Executive Summary
The widespread deployment of first-person view unmanned aerial systems has fundamentally altered the tactical and operational realities of modern warfare. Originally adapted from civilian recreational racing models, first-person view drones have transitioned into highly lethal precision-guided munitions that provide organic close air support to small infantry units. This report provides a detailed analysis of the technological and doctrinal evolutions observed between 2022 and 2026. The analysis tracks the maturation of drone warfare from isolated loitering munition strikes to coordinated systems warfare involving multi-domain unmanned assets.
Significant vulnerabilities in the global hardware supply chain have been exposed, particularly regarding critical dependencies on foreign metallurgy and semiconductor manufacturing. In response, military forces and defense industrial bases have accelerated decentralized manufacturing protocols, utilizing additive manufacturing networks to bypass traditional procurement bottlenecks. Concurrently, the electromagnetic spectrum has become a highly contested domain. To mitigate the effects of advanced electronic warfare, localized software modifications have been engineered to bypass signal jamming, while cutting-edge artificial intelligence and visual inertial odometry facilitate navigation and terminal guidance in environments where satellite navigation is denied.
These technological advancements have catalyzed profound paradigm shifts in global military doctrine. Classical principles of mass maneuver and concentration are collapsing under the persistent surveillance of unmanned aerial systems. Infantry units are being forced to disperse into micro-assault groups to survive. Similarly, the deployment of armored vehicles has been drastically curtailed, requiring tanks to operate several kilometers behind the front lines while engineers race to integrate new active protection systems and counter-drone electronic warfare arrays. The integration of unmanned systems into everyday combat operations represents a systemic transformation in global warfighting strategies.
1.0 Introduction
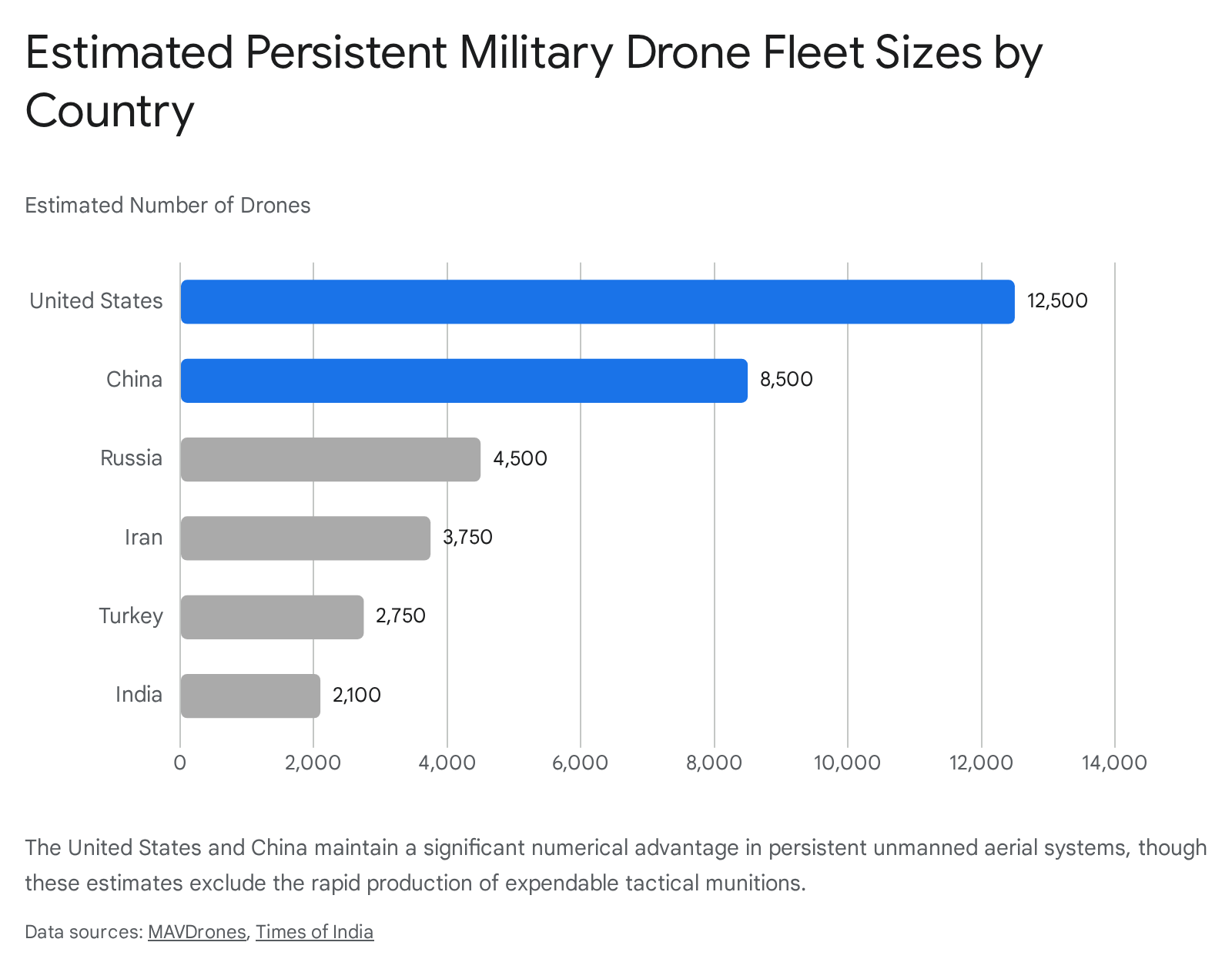
