1. Executive Summary
The fundamental calculus of global military supremacy is undergoing a structural realignment, signaling the definitive end of an era dominated by exquisite, capital-intensive weapons systems. For decades, the United States military has relied on a strategy of conventional overmatch derived from the “Second Offset”—a paradigm defined by stealth, advanced sensing, and highly capable, expensive precision-guided munitions.1 However, the democratization of technology, driven by commercial electronics, artificial intelligence (AI), and satellite navigation, has flattened the precision advantage that the United States once uniquely held.2 Precision is no longer a scarce or expensive commodity; it can now be delivered at massive scale through low-cost, intelligent autonomous systems.2 This rapid transition from “exquisite precision” to “precise mass” introduces an era of extreme asymmetric threats, fundamentally threatening traditional U.S. force posture, base defense, and procurement doctrines.2
This comprehensive report provides a detailed analysis of the strategic, operational, and industrial adaptations required for the U.S. military to counter these extreme asymmetric threats. While the necessity of producing lower-cost weapons is widely acknowledged within the defense establishment, this analysis focuses on the frequently overlooked dimensions of the conflict paradigm. These include the architectural vulnerability of true distributed swarms, the cognitive limitations of human operators in autonomous environments, the fragility of software-defined forces operating in contested electromagnetic spectrums, and the deep logistical and supply chain vulnerabilities inherent in attempting to scale an attritable force.4
Key findings indicate that the current defense architecture is highly vulnerable to adverse cost-exchange ratios, where multimillion-dollar interceptors are routinely expended against inexpensive loitering munitions, creating an unsustainable trajectory of economic and manufacturing attrition.2 Furthermore, while the Department of Defense (DoD) is attempting to pivot toward mass through rapid fielding initiatives like Project Replicator, the defense industrial base (DIB) remains structurally constrained by legacy acquisition models, bureaucratic friction, and a critical, high-risk dependency on foreign adversaries for the foundational elements of modern warfare, particularly microelectronics and rare earth elements.6
To regain and sustain dominance, the U.S. military must look far beyond simply acquiring cheaper platforms. It must systematically invest in multi-layered, non-kinetic defensive architectures—specifically high-power microwave (HPM) and directed energy weapons (DEW)—to neutralize the severe cost-exchange disadvantage.11 Simultaneously, the joint force must redesign its command and control (C2) networks to operate effectively in denied, degraded, intermittent, and limited (DDIL) bandwidth environments, shifting from cloud-dependent software models to resilient edge-computing architectures.7 Finally, military doctrine must evolve to address the “Mind-Tech Nexus,” optimizing the human-machine interface to manage the inevitable cognitive overload of modern combat, and radically rethinking restrictive human-in-the-loop policies that fail to match the speed and scale of machine-driven warfare.14
2. The Strategic Context: The End of Sanctuary and the Economics of Mass
2.1 The Erosion of the Second Offset Strategy
To understand the depth of the current strategic vulnerability, it is necessary to trace the evolution of U.S. military dominance. In the 1970s and 1980s, facing the numerical superiority and rapid nuclear expansion of the Soviet Union, U.S. defense planners recognized that traditional attrition warfare was untenable.1 They subsequently pursued what became known as the “Second Offset” strategy.1 This approach leveraged emerging advancements in microelectronics, precision-guided munitions (PGMs), stealth technology, and highly capable intelligence, surveillance, and reconnaissance (ISR) networks to achieve conventional overmatch.1 The underlying assumption of the Second Offset was that highly sophisticated, highly survivable, and highly expensive platforms could defeat massed, less sophisticated adversary forces through the precise and surgical application of force.1
Today, that foundational assumption has become a strategic liability. The technological barriers to entry for precision guidance have totally collapsed. Adversaries, ranging from near-peer competitors like China and Russia to non-state actors and proxy militias in the Middle East, have unfettered access to commercially derived technologies that replicate the kinetic effects of exquisite PGMs at a fraction of the cost.2 The proliferation of small unmanned aircraft systems (sUAS), loitering munitions, and cheap ballistic missiles has created an environment where precision is ubiquitous. This has led to the emergence of “precise mass”—the high-volume use of low-cost drones—as a defining and permanent feature of modern warfare.2
2.2 The Death of Sanctuary and the Vulnerability of Capital Platforms
The ubiquity of low-cost, pervasive lethality has effectively ended the concept of sanctuary for U.S. forces and their allies.17 Miniaturization, extended battery and fuel endurance, and pervasive connectivity allow autonomous systems to detect, track, and attack combatants, non-combatants, and capital-intensive military assets deep within previously secure, rear-echelon zones.17
