Executive Summary
The final week of January 2026 marks a strategic pivot point for the People’s Republic of China (PRC), characterized by the most aggressive consolidation of military authority under President Xi Jinping since the 20th Party Congress. The dominant development of the reporting period is the systemic purge of the Central Military Commission (CMC), notably the investigation of Vice Chairman Zhang Youxia and General Liu Zhenli, which has effectively hollowed out the professional leadership of the People’s Liberation Army (PLA).1 This internal restructuring occurs against a backdrop of heightened regional tension, underscored by a historic drone incursion over Taiwanese-administered Pratas Island and the deployment of massive maritime militia “floating barriers” in the East China Sea.3
On the diplomatic front, Beijing has executed a sophisticated “thaw” in its relations with Western Europe, utilizing the official visit of UK Prime Minister Keir Starmer to secure a range of economic and security agreements. These outcomes, including visa-free travel for UK nationals and a reduction in whisky tariffs, reflect a tactical effort to decouple European economic interests from the more confrontational posture of the United States.5 Concurrently, China has reached a milestone of 35% self-sufficiency in semiconductor manufacturing equipment, bolstered by domestic breakthroughs in high-energy ion implantation and the scaling of 28nm lithography to 7nm yields.8
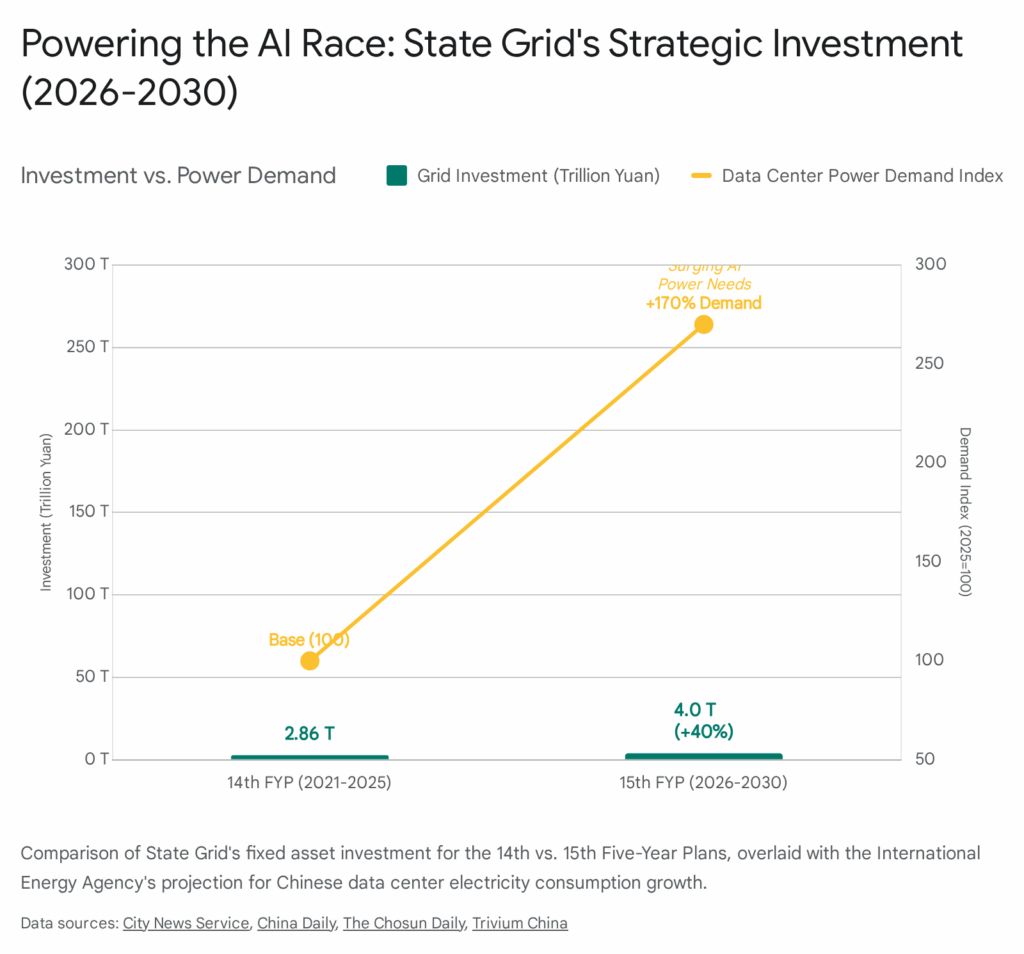
Internal stability remains a primary concern for the Chinese Communist Party (CCP). Economic grievances—driven by unpaid wages, real estate defaults, and rising underemployment—fueled over 5,000 recorded protests in the preceding year.10 The state has responded with the implementation of a rigorous new cybersecurity regime and the deployment of quantum-enabled intelligence tools designed to monitor and neutralize dissent before it reaches a point of geographic contagion.12 As China enters the first year of the 15th Five-Year Plan (2026-2030), the interplay between radical internal purges, technological indigenization, and grey-zone military escalation defines the current strategic landscape.