The proliferation of small, low-cost unmanned aerial systems has initiated a structural transformation in land combat. This shift is not merely the introduction of a new tactical tool but represents a foundational change in battlefield dynamics, force structure, and military methodology.1 Unmanned systems across multiple domains have invalidated traditional assumptions regarding airpower, force protection, and the sustainability of armored maneuver.2 By early 2026, the volume of drone deployment reached unprecedented levels, with some nations planning to supply upward of 10 million first-person view drones to frontline units.3 The sheer scale of this deployment has fundamentally altered the geometry of the battlefield.
This volume of deployment has created a highly contested airspace at low altitudes, effectively establishing the air-ground littoral as an independent combat arena that is deeply intertwined with ground operations.1 The current trajectory of drone warfare suggests a shift toward Tactical Network-Centric Warfare, a decentralized operational model that merges precision, autonomy, and information dominance at the lowest tactical echelons.4 The transition from myth to operational reality occurs not over decades, but within weeks, underscoring the compressed timescale of military innovation in high-intensity conflict.2
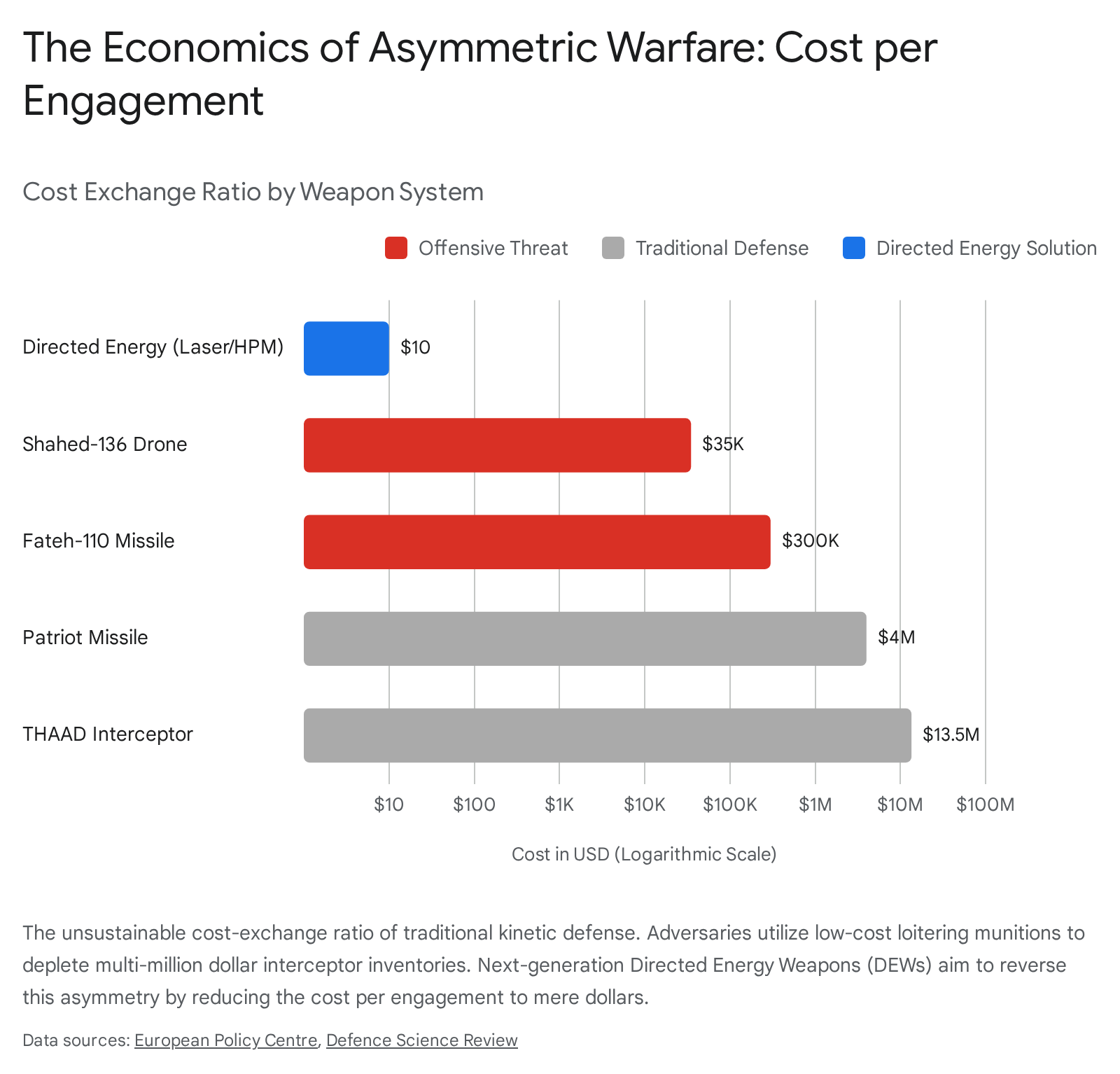
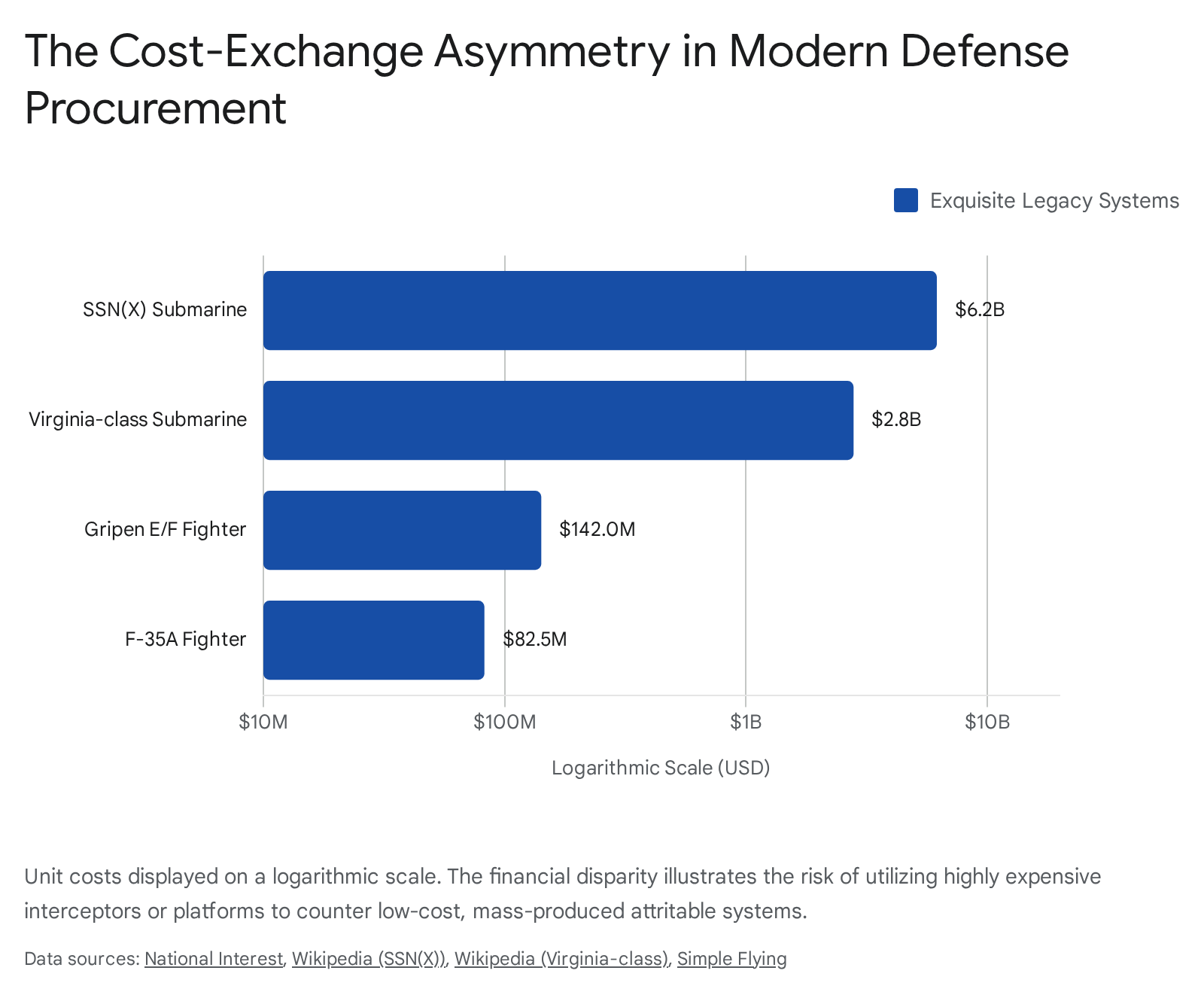
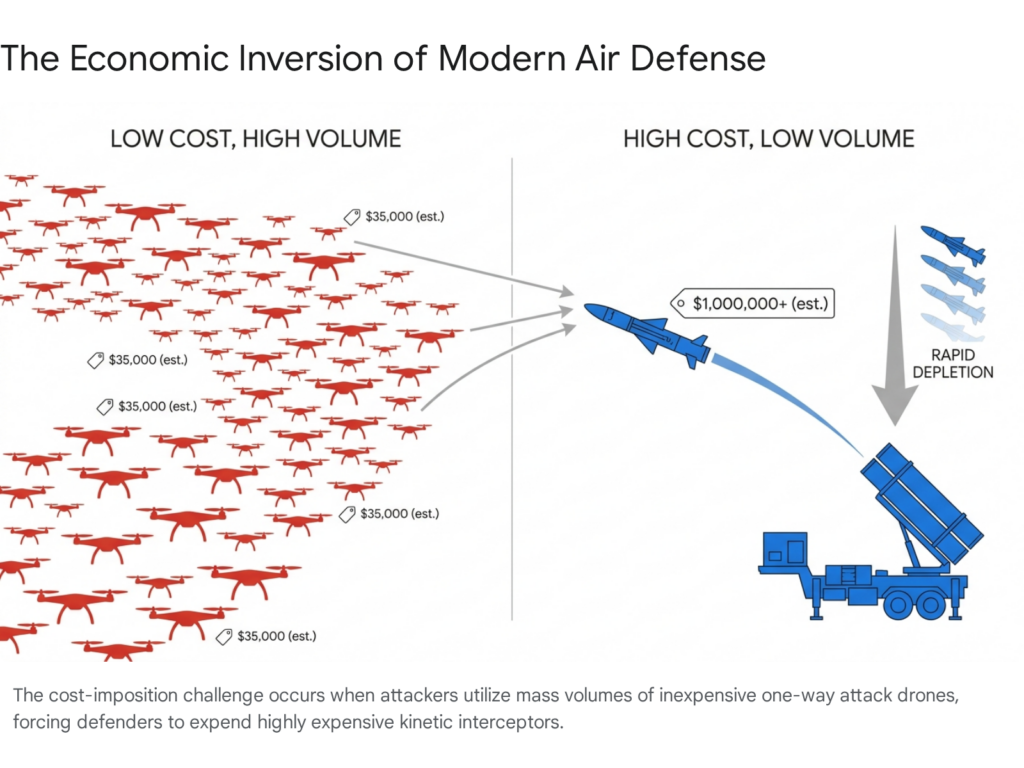
The economics of modern warfare have been shattered by these low-cost systems. A first-person view drone costs roughly $400 to $600 to build and deploy.5 Conversely, an M1 Abrams main battle tank costs approximately $8 million, and a Russian T-90M requires close to $4.5 million to manufacture.6 When a $500 drone routinely destroys a multi-million dollar armored vehicle, the cost-exchange ratio heavily favors the drone operator, forcing militaries to reconsider the financial sustainability of traditional heavy armor.6 The following sections analyze the precise mechanisms of this evolution, focusing on tactical methodologies, hardware supply chain resilience, software adaptations for contested electromagnetic environments, and the subsequent rewrites of infantry and armored doctrines.
2.0 The Evolution of Unmanned Tactical Strike Capabilities
The tactical application of first-person view drones has evolved rapidly from improvised nuisance attacks to synchronized, mass-scale strikes integrated into broader combined arms operations. This evolution is characterized by range extension, the introduction of automated terminal guidance, and the transition toward coordinated systems warfare.