In the Indo-Pacific theater, this dynamic is particularly acute and presents the most significant challenge to U.S. operational planning. China’s anti-access/area-denial (A2/AD) strategy utilizes the immense depth of its landmass to posture air, missile, and antisatellite forces, effectively creating robust sanctuaries for the People’s Liberation Army (PLA) while denying the same operational depth to the United States and its regional allies.18 If the PLA is permitted to operate from these defended interiors without the threat of sanctuary denial, they possess the capacity to generate massive air and missile salvos that will severely attrit U.S. forces and completely undermine distributed warfighting strategies.18 Without deep magazines of substantially enhanced counter-drone capabilities, the United States risks having its forces overwhelmed by massed Chinese drone attacks, which could decisively tip the balance in a conflict over Taiwan or operations within the First Island Chain.19
This dynamic forces a profound re-evaluation of the future role of large surface combatants (LSCs) and apex platforms like aircraft carriers. The U.S. Navy operates 11 highly complex aircraft carriers, each representing an investment of tens of billions of dollars when accounting for the ship, the embarked air wing, and the massive logistics infrastructure required to sustain them.20 In an era where adversaries can deploy inexpensive DF-21D “carrier killer” ballistic missiles and next-generation AI-powered cruise missiles in massive salvos, the survivability of a $35 billion carrier strike group is increasingly questionable.22 Similarly, the role of heavy armor and main battle tanks is being rapidly degraded by the proliferation of highly accurate, low-cost first-person view (FPV) drones, which have been used effectively in recent conflicts to destroy multimillion-dollar armored vehicles with strikes costing only a few hundred dollars.10
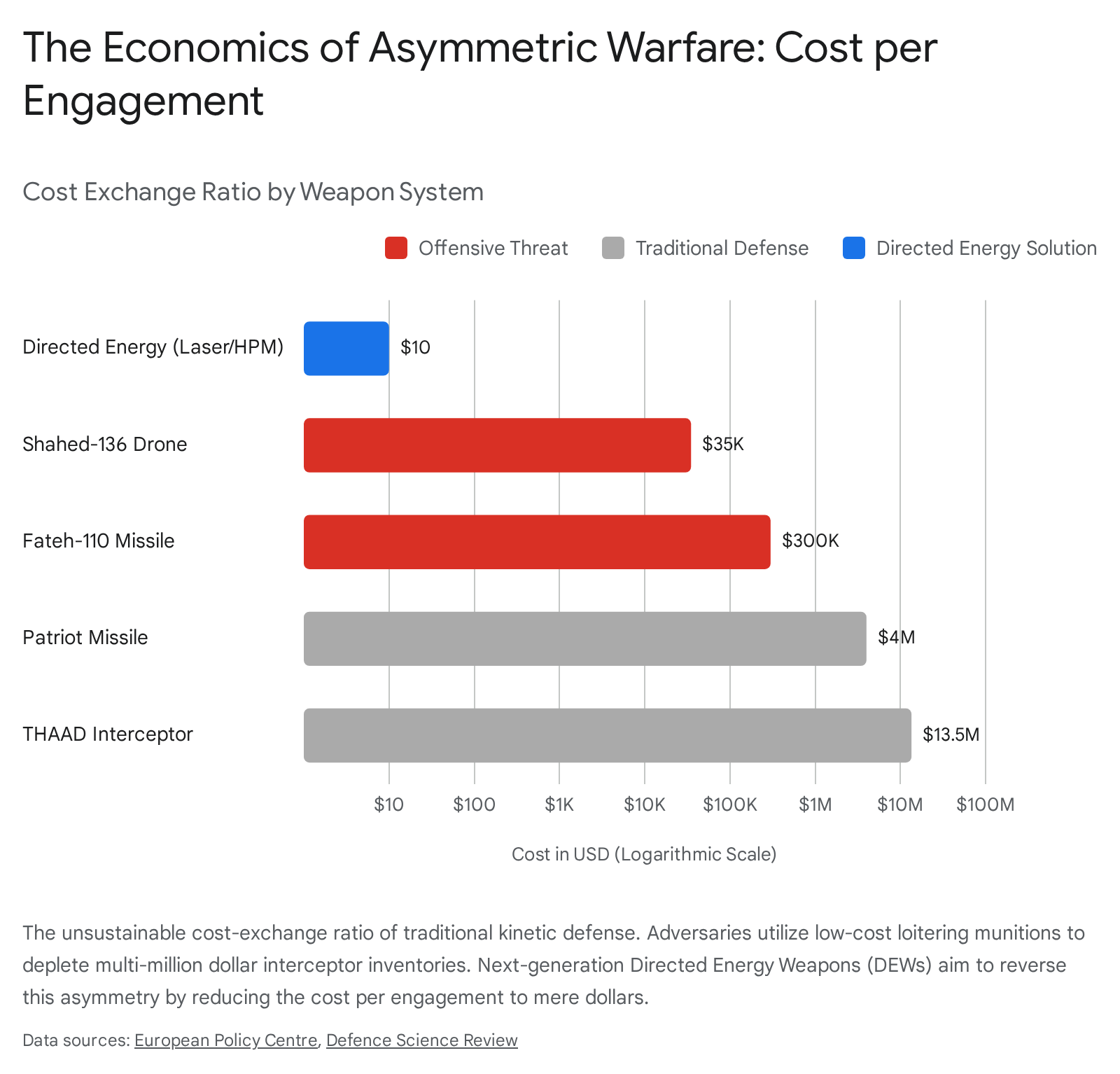
2.3 The Structural Imbalance of the Cost-Exchange Ratio
The most immediate, severe, and mathematically unforgiving vulnerability facing the U.S. military today is economic attrition via the cost-exchange ratio.8 Modern conflicts, ranging from the defense of shipping lanes in the Red Sea to the ongoing war in Ukraine, repeatedly demonstrate that adversaries are utilizing cheap munitions to impose disproportionate financial and logistical costs on advanced Western militaries.2
Adversarial systems like the Iranian Shahed-136 loitering munition represent a deliberate design philosophy centered entirely on affordability, simplicity, and rapid scalability.23 Unlike exquisite U.S. UAVs equipped with proprietary sensors, these drones rely on basic commercial GPS guidance and simple piston engines, resulting in an estimated unit cost of approximately $20,000 to $50,000.2 In stark contrast, U.S. and allied air defense architectures rely heavily on highly sophisticated kinetic interceptors designed for a previous era of warfare. For example, a single Patriot missile interceptor costs roughly $4 million, a Standard Missile-2 (SM-2) utilized by the U.S. Navy costs approximately $2 million, and a Terminal High Altitude Area Defense (THAAD) interceptor ranges from $12 million to $15 million.2 Even against the relatively rudimentary ballistic missiles these systems are designed to defeat, such as the Iranian Fateh-110 series (estimated at a few hundred thousand dollars each), the financial imbalance is staggering.2
| Threat System (Offensive) | Estimated Unit Cost | Defensive Interceptor | Estimated Unit Cost | Cost-Exchange Ratio |
| Commercial Quadcopter | ~$500 | Stinger Missile | ~$100,000 | 1:200 |
| Houthi Attack Drone | ~$2,000 | Standard Missile-2 (SM-2) | ~$2,000,000 | 1:1,000 |
| Shahed-136 Loitering Munition | $20,000 – $50,000 | Patriot Missile Interceptor | ~$4,000,000 | 1:80 to 1:200 |
| Fateh-110 Class Ballistic Missile | ~$300,000 | THAAD Interceptor | $12,000,000 – $15,000,000 | 1:40 to 1:50 |
This profound asymmetry extends well beyond the munitions themselves. The sensor networks required to detect and track these cheap threats are exorbitant capital investments. For instance, the AN/TPY-2 radar system that supports the THAAD network can cost upwards of $1 billion.2 Intelligence reports indicate that two such highly advanced radar systems were recently disabled by Iranian drones costing roughly $30,000 each, resulting in an adverse cost-exchange ratio of greater than 30,000 to one.2
This economic paradigm allows adversaries to employ a strategy of intentional exhaustion. By launching large numbers of relatively cheap drones and missiles in mixed, pulsed salvos, attackers stretch defensive systems to their absolute limits and rapidly consume interceptor inventories.2 Even when these attacks are successfully intercepted with a 100% success rate, they still impose a heavy strategic cost. Every interceptor fired must be replaced via complex, slow-moving supply chains that can take years to replenish, whereas the attacker can rapidly produce additional drones using commercial components and simple manufacturing processes.2 Relying on traditional kinetic interception as the primary means of defense is mathematically and industrially unsustainable against a peer adversary capable of generating millions of attritable systems.19
3. Beyond “Cheap Weapons”: The Overlooked Dimensions of Asymmetric Threat
The prevailing discourse surrounding military modernization often concludes with the simplistic recommendation that the U.S. must produce lower-cost weapons in greater quantities. This is a severe oversimplification of the threat matrix. While mass is undoubtedly required, focusing solely on the physical platform ignores the underlying architecture, the human element, and the cognitive constraints of future warfare.