1. Leadership and Party Governance: The Final Consolidation
The reporting week has witnessed a fundamental transformation of the PRC’s high command. On January 24, 2026, the Ministry of National Defense confirmed that General Zhang Youxia, Vice Chairman of the CMC, and General Liu Zhenli, Chief of the CMC Joint Staff Department, are under “open investigation” for serious violations of discipline and law.1 This development is not merely an extension of the ongoing anti-corruption campaign but represents a decisive move to eliminate the last vestiges of independent professional military leadership within the CCP.16
1.1. The Purge of the Central Military Commission
The removal of Zhang Youxia is particularly significant due to his long-standing personal ties to Xi Jinping. Both men are “princelings” whose fathers served together during the Chinese Civil War.17 Zhang was seen as Xi’s primary enforcer within the military and one of the few remaining leaders with actual combat experience from the Sino-Vietnamese conflicts of the 1980s.2 The official indictment, circulated through the Liberation Army Daily, accuses the generals of “seriously trampling upon the CMC Chairman Responsibility System,” a clear signal that they were perceived as obstructing Xi’s absolute control or building independent factional networks.1
| CMC Member | Status (as of Jan 31, 2026) | Significance of Removal |
| Xi Jinping | Chairman (Active) | Absolute centralized command 2 |
| Zhang Youxia | Vice Chairman (Purged) | Highest-ranking professional soldier; combat veteran 1 |
| He Weidong | Vice Chairman (Purged Oct 2025) | Former enforcer; replaced by discipline official 16 |
| Liu Zhenli | CMC Member (Purged) | Operational lead for Joint Staff; liaison to Western militaries 1 |
| Zhang Shengmin | CMC Member (Active) | Top discipline and anti-corruption official 15 |
The purge has reduced the CMC from its traditional seven-member structure to just two active members: Xi Jinping and the discipline chief Zhang Shengmin.2 Intelligence analysts suggest that this “clearing of the slate” is an anticipatory move ahead of the 21st National Congress in 2027. By removing senior generals who could serve as alternative power centers or question succession plans, Xi has ensured that the military will not emerge as an independent political actor during a potentially tense transition period.1 However, this hollowing out of the command structure introduces extreme operational risk. The loss of Zhang Youxia, who was a key figure in military-to-military dialogues with the United States, significantly undermines the prospects for strategic stability and increases the likelihood of miscalculation during regional crises.2
1.2. Law-Based Governance and 2026 Economic Directives
Parallel to the military reshuffle, the Political Bureau of the CPC Central Committee held a critical meeting on January 26 to finalize economic work for 2026 and review new regulations on “law-based governance”.19 The meeting emphasized that 2026 is a year of “significance in the process of advancing Chinese modernization,” marking the launch of the 15th Five-Year Plan.19 The leadership has committed to a “more proactive fiscal policy” alongside a “moderately loose monetary policy,” signaling a shift toward aggressive stimulus to counter persistent deflationary pressures and a fragile property sector.19
The new regulations on law-based governance are intended to institutionalize the Party’s leadership over the legal system at a “higher stage”.19 This involves integrating Party directives directly into judicial and administrative processes, further eroding the distinction between the CCP and the state. The meeting also underscored the necessity of “bottom-line thinking” to defuse risks in key areas, a reference to the escalating debt problems of local governments and the systemic vulnerabilities of the banking sector.19
1.3. The 2026 Anti-Corruption Framework
On January 25, the Political Bureau met to plan the Party’s efforts to “improve conduct and build integrity” for the coming year.21 Xi Jinping presided over the session, which characterized the 2025 anti-corruption drive as a success but warned that “full and rigorous Party self-governance” must advance with higher standards in 2026.21 This directive serves as a mandate for continued purges within the civil service and the military, particularly targeting officials involved in the procurement of high-tech equipment and those overseeing the 15th Five-Year Plan’s capital-intensive projects.20 The emphasis on “self-revolution” suggests that the CCP leadership views perpetual internal cleansing as the only mechanism to prevent the “Evergrande-style” contagion from affecting the Party’s governing efficiency.20
