-cybersecurity-firm-identifies-critical-drone-software-vulnerability
- The best SDKs for developers of applications for drones: 3D Robotics and DJI – BBVA, accessed April 24, 2026, https://www.bbva.com/en/the-best-sdks-for-developers-of-applications-for-drones-3d-robotics-and-dji/
- How Drone and UAV Technology Will Exacerbate Data Privacy Issues – Logikcull, accessed April 24, 2026, https://www.logikcull.com/blog/drone-uav-technology-will-exacerbate-data-privacy-issues
- The Pentagon’s New Mandate: Speed, Innovation, and Commercial Tech – Greymatter.io, accessed April 24, 2026, https://greymatter.io/blog/the-pentagons-mandate-speed-innovation-commercial-tech/
- The fresh maintenance and sustainment challenges as UAVs take off in defense, accessed April 24, 2026, https://militaryembedded.com/unmanned/counter-uas/the-fresh-maintenance-and-sustainment-challenges-as-uavs-take-off-in-defense
- Theater Sustainment Transformation: Lessons from the Russia-Ukraine War – Army.mil, accessed April 24, 2026, https://www.army.mil/article/274914/theater_sustainment_transformation_lessons_from_the_russia_ukraine_war
- The Evolution of – Purdue Agriculture, accessed April 24, 2026, https://ag.purdue.edu/department/extension/ppp/resources/ppp-publications/_docs/ppp-154.pdf
- Lessons from the Ukraine Conflict: Modern Warfare in the Age of Autonomy, Information, and Resilience – CSIS, accessed April 24, 2026, https://www.csis.org/analysis/lessons-ukraine-conflict-modern-warfare-age-autonomy-information-and-resilience
- IP and Data Rights: Protecting DoD’s Access to Innovation – National Defense Industrial Association, accessed April 24, 2026, https://www.ndia.org/-/media/sites/ndia/policy/ip-and-data-rights/ip-and-data-rights-white-paper.pdf?download=1?download=1
- Who Controls the Wrench: The Debate Over the “Right to Repair” – CSIS, accessed April 24, 2026, https://www.csis.org/analysis/who-controls-wrench-debate-over-right-repair
- From Ukraine to the Middle East, GPS Disruption Drives Demand for Next-Generation Defense Technology – GlobeNewswire, accessed April 24, 2026, https://www.globenewswire.com/news-release/2026/04/20/3276999/0/en/from-ukraine-to-the-middle-east-gps-disruption-drives-demand-for-next-generation-defense-technology.html
- Cybersecurity Challenges in Drone-Based Systems – Anvil Labs, accessed April 24, 2026, https://anvil.so/post/cybersecurity-challenges-in-drone-based-systems
- Implementing DoD Replicator Initiative at Speed and Scale – Defense Innovation Unit, accessed April 24, 2026, https://www.diu.mil/latest/implementing-the-department-of-defense-replicator-initiative-to-accelerate
- Defense Innovation Unit Announces Software Vendors to Support Replicator, accessed April 24, 2026, https://www.diu.mil/latest/defense-innovation-unit-announces-software-vendors-to-support-replicator
- Replicator: Changing the Way DoD Accelerates Software for Autonomous Systems, accessed April 24, 2026, https://www.youtube.com/watch?v=P3BM0DJqads
- Memorandum: Replicator 2 Direction and Execution – Defense Innovation Unit, accessed April 24, 2026, https://www.diu.mil/latest/memorandum-replicator-2-direction-and-execution
- Frontline Fusion: The Network Architecture Needed to Counter Drones, accessed April 24, 2026, https://mwi.westpoint.edu/frontline-fusion-the-network-architecture-needed-to-counter-drones/
- Advances and Challenges in Drone Detection and Classification Techniques: A State-of-the-Art Review – PMC, accessed April 24, 2026, https://pmc.ncbi.nlm.nih.gov/articles/PMC10780901/
- AUSA 2025: Assured PNT, Launch Effects, Autonomy – Inside Unmanned Systems, accessed April 24, 2026, https://insideunmannedsystems.com/ausa-2025-assured-pnt-launch-effects-autonomy/
- Army Under Secretary visits Red River, eyes SkyFoundry future | Article, accessed April 24, 2026, https://www.army.mil/article/289507/army_under_secretary_visits_red_river_eyes_skyfoundry_future
- Army aims to manufacture 10,000 drones per month by 2026 – DefenseScoop, accessed April 24, 2026, https://defensescoop.com/2025/10/14/army-small-drones-skyfoundry/
- Unmanned, unmatched: How APG is transforming military operations | Article – U.S. Army, accessed April 24, 2026, https://www.army.mil/article/289346/unmanned_unmatched_how_apg_is_transforming_military_operations
- U.S. Government Aerospace Procurement Updates and Implications for Intellectual Property, accessed April 24, 2026, https://www.knobbe.com/blog/u-s-government-aerospace-procurement-updates-and-implications-for-intellectual-property/
- U.S. Government Aerospace Procurement Updates and Implications for Intellectual Property, accessed April 24, 2026, https://www.jdsupra.com/legalnews/u-s-government-aerospace-procurement-2812490/
- IP Cadre – acq.osd.mil, accessed April 24, 2026, https://www.acq.osd.mil/asda/dpc/api/ip-cadre.html
- Protecting IP, Data Rights In Other Transaction Agreements – National Defense Magazine, accessed April 24, 2026, https://www.nationaldefensemagazine.org/articles/2025/7/15/viewpoint-protecting-ip-data-rights-in-other-transaction-agreements