2.1 From Isolated Strikes to Systems Warfare
In the initial phases of recent high-intensity conflicts, first-person view drones were primarily utilized as single-use, line-of-sight precision munitions. Operators targeted isolated infantry positions or light vehicles within a limited radius, often relying on the element of surprise.3 By 2026, this approach evolved into a concept defined as systems warfare.3 Combat operations are now planned with the assumption of persistent unmanned aerial presence.3 Small drones are utilized to adjust artillery fire, disrupt logistics networks, conduct counter-battery operations, and provide direct, organic support to infantry assaults.3 Ukrainian forces, for example, report conducting over 11,000 combat drone missions per day, striking over 150,000 verified targets in a single month.7
A critical development in this phase is the integration of unmanned ground vehicles with aerial platforms. Tactical operations increasingly feature ambush scenarios where unmanned ground vehicles serve as remote launch platforms for first-person view drones, delivering the aerial systems deep into defensive lines before launch.3 This multi-domain integration reduces the risk to human operators while projecting unmanned strike capabilities further into contested territory. The operator’s role is shifting toward that of a tactical manager who selects the target and timing of the attack, oversees a group of drones, and manages the broader deployment scenario rather than controlling every micro-movement of a single aircraft.3
These tactical capabilities have also been weaponized for psychological and cognitive warfare. In areas such as the Nikopol district, drone units have been documented striking civilian infrastructure, markets, and vehicles to restrict movement and instill psychological terror.8 This normalization of drone strikes on non-combatants highlights the easily exportable nature of these tactics, raising significant concerns for global counterterrorism efforts as violent extremist organizations observe and adopt these low-cost precision strike methods.10
2.2 Overcoming Line-of-Sight Limitations, Relays and Motherships
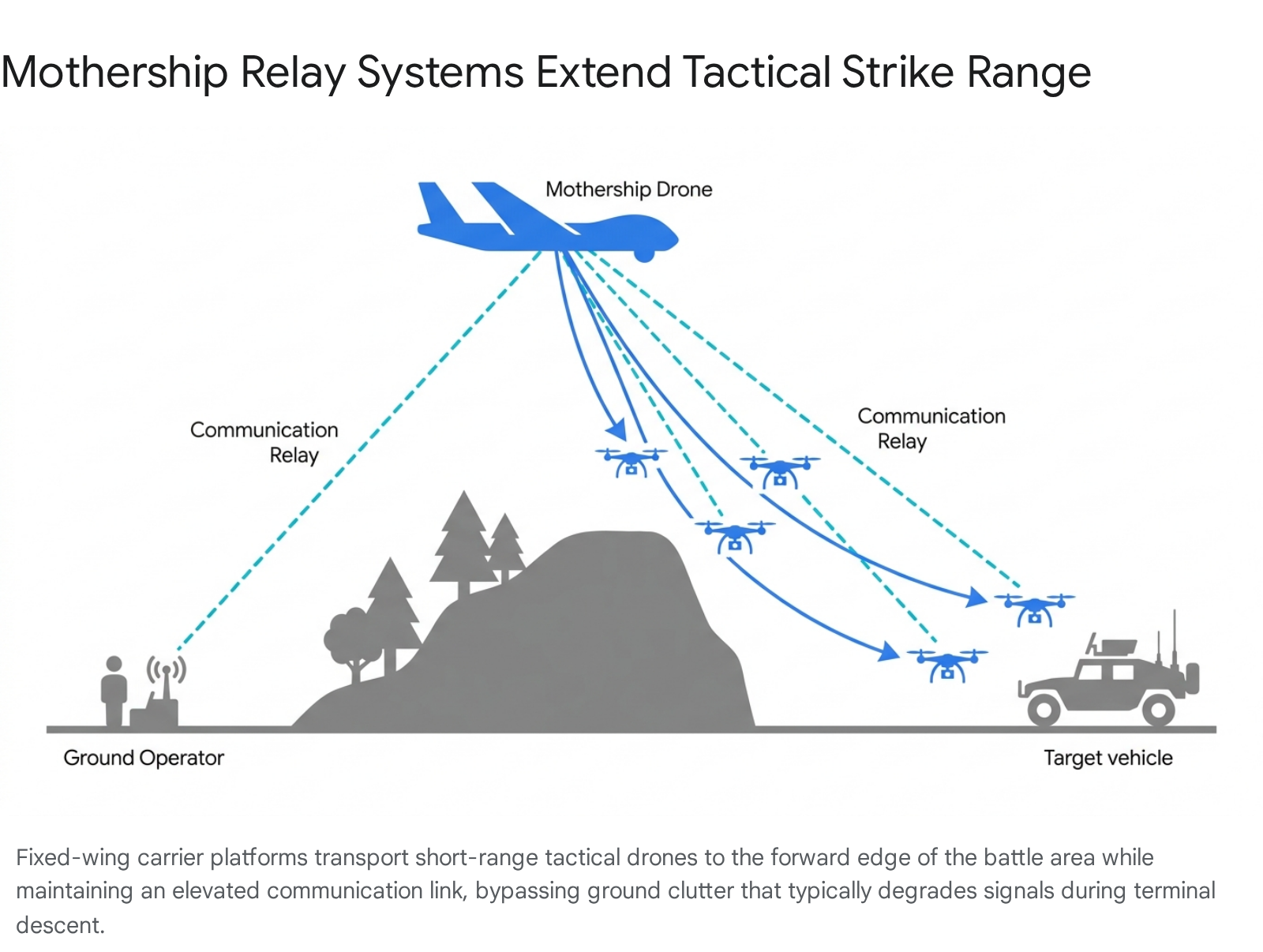
A primary limitation of traditional first-person view drones is their reliance on a continuous radio frequency link between the operator and the aircraft. As these drones drop in altitude during the terminal phase of an attack, ground clutter, foliage, and terrain features frequently obstruct the signal, leading to mission failure and loss of the aircraft.11 To overcome this physical limitation, military engineers have developed and deployed aerial relay systems and mothership drones.
Mothership platforms function as airborne carriers and data-link nodes.11 These larger aircraft, such as the Russian Pchelka or modified Orlan and Molniya fixed-wing drones, transport smaller, battery-limited first-person view drones to the edge of their combat radius before deploying them.11 By loitering at high altitudes, the mothership provides a direct, unobstructed line-of-sight relay between the ground controller and the attacking drone, bypassing terrain interference entirely.11
This relay capability extends the effective strike range to upwards of 60 kilometers, allowing forces to target critical logistics routes, command posts, and staging areas deep in the tactical rear.11 Operation Spiderweb, a coordinated strike operation, demonstrated how deep-penetration drones could successfully strike strategic aviation bases far beyond the immediate front lines, yielding high-value disruption across vast ranges.13 These motherships are considered attritable assets, meaning their cost is low enough that losing them during a mission is an acceptable trade-off for the operational advantages they provide.11
2.3 Fiber-Optic Command Links
In environments saturated by electronic warfare, traditional radio frequency control links are highly vulnerable to jamming and interference. Both sides in modern conflicts deploy advanced jamming techniques that broadcast high-power electromagnetic energy over specific frequency bands to drown out legitimate control signals.14 To ensure absolute control reliability, developers have introduced fiber-optic controlled drones.15
These platforms trail a spool of lightweight, bend-insensitive fiber-optic cable, typically G657A2 single-mode fiber with a diameter of 0.26 mm to 0.45 mm, which physically connects the drone to the operator.16 Because the control signals and high-definition video feeds travel through light pulses within the fiber rather than across the open electromagnetic spectrum, these drones are entirely immune to radio frequency jamming and spoofing.1 Furthermore, the lack of radio emissions prevents adversary electronic intelligence units from detecting the drone’s presence or geolocating the operator’s position via signal triangulation.1
Operational deployments in 2025 and 2026 have demonstrated that fiber-optic drones can maintain stable video feeds and command links at ranges of up to 50 kilometers, giving them operational parity with highly expensive precision-guided artillery munitions such as the M982 Excalibur.15 The attenuation loss of the fiber over these distances is exceptionally low, ensuring high-bandwidth communication is preserved until the moment of impact.16
2.4 Autonomous Swarming and Target Acquisition
The next evolutionary phase involves fully autonomous drone swarms capable of prosecuting targets without continuous human oversight. Russian forces have established the Rubikon Center for Advanced Unmanned Technologies, focusing on artificial intelligence capabilities that allow a single operator to control multiple drones simultaneously.7 By utilizing cruise control modes and autonomous navigation, operators can manage swarms that dynamically adapt to the environment, bypassing GPS jamming and radio interference.12
Western militaries are pursuing similar capabilities. The United States Department of Defense launched the Replicator initiative, aiming to field thousands of autonomous, attritable systems to overcome adversary mass.20 While initial goals faced technical hurdles regarding software integration and command structures, the push toward multi-agent, artificial intelligence-driven swarms remains a critical priority for achieving drone dominance.20 These swarms leverage decentralized swarm intelligence, mirroring biological patterns where individual units communicate with one another to execute complex, coordinated maneuvers without requiring a central ground-based controller.19
3.0 Hardware Supply Chain Vulnerabilities and Improvisations
The rapid scaling of drone warfare has exposed severe vulnerabilities in global military supply chains. The components required to build millions of tactical drones rely heavily on raw materials and manufacturing bases concentrated in specific geopolitical regions, forcing defense sectors to improvise and onshore production.