2. Foreign Affairs and Diplomatic Re-engagement
During the reporting week, Beijing has prioritized “shuttle diplomacy” and high-level bilateral engagements to counter what it perceives as a Western attempt to form a unified containment bloc. The centerpiece of this effort was the official visit of UK Prime Minister Keir Starmer, which signals a tactical shift in China’s European policy.5
2.1. The China-UK “Strategic Thaw”
Prime Minister Starmer’s visit from January 28 to 31 is the first by a UK head of government in eight years.5 The visit was framed by the PRC Ministry of Foreign Affairs as an opportunity to “open a new chapter” in a relationship that had been characterized by “ice ages” in recent years.6 President Xi Jinping and Premier Li Qiang engaged in intensive negotiations that resulted in 12 intergovernmental cooperation documents and a commitment to a “long-term and consistent comprehensive strategic partnership”.5
| Agreement Area | Specific Outcome | Strategic Implication |
| Visa Policy | 30-day visa-free travel for UK nationals | Encourages direct business and cultural engagement; aligns UK with EU partners like France/Germany 6 |
| Trade | Whisky tariffs reduced from 10% to 5% | Direct concession to a key UK export sector; signals openness to further trade liberalization 5 |
| Security | Resumption of high-level security dialogue | Re-establishes communication on counter-terrorism and regional stability 5 |
| Intelligence | Joint efforts against organized crime and small boat migration | Pragmatic cooperation on UK domestic priorities (e.g., stopping small boat engines manufactured in China) 6 |
| Finance | Establishment of China-UK Financial Working Group | Deepens integration of London as an offshore RMB clearing hub 5 |
| Climate | High-level China-UK climate and nature partnership | Focuses on shared global challenges as a “soft” area for continued engagement 5 |
These agreements demonstrate a calibrated PRC strategy to use economic “carrots” to influence the UK’s geopolitical positioning. By offering 30-day visa-free travel, Beijing aims to bring the UK into its “visa-free circle,” which now includes over 50 countries.6 Furthermore, the reduction in whisky tariffs and the agreement to conduct a feasibility study for a services trade agreement are designed to appeal to the UK’s core economic strengths.6 For Beijing, the primary goal is to prevent the UK from fully aligning with the United States on technology restrictions and security guarantees for Taiwan.6
2.2. Northeast Asia: The China-Japan-South Korea Triangle
In Northeast Asia, the diplomatic landscape remains fraught with tension, primarily centered on the “existential” crisis in the Taiwan Strait. South Korean President Lee Jae-myung conducted a series of state visits to Beijing (January 4-6) and Nara, Japan (January 13-14), attempting to act as a regional mediator.27 While Beijing provided Lee with the “highest level of protocol,” Xi Jinping utilized the summit to urge South Korea to “stand on the right side of history” and “defend the fruits of victory in World War II,” a clear reference to historical grievances against Japan.28
The relationship between China and Japan has deteriorated into a state of active crisis. Prime Minister Sanae Takaichi’s remarks that a Chinese attack on Taiwan would constitute an “existential crisis for Japan” have prompted a multi-front retaliation from Beijing.29
- Export Controls: On January 6, China announced a ban on the export of over 800 “dual-use” goods to Japan, including critical rare earth materials and minerals essential for high-tech manufacturing.29
- Diplomatic Protests: China summoned the Japanese ambassador to protest Takaichi’s remarks, while the Chinese consul general in Osaka made threatening comments on social media.30
- Economic Coercion: Beijing has reimposed bans on Japanese seafood and implemented unofficial restrictions on Japanese entertainment products.29
South Korea finds itself “sandwiched” between these two powers. While President Lee has sought to restore “balance” to Korean foreign policy, his government remains cautious, reaffirming its commitment to the One China policy in Beijing while simultaneously deepening security ties with Japan in Nara.27 The “shuttle diplomacy” initiated by Lee has achieved limited success in de-escalating the China-Japan rift, as Beijing continues to use its relationship with Seoul as a wedge to isolate Tokyo.28
2.3. Outreach to Global Partners
Beyond the major powers, China has hosted a series of visits from leaders of smaller nations, reflecting its broader strategy to solidify support among the Global South and “middle powers.”
