1. Executive Summary
The transition toward the widespread adoption of Commercial Off-The-Shelf (COTS) Unmanned Aerial Systems (UAS) represents a profound paradigm shift in modern military operations and acquisition strategies. Driven by the necessity for rapid procurement, reduced unit costs, and the urgent need to match the highly accelerated innovation cycles observed in contemporary conflicts, the United States Department of Defense (DoD) is heavily investing in civilian technology ecosystems. However, the operationalization of commercial technology within military architectures introduces a highly complex spectrum of systemic, cyber, environmental, and geopolitical risks that are frequently misunderstood or entirely overlooked by policymakers. There is a persistent, overarching tendency to fixate on the physical airframe’s capabilities—such as payload capacity, battery life, and optical resolution—while critically neglecting the vast, underlying infrastructure required to securely design, build, operate, and sustain these systems in highly contested, multidomain environments.
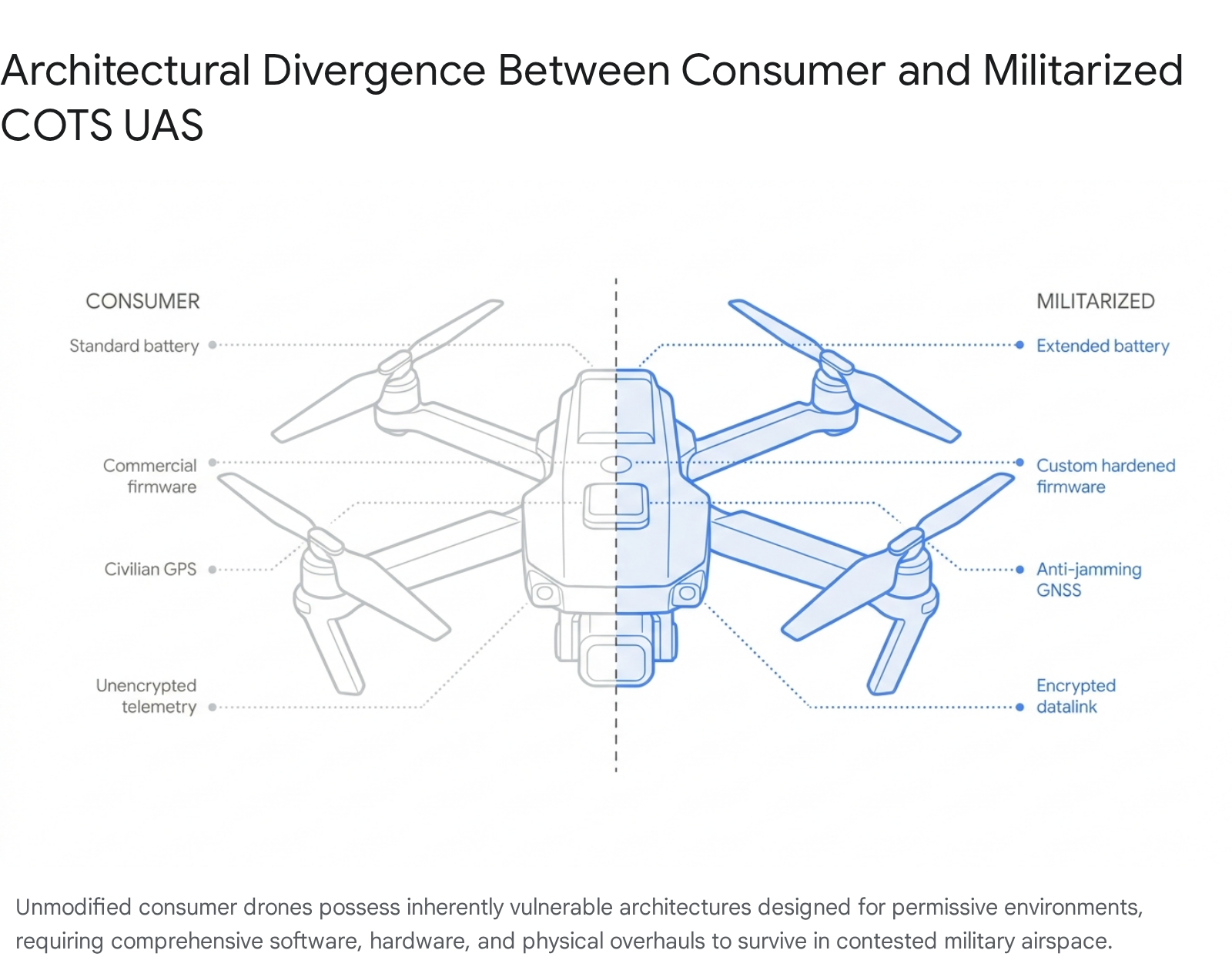
The rapid integration of civilian technology into military frameworks creates an inherent and dangerous architectural mismatch. Consumer drones are meticulously engineered to maximize profit margins for operation in benign, permissive civilian environments. They are designed for continuous internet connectivity, relying heavily on centralized firmware updates, commercial mapping Application Programming Interfaces (APIs), and unencrypted, easily accessible telemetry protocols. When deployed in rigorous military contexts, these convenience-oriented features immediately transform into critical, systemic vulnerabilities. Adversaries possess the sophisticated capability to exploit unvetted commercial firmware, intercept unencrypted data links, and leverage hardware backdoors to neutralize, track, or actively hijack commercial systems. Furthermore, commercial components are typically rated only for standard civilian environments. They critically lack the robust environmental hardening necessary to survive the extreme temperature fluctuations, salt fog corrosion, outgassing, and electromagnetic interference that are ubiquitous in military operations.