3.1 The Architectural Illusion: We Are Not Yet Seeing True Swarms
A critical oversight in current threat assessments is the pervasive mischaracterization of existing drone operations as true “swarms.” What defense observers and analysts frequently witness—whether it is choreographed drone light shows in China, leader-follower autonomous teaming experiments, or massed first-person view (FPV) drone deployments in Ukraine and the Middle East—is merely robotic maneuver en masse.4 One hundred drones operated by a single person, or dozens of loitering munitions pre-programmed to strike specific fixed coordinates, do not constitute a swarm.4
A genuine swarm is, by definition, a distributed system.4 It operates as a singular entity rather than a plural collection of platforms. It is overwhelming not just in its scale, but in its unity, resilience, and capacity to adapt intelligently to changing circumstances at machine speed without a single point of failure.4 In a true swarm, if a percentage of the drones are destroyed by kinetic interceptors, the remaining entities instantly reallocate targeting priorities, share decentralized sensor data, and optimize their attack vectors autonomously. The defense industry has largely failed to deliver the distributed systems infrastructure required for this resilient, collaborative swarming behavior, instead focusing predominantly on platform capability inputs like hardware, manufacturing volume, and GPS integration.4 By labeling groups of remotely piloted products as “swarms,” the defense establishment has robbed the concept of its strategic meaning and blunted the demand signal for true distributed autonomy.4 The transformative strategic leap that analysts are overlooking is the imminent arrival of collaborative autonomy. When adversaries achieve true distributed swarming, current linear defense mechanisms will be instantly paralyzed by the swarm’s non-linear, self-healing adaptability.4
| From a publishing perspective, this report was authored before the late-March 2026 Kupiansk strike by Ukraine on a Russian armored column that involved a true swarm. Click here to read a dedicated report on that event. |
3.2 The Mind-Tech Nexus and the Threat of Cognitive Overload
As the U.S. military actively integrates more autonomous systems into its ranks, a severe vulnerability emerges regarding human cognitive capacity. The development of Human-Machine Integrated Formations (HMIF) requires human operators to interact with and manage multiple interdependent autonomous systems simultaneously.5 This dynamic convergence of human factors (such as perception, the will to fight, and decision-making capabilities) with advanced technology is formally termed the “Mind-Tech Nexus”.14
However, current user interfaces and command structures are fundamentally ill-equipped to handle the resulting information overload.5 The dynamic interplay of managing multiple uncrewed assets—monitoring sensor feeds, approving targeting data, and coordinating maneuver—rapidly scales cognitive demands beyond the physiological limits of individual human operators.5 This overload extends beyond the individual, impacting wider team and unit-level operational effectiveness.5
Adversaries are acutely aware of this vulnerability. China, through its expansive “China Brain Project,” and Russia, through its pioneering use of AI to exploit cognitive vulnerabilities, are deeply focused on the intersection of neuroscience and artificial intelligence to enhance their own performance while seeking to suppress the cognitive capabilities of U.S. forces.14 If U.S. procurement does not prioritize AI-driven swarm control systems that filter immense datasets and present intuitive, tactical autonomy contracts, operators will be paralyzed by decision fatigue in the heat of battle.26 Future capabilities must lean on intelligent agents that ease the cognitive load, allowing the human tactical leader to concentrate on the broader design of the maneuver and its execution, rather than micro-managing the flight paths of individual drones.26 Additionally, research into Brain-Computer Interfaces (BCI) presents a disruptive, albeit ethically complex, future pathway for direct man-machine neural communication to alleviate these cognitive bottlenecks during high-stress tactical operations.27
3.3 Doctrinal Paralysis: The Human-in-the-Loop Fallacy
Compounding the critical issue of cognitive overload is a widely misunderstood doctrinal limitation regarding lethal autonomous weapons systems. A pervasive myth within defense circles and the broader public is that Department of Defense Directive 3000.09 prohibits fully autonomous weapon systems or strictly mandates that a “human must be in the tactical loop” for all lethal engagements.16 In reality, the directive does not categorically prohibit autonomous engagement, nor does it mandate a human in the loop for every system.16
Robotic weapons are generally categorized by human involvement:
- Human-in-the-Loop: Robots that can select targets and deliver force only with an explicit human command.28
- Human-on-the-Loop: Robots that can select targets and deliver force under the active oversight of a human operator who retains the ability to override the machine’s actions.28
- Human-out-of-the-Loop: Robots capable of selecting targets and delivering force entirely without human input or interaction.28
Maintaining a strict human-in-the-loop or even human-on-the-loop posture creates an artificial and potentially fatal operational bottleneck. Against a true AI-driven adversary swarm executing complex, coordinated decisions at machine speed, human-dependent systems will be vastly outpaced and decisively defeated.4 The ethical, legal, and policy debates surrounding human-out-of-the-loop weapons must rapidly reconcile with the operational reality of the modern battlefield.29 In high-intensity, drone-saturated environments, removing humans from the micro-decision cycle is not a moral failing; it is a baseline requirement for force survival.
Consider a historical counterfactual: During the 1991 Gulf War, General Norman Schwarzkopf directed his air component to degrade Iraqi armor units by 50% prior to ground engagement.15 If, instead of manned aircraft, Schwarzkopf possessed a swarm of AI-enabled lethal autonomous weapons, requiring a human operator to individually validate and approve every single strike against thousands of tanks would negate the speed and shock value of the swarm.15 The failure to prepare command structures and legal frameworks for this inevitable transition toward delegated lethal autonomy represents a critical strategic blind spot that adversaries will exploit.29
4. Software-Defined Warfare and Its Strategic Vulnerabilities
To effectively counter intelligent mass, the DoD is currently undertaking a profound digital transformation, attempting to pivot away from a hardware-centric, industrial-age organization toward a software-centric, digital-age force.31 This transition is absolute essential; rigid, linear, long-lead-time hardware procurement programs are inherently incompatible with the rapid iterations required to field AI capabilities at scale and counter fast-evolving, commercially driven drone threats.33
4.1 Transitioning the Architecture: Open DAGIR and Interoperability
The traditional military procurement model deeply embeds custom software within proprietary hardware solutions (such as those found in legacy fighter jets and the Aegis Weapons System), creating severe vendor lock-in and stifling interoperability.33 Modernization requires forcefully decoupling the two.