- Azerbaijan: Foreign Minister Jeyhun Bayramov visited Beijing on January 28-29, focusing on connectivity projects under the Belt and Road Initiative (BRI).22
- Uruguay: President Yamandú Orsi visited on January 26 to discuss agricultural trade and a potential free trade agreement.33
- Finland: Prime Minister Petteri Orpo concluded a visit in late January, with discussions centered on “friendly ties” and “mutual respect,” despite EU-wide tensions regarding China’s role in the Ukraine crisis.33
- APEC 2026: China has announced it will host the first APEC senior officials’ meeting in Guangzhou from February 1 to 10, themed “Building an Asia-Pacific Community to Prosper Together”.35 This serves as an early platform for China to set the regional economic agenda for its host year.
3. Military Strategy and Tactical Readiness
The PLA’s operational activities in the final week of January 2026 indicate a shift from large-scale exercises to targeted provocations and the testing of new asymmetric capabilities. This follows the massive “Justice Mission 2025” blockade exercise conducted in late December.36
3.1. Airspace Violations and Pratas Island
On January 17, 2026, the PLA flew a surveillance drone through Taiwanese territorial airspace over Pratas (Dongsha) Island.3 Intelligence analysts believe this is the first confirmed violation of Taiwan’s 12-nautical-mile territorial airspace by a PLA aircraft in decades.3
- Tactical Intent: The incursion appears designed to test Taiwan’s response to an unambiguous violation of its sovereignty without triggering a full-scale military escalation. Pratas is a remote outpost with no civilian population, making it a “soft” target for testing thresholds.3
- Erosion of Awareness: By normalizing such incursions, the PLA aims to degrade the Taiwanese military’s threat awareness, complicating its ability to identify the transition from “routine” grey-zone activity to an actual assault.3
- Legal Signaling: The flight serves to assert PRC sovereignty over the entire South China Sea and the Taiwan Strait, challenging the legitimacy of the median line and Taiwan’s Air Defense Identification Zone (ADIZ).3
3.2. Integration of the “Maduro Model” for Decapitation Strikes
An emerging theme in PLA training is the adaptation of tactical lessons from recent U.S. special operations. The PLA has reportedly integrated lessons from the U.S. operation to capture Venezuelan President Nicolas Maduro on January 3 into its planning for Taiwan.3
Recent exercises have simulated “decapitation strikes” against political leadership, focusing on:
- Special Operations Forces (SOF): Practicing the clearance of target buildings and the elimination of “terrorists” (a standard euphemism in PLA drills for opposing political figures).3
- Electronic Warfare (EW): Utilizing the J-16’s EW pods to suppress enemy air defense radars, a capability directly compared to the EA-18 Growler used in the Venezuela raid.3
- Rapid Insertion: Rehearsing helicopter-borne raids and the use of “surprise weapons” like uncrewed helicopters and swarm drones to paralyze Taipei’s decision-making apparatus.38
While analysts at the Institute for the Study of War (ISW) note that a decapitation strike is unlikely to succeed without the support of a large-scale invasion, the PLA’s focus on these capabilities suggests a desire to achieve a “quick win” that could force a Taiwanese capitulation before international intervention can materialize.3
3.3. Maritime Militia and “Floating Barriers”
The role of the People’s Armed Forces Maritime Militia (PAFMM) has been significantly elevated in recent months. Between January 9 and 12, approximately 1,400 Chinese fishing vessels mobilized into a 200-mile-long “barrier” in the East China Sea for over 30 hours.4
| Date | Location | Scale | Formation |
| Dec 25-27, 2025 | NE of Taiwan | 2,000 vessels | Reverse L-shape; 290 miles 3 |
| Jan 9-12, 2026 | East China Sea | 1,400 vessels | 200-mile barrier 3 |
These “floating walls” demonstrate a high level of coordination and serve multiple military functions:
- Navigation Blockade: Physically obstructing shipping lanes and naval access to key ports.4
- Reconnaissance: Providing a dense network of sensors to monitor adversary naval movements.4
- Saturation: Overwhelming enemy sensors and creating “too many targets” for defensive systems to track effectively during a conflict.4
- Political Signaling: Demonstrating the PLA’s ability to mobilize civilian resources for military ends, particularly as a show of force against Japan following Prime Minister Takaichi’s comments.3
3.4. New Technology Unveilings
The January military parade in Beijing provided the first public viewing of several next-generation systems intended to project power and deter U.S. intervention.39