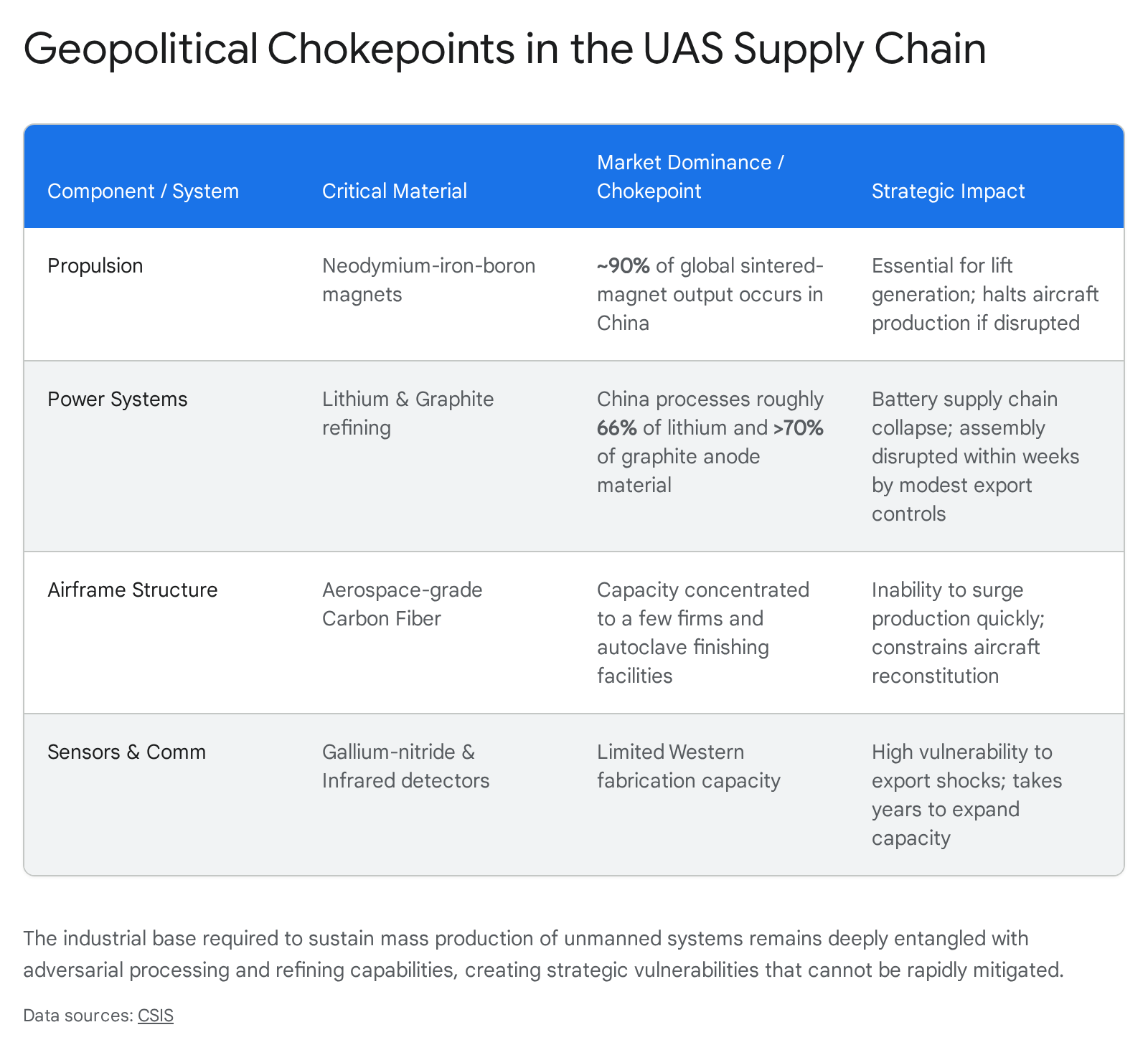
Beyond the immediate technical limitations, the Department of Defense faces profound, long-term geopolitical and supply chain vulnerabilities. The global commercial drone market and its underlying raw material supply chains—ranging from carbon fiber precursors and rare-earth magnets to lithium refinement and gallium-nitride semiconductors—are disproportionately controlled by adversarial nations. A heavy reliance on these foreign-dominated pipelines exposes the domestic defense industrial base to the catastrophic risk of sudden logistical disruptions and coercive export controls during geopolitical crises.
To successfully enable warfighters and achieve sustained technological overmatch, defense leadership must adopt a holistic, structural approach to securing and hardening commercial pipelines. This necessitates moving far beyond a legacy “trust but verify” model to implementing rigorous Zero Trust architectures at both the software and silicon levels. It requires the mandatory integration of machine-readable Software Bill of Materials (SBOMs), rigorous hardware verification using Physical Unclonable Functions (PUFs), the strict enforcement of the American Security Drone Act (ASDA), and the complete restructuring of sustainment models to align with the compressed, three-month innovation cycles currently defining modern drone warfare. This report details these overlooked vulnerabilities and outlines the systemic engineering, cyber, and policy requirements necessary to safely integrate COTS technology into the joint force.
2. The Fallacy of Direct Commercial Adoption: Operational Realities and Electronic Warfare
A foundational risk in the integration of civilian technology into military operations stems from a dangerous, pervasive misconception regarding the term “Commercial Off-The-Shelf” itself.1 Within the context of modern defense procurement, the drive for rapid adoption has routinely led to the conflation of unmodified consumer drones with specifically militarized systems that simply happen to be built from commercial components.1
The Flawed Paradigm of Direct Adoption
In an effort to rapidly equip forward-deployed forces, some allied militaries have adopted overly permissive policies allowing individual units to purchase and operate commercial UAS with minimal friction, often requiring little more than basic registration with military aviation authorities.1 While this significantly accelerates operator familiarization and tactical experimentation, it exposes the broader force to severe operational security and force protection risks.1 The reality of the modern battlefield, particularly observed in the highly contested airspace of the ongoing conflict in Ukraine, emphatically demonstrates that an unmodified civilian drone—such as a standard DJI or Parrot model purchased from a commercial retailer—is functionally obsolete and highly dangerous to its human operator if deployed without significant, structural modification.1
Unmodified COTS UAS are riddled with potentially lethal vulnerabilities that severely limit their military utility and operational lifespan.1 The primary operational risk is an absolute lack of electronic warfare (EW) resilience. Consumer drones are inherently designed to operate in uncongested, uncontested electromagnetic environments, making their command and control (C2) links highly susceptible to both kinetic jamming and non-kinetic cyber takeover.2 Jamming systems emit high-power radio frequency (RF) signals that saturate the receiver, disrupting the communication link and typically forcing the drone to hover aimlessly, initiate an emergency landing, or attempt a return to its takeoff point—often directly exposing the operator’s location.2 In contrast, RF-based cyber takeover is a more innovative, non-kinetic approach that seizes total administrative control of a hostile or compromised drone.2 This allows adversaries to not only neutralize the asset but actively redirect it, utilize it for unauthorized surveillance of friendly positions, or turn its payload against the original operators.2
The Necessity of Comprehensive Militarization
The term COTS is frequently and incorrectly misused by mainstream defense reporting to describe UAS that, while originally developed from commercial components, have been heavily modified and redesigned specifically for warfare.1 The distinction between a consumer toy and a military asset is critical. Militarized COTS systems undergo extensive software and hardware reconfiguration. This includes the removal of manufacturer-imposed flight limits, the integration of advanced resistance to Global Navigation Satellite System (GNSS) spoofing, and the enabling of high-capacity batteries and specialized payload drop mechanisms.3
When strategic leadership incorrectly assumes that commercial availability directly equates to military readiness, it bypasses the rigorous, systemic engineering processes required to properly harden the system.4 To operate effectively, a drone must transition from being an isolated, standalone commercial product into a secure, integrated node within the military’s broader tactical network. This process requires the physical removal of commercial telemetry beacons, the installation of military-grade cryptographic encryption, and the physical modification of the airframe to support munitions or advanced optical sensor arrays.5 Failing to recognize the systemic architectural gap between a consumer product and a militarized asset leads to immediate force protection failures, as operators are forced to field fragile, highly observable systems against sophisticated adversarial EW capabilities.