Initiatives like the Chief Digital and Artificial Intelligence Office’s (CDAO) “Open DAGIR” blueprint emphasize a transition to data-centric architectures based on the principles of interoperability and replaceability.33 The goal is to function akin to a smartphone app store, where the DoD owns the underlying infrastructure and can rapidly buy, retain, or remove individual software applications from an AI marketplace, deploying them across various existing hardware platforms.33 This modular, capability-driven approach ensures that a radar system or combat vehicle procured today remains operationally relevant for decades via continuous, non-disruptive digital reconfiguration, shifting the focus from buying static platforms to acquiring evolving mission capabilities.34 Furthermore, the bureaucratic Authority to Operate (ATO) process, which has historically hobbled rapid deployment, must shift toward continuous ATOs integrated directly into DevSecOps pipelines, ensuring predictable and secure pathways to deployment.33
4.2 The Testing Dilemma of Non-Deterministic Systems
While software-defined arsenals promise unprecedented agility, they introduce severe validation and testing challenges. The Pentagon’s Office of the Director of Operational Test and Evaluation has historically relied on deterministic testing methodologies, verifying that a specific input always yields a specific, predictable output.35 However, AI and machine learning models are inherently non-deterministic; their outputs change and evolve based on dynamic, unpredictable environmental inputs and continuous learning.35 Racing ahead with software innovation while simultaneously cutting back on rigorous, tech-augmented oversight risks fielding brittle, unproven systems that fail unexpectedly when subjected to the chaos of combat.35 Procurement strategies must pivot to invest heavily in modernized test enterprises, utilizing digital twins, distributed synthetic simulation environments, and continuous combat-data-loop testing to ensure reliability without sacrificing deployment speed.34
4.3 Friction, Fog, and Failure: The DDIL Vulnerability
Perhaps the most profound, yet frequently overlooked, vulnerability of a software-defined force is its absolute reliance on pristine networked connectivity. The military’s overarching vision of Joint All-Domain Command and Control (JADC2)—where sensors seamlessly pass data to effectors via cloud-connected architectures across all domains—assumes an uncontested electromagnetic spectrum.7
In a peer conflict, this assumption is a dangerous illusion. The electromagnetic spectrum (EMS) and cyber domains are now contested key terrain.37 The deep integration of cyber warfare and electronic warfare (EW) down to the tactical level means that sophisticated adversaries will actively target U.S. networks, spoof sensors, poison AI training datasets, and aggressively jam communications.37 In Denied, Degraded, Intermittent, and Limited (DDIL) bandwidth environments, cloud-dependent software architectures will experience catastrophic failure.7 If hardware platforms rely entirely on centralized software algorithms that cannot be reached due to localized communication denial, units will be functionally paralyzed, returning to a state of uncoordinated, blind operations.7 A truly resilient software-defined force must prioritize edge computing—localized AI processing power situated directly on the tactical platform that does not require reach-back to the cloud—and autonomous fallback operations capable of functioning through complete spectrum isolation.7
5. Architectural Shifts in Defense Systems: The Multi-Layered Approach
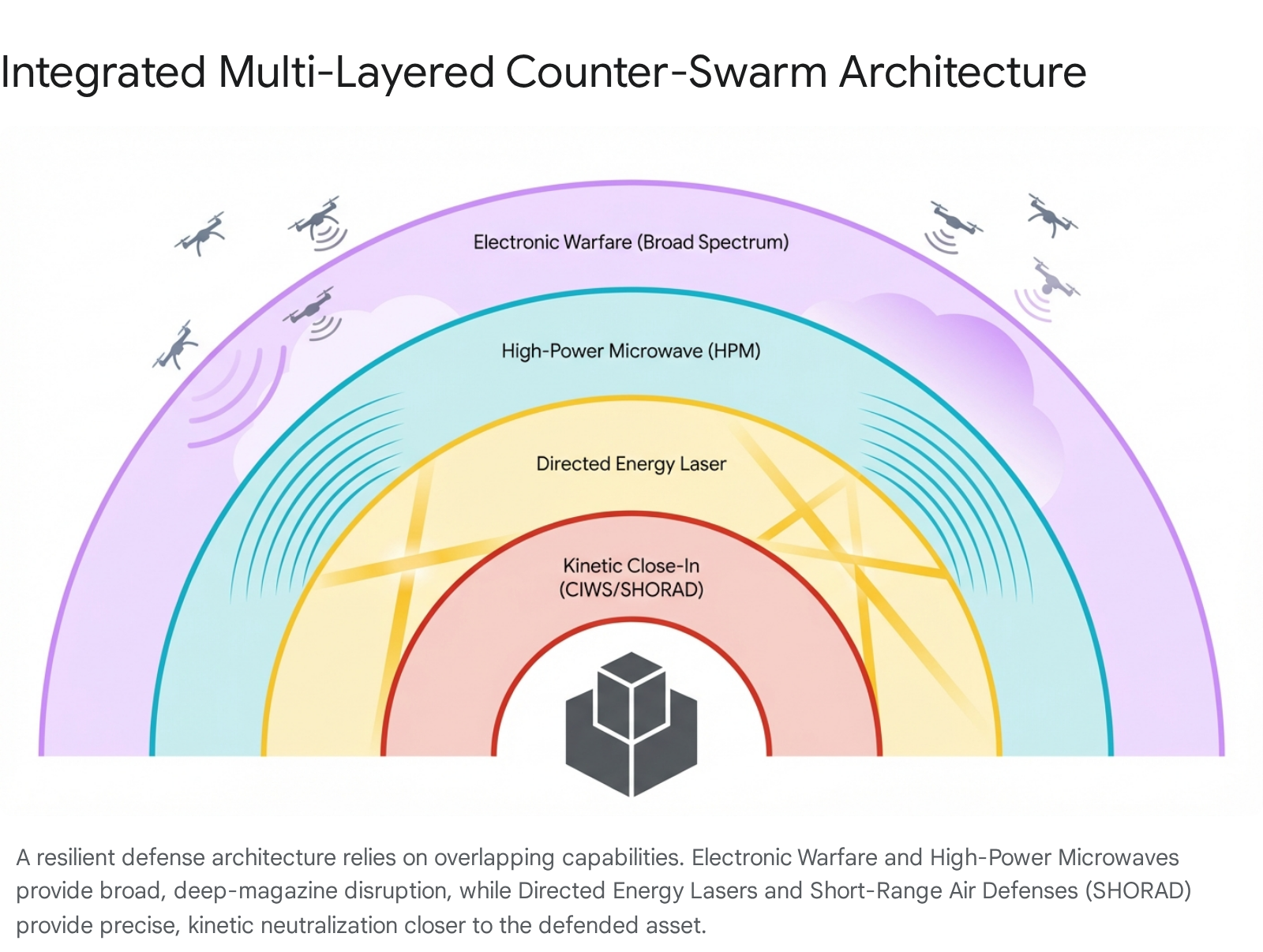
It must be explicitly understood that there is no single “silver bullet” technology capable of defeating the asymmetric threat of autonomous swarms.24 Exclusively relying on traditional kinetic air and missile defense leaves the joint force highly vulnerable to both physical saturation and economic exhaustion.41 Therefore, military strategy must decisively pivot toward a deep-magazine, multi-layered defensive architecture that seamlessly integrates cyber, electronic warfare (EW), directed energy weapons (DEW), and short-range kinetic interceptors.12
5.1 Reconstituting Short-Range Air Defense (SHORAD)
Decades of unrivaled air dominance following the Cold War led the U.S. Army to largely divest from its organic short-range air defenses, creating a massive, highly exploitable vulnerability at the tactical level.41 Defending forward operating bases and maneuvering forces requires the immediate reconstitution of SHORAD units. These units must be equipped with large stockpiles of high-volume, cost-effective kinetic interceptors.19 A reformed shot doctrine must dictate that these short-range interceptors are reserved explicitly for engagements against low-tier drones, rigorously preserving exquisite, multimillion-dollar missiles for high-value threats like cruise missiles and manned aircraft.19
5.2 Electronic Warfare (EW) as the Invisible Shield
EW represents the crucial first non-kinetic layer of the defensive architecture. By actively dominating the electromagnetic spectrum, defenders can intercept, analyze, and disrupt the navigation, communication, and command links of incoming drone swarms.25 Militaries are developing advanced capabilities, such as the conceptual Modular Electromagnetic Spectrum Deception Suite (MEDS), designed to create intense electromagnetic noise, reproduce the signatures of friendly units for deception, and saturate adversarial sensors and processing capabilities.38 Because EW effectors emit electromagnetic energy rather than expending physical munitions, they offer an infinite magazine depth and highly favorable cost-exchange ratios, crucial for neutralizing or “thinning the herd” of a massive, coordinated attack before it reaches kinetic range.44 However, analysts must recognize that as drones become fully autonomous, relying increasingly on machine vision and internal inertial navigation rather than external GPS or operator RF links, the efficacy of traditional EW jamming will naturally degrade, necessitating the activation of the next defensive layer.12
5.3 Directed Energy Weapons (DEW) and High-Power Microwave (HPM)
The most vital technological investment required to decisively counter the swarm threat is the rapid operationalization and fielding of directed energy capabilities. These systems provide near-instantaneous, light-speed engagement with a virtually unlimited magazine capacity (constrained only by power generation), dropping the cost of engagement to mere pennies or dollars per shot.12