- Hypersonic Anti-Ship Missiles: The YJ-15, YJ-17, YJ-19, and YJ-20 were showcased, all capable of hypersonic speeds, making them extremely difficult for carrier-based Aegis systems to intercept.39
- Strategic Nuclear Forces: The DF-61, a new intercontinental ballistic missile (ICBM) launched from mobile platforms, and the DF-5C, a silo-based ICBM with an estimated range of 20,000 kilometers, were debuted.39
- Uncrewed Systems: The AJX002 submarine drone was unveiled, described as a “cutting-edge surprise weapon” for covert blockade and swarm-networked attacks.39
- Stealth Fighters: The carrier-based version of the J-35 stealth multirole fighter was presented, signaling the maturing of China’s naval aviation capability.39
4. The Economic Battleground: Semiconductor Sovereignty
A historic milestone was reached in January 2026 as China officially attained 35% self-sufficiency in semiconductor manufacturing equipment.8 This surge—up from 25% two years ago—represents a decisive shift in the technological landscape and suggests that Beijing’s strategy of “indigenization” is beginning to overcome Western export controls.8
4.1. Technical Breakthroughs in “Chokepoint” Technologies
The reporting period featured several key announcements from state institutions and private-sector champions regarding the localization of core chipmaking tools.
- High-Energy Ion Implantation: The China National Nuclear Corporation (CNNC) and the China Institute of Atomic Energy validated the Power-750H, China’s first domestically produced tandem-type high-energy hydrogen ion implanter.8 This tool is essential for “doping” silicon wafers to produce power semiconductors like Insulated-Gate Bipolar Transistors (IGBTs), which are the “heart” of electric vehicles (EVs) and renewable energy systems.8 This breakthrough effectively ends China’s total reliance on Western firms like Applied Materials for this critical stage of production.8
- DUV Lithography Scaling: Shanghai Micro Electronics Equipment (SMEE) has scaled its SSA800 series, 28nm Deep Ultraviolet (DUV) machines, which are now in full-scale production.8 Major foundries like SMIC are reportedly using multi-patterning techniques with these domestic tools to achieve 7nm and even 5nm yields, providing the necessary processing power for AI accelerators and high-end consumer electronics.8
- EUV Prototype: Huawei and a consortium in Shenzhen have validated a functional Extreme Ultraviolet (EUV) lithography prototype using Laser-Induced Discharge Plasma (LDP) technology.8 While commercial-grade tools are not expected until 2028, this development represents a radical departure from Western optical designs and could allow China to bypass existing patent barriers.8
4.2. Market Dynamics and Corporate Maneuvers
The push for self-sufficiency has triggered a wave of initial public offerings (IPOs) and structural reorganizations among Chinese chipmakers.
- Moore Threads: The AI chipmaker, which aims to rival Nvidia, reportedly tripled its revenue in 2025.41
- Alibaba and Baidu: Both tech giants have announced plans to spin off their semiconductor units as independent listings to capitalize on the “enthusiasm for locally made processors”.41
- Strategic Investment: Amazon is reportedly considering a $50 billion investment in OpenAI, which has driven massive interest in the AI inference market.42 China is responding by accelerating its own inference-focused chips, such as the upcoming products from Moore Threads, to capture this burgeoning sector.41
4.3. Response to External Pressures
Despite the flexible licensing policy for Nvidia H200 chips announced by the Trump administration on January 15, the Chinese government has reportedly instructed domestic firms to stop using cybersecurity software from U.S. and Israeli companies like CrowdStrike and Palo Alto Networks.43 This “software ban” is a direct response to U.S. restrictions on Chinese-made software and hardware and reflects a broader effort to purge foreign technology from sensitive networks.44
| U.S. Action (Jan 2026) | Chinese Response | Strategic Result |
| BIS Rule formalizing license for H200 chips 43 | Instruction to stop using US/Israeli security software 44 | Symmetrical “decoupling” in high-trust sectors |
| 25% Tariff on advanced chip imports 43 | Accelerated funding for “Power-750H” and SMEE SSA800 8 | Incentivizing local tool adoption via cost-matching |
| Annual approval for US tools in foreign-owned fabs 46 | Expansion of 28nm-to-7nm multi-patterning yields 8 | Utilizing “mature” nodes for “advanced” outcomes |
5. Cyber, Intelligence, and Internal Security
The domestic security landscape in January 2026 is defined by a rigorous new legal framework and the deployment of advanced surveillance technologies aimed at maintaining “regime security” above all else.11
5.1. The Amended Cybersecurity Law (CSL)