3. Software Vulnerabilities and the Cyber Attack Surface of Civilian Platforms
The integration of civilian technology into military architectures dramatically expands the software attack surface. Consumer drones are heavily optimized for ease of use, seamless social connectivity, and strict adherence to civilian regulatory compliance, resulting in software architectures that fundamentally conflict with the rigid demands of military operational security.6
The Remote ID Vulnerability and Unencrypted Telemetry
To comply with global civilian aviation regulations, market-leading commercial drone manufacturers, such as DJI (which holds an estimated 94% share of the consumer market), implement proprietary tracking protocols designed to transmit the position of both the drone and its human operator to authorized civilian entities.6 However, extensive academic reverse engineering of these firmware systems reveals catastrophic security flaws that directly threaten the lives of military operators.6
Contrary to widespread vendor claims and public belief, protocols such as DJI’s proprietary DroneID transmit highly sensitive telemetry data entirely unencrypted over the air using the proprietary DJI Universal Markup Language (DUML) over the OcuSync transmission protocol.6 Using inexpensive, commercially available hardware—specifically, off-the-shelf Software Defined Radios (SDR) like the Ettus USRP B205-mini—adversarial forces or unauthorized third parties can easily receive, demodulate, and decode these OFDM (Orthogonal Frequency Division Multiplexing) symbol packets in real-time.6 The intercepted payloads continuously broadcast the precise GPS coordinates (longitude, latitude, altitude, and height), precise velocity, and unique serial identification of the drone.6
More critically, the payload simultaneously broadcasts the exact geographical coordinates of the remote pilot’s smartphone application and the designated “home point”.6 In a combat scenario, this complete lack of encryption transforms the commercial drone into an unintentional homing beacon, directly facilitating rapid, targeted artillery barrages or counter-drone strikes against the human operator. Furthermore, these tracking protocols perform absolutely no internal consistency checks regarding the physical distance between the drone and the pilot’s reported GPS position.6 Researchers have demonstrated that an adversary can trivially spoof the operator coordinates using a standard, non-rooted smartphone and a basic GPS spoofing application, effectively broadcasting false locations to confuse friendly intelligence and compromise the integrity of the entire airspace monitoring system.6
Privilege Escalation, Fuzzing, and Hardware Backdoors
Commercial drones rely on highly complex, integrated cyber-physical systems utilizing diverse operating systems. Depending on the specific component’s complexity, these range from standard Android environments to 32-bit ARM Linux operating systems and custom Real-Time Operating Systems (RTOS) utilized in the transceiver processors to manage time-critical RF connections.6 Advanced security analyses employing novel generational black-box fuzzing methodologies and deep hardware testing have uncovered severe vulnerabilities within these commercial systems, ranging from simple denial of service to arbitrary command execution.6
In a single comprehensive study, researchers identified 16 distinct vulnerabilities ranging from low to critical severity. Fourteen of these identified bugs can be triggered remotely via interactions with the operator’s smartphone, allowing an attacker to intentionally crash the drone mid-flight, posing a severe kinetic safety risk.6 More critically, researchers successfully demonstrated the ability to achieve root-level privilege escalation on commercial drones and their corresponding remote controllers.6 This elevated level of administrative access permits unauthorized users or adversaries to completely disable or bypass mandatory safety countermeasures, such as geofencing algorithms designed to enforce no-fly zones around critical military infrastructure.6
In the context of COTS military adoption, traditional network-based reconnaissance is highly insufficient. The studies conclude that if deep hardware testing—such as physical access methods including Joint Test Action Group (JTAG) debugging, electromagnetic interference (EMI) based testing, and side-channel analysis—is not rigorously applied, undocumented vulnerabilities, hardware backdoors, and intentional network obfuscation mechanisms will remain entirely hidden from military evaluators.7
The Centralized Distribution Risk: Lessons from the 1001 Firmware Attack
The fundamental reliance on commercial software distribution models represents a critical, often-ignored vulnerability, particularly acute during geopolitical crises. Commercial drones require continuous firmware updates to maintain optimal operability, update geographic no-fly zones, and patch emerging vulnerabilities. In the civilian sector, these updates are pushed over the air via centralized, vendor-controlled cloud servers.3
The immense strategic risk of this centralized architecture was recently demonstrated in the ongoing Ukraine conflict. Russian developers created a highly specialized custom firmware, known internally as “1001,” specifically designed to repurpose civilian DJI drones for active military use by removing manufacturer-imposed flight limits, improving resistance to GPS spoofing, and enabling the utilization of high-capacity batteries.3 Because this highly specialized software could not be publicly downloaded without drawing attention or manufacturer intervention, it was distributed through a clandestine network of drone service centers.3 These centers utilized pre-configured laptops, referred to as “terminals,” which securely connected to a remote central server to receive the firmware packages.3
However, unidentified hackers successfully targeted and breached the remote servers responsible for delivering these critical updates.3 The perpetrators displayed false messages on the terminals used by the operators and subsequently disabled the entire firmware distribution system.3 While the developers claimed the firmware itself was not compromised with malicious code, the cyberattack successfully paralyzed the supply chain.3 Without functioning terminals connecting to the central infrastructure, the Russian military was entirely unable to “reflash” or update newly procured commercial drones for battlefield deployment, significantly limiting their operational capacity.3
This incident underscores the severe operational risk of integrating COTS systems that inherently require “phoning home” to commercial servers. Military architectures demand localized, fully air-gapped updating mechanisms. If the United States relies on commercial ecosystems that mandate internet connectivity for authentication or updates, an adversary can simply sever the update pipeline, effectively grounding the fleet without firing a single kinetic shot.