Laser-Based DEWs: High-energy laser systems are highly effective for the precise, sequential targeting of individual drones, loitering munitions, and rocket artillery. They operate by thermally degrading the target’s structural integrity or blinding its optics, typically engaging effectively at ranges of 1 to 5 kilometers.12
High-Power Microwave (HPM): While lasers must engage targets one at a time, HPM systems represent the true counter-swarm capability. Weapons like the Epirus Leonidas and the Marine Corps’ newly delivered Expeditionary Directed Energy Counter-Swarm (ExDECS) do not rely on precision tracking of single targets. Instead, they emit broad, directed bursts of electromagnetic energy capable of instantly disabling the sensitive electronics of massive drone swarms across a wide area in a single engagement.11 Unlike kinetic fragmentation, modern HPM is heavily software-defined; its waveforms can be dynamically adjusted via AI to counter evolving adversarial shielding tactics, and it offers a low-to-no collateral damage profile, allowing intercepted drones to drop safely within pre-identified zones.11 Moving these HPM systems from prototype testing into formalized programs of record is an urgent strategic imperative that cannot be delayed.19
6. Procurement, the Defense Industrial Base, and the Reality of Scaling
The U.S. Defense Industrial Base (DIB) is fundamentally misaligned with the rapid production requirements of the modern threat environment. Following the Cold War, deep industrial consolidation and a commercial pivot toward just-in-time supply chains optimized the DIB for peacetime efficiency and the low-volume production of highly complex platforms. It was not optimized for the wartime mass, redundancy, or rapid surge capacity required today.48
6.1 The Friction of Transitioning to Attritable Systems
The strategic paradigm is shifting violently from procuring a small number of exquisite, heavily armored, multi-decade platforms to fielding thousands of attritable, autonomous systems designed to be expendable and rapidly replaceable.10 The DoD’s Project Replicator exemplifies this necessary ambition, aiming to field “multiple thousands” of all-domain attritable autonomous (ADA2) systems within an aggressive 18 to 24-month timeframe to directly counter Chinese military mass.50 A second iteration, Replicator 2, has already expanded the initiative to focus urgently on counter-UAS capabilities to protect critical installations.50
However, the bureaucratic “immune system” of defense procurement remains a formidable obstacle to this vision. Independent analysis of Replicator-related contract awards indicates that the average timeline from solicitation to first-article delivery remains approximately 19 months.10 While this technically falls within the original 24-month objective, it is only marginally faster than traditional, sluggish acquisition programs, indicating that Replicator may have met the letter of its mandate while failing to deliver the spirit of deep institutional transformation.10 In stark contrast, Ukrainian drone developers actively iterate and field entirely new systems within weeks based on real-time combat feedback.2 The U.S. acquisition apparatus, burdened by rigid capability requirements, extensive congressional oversight, and an aversion to risk, struggles immensely to adopt the commercial-first, iterative software-development pace necessary to dominate the low-cost autonomy space.10
6.2 Private Capital and the Valley of Death
Venture capital and private equity recognize the shifting paradigm and are pouring record funds into the defense sector. In 2025, venture capital investments exceeding $10 million in defense-focused companies grew dramatically, reaching more than $16 billion annually.54 Investors are placing massive bets on new entrants promising faster timelines, lower costs, and significant capability gains in AI and autonomous systems.54
Yet, this massive influx of private capital alone does not produce military readiness. The protracted defense development cycles and the notoriously treacherous path from successful prototype to scaled production—often referred to as the “Valley of Death”—threaten to stall this wave of innovation.54 Financial backers demand rapid, predictable returns, while the government relies on slow, episodic budgeting cycles and thin supplier networks.49 Without structural reforms to align acquisition pathways with commercial production realities, streamline Authority to Operate (ATO) processes, and provide sustained, multiyear demand signals, private investment will inevitably dry up before it translates into fielded capability at meaningful scale.49
6.3 Additive Manufacturing as a Scaling Mechanism
To achieve industrial speed and resilience, the DIB must embrace decentralized production methodologies. Additive manufacturing (industrial 3D printing) is emerging as a critical, strategic asset.55 With the U.S. Department of Defense’s FY 2026 budget request allocating $3.3 billion specifically for AM-related projects (an 83% increase from the previous year), the technology is moving from the periphery to the core of defense production.55 Additive manufacturing allows the military to bypass delinquent traditional product contracts, enabling the rapid, localized production of quick, limited-use components, munitions, and drone chassis directly at the point of need.55 It facilitates the critical transition from vulnerable, centralized mass production to resilient, point-of-origin manufacturing, significantly mitigating supply chain disruption risks.55
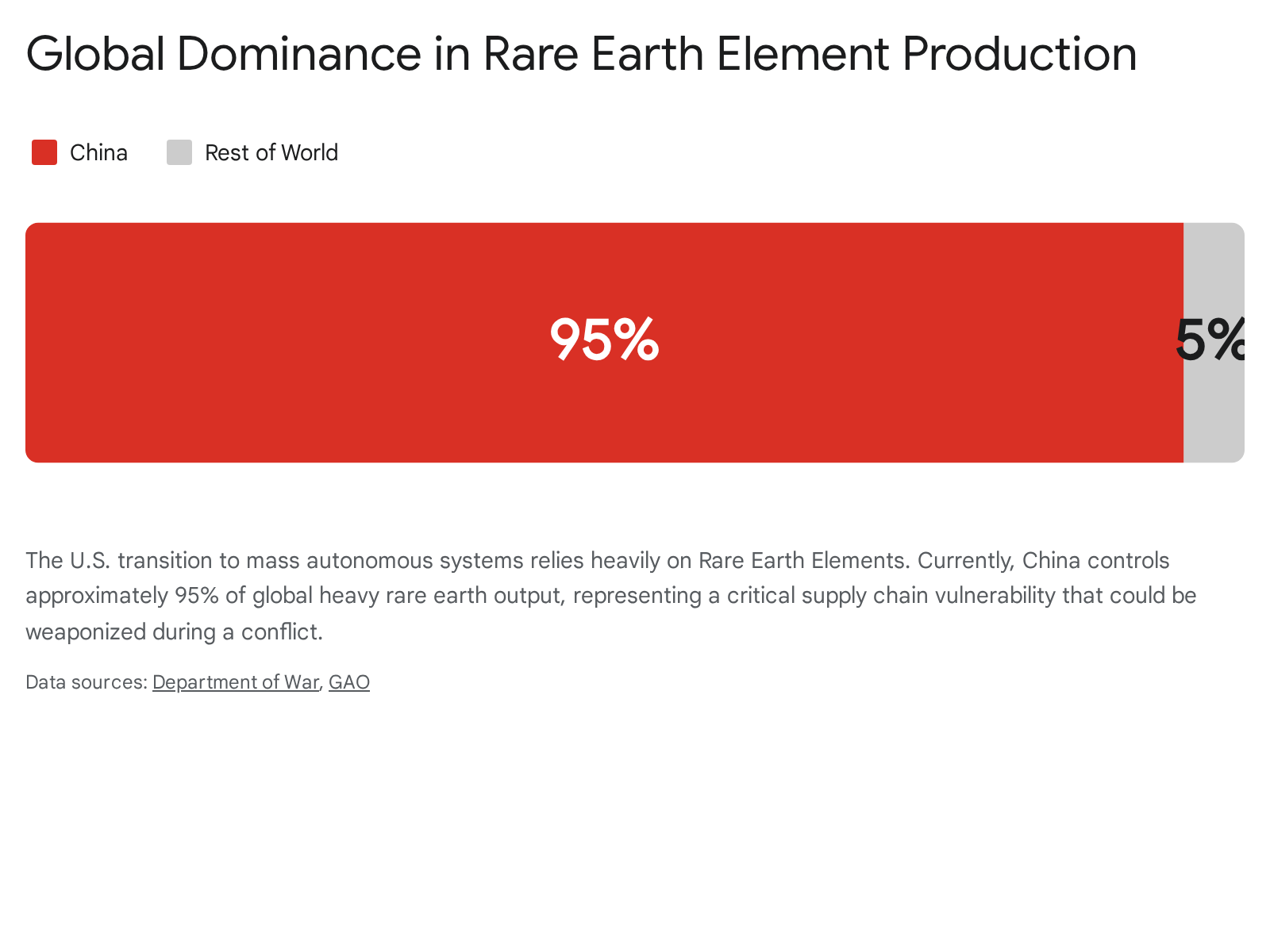
6.4 The Fragility of the Supply Chain: The Rare Earth Dilemma
A profound, systemic vulnerability underpinning the entire U.S. pivot to intelligent mass is the extreme fragility of the sub-tier supply chain, specifically regarding critical minerals and microelectronics. High-performance combat capabilities, drone propulsion motors, advanced optical sensors, and precision munitions all depend absolutely on a reliable supply of Rare Earth Elements (REEs), including gallium, antimony, and germanium.6