The amended CSL, which took effect on January 1, 2026, marks the most significant tightening of China’s cyber regime in a decade.12
Key Reporting and Enforcement Mechanisms:
- Compressed Timelines: Critical Information Infrastructure Operators (CIIOs) must report “relatively major” incidents within one hour.14
- Increased Penalties: Fines for CIIOs have been raised to a maximum of RMB 10 million (approx. $1.4 million) for violations that result in “especially grave” consequences.12
- Extraterritorial Scope: The law now applies to any activity overseas that endangers PRC cybersecurity. This provides a legal basis for the Ministry of Public Security to freeze the assets of foreign organizations or individuals deemed to have “smeared” China or engaged in digital sabotage.12
- AI Governance: Article 20 of the amended law formally embeds AI governance into national security legislation, mandating that the state support the development of “secure and controllable” AI while strengthening ethical norms.47
5.2. Quantum Warfare and Intelligence Gathering
The PLA confirmed in mid-January that it is testing over 10 experimental quantum cyber warfare tools in front-line missions.13 These tools, developed by the National University of Defense Technology, are designed to:
- Process Battlefield Data: Analyzing massive volumes of intelligence in seconds to enhance decision-making.13
- Intelligence Extraction: Gathering high-value data from public cyberspace that conventional computing methods cannot process efficiently.13
- Counter-Stealth: Utilizing quantum sensing to detect aircraft and vessels that utilize traditional stealth technologies.13
This development aligns with China’s broader “Quantum Technology Strategy,” which has seen over $15 billion in public funding since 2018.13 While the U.S. maintains a lead in certain areas of quantum computing, China has established clear dominance in quantum-secure communications and scientific research volume.52
5.3. Cyberattacks on Taiwan’s Critical Infrastructure
Taiwan’s National Security Bureau (NSB) released a report on January 4 documenting an “unprecedented” scale of Chinese cyber operations in 2025.53
- Volume: An average of 2.63 million intrusion attempts per day, a 6% increase from the previous year.53
- Coordination: 23 of the 40 major PLA military maneuvers in 2025 were closely synchronized with cyber escalations.53
- Targeting: A 1,000% spike in attacks targeting the energy sector, indicating a shift from passive intelligence gathering to “active operational preparation of the environment”.53
- Techniques: The persistent use of “living off the land” (LOTL) tactics by groups such as Flax Typhoon, which leverage built-in system tools to perform malicious actions without installing external malware, making detection extremely difficult.53
6. Social Stability and Internal Grievances
Despite the extensive security apparatus, economic strain has led to a surge in public dissent. The China Dissent Monitor recorded over 5,000 incidents in 2025, with economic grievances motivating 85% of these protests.10
6.1. The Geography and Drivers of Unrest
Protests have been observed in both bustling urban centers like Shenzhen and smaller provincial cities like Jiangyou.10 The primary drivers include:
- Wage Theft: Unpaid wages accounted for a plurality of labor disputes.10
- Property Defaults: Homeowners protesting undelivered apartments from collapsed real estate developers.10
- Land Seizures: Forced seizures of rural land for infrastructure projects.10
- Underemployment: The rise of “flexible employment” and the threat of wage delays even for civil servants.20
The CCP has responded with a dual strategy of “relational repression” and digital erasure.11 Authorities use neighbors and family members to pressure protesters while an “army of censors” scrubs any evidence of dissent from social media to prevent “geographic contagion”.10 The closure of many NGOs and advocacy groups has left individuals with fewer avenues for redress, paradoxically driving more people toward spontaneous street action.10
6.2. Religious and Ethnic Control
The reporting period also notes a massive crackdown against religious communities, described as the largest since 2018.
- Protestantism: Authorities surrounded a church in Wenzhou with special forces and bulldozers for demolition.54 The Beijing Zion Church has also faced a nationwide crackdown.54
- Tibet and Xinjiang: The state has intensified “preventive immunization” measures, including mandatory boarding schools and the marginalization of local language instruction, to neutralize ideas considered “politically threatening”.11
7. Maritime Incidents and Sovereignty Assertion
The South China Sea remains a primary theater for the assertion of PRC sovereignty through both military and administrative means.