4. Environmental Fragility and the Discrepancy in Survivability Standards
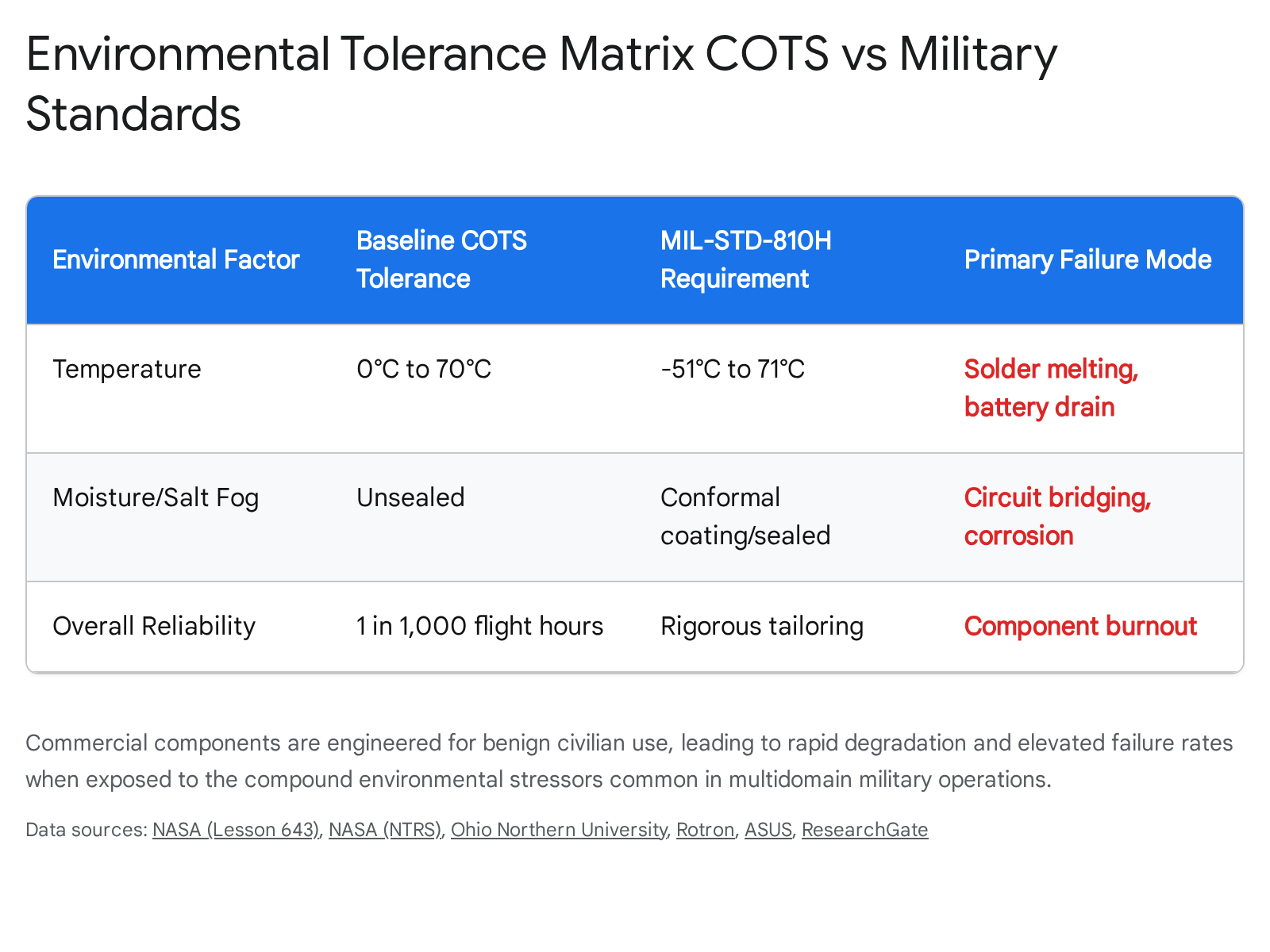
A fundamental and frequently catastrophic divergence between commercial technology integration and strict military requirements lies in environmental survivability. While the Department of Defense requires systems capable of reliably executing missions across every extreme climatic zone on Earth—from arctic tundras to humid maritime environments—commercial drone components are engineered strictly to maximize profit margins for benign, predictable civilian use cases.
The Chasm Between Commercial Specifications and MIL-STD-810H
The vast majority of COTS electronic components are rated for optimal operation only within a narrow temperature band, typically between 0 °C and 70 °C.8 These commercial parts face severe, highly predictable limitations when forced into extended temperature ranges due to the rapid degradation of the constituent materials utilized in their low-cost manufacturing.8 Conversely, purpose-built military hardware must adhere to the rigorous, highly structured testing methodologies outlined in defense standards such as MIL-STD-810H for whole systems, and MIL-STD-202 for individual electronic components (such as resistors, capacitors, and switches).9
Unlike commercial standards that often rely on fixed, generic testing procedures with set parameters, MIL-STD-810H requires a comprehensive assessment of the critical environmental profiles a system is likely to encounter throughout its entire life cycle.12 This encompasses both logistical transport and violent tactical deployment.12 This rigorous management and engineering process, known as tailoring, ensures that a component designed for a high-altitude aircraft is subjected to an entirely different stress profile than a component destined for a highly humid, shipboard maritime application.12
When COTS electronics are forced into military environments without comprehensive structural and electrical hardening, the results are routinely catastrophic. Unmanned aerial vehicles inherently experience a baseline failure rate of approximately 1 in 1,000 flight hours—a staggering rate that is two full orders of magnitude higher than commercial manned aircraft, which fail at a rate of roughly 1 in 100,000 flight hours.13 High failure rates in UAS are frequently and directly linked to deficiencies in preoperational testing and the rapid, expected deterioration of consumer-grade materials under military stress profiles.13
Compounding Stressors: Temperature, Outgassing, and Salt Fog
The combination of specific environmental factors in military operations exponentially accelerates component failure in unhardened COTS drones.14
- Extreme Temperature and Outgassing: High ambient temperatures impose severe, often immediate stress on COTS electronics, frequently causing catastrophic failures such as the physical melting of low-grade solder joints and the thermal burnout of solid-state devices.14 Furthermore, as operational altitudes increase and atmospheric pressure decreases, the outgassing of material constituents (the release of trapped gases in plastics and adhesives) increases significantly.14 Elevated temperatures highly intensify this outgassing effect, causing adjacent components to degrade, short out, or lose structural integrity.14 High temperatures also vastly increase the rate of moisture penetration into poorly sealed commercial airframes.14
- Cold Weather Degradation and Spray Drift: Conversely, extreme cold weather drastically reduces the chemical efficiency of the commercial lithium-ion power systems utilized in consumer drones. Studies indicate that cold conditions can degrade battery efficiency by up to 40%, leading to highly unpredictable flight times, severely reduced payload capacities, and unexpected mission failure mid-flight.15 Furthermore, operational variables such as wind speed drastically affect performance; crosswinds or headwinds significantly increase the battery load as the drone fights to maintain stability, severely reducing operational precision.15
- Salt Fog and Corrosion: Operations in maritime, littoral, or coastal environments expose drones to a highly destructive element: salt fog.16 Salt fog is a corrosive mist composed of airborne salt particles that easily penetrate the unsealed internal compartments of a COTS drone, settling on motors, printed circuit boards (PCBs), and delicate metal components.16 When these salt particles inevitably combine with ambient moisture, they become highly corrosive, rapidly eating away at circuit connections and motor terminals.16 Over time, as salt accumulates, it literally bridges the microscopic gaps in commercial circuitry, creating unintended electrical paths that cause immediate short circuits, unpredictable performance issues, and complete, unrecoverable system failures.16
To achieve the necessary resilience required by the DoD, military systems require the integration of advanced thermal control elements, thick conformal coating of all internal printed circuit boards, and the application of specialized shielding materials.8 While novel, cutting-edge approaches—such as the integration of Negative Index Materials (NIM) designed to disperse microwave energy and robust structural shielding to combat electromagnetic interference (EMI)—can mitigate environmental degradation, these essential modifications add significant physical mass and extreme financial cost to the platform.17 Leadership must clearly recognize that procuring an inexpensive COTS airframe represents only the initial, baseline cost; the subsequent specialized engineering required to actually ruggedize the system to military standards frequently negates the initial financial advantage entirely.18
5. The Technology Integration Gap: Shattering Software Stovepipes
The Department of Defense currently faces a profound integration gap that threatens to undermine its massive investments in autonomous systems. Historically, strategists have warned of capability deficits relative to adversaries—such as the bomber gap of the 1950s or the missile gap of the 1960s.19 Today, however, the primary risk is not necessarily a deficit in the physical capabilities the joint force possesses, but rather a persistent, systemic failure to connect the advanced capabilities it already owns.19 As billions of dollars are aggressively invested in commercial drone technology, the hardware is arriving at the tactical edge, but the software architecture required to intelligently integrate these disparate systems remains firmly stuck in antiquated, siloed paradigms.19
Fragmented Standards and the Limitations of Legacy Formats
Warfighters require fielded, sustained, and highly integrated combat capability, not isolated science projects.19 The integration of civilian technology into multidomain military operations is severely hindered by fragmented technical standards stored across disparate, unconnected organizational repositories.19 Currently, critical data models and interface specifications are scattered across platforms such as git.mil, TAK.gov, and STITCHES, each possessing entirely different classification domains, authentication protocols, and access requirements.19
Furthermore, historically, the DoD has published official interoperability standards in non-machine-readable formats, such as PDF documents housed in the Defense Logistics Agency’s ASSIST database.19 While PDF documents are human-friendly, they are entirely useless to automated systems. In an era where AI-accelerated decision-making dictates the pace of battle, publishing complex technical standards in formats that machines cannot natively ingest severely cripples the speed of integration, forcing human engineers into a perpetual state of manual translation.19 A true modular open systems approach acts as a strategic deterrent in itself; a force capable of reconfiguring, integrating, and adapting software architectures faster than an adversary can target them holds a decisive advantage.19 However, systems that cannot natively interoperate succumb to the negative implications of Metcalfe’s Law, where isolated nodes actually reduce the return on investment of every other system within the network.19
Foundational Technologies for Joint Integration