3.1 Strategic Raw Material Chokepoints
The architecture of modern drone warfare is fundamentally underpinned by specialized chemistry and metallurgy, areas where Western defense industrial bases are dangerously dependent on foreign sources.21 Analysis indicates that the hardware supply chain is constrained by several strategic material chokepoints 21:
First, the production of structural materials relies heavily on composites and specialized alloys. High-strength carbon fiber, essential for lightweight and rigid airframes, requires a polyacrylonitrile precursor.21 Aerospace-grade carbon fiber production cannot be surged quickly and is limited to specific autoclave facilities globally. Furthermore, aluminum-lithium alloys and specialized titanium, such as Ti-6Al-4V, are critical for high-heat zones, fasteners, and landing gear.21
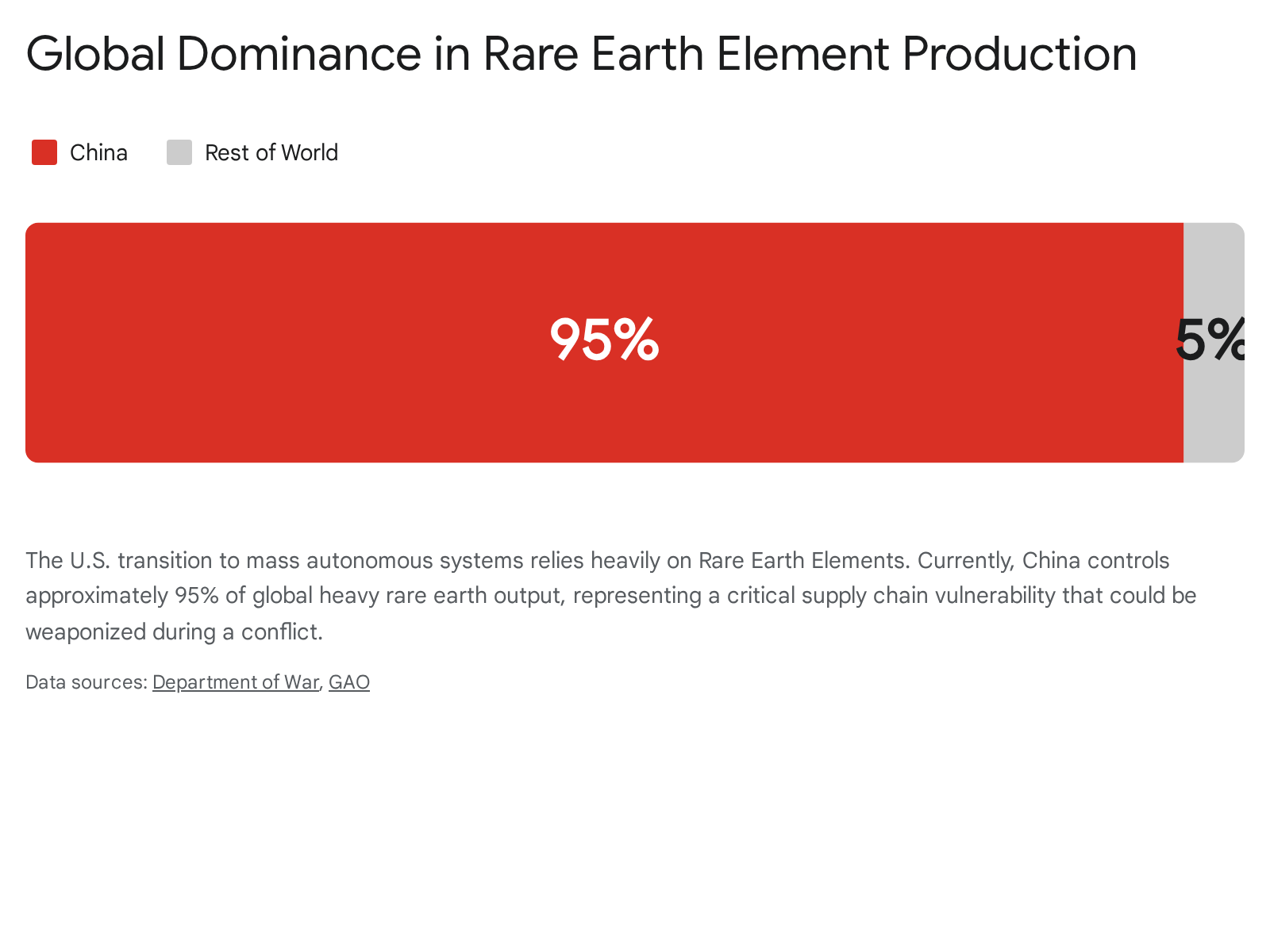
Second, propulsion systems are highly dependent on rare-earth magnets. Neodymium-iron-boron magnets are critical for the lightweight, high-torque brushless motors used in quadcopters.21 Approximately 90 percent of the global output for sintered-magnet processing and magnetization is concentrated in China.21 Even if rare-earth oxides are mined elsewhere, the critical steps of finishing and magnetization represent a severe bottleneck.
Third, power systems rely on specific battery chemistries. The refining capacity for lithium, graphite anode material, nickel, and cobalt presents a heavier bottleneck than the extraction of the raw ores.21 China processes over seventy percent of the world’s graphite anode material, and modest export controls have previously disrupted assembly lines within weeks.21
Fourth, the “brains” and “eyes” of these systems depend on advanced semiconductors. Gallium-Nitride power amplifiers and infrared detectors utilizing indium antimonide are essential for communication arrays and optical sensors.21 The fabrication facilities for these specialty semiconductors require years to expand and cannot easily absorb export shocks or sudden scaling requirements.21 When foreign suppliers impose export restrictions on critical components, the tactical capabilities of reliant nations are immediately degraded, leading to increased costs and severe battlefield attrition.21
3.2 Decentralized Manufacturing and Additive Printing Networks
To circumvent these massive supply chain vulnerabilities, military operators and civilian engineering networks have pioneered decentralized manufacturing protocols. Additive manufacturing, commonly known as 3D printing, has transformed deployed units and civilian basements into localized micro-production hubs.22
By distributing production across hundreds of independent locations, military forces have created resilient supply networks that cannot be disabled by a single strategic strike.23 In Ukraine, volunteer networks utilize consumer-grade fused deposition modeling printers to continuously manufacture airframe components, antenna mounts, and specialized casings that adapt legacy Soviet munitions for aerial delivery.23 These networks operate via secure online marketplaces where military units post specific component requirements, and independent operators fulfill the orders locally.25 Reports indicate that a single 400-operator network successfully produced over 100 tonnes of polymer parts for frontline units.25
This methodology shifts the military logistics model from rigid just-in-time delivery to agile point-of-need sustainment.22 The United States Army’s 173rd Airborne Brigade Hawkeye Platoon demonstrated this capability by assembling quadcopters from 3D-printed parts directly on base, building battlefield-ready drones in roughly four hours.26 This allows forces to rapidly iterate designs based on immediate tactical feedback without waiting for sluggish, multi-year defense procurement cycles.22
3.3 Regulatory Shifts and Domestic Production Initiatives
In the United States, sweeping regulatory changes have accelerated the development of a domestic drone supply chain. Policies such as the National Defense Authorization Act strictly prohibit the use of specific foreign-produced unmanned systems and critical components, driving immense demand for compliant domestic hardware.27 The Federal Communications Commission has actively updated its Covered List to bar foreign-made drones from obtaining the equipment authorizations required for operation in the United States.28
To fill this void, the Department of Defense launched the Drone Dominance Program and the SkyFoundry initiative.29 SkyFoundry, led by the Army Materiel Command, aims to mass-produce 10,000 small drones per month by late 2026 by establishing high-tech manufacturing hubs, such as the proposed facility at the Red River Army Depot in Texas.30 The goal is to strengthen supply chains and manufacturing capacity to a point where military services can affordably procure the necessary volume of attritable systems through regular budgeting.31 Private companies, such as Unusual Machines, have rapidly scaled their operations to meet this demand, increasing daily domestic motor production to over 1,500 parts per day to serve the enterprise and defense markets.32
3.4 Active Component Sourcing and Validation
Despite the push for bespoke military systems, commercial off-the-shelf components remain the backbone of tactical drone assembly. A validation sweep of leading component vendors as of April 2026 confirms the availability of critical parts required for long-range, heavy-lift, and electronic warfare-resilient applications. Table 1 details specific components currently in stock, reflecting the localization of parts that meet rigorous operational standards.