Currently, the United States is dangerously dependent on its primary strategic competitor for these materials. China controls approximately 95% of the global output of heavy rare earths.6 The U.S. imports almost 100% of the rare earths it consumes, with nearly three-quarters of those imports originating directly from China.6 This near-monopoly grants Beijing the unchecked capability to weaponize the supply chain, threatening to paralyze the U.S. defense industrial base and compromise military readiness instantly during a geopolitical crisis.6
While the DoD is taking steps to mitigate this by utilizing direct government intervention and public-private partnerships—such as a $400 million equity stake and $150 million debt investment in MP Materials to establish price floors and onshore refinement capabilities, alongside investments in Lithium Americas and Trilogy Metals—these efforts take years to mature.57 The immediate reality remains that scaling to millions of attritable drones requires foundational materials that the U.S. currently does not domestically control.9
7. The Logistical Realities of Million-Drone Armies
The stated ambition of the U.S. military to acquire millions of unmanned systems—marking a historic expansion of the drone force—forces a fundamental, ground-up redesign of strategic military logistics.58 The agility of modern warfare dictates that low-cost platforms should be moved quickly through R&D, procured rapidly, and then unhesitatingly discarded or expended as superior technologies emerge, closely mirroring the rapid evolution seen in early military aviation.59
This new “attritable mindset” fundamentally changes the logistical equation.58 The military logistics enterprise must forcefully pivot away from a sustainment model based on the complex, long-term maintenance of exquisite platforms. Exquisite sustainment requires deep, expensive inventories of proprietary spare parts, highly specialized mechanics, and secure, rear-echelon repair depots.58 Conversely, the new model must be optimized for rapid throughput, modular component replacement in the field, and the continuous delivery of high-volume consumables (such as drone batteries, commercial motors, and simple munitions).58
Sustaining a million-drone force without collapsing the supply lines requires automating the logistics tail itself. Initiatives like the Autonomous Transport Vehicle Systems (ATV-S), which aims to field heavy HEMTT PLS2 trucks equipped with built-in autonomy suites and collision avoidance, are vital.59 Projections indicate that automating these medium and heavy logistics trucks could increase sustainment throughput by up to 50%, ensuring that the insatiable material demands of a drone-saturated battlefield are met.59 Furthermore, the logistics network must be tightly integrated into a data-centric command and control structure. By leveraging advanced analytics and artificial intelligence, the Army Sustainment Enterprise (ASE) can utilize predictive logistics to preemptively manage the massive flow of attritable assets directly to the tactical edge, preventing human logisticians from being overwhelmed by the sheer scale of the resupply requirements.60
8. Strategic Recommendations for the Post-Exquisite Era
The transition to an era defined by extreme asymmetric threats and intelligent mass requires the Department of Defense to move aggressively beyond incremental modernization. A wholesale, structural restructuring of operational strategy, acquisition culture, and force design is imperative to maintain parity, let alone overmatch.
- Rebalance Force Structure Away from Capital Concentration: The U.S. military must critically and objectively assess the survivability and utility of its most capital-intensive platforms in a precise-mass environment. While aircraft carriers and heavy armor will retain specific, highly protected roles in global power projection, their inherent vulnerability to cheap, swarming munitions dictates that future budget allocations must heavily favor distributed, autonomous, and unmanned systems.20 Programs like the Air Force’s Collaborative Combat Aircraft (CCA)—which pairs relatively inexpensive autonomous drones with manned fighters for intelligence gathering and strike missions—must be accelerated and scaled, absorbing combat attrition without resulting in catastrophic strategic or financial failure.62
- Mandate Multi-Layered, Non-Kinetic Defense Deployments: The DoD must rapidly transition high-power microwave (HPM) and directed energy weapons (DEW) from the experimental testing phase to scaled, fully funded programs of record.19 Base defense, maritime protection, and mobile force protection must rely primarily on these non-kinetic systems to defeat massive drone swarms economically. Exquisite, multimillion-dollar kinetic interceptors must be strictly reserved, by updated doctrine, for high-tier threats like hypersonic glide vehicles, advanced ballistic missiles, and manned aircraft.19
- Restructure the Acquisition Bureaucracy for Software and Attritability: The monolithic acquisition process must be formally decoupled into separate, specialized tracks for hardware and software. Software procurement must be permitted to operate on commercial DevSecOps timelines, utilizing continuous Authorities to Operate (ATO) and adhering to Open DAGIR principles to ensure rapid iteration and cross-platform interoperability.33 For attritable hardware, the DoD must provide sustained, legally binding multiyear demand signals to private capital markets. Furthermore, procurement must prioritize manufacturers capable of modular design and point-of-origin additive manufacturing, aggressively reducing reliance on vulnerable, trans-Pacific rare earth supply chains.49
- Harden the Software-Defined Force Against DDIL Environments: The ambitious pursuit of JADC2 and cloud-enabled algorithmic warfare must be aggressively balanced with investments in edge computing capabilities.7 Weapon systems and autonomous platforms must be fundamentally designed to function semi-autonomously, seamlessly transitioning to localized processing and independent engagement protocols when the electromagnetic spectrum is denied by advanced cyber or electronic warfare.7
- Adapt Doctrine to the Mind-Tech Nexus: Military leadership must urgently update ethical and operational doctrines regarding delegated autonomous lethality. In true high-speed swarm environments, human-in-the-loop policies will result in operational paralysis and defeat.15 Doctrine must shift to permit human-on-the-loop or fully autonomous localized engagements governed by strict, pre-programmed rules of engagement (tactical autonomy contracts).26 Simultaneously, AI must be utilized to filter battlespace data, preventing debilitating cognitive overload in human commanders and ensuring they remain focused on broader strategic maneuver rather than micro-tactical execution.5