To bridge this critical integration gap and properly support the realization of the Joint Warfighting Concept and Joint All-Domain Command and Control (JADC2) initiatives, the military must aggressively transition to machine-readable formats (such as protocol buffers, JSON, and XML schemas) and implement three foundational architectural technologies.19
| Foundational Technology | Operational Function | Integration Mechanism |
| Ontology Management | Serves as a shared, universal vocabulary for machines across the joint force. | Solves complex entity, relationship, and hierarchy resolution problems at massive scale. Ensures that optical sensor data generated by a commercial drone is natively understood by an artillery targeting system without manual translation. Key initiatives include the Maven Smart System and Next Generation Command and Control.19 |
| Conflict-Free Replicated Data Types (CRDTs) | Enables decentralized data synchronization in degraded environments. | Commercial drones expect continuous, high-bandwidth connections. In combat, connectivity is routinely severed. CRDTs (utilized in systems like Anduril Edge Data Mesh or Ditto) allow for the efficient, mathematically guaranteed distribution of data across tactical edge devices during intermittent connectivity, synchronizing intelligence once networks are restored.19 |
| Zero-Trust Network Architecture | Provides the essential security wrapper for vulnerable commercial nodes. | Treats every COTS device as inherently untrusted. Mandates continuous authentication and strict policy-based access control before permitting sensitive sensor-to-shooter data flows, ensuring that compromised commercial drones cannot map or infect the broader network.19 |
Without the immediate establishment of a unified code repository and a canonical, universally adopted data model registry, the rapid proliferation of COTS drones will simply result in thousands of uncoordinated, highly vulnerable sensors operating in isolation.
6. Geopolitical Supply Chain Dependencies and Material Chokepoints
Perhaps the most critical systemic oversight regarding the mass integration of COTS drone technology is the DoD’s profound reliance on underlying supply chains that are overwhelmingly controlled by geopolitical adversaries. Policymakers and military leaders have a deeply ingrained tendency to focus almost exclusively on higher-order hardware and software components—such as airframes, autonomy algorithms, and AI targeting—while entirely missing the underlying chemistry and metallurgy required to build them.21 The ability to sustain the mass production of unmanned systems during a protracted conflict requires unhindered, continuous access to highly specialized composites, alloys, and semiconductors.21 Over the past two decades, the United States and its key allies have systematically shed massive capacity in the mining, refining, and manufacturing sectors, resulting in a domestic defense industrial base that is now deeply entangled with, and reliant upon, adversarial ecosystems.21
The Metallurgy and Chemistry of Drone Warfare
Almost every modern drone utilized in contemporary conflicts, from palm-sized quadcopters guiding artillery to sophisticated long-range loitering munitions, depends heavily on raw materials and sub-components originating in Chinese factories and refineries.21 This extreme material dependency translates into several highly fragile strategic chokepoints:
- Structural Materials: The skeletal foundation of most advanced unmanned aircraft relies heavily on aerospace-grade carbon fiber.21 While the raw precursor materials are produced in multiple nations including the US and Japan, the highly specialized advanced autoclave facilities and finishing capacities required for aerospace applications remain highly concentrated.21 A targeted disruption in this single node cannot be surged quickly, resulting in the immediate halting of production lines across multiple distinct aircraft programs.21
- Propulsion: The fundamental ability of a drone to turn electrical current into physical lift relies entirely on Neodymium-iron-boron (NdFeB) magnets.21 Currently, China processes and finishes an estimated 90% of the world’s entire sintered-magnet output.21 Even if allied nations successfully open new rare-earth oxide mines, the immense environmental and capital costs associated with the magnetization and finishing processes—which pushed these industries offshore two decades ago—keep the true chokepoint firmly anchored within Chinese borders.21
- Power and Sensors: High-capacity batteries are essential for flight endurance. China currently refines roughly two-thirds of the world’s lithium and processes over 70% of its critical graphite anode material.21 Furthermore, the specialized drone optics, thermal imaging, and high-frequency communications equipment rely fundamentally on specialty semiconductors, including gallium-nitride power amplifiers and highly sensitive infrared detectors (manufactured from indium antimonide and mercury cadmium telluride).21 These specific components are produced in only a small handful of Western fabrication facilities, which require years to expand and are currently entirely unable to absorb severe export shocks.21
Beijing has increasingly demonstrated both the capability and the willingness to utilize these supply chains as a primary strategic lever, imposing global export controls on defense-related minerals—such as the 2023 restrictions on graphite—to deliberately disrupt assembly lines and constrain allied manufacturing capabilities within weeks.21 Industrial resilience must now be considered perfectly equivalent to combat power; drone warfare scales entirely through manufacturing capacity built on secure material inputs, not through conceptual innovation alone.21
Policy Responses: The American Security Drone Act and OMB Directives
Recognizing that an absolute reliance on foreign-manufactured systems critically undermines domestic technological sovereignty and leaves the government permanently exposed to hard-to-detect embedded surveillance capabilities, the U.S. government has initiated sweeping legislative and policy changes.23 Driven by the mandates of the American Security Drone Act (ASDA) of 2023, the Office of Management and Budget (OMB) issued Memorandum M-26-02, which establishes strict, comprehensive, government-wide requirements for UAS procurement and operations.23
Under these new directives, federal agencies are legally mandated to recognize UAS not merely as aircraft, but as highly sensitive Information Technology (IT) systems deeply integrated into federal networks.23 The policy requires agencies to conduct joint impact assessments utilizing Federal Information Processing Standard (FIPS) 199 prior to any procurement, mandating the implementation of strict access controls such as multifactor authentication (MFA) per NIST SP 800-63, and ensuring that all mission-related data is heavily encrypted both at rest and during transmittal.23
Crucially, the memorandum establishes a hard deadline: on or after December 22, 2025, federal funds—including grants provided to non-federal entities—are strictly prohibited from being utilized to procure or operate any UAS from sources classified as “FASC-prohibited” (Federal Acquisition Security Council prohibited foreign adversaries).23 Strict exemptions exist solely for specific national security operations, electronic warfare training, and critical research, provided the drone is physically modified to ensure it is rendered entirely incapable of transferring data to adversarial entities.23
While these isolationist policies are undoubtedly essential for long-term national security, the stark reality is that the domestic US drone industry currently produces only a tiny fraction of the output generated by Chinese companies. Currently, Chinese market leader DJI dominates an estimated 70% to 90% of the global civilian and commercial market, exporting approximately four million units annually compared to domestic U.S. production of barely 100,000.22 Transitioning the DoD away from foreign COTS hardware will require massive, sustained domestic investment to overcome these deeply entrenched material chokepoints and build a resilient industrial base.