Table 1: Verified FPV Component Stock and Specifications (April 2026)
| Manufacturer | Component Category | Specific Model | Technical Specifications | Price (USD) | Stock Verification | Verified URL |
| iFlight | Cinelifter Motor | XING2 2809 | 1250KV, N52H Curved Arc Magnets, 5mm Titanium Alloy Shaft | $37.99 | In Stock | Product Link |
| iFlight | Heavy-Duty FPV Motor | XING2 2207 | 1750KV / 2050KV / 2750KV variants, 4S-6S Input Voltage | $23.99 | In Stock | Product Link |
| iFlight | Flight Controller | BLITZ H7 Pro | STM32H743 MCU, In-built OSD, compatible with high-draw ESCs | $75.99 | In Stock | Product Link |
| BetaFPV | Radio Receiver | ELRS Micro | 2.4GHz ISM, ESP8285 MCU, PWM or CRSF Output Protocol | $12.99 | In Stock | Product Link |
| Unusual Machines | Domestic Motor Assembly | UMAC NDAA Motors | Scaled to 15,000 units/month, compliant with US defense restrictions | N/A (B2B) | Scaling Production | (https://www.unusualmachines.com/press-release/) |
Data sourced directly from manufacturer inventory systems.32 Certain components feature packing updates, such as the inclusion of heavier M3x10 screws for improved structural integrity during high-torque maneuvers.34
4.0 Localized Software Modifications for GNSS-Denied Environments
The electromagnetic spectrum is constantly contested in modern operations. Electronic warfare units routinely deploy high-power jammers to sever the communication links between operators and drones, and to disrupt Global Navigation Satellite Systems.14 When a drone loses its satellite navigation signal, standard autopilots cannot determine precise location, altitude, or speed, leading to severe drift and eventual mission failure.36
4.1 Adapting Open-Source Firmware to Counter Electronic Warfare
To combat command-link spoofing and broad-spectrum jamming, developers have heavily modified open-source flight software. An overwhelming majority of drones rely on software such as Betaflight to configure flight controllers, and the Express Long Range System to link the radio receiver to the ground station.38 In their standard configuration, these systems operate within fixed frequency ranges dictated by peacetime regulations.38
However, because the source code is openly available, military developers have customized these protocols for combat. One significant adaptation observed in the field is Totalitarian LRS, a highly modified version of the ExpressLRS protocol.38 While standard ExpressLRS utilizes LoRa modulation, Totalitarian LRS expands the frequency-hopping spread spectrum across a significantly wider and unconventional spectrum, ranging from 425 to 970 MHz and 2.2 to 2.7 GHz.38 Furthermore, developers completely rewrote the frequency-hopping algorithm to prevent adversary electronic warfare operators from spoofing the signal or injecting fake data packets into the control stream.38
4.2 Failsafe Disablement and Operational Masking
Complementing the radio link modifications, customized flight controller firmware, known as Totalitarian Betaflight, drastically alters how the drone reacts to signal interference. Standard civilian drones are programmed to execute a strict failsafe protocol, cutting power to the motors and dropping from the sky if the connection to the pilot is lost or if a spoofed disarm command is received.38
In a combat environment where signal loss is guaranteed, this safety feature becomes a critical vulnerability. The modified Totalitarian firmware disables the airborne disarm function entirely, ensuring the motors continue running even under severe electronic attack.38 While this prevents spoofing-based crashes, it also means legitimate operators cannot easily disarm the drone once it is armed, requiring strict handling protocols.38 Additionally, the software includes operational masking capabilities, allowing operators to deactivate on-screen telemetry to hide the launch point’s location from adversaries attempting to track the drone’s path via intercepted video feeds.38
4.3 Visual Inertial Odometry and Zero-Shot Global Localization
While firmware modifications protect the radio link, they do not solve the problem of navigating without satellite signals. To achieve true autonomy in satellite-denied environments, modern drones are being equipped with multi-modal sensor fusion and edge-computing artificial intelligence.36
Advanced software frameworks, such as the OMNInav system, replace traditional satellite inputs by utilizing visual inertial odometry and simultaneous localization and mapping techniques.39 These systems continuously fuse data from onboard inertial measurement units, barometers, and magnetometers to track movement precisely.36 However, inertial sensors inevitably accumulate drift over time. To correct for this drift, the software employs artificial intelligence models trained on extensive datasets of satellite imagery.39
By matching the live, real-time feed from the drone’s optical or thermal cameras against pre-loaded geographical maps, the system can determine its exact absolute position globally, an action known as zero-shot global localization.39 These models are highly trained for cross-modality registration, allowing them to match live infrared camera data against pre-stored visible-light maps, ensuring reliable navigation even in low-light conditions or heavily altered urban environments.39
4.4 Automated Terminal Guidance and Machine Vision
The most critical phase of a precision drone strike is the final approach. As the drone dives toward the target, the line-of-sight signal is frequently lost due to the curvature of the earth and the dense presence of local vehicular electronic warfare jammers.11 To ensure target engagement despite total signal loss, drones are being equipped with machine vision and automated terminal guidance modules.40
Software solutions provided by companies like Spleenlab allow the drone to utilize onboard processors to visually lock onto a target.42 Once the operator designates the target on their screen and the drone enters the terminal phase, the artificial intelligence takes complete control of the flight surfaces.41 The drone autonomously tracks the moving object and adjusts its trajectory to intercept with an approach accuracy of ±0.2 meters, completely independent of GPS or radio links.41 This renders local radio jammers entirely ineffective because the drone no longer requires external commands to process the final kinetic strike.41
5.0 Paradigm Shifts in Global Infantry Doctrine
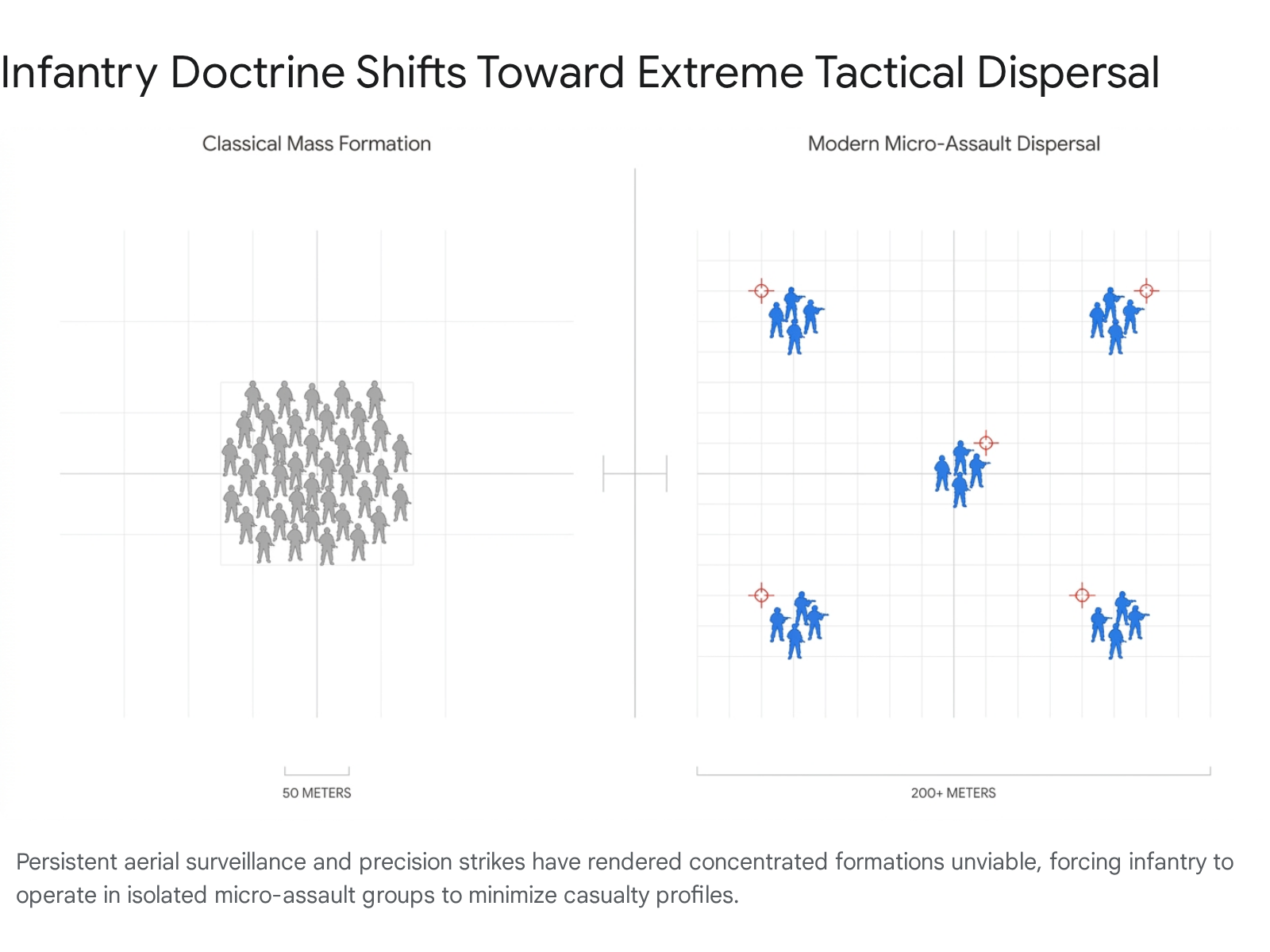
The pervasive presence of highly lethal, precision-guided drones has initiated a profound crisis for traditional ground force doctrine. Military frameworks established during the Cold War, which rely heavily on the massing of troops and the concentration of overwhelming firepower, are proving critically vulnerable to persistent aerial attrition.1
5.1 The Collapse of Classical Mass Maneuver
Historically, military doctrine dictated that forces must concentrate their combat power at decisive points to break through enemy defensive lines.1 However, the modern battlefield has achieved a state of near-total transparency. The skies are saturated with low-cost reconnaissance drones capable of detecting movement instantly and relaying coordinates to artillery units or strike drone operators within seconds.13
Consequently, forces can no longer assemble above the company echelon without triggering immediate detection and catastrophic engagement by networked sensor-shooter systems.1 Any concentration of vehicles or personnel is rapidly identified and targeted, rendering large-scale mechanized assaults operationally unfeasible under current conditions.1 The era of key strongpoints and traditional fortified trenches is ending, replaced by defensive fronts that are thinner, deeper, and heavily reliant on decoys.1
5.2 Tactical Dispersal and the Micro-Assault Group
To survive under persistent aerial surveillance and the constant threat of first-person view drone strikes, infantry units have been forced to adopt extreme dispersal tactics. The traditional platoon-sized assault formation has been reduced to highly distributed micro-assault groups consisting of merely four to six soldiers.44
Ground movement is severely restricted and heavily managed. Forces rely heavily on pre-positioned, concealed fighting positions, often referred to as spider holes, allowing them to rapidly disappear from aerial observation.44 Movement has shifted almost exclusively to short, rapid bounds of 200 to 400 meters, predominantly conducted under the cover of darkness.44 Furthermore, thermal camouflage netting has transitioned from a specialized reconnaissance asset to mandatory, standard-issue equipment down to the individual squad level.44
5.3 The Dispersion Paradox and Defensive Vulnerabilities
This extreme tactical dispersal creates a severe operational paradox. While scattering troops across the landscape improves survivability against area-of-effect artillery and drone strikes, it isolates individual squads and strips them of their ability to provide mutually supporting fire.44
When soldiers are dispersed into small groups of four to six, they lack the organic firepower to suppress enemy advances or defend against coordinated drone swarms. This geometric failure of tactical positioning has led to instances where fully autonomous or remotely piloted drones have captured fortified positions without deploying human infantry, as isolated soldiers, unable to receive support from neighboring units, are systematically eliminated or forced to surrender directly to the aerial vehicles.44 The inability to concentrate force for defense represents a critical vulnerability in current land warfare adaptations.