The United States military cannot out-spend the severe economic asymmetry of the modern battlefield, nor can it rely on the historical sanctuary of geographic distance. Victory in future conflicts will be determined not by the exquisite sophistication or unit cost of an individual weapon platform, but by the architectural resilience, software agility, and cognitive integration of a deeply distributed, logistically sustainable, massed force.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Sources Used
- On Optimism About New Military Technologies – Texas National Security Review, accessed April 8, 2026, https://tnsr.org/roundtable/on-optimism-about-new-military-technologies/
- The new economics of warfare – European Policy Centre (EPC), accessed April 8, 2026, https://www.epc.eu/publication/the-new-economics-of-warfare/
- First Ukraine, Now Iran: A New Era of Drone Warfare Takes Hold, accessed April 8, 2026, https://www.cfr.org/articles/the-new-era-of-drone-warfare-takes-root-in-iran
- Drones Aren’t Swarming Yet — But They Could – War on the Rocks, accessed April 8, 2026, https://warontherocks.com/2025/08/drones-arent-swarming-yet-but-they-could/
- (PDF) Cognitive Workload Considerations for Human-Machine Integrated Formations, accessed April 8, 2026, https://www.researchgate.net/publication/390799258_Cognitive_Workload_Considerations_for_Human-Machine_Integrated_Formations
- Securing Rare Earth Elements a National Security Imperative, Official Says – Department of War, accessed April 8, 2026, https://www.war.gov/News/News-Stories/Article/Article/4413490/securing-rare-earth-elements-a-national-security-imperative-official-says/
- Friction, Fog, and Failure in a Software-Defined Force – War on the Rocks, accessed April 8, 2026, https://warontherocks.com/2025/07/friction-fog-and-failure-in-a-software-defined-force/
- Cost and Value in Air and Missile Defense Intercepts – CSIS, accessed April 8, 2026, https://www.csis.org/analysis/cost-and-value-air-and-missile-defense-intercepts
- Critical Materials: Action Needed to Implement Requirements That Reduce Supply Chain Risks | U.S. GAO, accessed April 8, 2026, https://www.gao.gov/products/gao-24-107176
- The Pentagon’s Replicator Initiatives’ Real Challenge Is Cultural, Not Technical, accessed April 8, 2026, https://www.gotechinsights.com/blog/replicator
- A Counter to Drone Swarms: High-Power Microwave Weapons – DroneShield, accessed April 8, 2026, https://www.droneshield.com/blog/a-counter-to-drone-swarms-high-power-microwave-weapons
- DEFENCE SCIENCE REVIEW, accessed April 8, 2026, https://www.defencesciencereview.com.pl/pdf-216776-135052?filename=Laser-Based-Directed-Ener.pdf
- The Future of Defense Tech – Booz Allen, accessed April 8, 2026, https://www.boozallen.com/insights/defense/the-future-of-defense-tech.html
- Human, Machine, War: How the Mind-Tech Nexus will Win Future Wars – Department of War, accessed April 8, 2026, https://media.defense.gov/2025/Apr/18/2003694020/-1/-1/1/B-188%20HMW%20FINAL%204.8.25%20-%20WITH%20508%20CHECK.PDF
- Please Stop Saying ‘Human-In-The-Loop’ – Institute for Future Conflict (IFC), accessed April 8, 2026, https://ifc.usafa.edu/articles/please-stop-saying-human-in-the-loop
- Autonomous Weapon Systems: No Human-in-the-Loop Required, and Other Myths Dispelled – War on the Rocks, accessed April 8, 2026, https://warontherocks.com/2025/05/autonomous-weapon-systems-no-human-in-the-loop-required-and-other-myths-dispelled/
- Killing Sanctuary: The Coming Era of Small, Smart, Pervasive Lethality – War on the Rocks, accessed April 8, 2026, https://warontherocks.com/2017/09/killing-sanctuary-the-coming-era-of-small-smart-pervasive-lethality/
- MITCHELL INSTITUTE Policy Paper, accessed April 8, 2026, https://www.mitchellaerospacepower.org/app/uploads/2026/02/Strategic_Attack_Denying_Sanctuary_Policy_Paper_64.pdf
- CNAS Report Finds U.S. Military Unprepared for Drone Threat | CNAS, accessed April 8, 2026, https://www.cnas.org/press/press-release/cnas-report-finds-u-s-military-unprepared-for-drone-threat
- The Future of Seapower – CSIS, accessed April 8, 2026, https://www.csis.org/analysis/chapter-11-future-seapower
- The Future of The Future of Aircraft Carriers – U.S. Naval War College Digital Commons, accessed April 8, 2026, https://digital-commons.usnwc.edu/cgi/viewcontent.cgi?article=1551&context=nwc-review
- AI is Shaping the Future of War – NDU Press, accessed April 8, 2026, https://ndupress.ndu.edu/Media/News/News-Article-View/Article/2846375/ai-is-shaping-the-future-of-war/
- The Economics of Modern Warfare: Cost–Benefit Dynamics Between Shahed drone and Air Defense Interceptors – Fatuma’s Voice, accessed April 8, 2026, https://fatumasvoice.org/283364/
- COUNTERING THE SWARM – Amazon S3, accessed April 8, 2026, https://s3.us-east-1.amazonaws.com/files.cnas.org/documents/Report_CUAS_Defense_Sep-2025_final.pdf
- Electronic Warfare vs. Directed Energy: Which C-UAS Approach Wins the Scaling War?, accessed April 8, 2026, https://www.dronesense.ai/electronic-warfare-vs-directed-energy-which-c-uas-approach-wins-the-scaling-war-2/
- AI-Driven Swarm Control: The future of drone warfare | Thales Group, accessed April 8, 2026, https://www.thalesgroup.com/en/news-centre/insights/defence/land/ai-driven-swarm-control-future-drone-warfare
- Brain-Computer Interfaces: U.S. Military Applications and Implications, An Initial Assessment – RAND, accessed April 8, 2026, https://www.rand.org/content/dam/rand/pubs/research_reports/RR2900/RR2996/RAND_RR2996.pdf
- Reality in Autonomous Systems: It starts the Loop | The Cove – Australian Army, accessed April 8, 2026, https://cove.army.gov.au/article/reality-autonomous-systems-it-starts-loop
- Cheap Drones, Expensive Lessons: Ethics, Innovation, and Regulation of Autonomous Weapon Systems – The Henry M. Jackson School of International Studies, accessed April 8, 2026, https://jsis.washington.edu/news/cheap-drones-expensive-lessons-ethics-innovation-and-regulation-of-autonomous-weapon-systems/
- Unleashing Drone Dominance: Rethinking Department of Defense Weapons Reviews, accessed April 8, 2026, https://lieber.westpoint.edu/unleashing-drone-dominance-rethinking-department-defense-weapons-reviews/