7. Redefining Sustainment: The Attrition Cycle and Advanced Manufacturing
The traditional Department of Defense acquisition and sustainment model—long characterized by multi-year development cycles, rigid Programs of Record (PoR), and the sluggish “waterfall” approach to software engineering—is fundamentally incompatible with the harsh realities of modern COTS drone warfare.27 To maintain lucrative contracts, legacy prime defense contractors frequently exploit their deep understanding of military requirements built over decades, resisting the adoption of the highly agile, rapid development models necessary for modern software integration.28
The Compressed Innovation Cycle
Observations from the brutal conflict in Ukraine indicate that the innovation cycle for battlefield robotics has compressed from years down to approximately three months.29 In this hyper-accelerated environment, tens of thousands of highly disposable, low-cost First-Person-View (FPV) drones are deployed monthly by the Ukrainian Unmanned Systems Forces.29 Tactical adaptations—such as the rapid transition from highly vulnerable radio-linked drones to advanced fiber-optic-tethered variants that physically bypass Russian electronic jamming, or the integration of GPS-free navigation and AI-assisted autonomous targeting—move from initial prototype to mass field deployment at a pace mimicking commercial software releases rather than traditional defense procurement.29
Ukraine achieved this unprecedented rapid iteration by creating direct, digital feedback loops seamlessly connecting frontline warfighters with domestic manufacturers.32 Systems like Army+ and DOT-Chain have redefined the individual soldier as a co-developer, fundamentally shifting the paradigm from centralized, bureaucratic procurement to decentralized, highly agile iteration.32 Peacetime militaries are traditionally structured to build vast, static stockpiles of exquisite hardware over decades. However, in modern conflicts where equipment is attrited at an extraordinary rate, sustaining operations requires the organizational capacity to continually redesign, upgrade, and mass-manufacture components directly in response to enemy technological adaptations.29
Transforming in Contact 2.0 and Tactical Edge Manufacturing
The United States Army’s “Transforming in Contact (TiC) 2.0” initiative acknowledges this monumental shift, aggressively pushing for the dynamic field-testing of COTS drones and loitering munitions directly within brigade combat teams and other combat formations.5 Units are currently testing highly vetted commercial systems, such as the Neros Archer (a high-performance FPV drone optimized for long-range missions and EW resistance) and the PDW C100 Multi-Mission Platform (a portable system explicitly designed for universal payload integration with a munitions-release device, which is actively setting the standard for DoD drone munitions).5
A critical strategic output of this initiative is the stark realization that ordnance and sustainment units must fundamentally adapt to support a highly responsive, in-theater drone munitions supply chain.5 Currently, safely pairing fragile commercial drones with lethal munitions requires rigorous safety features, such as critical arming mechanisms to prevent accidental detonation during handling, and highly specialized directional-dropping kits to ensure munitions achieve desired impact angles and reduce dispersion.5
Learning directly from the clandestine production facilities utilized by the Ukrainian military—which salvage damaged or unserviceable conventional ammunition and missiles to create bespoke drone munitions—the DoD is recognizing the massive strategic potential of utilizing advanced manufacturing at the tactical edge.5 By equipping brigade ammunition transfer points and echelon-above-brigade ordnance companies with robust 3D printers, specialized training, and certified digital design files from the defense industrial base, ordnance units can salvage unserviceable traditional ammunition.5 They can modify this ordnance with 3D-printed components and rapidly supply frontline forces with COTS-compatible munitions.5 This revolutionary approach shifts the sustainment burden away from relying on highly vulnerable, slow trans-oceanic shipping, replacing it with resilient, localized manufacturing capability that does not draw down standard strategic combat loads.5
8. Securing the Commercial Pipeline: From Silicon to Software
To safely leverage the immense speed, scalability, and affordability of commercial technology, the Department of Defense must enforce stringent, continuous validation and hardening mechanisms across both the software and hardware supply chains. The era of accepting “black box” commercial products based solely on superficial vendor attestations is permanently over.34
The Blue UAS Framework and Zero Trust Architecture
The Defense Innovation Unit (DIU) established the Blue UAS program to create a highly streamlined, DoD-wide procurement pathway explicitly for trusted commercial drone technology.35 Platforms and components that are selected for the Blue UAS Cleared List (which is currently transitioning to the oversight of the Defense Contract Management Agency) undergo extraordinarily thorough, multi-stage evaluations.35 These intensive assessments ensure strict, verified compliance with National Defense Authorization Act (NDAA) Section 848 supply chain mandates, utilizing rigorous supply chain audits to verify that no critical system components originate from prohibited nations (including China, Russia, Iran, and North Korea).35 Furthermore, the systems are subjected to intensive, ongoing cybersecurity penetration testing, which deeply evaluates all system interfaces as potential entry points, scrutinizes API security and access controls, and validates the implementation of data encryption both at rest and in transit.23
Central to securing these highly vulnerable commercial pipelines is the mandatory implementation of Zero Trust Architecture (ZTA) for the entire UAS fleet.20 The Zero Trust framework strictly mandates the physical or logical segmentation of networks to prevent potential breaches from spreading to the broader enterprise network, and requires that every single software component and data exchange is continuously verified and authenticated.20
Software Bills of Materials (SBOM) and Supply Chain Transparency
A critical, highly effective forcing function for achieving necessary software transparency is the strict enforcement of the Software Bill of Materials (SBOM).34 As explicitly directed by OMB Memorandum M-26-05, federal agencies are rapidly transitioning away from manual compliance spreadsheets, empowering leadership to demand raw, dynamic, machine-readable SBOM data (utilizing rigorous modern standards such as CycloneDX and SPDX).34 An SBOM provides a comprehensive, formal, nested inventory detailing the exact provenance and integrity of every single third-party and open-source software component embedded within a product.34