5.4 Institutionalizing Organic Squad-Level Air Support
Recognizing the permanence of this shift, global military institutions are actively rewriting their foundational doctrines. The United States Army, for instance, has fundamentally overhauled its capstone operations manual, Field Manual 3-0, to prioritize drone dominance.45 The traditional, multi-year doctrinal update cycle has been abandoned in favor of iterative, experience-driven updates based on immediate battlefield feedback from active conflict zones.45
New operational imperatives explicitly direct commanders to protect against constant observation and to utilize unmanned systems to make initial contact with the enemy, preserving human elements.45 First-person view drones and loitering munitions are now functioning as organic, expeditionary close air support.46 Rather than relying on higher-echelon assets like fighter jets or attack helicopters, which require complex clearance protocols and safe separation distances, infantry squads can now independently strike fortified positions and armored threats with pinpoint accuracy.1 Doctrinal mandates dictate that unmanned systems must be integrated into every infantry squad, forcing soldiers to train with and treat drones as standard organic weapons equivalent to their primary rifles or communication gear.30
6.0 The Transformation of Armored Vehicle Deployment
The proliferation of cheap, highly maneuverable unmanned aircraft has precipitated a severe crisis for mechanized warfare. Main battle tanks, representing millions of dollars in investment and decades of complex engineering, are routinely neutralized by commercial drones carrying retrofitted anti-tank munitions.
6.1 Top-Attack Profiles and Standoff Range Mandates
Armored vehicle design has historically prioritized heavy frontal armor thickness to survive direct kinetic engagements with opposing tanks and anti-tank guided missiles.48 First-person view drones exploit this legacy design paradigm by utilizing complex, multi-axis maneuverability to strike vehicles where their armor is significantly weaker, specifically the engine deck, the rear compartment, and the turret roof.48
The precision of expert drone operators allows them to target specific vulnerable components, such as optics, tracks, or open crew hatches, immobilizing the vehicle even if the main armor plating is not fully breached.50 Because a single drone can achieve a mobility or catastrophic kill on a high-value asset, military commanders are increasingly withholding heavy armor from frontline assaults. Tanks and infantry fighting vehicles are frequently relegated to indirect fire roles, operating at standoff distances of 5 to 10 kilometers behind the zero line to avoid detection and destruction by loitering drone swarms.50
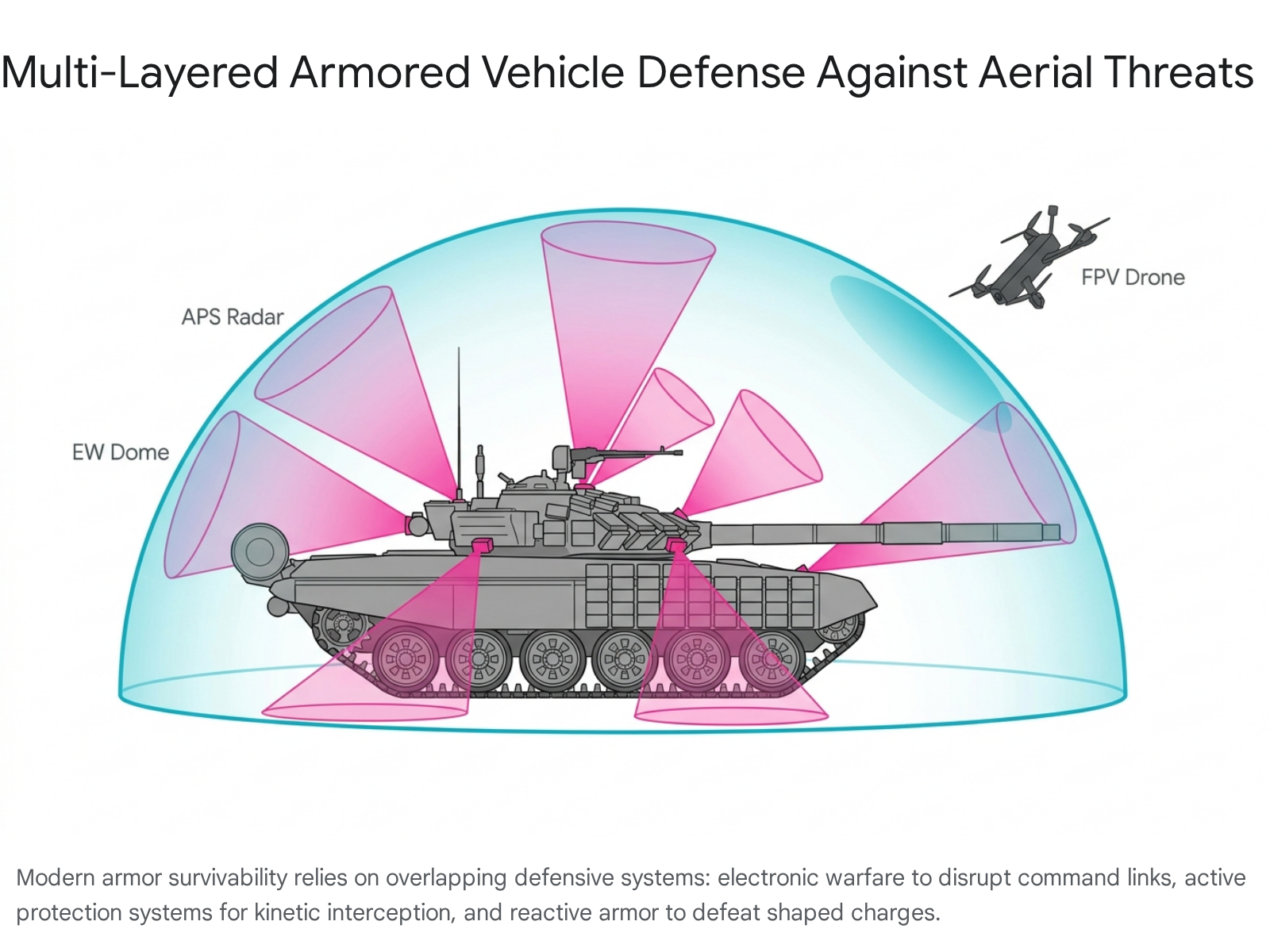
6.2 Vehicular Electronic Warfare Domes and Signal Jamming
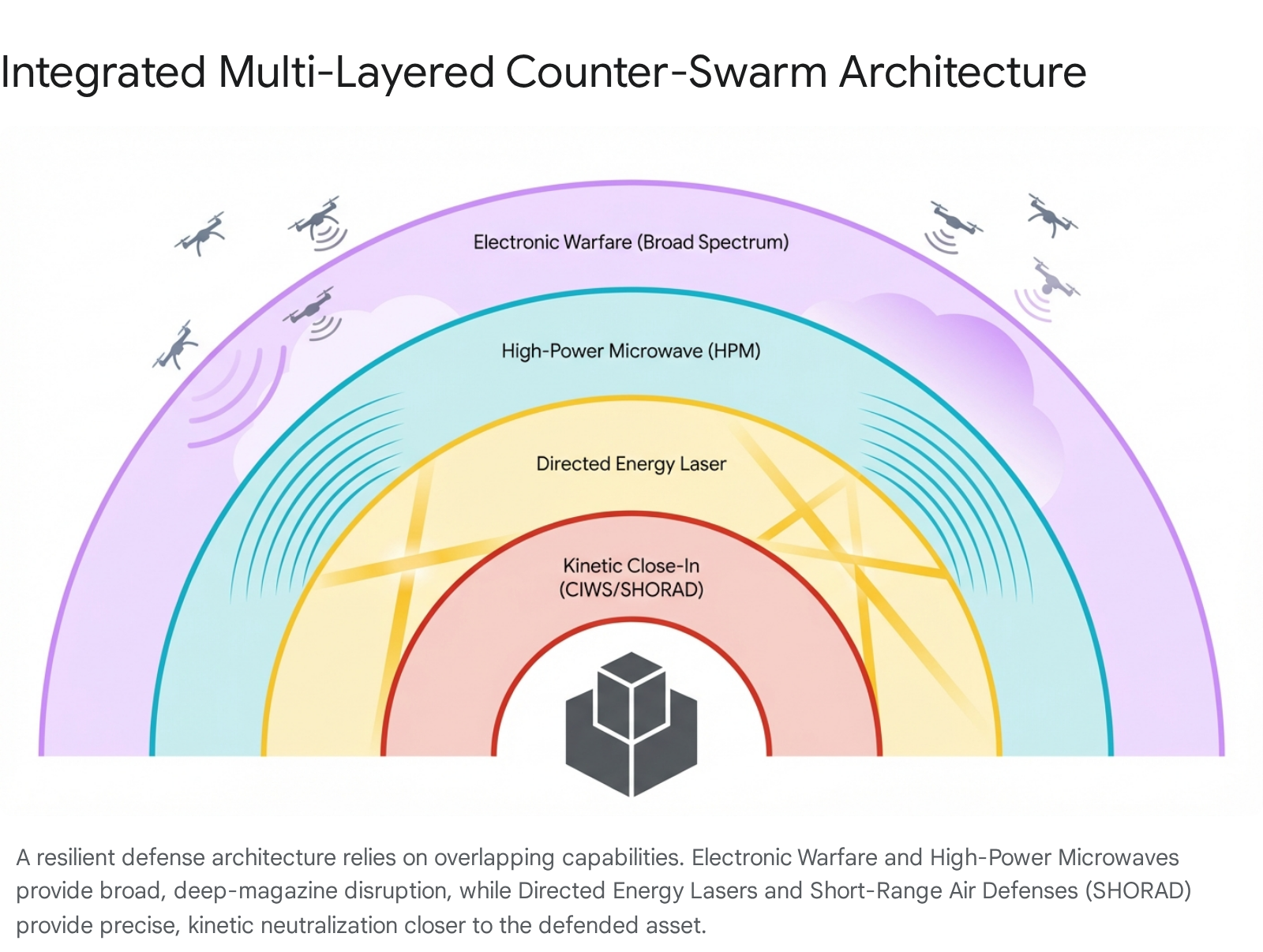
To restore the forward maneuverability of armored columns, defense industries are rapidly integrating counter-unmanned aerial system technologies directly onto vehicular platforms.