- Atlantic Council Commission on Software-Defined Warfare: Final …, accessed April 8, 2026, https://www.atlanticcouncil.org/in-depth-research-reports/report/atlantic-council-commission-on-software-defined-warfare/
- DOD Needs to Modernize its Software Architecture for Next-Gen Warfare, Report Says, accessed April 8, 2026, https://www.nextgov.com/modernization/2022/09/dod-needs-modernize-its-software-architecture-next-gen-warfare-report-says/376893/
- A Blueprint for Digital Transformation at the Department of Defense, accessed April 8, 2026, https://warontherocks.com/2025/01/a-blueprint-for-digital-transformation-at-the-department-of-defense/
- Shaping the future of defence through software | HENSOLDT, accessed April 8, 2026, https://www.hensoldt.net/insights/shaping-the-future-of-defence-through-software-interview-with-sven-heursch
- The Pentagon’s Software Revolution and Its Testing Dilemma – War on the Rocks, accessed April 8, 2026, https://warontherocks.com/2025/09/the-pentagons-software-revolution-and-its-testing-dilemma/
- Achieving Spectrum Dominance by Defeating the EW Kill Chain: Sponsored Content, accessed April 8, 2026, https://www.afcea.org/signal-media/achieving-spectrum-dominance-defeating-ew-kill-chain-sponsored-content
- Reimagining Contested Communications – Modern War Institute -, accessed April 8, 2026, https://mwi.westpoint.edu/reimagining-contested-communications/
- Modern Electromagnetic Spectrum Battlefield – NDU Press – National Defense University, accessed April 8, 2026, https://ndupress.ndu.edu/Media/News/News-Article-View/Article/2846737/modern-electromagnetic-spectrum-battlefield/
- How NATO can integrate AI to prevail in future algorithmic warfare – Atlantic Council, accessed April 8, 2026, https://www.atlanticcouncil.org/in-depth-research-reports/report/how-nato-can-integrate-ai-to-prevail-in-future-algorithmic-warfare/
- What Are Asymmetric Strategies? D O C U M E N T E D B R I E F I N G – RAND, accessed April 8, 2026, https://www.rand.org/content/dam/rand/pubs/documented_briefings/2005/DB246.pdf
- CNAS Insights | America Isn’t Ready for a Drone War, accessed April 8, 2026, https://smallwarsjournal.com/2026/02/23/cnas-insights-america-isnt-ready-drone-war/
- Counter UAS for Drone Defense and National Security – Lockheed Martin, accessed April 8, 2026, https://www.lockheedmartin.com/en-us/capabilities/counter-unmanned-aerial-systems.html
- Spectrum superiority: Electronic warfare and future conflict – TRENDS Research & Advisory, accessed April 8, 2026, https://trendsresearch.org/insight/spectrum-superiority-electronic-warfare-and-future-conflict/
- DoD Electromagnetic Spectrum Superiority Strategy 2020 – Department of War, accessed April 8, 2026, https://media.defense.gov/2020/Oct/29/2002525927/-1/-1/0/electromagnetic_spectrum_superiority_strategy.pdf
- GOVERNMENT PERSPECTIVE: Directed Energy in Air Base Defense Can Save the Arsenal, accessed April 8, 2026, https://www.nationaldefensemagazine.org/articles/2025/8/11/government-perspective-directed-energy-in-air-base-defense-can-save-the-arsenal
- Marines Get Their First High Power Microwave Weapon For Taking On Drone Swarms, accessed April 8, 2026, https://www.twz.com/land/marines-get-their-first-high-power-microwave-weapon-for-taking-on-drone-swarms
- Epirus’ Leonidas High-Power Microwave Defeats 49-Drone Swarm, 100% of Drones Flown at Live-Fire Demonstration, accessed April 8, 2026, https://www.epirusinc.com/press-releases/epirus-leonidas-high-power-microwave-defeats-49-drone-swarm-100-of-drones-flown-at-live-fire-demonstration
- Rogers: Revitalizing the Defense Industrial Base Is Our Top Priority This Year, accessed April 8, 2026, https://armedservices.house.gov/news/documentsingle.aspx?DocumentID=6411
- An Era of Global Rearmament and the U.S. Defense Industrial Base – JPMorgan Chase, accessed April 8, 2026, https://www.jpmorganchase.com/content/dam/jpmorganchase/documents/center-for-geopolitics/jpmc-cfg-us-dib-v4-ada-remediated.pdf
- Pentagon’s Replicator Initiative Sets Sights on Counter-UAS – National Defense Magazine, accessed April 8, 2026, https://www.nationaldefensemagazine.org/articles/2024/12/16/pentagons-replicator-initiative-sets-sights-on-counteruas
- Is Replicator Replicable? | The Belfer Center for Science and International Affairs, accessed April 8, 2026, https://www.belfercenter.org/research-analysis/replicator-replicable
- Joint Interagency Task Force Announces First Replicator 2 Purchase to Counter Homeland Drone Threats – Department of War, accessed April 8, 2026, https://www.war.gov/News/News-Stories/Article/Article/4377021/joint-interagency-task-force-announces-first-replicator-2-purchase-to-counter-h/
- Pentagon Efforts to Boost Industrial Base Not Moving Needle Yet, accessed April 8, 2026, https://www.airandspaceforces.com/pentagon-industrial-base-reforms-report/
- Will private capital and disruption reshape the defense industrial base?, accessed April 8, 2026, https://breakingdefense.com/2026/04/will-private-capital-and-disruption-reshape-the-defense-industrial-base/
- The Expanding Role of Additive Manufacturing in the Defense Industrial Base, accessed April 8, 2026, https://www.rapid3devent.com/event/news/the-expanding-role-of-additive-manufacturing-in-the-defense-industrial-base/
- Air Force Global Futures Report, accessed April 8, 2026, https://www.af.mil/Portals/1/documents/2023SAF/Air_Force_Global_Futures_Report.pdf
- Washington Goes Shopping: Investing Its Way Out of the Rare Earth Crisis – Defense Security Monitor, accessed April 8, 2026, https://dsm.forecastinternational.com/2025/10/14/washington-goes-shopping-investing-its-way-out-of-the-rare-earth-crisis/
- US Army Plans to Acquire One Million Drones, Marking a Historic Expansion – Dronelife, accessed April 8, 2026, https://dronelife.com/2025/11/08/us-army-plans-to-acquire-one-million-drones-marking-a-historic-expansion/
- Report: What Unmanned Systems is America’s Military Buying in 2026?, accessed April 8, 2026, https://insideunmannedsystems.com/report-what-unmanned-systems-is-americas-military-buying-in-2026/
- currentissue.pdf – Army Sustainment University, accessed April 8, 2026, https://alu.army.mil/alog/currentissue.pdf
- Artificial Intelligence and Future Warfare | Hudson Institute, accessed April 8, 2026, https://www.hudson.org/defense-strategy/artificial-intelligence-future-warfare
- Air Force wants almost $1B to buy first CCA drones in 2027 | DefenseScoop, accessed April 8, 2026, https://defensescoop.com/2026/04/06/air-force-wants-to-procure-first-cca-drones-in-2027/