Adversaries frequently target the software supply chain by covertly inserting malicious code into widely used, seemingly innocuous commercial libraries. Notable historical examples include the scalable exploitations of 3CX, the MOVEit managed file transfer application, and the discovery of Pushwoosh—a Russian-rooted technology embedded in thousands of applications utilized by the US Army and the CDC to collect precise user geolocation data.39 Without deep, machine-readable visibility into the code provenance, the DoD risks deploying COTS drones that harbor latent, catastrophic vulnerabilities, such as unauthorized geolocation tracking or covert data exfiltration routines back to foreign servers.20 Continuous, automated monitoring of SBOMs transforms an opaque operational risk into a quantifiable, manageable asset, ensuring that vulnerabilities are identified and neutralized before the system is fielded.34
Hardware Validation and Physical Unclonable Functions (PUF)
Securing the software layer is entirely insufficient if the underlying commercial silicon is inherently compromised. The global semiconductor supply chain is highly vulnerable to the insertion of Hardware Trojans and sophisticated side-channel analysis—semi-intrusive attacks that exploit physical leakages, such as minute variations in power consumption or electromagnetic radiation, to extract sensitive cryptographic keys.41 If counterfeit or maliciously altered chips are integrated into critical military hardware, they can subtly alter system behavior or covertly leak sensitive operational data directly to unauthorized parties.43
To effectively mitigate these intrusive and semi-intrusive hardware threats, commercial silicon must be validated at the microscopic level using Physical Unclonable Functions (PUFs).42 A PUF leverages the inevitable, microscopic, random physical variations that occur during the semiconductor manufacturing process to generate a highly unique, intrinsic digital “fingerprint” for every single microchip.42 Because these physical characteristics cannot be cloned, replicated, or accurately predicted by an adversary, the PUF serves as an irrefutable, tamper-proof Root of Trust (RoT) for the device.42 By requiring PUF-based challenge-response authentication mechanisms within all COTS components, the DoD can cryptographically verify the true origin and absolute integrity of a drone’s hardware, permanently preventing unauthorized, cloned, or altered devices from connecting to secure military networks.42
9. Strategic Conclusions and Policy Recommendations
The widespread integration of Commercial Off-The-Shelf drone technology is not merely a tactical procurement strategy; it represents a fundamental, structural shift in how the modern military builds, sustains, and scales lethal combat power. However, the prevailing premise that the Department of Defense can simply purchase its way to strategic dominance via commercial civilian retailers is a highly dangerous fallacy. Commercial drones undeniably speed up acquisition, but without rigorous, systemic hardware and software hardening, they introduce unmanageable, catastrophic vulnerabilities directly at the tactical edge.
To successfully enable warfighters to operate safely in contested environments, defense leadership must prioritize the following strategic imperatives:
- Enforce Absolute Architectural Transparency: Leadership must unequivocally mandate the use of automated, machine-readable SBOMs and PUF-based hardware authentication for all commercial systems entering the defense ecosystem. Opaque commercial software and unverified foreign silicon represent unacceptable operational risks that directly threaten force protection.
- Decouple from Centralized Commercial Infrastructure: Military platforms must never rely on commercial, cloud-based APIs or centralized internet servers for telemetry, mapping, or firmware updates. As demonstrated by the disruption of Russian 1001 firmware, all COTS systems must be capable of operating on fully air-gapped networks with localized, highly secure update mechanisms to prevent supply chain paralysis during advanced cyber warfare.
- Modernize the Sustainment Paradigm at the Tactical Edge: The ability to field effective drone forces relies entirely on matching the adversary’s highly compressed innovation cycle. The DoD must rapidly transition from hoarding massive, static hardware stockpiles to investing in dynamic, in-theater advanced manufacturing capabilities. By equipping ordnance units with 3D printing technology and establishing universal payload integration standards, the joint force can adapt commercial hardware and munitions at the speed of conflict.
- Invest in Domestic Material Resiliency: While software and system architecture can be secured internally through rigorous Zero Trust frameworks, the absolute physical dependency on adversarial nations for aerospace-grade carbon fiber, specialty semiconductors, and rare-earth magnets remains a critical, overarching strategic threat. Continued, aggressive legislative support for domestic extraction, specialized refining, and advanced manufacturing is paramount to ensuring the physical availability of drone technology in future conflicts.
The battlefield utility and economic advantages of COTS technology are undeniable, but realizing this potential requires a highly sophisticated engineering translation from civilian convenience to rugged military survivability. By directly addressing the overlooked systemic requirements necessary to secure, harden, and evolve these commercial architectures, the Department of Defense can harness the rapid, iterative innovation of the commercial sector without compromising the security and lethality of the joint force.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Sources Used
- Short Bursts – Curran – COTS drones – Canada.ca, accessed April 24, 2026, https://www.canada.ca/en/army/services/canadian-army-journal/articles/2025/short-bursts-curran-cots-drones.html
- COTS Drones: Impact, Threats, and Drone Mitigation Techniques – D-Fend Solutions, accessed April 24, 2026, https://d-fendsolutions.com/blog/cots-drones-impact-and-drone-mitigation-techniques/
- Cyberattack deals blow to Russian firmware used to repurpose …, accessed April 24, 2026, https://therecord.media/cyberattack-russia-firmware-blow-hackers
- CHIPS Articles: Department Guidance on Procurement and Operation of DoD Unmanned Aircraft Systems – doncio.navy.mil, accessed April 24, 2026, https://www.doncio.navy.mil/chips/ArticleDetails.aspx?ID=15068
- Transforming in Contact 2.0: Drone Munitions Sustainment | Article …, accessed April 24, 2026, https://www.army.mil/article/286568/transforming_in_contact_2_0_drone_munitions_sustainment
- Drone Security and the Mysterious Case of DJI’s DroneID – NDSS …, accessed April 24, 2026, https://www.ndss-symposium.org/wp-content/uploads/2023/02/ndss2023_f217_paper.pdf
- The Digital Battlefield: Safeguarding Military Drones Against Cyberattacks – Digital Commons @ USF – University of South Florida, accessed April 24, 2026, https://digitalcommons.usf.edu/cgi/viewcontent.cgi?article=1129&context=mca
- Evaluation of COTS Electronic Parts for Extreme Temperature Use in NASA Missions, accessed April 24, 2026, https://ntrs.nasa.gov/api/citations/20090004581/downloads/20090004581.pdf