Electronic warfare suites are becoming standard equipment on modern tanks to combat the radio frequency links of attacking drones. Russian forces, for example, have attempted to standardize the installation of the Volnorez and Saniya electronic warfare systems on their T-80BVM tanks.41 The Saniya system generates a localized electromagnetic dome designed to detect drones from a distance of 1.5 kilometers and sever their command link within a 1 kilometer range, utilizing a power source capacity of up to 1100 watts.41
However, operational assessments indicate that these localized jammers often suffer from frequency loopholes and limited angles of area coverage.41 This leaves the vehicles highly vulnerable to drone operators who rapidly switch to alternative or non-standard radio frequencies.38 Furthermore, the advent of fiber-optic drones and autonomous terminal guidance completely bypasses these electromagnetic defenses, as the drone no longer relies on a vulnerable external radio signal to complete its terminal dive.1
6.3 Next-Generation Active Protection Systems
Kinetic defense mechanisms are also being aggressively upgraded to handle aerial threats. Advanced Active Protection Systems, such as the Israeli-designed Trophy system utilized on the Leopard 2A8, are being adapted.52 These systems utilize sophisticated radar arrays to detect incoming threats, track their trajectory, and fire explosively formed projectiles to neutralize the munitions before they make physical contact with the hull.52
While these systems are highly effective against traditional, horizontally fired anti-tank guided missiles and rocket-propelled grenades, manufacturers are urgently updating the sensor software and interceptor parameters. The goal is to allow the radar arrays to effectively track and engage small, low-altitude drones executing steep top-attack profiles from unconventional angles, a capability highlighted in recent patent filings for systems like the Russian Arena-M.49
6.4 Field Expedient Modifications and Passive Armor Upgrades
While waiting for the widespread fielding of next-generation active defense systems, combat troops have relied heavily on localized structural modifications. The deployment of physical barriers, colloquially known as top-attack protection screens or cope cages, has become ubiquitous across the battlefield.55
These metal frameworks, grilles, and netting are welded directly onto the turrets and engine decks to physically intercept incoming drones. Their primary function is to pre-detonate shaped-charge warheads before they strike the vehicle’s primary armor, dissipating the explosive jet.56 Even highly advanced Western platforms, such as the American-supplied M1A1 Abrams tanks operating in Ukraine, have been retrofitted in the field with extensive framework cages and dense layers of Kontakt-1 explosive reactive armor to survive the drone-saturated environment.57 The absolute necessity of these heavy, improvised physical defenses highlights the urgency with which military organizations must rethink future vehicle design, balancing the requirement for heavy armor survivability with the need for mobile platforms integrated directly into a network of counter-drone sensor webs.58
7.0 Conclusion
The evolution of first-person view drone tactics has forced a profound reassessment of modern warfare. What originated as a tactical stopgap measure to mitigate severe artillery shortages has rapidly matured into a sophisticated, highly scalable branch of military capability.59 As human operators and automated systems perfect the art of systems warfare, the physical and electronic landscapes of the battlefield are transforming at an unprecedented pace.
To maintain operational viability, global defense institutions are accelerating the decentralization of their hardware supply chains. By embracing additive manufacturing and localized assembly networks, militaries aim to overcome critical international material chokepoints and build resilience against supply disruptions.22 Simultaneously, the software governing these aircraft is being rapidly iterated to ensure robust resilience against intense electronic warfare. Technologies such as visual inertial odometry and autonomous terminal guidance are enabling precise navigation and targeting in regions entirely devoid of satellite coverage or radio connectivity.39
The compounding effects of these technological leaps have effectively collapsed legacy doctrines regarding massed infantry maneuver and concentrated armored assaults.1 Moving forward, survival and success in high-intensity conflict will demand extreme tactical dispersal, the ubiquitous integration of organic unmanned systems down to the individual squad level, and the continuous, rapid adaptation of both offensive drone logic and multi-layered defensive countermeasures.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Sources Used
- MCU Insights, vol. 16, no. 4 – Marine Corps University, accessed April 18, 2026, https://www.usmcu.edu/Outreach/Marine-Corps-University-Press/MES-Publications/MES-Insights/MCU-Insights-vol-16-no-4/
- Drone Warfare in Ukraine: From Myths to Operational Reality – Part 1, accessed April 18, 2026, https://researchcentre.army.gov.au/library/land-power-forum/drone-warfare-ukraine-myths-operational-reality-part-1
- From Quantity to Algorithms: How FPV Warfare Is Changing in 2026 – VGI-9, accessed April 18, 2026, https://vgi.com.ua/en/from-quantity-to-algorithms-how-fpv-warfare-is-changing-in-2026/
- (PDF) Tactical Network-Centric Warfare in Practice: FPV Drones and the Architecture of a New RMA – ResearchGate, accessed April 18, 2026, https://www.researchgate.net/publication/393440325_Tactical_Network-Centric_Warfare_in_Practice_FPV_Drones_and_the_Architecture_of_a_New_RMA
- Ukraine Drone Industry: Data Reports 2026 – WifiTalents, accessed April 18, 2026, https://wifitalents.com/ukraine-drone-industry-statistics/
- How $400 FPV Drones Are Destroying Tanks and Rewriting the Rules of War, accessed April 18, 2026, https://militarymachine.com/fpv-drones-destroying-tanks
- Russian Offensive Campaign Assessment, April 9, 2026 | ISW, accessed April 18, 2026, https://understandingwar.org/research/russia-ukraine/russian-offensive-campaign-assessment-april-9-2026/
- Ukraine Conflict Monitor: Russia-Ukraine war map | ACLED, accessed April 18, 2026, https://acleddata.com/monitor/ukraine-conflict-monitor
- Russia’s FPV drone campaign in Ukraine institutionalizes intentional civilian harm as a tool of war – Institute for the Study of War, accessed April 18, 2026, https://understandingwar.org/research/russia-ukraine/russias-fpv-drone-campaign-in-ukraine-institutionalizes-intentional-civilian-harm-as-a-tool-of-war/
- Moving Targets: Implications of the Russo-Ukrainian War for Drone Terrorism, accessed April 18, 2026, https://ctc.westpoint.edu/moving-targets-implications-of-the-russo-ukrainian-war-for-drone-terrorism/
- FPV Drone Motherships That Also Relay Their Signals Offer Huge …, accessed April 18, 2026, https://www.twz.com/air/fpv-drone-motherships-that-also-relay-their-signals-offer-huge-advantages
- Russian Force Generation & Technological Adaptations Update, October 9, 2025, accessed April 18, 2026, https://understandingwar.org/research/russia-ukraine/russian-force-generation-technological-adaptations-update-october-9-2025/
- How are Drones Changing War? The Future of the Battlefield – CEPA, accessed April 18, 2026, https://cepa.org/article/how-are-drones-changing-war-the-future-of-the-battlefield/
- Ukraine’s Future Vision and Current Capabilities for Waging AI-Enabled Autonomous Warfare – CSIS, accessed April 18, 2026, https://www.csis.org/analysis/ukraines-future-vision-and-current-capabilities-waging-ai-enabled-autonomous-warfare
- Russian Fiber-Optic FPV Drones: Operational Scale and Operator Training – RuAviation, accessed April 18, 2026, https://ruavia.su/russian-fiber-optic-fpv-drones-operational-scale-and-operator-training/
- Fibre Optics FPV Drone, accessed April 18, 2026, https://5.imimg.com/data5/SELLER/Doc/2026/1/577229561/JX/PC/CX/81615670/fibre-optics-drone.pdf