7.1. Scarborough Shoal and the “Devon Bay” Incident
On January 23, 2026, a Singapore-flagged cargo vessel, the Devon Bay, carrying 21 Filipino sailors, capsized approximately 100 kilometers northwest of Scarborough Shoal.55 The Chinese Coast Guard (CCG) and Southern Theater Command quickly moved to lead the rescue operations, pulling 17 sailors from the water.55
While the operation was presented as a humanitarian effort, analysts note its significance in the sovereignty dispute:
- Administrative Presence: By acting as the primary search-and-rescue (SAR) authority in the disputed area, China is demonstrating its “effective control”.55
- Increased Patrols: AMTI reports that CCG presence at Scarborough Shoal was “unprecedented” in 2025, with patrols observed on 352 days of the year.57 The total number of CCG ship days more than doubled from 516 in 2024 to 1,099 in 2025.57
- Clashes: The incident follows a summoning of the Philippine ambassador by Beijing over “inflammatory” social media posts by Philippine Coast Guard officials, highlighting the tinderbox nature of the relationship.56
7.2. Humanitarian Cooperation and Diplomatic Leverage
The rescue of Filipino sailors by the CCG provides Beijing with a potent narrative tool. Foreign Ministry spokesperson Guo Jiakun utilized the incident to highlight China’s role as a “responsible maritime power” while simultaneously criticizing the Philippines for “co-opting countries outside the region” (referring to the U.S. and Japan) to disrupt peace.56 This serves to portray China as the natural arbiter of South China Sea affairs, regardless of the 2016 Permanent Court of Arbitration ruling.
8. Conclusion and Future Outlook
The week ending January 31, 2026, reveals a China that is aggressively fortifying its internal and external foundations. The radical purge of the CMC suggests that President Xi Jinping has entered a new phase of “political purification” to ensure the military is a reliable tool for national rejuvenation, even at the cost of immediate operational cohesion.1 This internal consolidation is mirrored by the 35% semiconductor self-sufficiency milestone, which indicates that China is making tangible progress in its quest for technological autarky.8
Strategically, the use of “shuttle diplomacy” and targeted economic concessions toward the UK and South Korea suggests that Beijing is successfully complicating the U.S. effort to isolate it diplomatically.5 However, the escalating crisis with Japan and the normalizing of airspace violations over Pratas Island point toward a high-risk environment where miscalculation is increasingly likely.3
As the 15th Five-Year Plan commences, the key risks to watch include:
- CMC Succession: Who fills the hollowed-out command structure will determine the PLA’s tactical aggression in the Taiwan Strait for the next three years.
- Technological Acceleration: Any breakthrough in commercial-grade LDP-EUV tools would effectively neutralize the primary lever of Western technological containment.8
- Domestic Grievance Thresholds: Should economic grievances move from “unpaid wages” to broader calls for political reform, as seen in localized incidents this week, the CCP’s commitment to “regime security” will likely trigger an even more repressive digital and physical response.10
The current SITREP suggests that while China faces severe demographic and economic headwinds, its leadership has successfully centralized power to a degree that allows for rapid, if high-risk, strategic maneuvers across the political, economic, and military domains.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Sources Used
- IP26018 | What Zhang Youxia’s Purge Could Mean for China’s 21st Party Congress, accessed January 31, 2026, https://rsis.edu.sg/rsis-publication/idss/ip26018-what-zhang-youxias-purge-could-mean-for-chinas-21st-party-congress/
- What Xi’s Purge Of A Top General Means For China And Its Neighbors – Radio Free Europe, accessed January 31, 2026, https://www.rferl.org/a/china-general-zhang-youxia-military-russia-central-asia-taiwan/33660395.html
- China & Taiwan Update, January 23, 2026 | ISW, accessed January 31, 2026, https://understandingwar.org/research/china-taiwan/china-taiwan-update-january-23-2026/