- Military Standard (MIL-STD 810) – Introduction | Official Support | ASUS Global, accessed April 24, 2026, https://www.asus.com/support/faq/1050608/
- DEPARTMENT OF DEFENSE TEST METHOD STANDARD ENVIRONMENTAL ENGINEERING CONSIDERATIONS AND LABORATORY TESTS – Systel, accessed April 24, 2026, https://systelusa.com/wp-content/uploads/2022/08/MIL-STD-810H-Specification.pdf
- Environmental and Shock Testing Standards for Military Equipment – Defense Advancement, accessed April 24, 2026, https://www.defenseadvancement.com/resources/environmental-shock-testing-standards/
- COTS for Military Applications MIL-STD-810 – CVG Strategy, accessed April 24, 2026, https://cvgstrategy.com/cots-for-military-applications/
- Comparison between the reliability of a commercial and a military drone. – ResearchGate, accessed April 24, 2026, https://www.researchgate.net/figure/Comparison-between-the-reliability-of-a-commercial-and-a-military-drone_tbl1_327758171
- NASA Preferred Reliability Practices; Design and Test Practices for Aerospace Systems; Environmental Factors – NASA Lessons Learned database, accessed April 24, 2026, https://llis.nasa.gov/lesson/643
- Minimizing Drift and Streaking with the Use of Application Drones – DigitalCommons@ONU, accessed April 24, 2026, https://digitalcommons.onu.edu/eng_student_research_colloquium/2025/Presentations/16/
- Surviving Salt Fog in Naval Environments | AMETEK Rotron Aerospace & Defense Blog, accessed April 24, 2026, https://www.rotron.com/tech-corn/blog/salt-fog
- Hardening Unmanned Aerial Systems Against High Power … – DTIC, accessed April 24, 2026, https://apps.dtic.mil/sti/tr/pdf/AD1042082.pdf
- Cots Do 254 Safety Certifiable Avionics Hardware Lowers Cost Reduces Risk, accessed April 24, 2026, https://defense-solutions.curtisswright.com/media-center/articles/cots-do-254-safety-certifiable-avionics-hardware-lowers-cost-reduces-risk
- Shattering the Software Stovepipes: How to Close the US Military’s …, accessed April 24, 2026, https://mwi.westpoint.edu/shattering-the-software-stovepipes-how-to-close-the-us-militarys-technology-integration-gap/
- Cybersecurity Guidance: Chinese-Manufactured UAS – IC3, accessed April 24, 2026, https://www.ic3.gov/CSA/2024/240118.pdf
- The Drone Supply Chain War: Identifying the Chokepoints to Making …, accessed April 24, 2026, https://www.csis.org/analysis/drone-supply-chain-war-identifying-chokepoints-making-drone
- US drone manufacturers accelerate domestic supply chain development after China ban, accessed April 24, 2026, https://www.agenzianova.com/en/news/US-drone-manufacturers-accelerate-domestic-supply-chain-development-after-China-ban/
- M-26-02 Ensuring Government Use of Secure … – The White House, accessed April 24, 2026, https://www.whitehouse.gov/wp-content/uploads/2025/11/M-26-02-Ensuring-Government-Use-of-Secure-Unmanned-Aircraft-Systems-and-Supporting-United-States-Producers.pdf
- Drones and the Federal Government: What Contractors Need to Know About the Latest OMB Guidance | Insights | Holland & Knight, accessed April 24, 2026, https://www.hklaw.com/en/insights/publications/2025/12/drones-and-the-federal-government-what-contractors-need-to-know
- Regulatory Changes to Foster US Drone Supply Chains – Capstone DC, accessed April 24, 2026, https://capstonedc.com/insights/regulatory-changes-to-foster-us-drone-supply-chains/
- A global strategy to secure UAS supply chains – Atlantic Council, accessed April 24, 2026, https://www.atlanticcouncil.org/in-depth-research-reports/issue-brief/a-global-strategy-to-secure-uas-supply-chains/
- CHIPS Articles: COTS-Based Systems: Keys to Success, accessed April 24, 2026, https://www.doncio.navy.mil/chips/ArticleDetails.aspx?ID=3592
- Machine Failing: How Systems Acquisition and Software Development Flaws Contribute to Military Accidents – Texas National Security Review, accessed April 24, 2026, https://tnsr.org/2024/10/machine-failing-how-systems-acquisition-and-software-development-flaws-contribute-to-military-accidents/
- Ukraine’s Drones Are Killing Russian Soldiers Faster Than Moscow Can Replace Them, accessed April 24, 2026, https://complexdiscovery.com/ukraines-drones-are-killing-russian-soldiers-faster-than-moscow-can-replace-them/
- Why the Army Needs Units Driving Drone Development and How to Do It, accessed April 24, 2026, https://www.armyupress.army.mil/journals/military-review/online-exclusive/2025-ole/drone-development/
- The Future of Drones in Ukraine: A Report from the DIU-Brave1 Warsaw Conference – CSET, accessed April 24, 2026, https://cset.georgetown.edu/article/the-future-of-drones-in-ukraine-a-report-from-the-diu-brave1-warsaw-conference/
- How and Why Ukraine’s Military Is Going Digital – CSIS, accessed April 24, 2026, https://www.csis.org/analysis/how-and-why-ukraines-military-going-digital
- Transforming in Contact 2.0: Drone Munitions Sustainment – Line of Departure – U.S. Army, accessed April 24, 2026, https://www.lineofdeparture.army.mil/Journals/Army-Sustainment/Army-Sustainment-Archive/ASPB-Summer-2025/Transforming-in-Contact-20/
- What is an SBOM and Why Does it Matter for Government Contracts? – Second Front Systems, accessed April 24, 2026, https://www.secondfront.com/resources/blog/what-is-an-sbom-and-why-does-it-matter-for-government-contracts/
- What is Blue UAS? The Ultimate Guide to Secure Drone … – Mobilicom, accessed April 24, 2026, https://mobilicom.com/insight/what-is-blue-uas-the-ultimate-guide-to-secure-drone-compliance/
- Secure Drone Procurement Guidance: Blue UAS and Green UAS – AUVSI, accessed April 24, 2026, https://www.auvsi.org/sites/default/files/UAS-Procurement-Guidance-Memo-2024.pdf
- Blue UAS Refresh List, Framework Platforms and Capabilities Selected, accessed April 24, 2026, https://www.diu.mil/latest/blue-uas-refresh-list-and-framework-platforms-and-capabilities-selected
- UAS solutions for the U.S. DoD. – Defense Innovation Unit, accessed April 24, 2026, https://www.diu.mil/blue-uas
- The New Forcing Function to Sustain our National Security: SBOMs, accessed April 24, 2026, https://www.fortressinfosec.com/blog/the-new-forcing-function-to-sustain-our-national-security-sboms
- Zero Trust for Operational Technology Activities and Outcomes – DoD CIO, accessed April 24, 2026, https://dodcio.defense.gov/Portals/0/Documents/Library/ZT-OperationalTechnologyActivitiesOutcomes_v2.pdf
- A Low-Complexity Security Scheme for Drone Communication Based on PUF and LDPC, accessed April 24, 2026, https://www.mdpi.com/2504-446X/8/9/472
- Securing the IC Supply Chain – Integrating PUF-Based hardware security – PUFsecurity, accessed April 24, 2026, https://www.pufsecurity.com/document/securing-the-ic-supply-chain/
- A Survey of Security in UAVs and FANETs: Issues, Threats, Analysis of Attacks, and Solutions – arXiv, accessed April 24, 2026, https://arxiv.org/html/2306.14281v4
- 5G Hardware Supply Chain Security Through Physical Measurements – NIST Technical Series Publications, accessed April 24, 2026, https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.1278.pdf
- Hardware Implementation-Based Lightweight Privacy- Preserving Authentication Scheme for Internet of Drones Using Physically Unclonable Function – MDPI, accessed April 24, 2026, https://www.mdpi.com/1424-8220/26/7/2224