- Ukraine FPV Drone Explained! – YouTube, accessed April 18, 2026, https://www.youtube.com/watch?v=3VfYvVw8sMw
- Ptashka Drones Achieves 50 km Range with Successful Fiber Optic Drone Use, accessed April 18, 2026, https://militarnyi.com/en/news/ptashka-drones-achieves-50-km-range-with-successful-fiber-optic-drone-use/
- Drone Wars: Developments in Drone Swarm Technology – Defense Security Monitor, accessed April 18, 2026, https://dsm.forecastinternational.com/2025/01/21/drone-wars-developments-in-drone-swarm-technology/
- DoD promised a ‘swarm’ of attack drones. We’re still waiting. – Responsible Statecraft, accessed April 18, 2026, https://responsiblestatecraft.org/replicator/
- The Drone Supply Chain War: Identifying the Chokepoints to Making a Drone – CSIS, accessed April 18, 2026, https://www.csis.org/analysis/drone-supply-chain-war-identifying-chokepoints-making-drone
- Additive Manufacturing and the Land Forces Supply Chain: a Revolution Within a … – Eurosatory, accessed April 18, 2026, https://www.eurosatory.com/en/additive-manufacturing-and-the-land-forces-supply-chain-a-revolution-within-a-revolution/
- Not Just “Game of Lego”: How Ukraine Turned 3D-Printing into Decentralized Military Conveyor Belt | Defense Express, accessed April 18, 2026, https://en.defence-ua.com/events/not_just_a_game_of_lego_how_ukraine_turned_3d_printing_into_a_decentralized_military_conveyor_belt-18078.html
- Drone Manufacturing: Scaling Production and Cutting Costs with Automated 3D Printing, accessed April 18, 2026, https://dhr.is/blog/drone-manufacturing-scaling-production-and-cutting-costs-with-automated-3d-printing
- Secret Decentralized 3D Printing Networks Supply Drone Parts to Ukraine at Scale, accessed April 18, 2026, https://www.fabbaloo.com/news/secret-decentralized-3d-printing-networks-supply-drone-parts-to-ukraine-at-scale
- How Ukraine Turned DIY Drones into a Powerful War Force — and What Europe Can Learn, accessed April 18, 2026, https://orbitaltoday.com/2026/04/16/how-ukraine-turned-diy-drones-into-a-powerful-war-force-and-what-europe-can-learn/
- Regulatory Changes to Foster US Drone Supply Chains – Capstone DC, accessed April 18, 2026, https://capstonedc.com/insights/regulatory-changes-to-foster-us-drone-supply-chains/
- FCC Announces Wide-Ranging New Controls on Drones and Drone Components | HUB, accessed April 18, 2026, https://www.klgates.com/FCC-Announces-Wide-Ranging-New-Controls-on-Drones-and-Drone-Components-1-16-2026
- Pentagon must consider force structure in mass drone rollout – Army Technology, accessed April 18, 2026, https://www.army-technology.com/news/pentagon-must-consider-force-structure-in-mass-drone-rollout/
- Army aims to manufacture 10,000 drones per month by 2026 …, accessed April 18, 2026, https://defensescoop.com/2025/10/14/army-small-drones-skyfoundry/
- As Promised, War Department Moving Out Fast on Drone Dominance, accessed April 18, 2026, https://www.war.gov/News/News-Stories/Article/Article/4399192/as-promised-war-department-moving-out-fast-on-drone-dominance/
- Press Release – Unusual Machines, accessed April 18, 2026, https://www.unusualmachines.com/press-release/
- U.S. Maker of Drone Parts Now at Key Inflection Point – Streetwise Reports, accessed April 18, 2026, https://www.streetwisereports.com/article/2025/08/29/u-s-maker-of-drone-parts-now-at-key-inflection-point-1.html
- FPV Motors – iFlight, accessed April 18, 2026, https://shop.iflight.com/motors-cat88
- ELRS Micro Receiver – BETAFPV, accessed April 18, 2026, https://betafpv.com/products/elrs-micro-receiver
- AI-Based Navigation in GNSS-Denied Areas, accessed April 18, 2026, https://www.uavnavigation.com/company/blog/ai-based-navigation-gnss-denied-areas
- Navigating GPS-Denied Environments: Solutions and Challenges – GNSS Jamming, accessed April 18, 2026, https://www.gnssjamming.com/post/gps-denied-environments
- How software modifications affect drone warfare – The Russian …, accessed April 18, 2026, https://en.kkrva.se/how-software-modifications-affects-drone-warfare-the-russian-example/
- OMNInav: A Breakthrough in GPS-Denied Navigation for UAS – OKSI, accessed April 18, 2026, https://oksi.ai/omninav-gps-denied-navigation/
- Ukrainian Armor Upgrades Its Drone Line with New Warheads and Terminal Guidance, accessed April 18, 2026, https://en.defence-ua.com/industries/ukrainian_armor_upgrades_its_drone_line_with_new_warheads_and_terminal_guidance-18179.html
- New Saniya EW System Seeks to Protect russian Tanks From FPV Drones, But Where’s Overhyped Volnorez? | Defense Express, accessed April 18, 2026, https://en.defence-ua.com/weapon_and_tech/new_saniya_ew_system_seeks_to_protect_russian_tanks_from_fpv_drones_but_wheres_overhyped_volnorez-9181.html
- Terminal Guidance | Spleenlab, accessed April 18, 2026, https://www.spleenlab.ai/product-terminal-guidance
- I Fought in Ukraine and Here’s Why FPV Drones Kind of Suck – War on the Rocks, accessed April 18, 2026, https://warontherocks.com/2025/06/i-fought-in-ukraine-and-heres-why-fpv-drones-kind-of-suck/
- The Dispersion Paradox: When Sound Tactics Become a Death Sentence, accessed April 18, 2026, https://smallwarsjournal.com/2026/02/13/the-dispersion-paradox/
- Army Rewrites Drone Doctrine Force-Wide as “Drone Dominance …, accessed April 18, 2026, https://insideunmannedsystems.com/army-rewrites-drone-doctrine-force-wide-as-drone-dominance-becomes-priority/
- Emerging Counter-Drone Technologies and Asymmetric Defence Responses – CeSCube, accessed April 18, 2026, https://www.cescube.com/vp-emerging-counter-drone-technologies-and-asymmetric-defence-responses
- How Ukraine’s Drone War Is Forcing the U.S. Army to Rewrite Its Battle Doctrine, accessed April 18, 2026, https://www.military.com/feature/2025/10/19/how-ukraines-drone-war-forcing-us-army-rewrite-its-battle-doctrine.html
- Russia’s Changes in the Conduct of War Based on Lessons from Ukraine, accessed April 18, 2026, https://www.armyupress.army.mil/Journals/Military-Review/English-Edition-Archives/September-October-2025/Lessons-from-Ukraine/
- Russian Tanks Getting Anti-Drone Protection – New APS Upgrades Revealed – YouTube, accessed April 18, 2026, https://www.youtube.com/watch?v=1n5jfDrQIC8
- The New Arms Race: Global Drone Dominance and America’s Tactical Wake-Up Call, accessed April 18, 2026, https://smallwarsjournal.com/2025/12/16/the-new-arms-race/
- Russian Offensive Campaign Assessment, March 19, 2026 | ISW, accessed April 18, 2026, https://understandingwar.org/research/russia-ukraine/russian-offensive-campaign-assessment-march-19-2026/
- combat proven – Leonardo – Electronics, accessed April 18, 2026, https://electronics.leonardo.com/documents/16277707/18411670/trophy_datasheet.pdf?t=1563282195884
- The 5 Best Tanks in the World for 2026: Advanced Armor Redefining Ground Combat, accessed April 18, 2026, https://thedefensewatch.com/military-ordnance/the-5-best-tanks-in-the-world-for-2026/
- Do you think drones will eventually render tanks obsolete, just as cannons did with castles in the 16th century? : r/Military – Reddit, accessed April 18, 2026, https://www.reddit.com/r/Military/comments/1pmq9od/do_you_think_drones_will_eventually_render_tanks/
- How are Drones Changing Modern Warfare? | Australian Army Research Centre (AARC), accessed April 18, 2026, https://researchcentre.army.gov.au/library/land-power-forum/how-are-drones-changing-modern-warfare
- United States Plans to Equip its Tanks With Anti-Drone Grilles, accessed April 18, 2026, https://militarnyi.com/en/news/united-states-plans-to-equip-its-tanks-with-anti-drone-grilles/
- Ukraine’s Abrams Tanks Are Being Reinvented for Drone Warfare on the Front Line, accessed April 18, 2026, https://united24media.com/latest-news/ukraines-abrams-tanks-are-being-reinvented-for-drone-warfare-on-the-front-line-17480
- Armor in 2025: Getting Armored Brigades Back into the Fight – Line of Departure, accessed April 18, 2026, https://www.lineofdeparture.army.mil/Journals/Air-Defense-Artillery/ADA-Archive/2026-E-Edition/Armor-in-2025/
- Results of Ukraine’s Defense Industry in 2025: FPV Drones, accessed April 18, 2026, https://www.rnbo.gov.ua/en/Diialnist/7370.html