- China appears set on militarizing another reef in the South China Sea – Defense News, accessed January 31, 2026, https://www.defensenews.com/global/asia-pacific/2026/01/27/china-appears-set-on-militarizing-another-reef-in-the-south-china-sea/
- Foreign Ministry Spokesperson Guo Jiakun’s Regular Press Conference on January 30, 2026, accessed January 31, 2026, https://willemstad.china-consulate.gov.cn/eng/fyrth_5/202601/t20260130_11848328.htm
- What agreements have been made during Starmer’s trip to China …, accessed January 31, 2026, https://www.theguardian.com/politics/2026/jan/29/what-agreements-starmer-trip-china
- Starmer’s China visit yields long list of positive outcomes – Chinadaily.com.cn, accessed January 31, 2026, https://global.chinadaily.com.cn/a/202601/30/WS697c6546a310d6866eb36a2e.html
- China Reaches 35% Semiconductor Equipment Self-Sufficiency Amid Advanced Lithography Breakthroughs – Markets – The Daily Press, accessed January 31, 2026, https://business.smdailypress.com/smdailypress/article/tokenring-2026-1-21-china-reaches-35-semiconductor-equipment-self-sufficiency-amid-advanced-lithography-breakthroughs
- Nation clears key hurdle in its chip manufacturing push, accessed January 31, 2026, https://mobile.chinadaily.com.cn/html5/2026-01/21/content_014_696fd7a3ed50ccabe1520bb4.htm
- Protests Surge Across China Amid Economic Strain – Grand Pinnacle Tribune, accessed January 31, 2026, https://evrimagaci.org/gpt/protests-surge-across-china-amid-economic-strain-523641
- After a Wave of Protests, China’s Silent Crackdown | Journal of Democracy, accessed January 31, 2026, https://www.journalofdemocracy.org/after-a-wave-of-protests-chinas-silent-crackdown/
- China’s Cybersecurity Law Amendments Increase Penalties, Broaden Extraterritorial Enforcement – Latham & Watkins LLP, accessed January 31, 2026, https://www.lw.com/en/insights/chinas-cybersecurity-law-amendments-increase-penalties-broaden-extraterritorial-enforcement
- China Accelerates Military Modernisation With Quantum Computing, AI And Advanced Cyber Warfare Systems – Swarajya, accessed January 31, 2026, https://swarajyamag.com/infrastructure/china-accelerates-military-modernisation-with-quantum-computing-ai-and-advanced-cyber-warfare-systems
- China’s Cybersecurity Incident Reporting Measures Come into Effect – Mayer Brown, accessed January 31, 2026, https://www.mayerbrown.com/en/insights/publications/2025/12/chinas-cybersecurity-incident-reporting-measures-come-into-effect
- The 2026 National Defence Strategy: US-China Dialogue For …, accessed January 31, 2026, https://icds.ee/en/the-2026-national-defence-strategy-us-china-dialogue-for-strategic-stability-in-a-shaky-environment/
- The Purge of Zhang Youxia: Reading China’s Army-Party Relations Through Tea Leaves, accessed January 31, 2026, https://www.institutmontaigne.org/en/expressions/purge-zhang-youxia-reading-chinas-army-party-relations-through-tea-leaves
- Top Chinese general purged from military on accusations of betraying Xi Jinping, accessed January 31, 2026, https://www.washingtonexaminer.com/news/world/4433339/top-chinese-general-purged-military-accusations-betraying-xi-jinping/
- China’s top general under investigation for alleged violations amid corruption crackdown, accessed January 31, 2026, https://www.theguardian.com/world/2026/jan/26/china-top-ranking-general-zhang-youxia-investigation
- CPC leadership holds meeting on 2026 economic work, regulations on law-based governance, accessed January 31, 2026, http://en.moj.gov.cn/2025-12/09/c_1146594.htm
- China Outlook 2026: Xi to Focus on Domestic Stability Amid External Volatility – SinoInsider, accessed January 31, 2026, https://sinoinsider.com/2025/12/china-outlook-2026-xi-focus-domestic-stability-external-volatility/
- Xi chairs CPC leadership meeting on Party conduct, anti-corruption work, accessed January 31, 2026, https://english.www.gov.cn/news/202512/25/content_WS694cb9bcc6d00ca5f9a08459.html
- Foreign Ministry Spokesperson Guo Jiakun’s Regular Press Conference on January 27, 2026_Ministry of Foreign Affairs of the People’s Republic of China, accessed January 31, 2026, https://www.fmprc.gov.cn/eng/xw/fyrbt/202601/t20260127_11846105.html
- What China, the UK achieved during Starmer’s visit – CGTN, accessed January 31, 2026, https://news.cgtn.com/news/2026-01-30/Whisky-visas-and-more-What-China-UK-achieved-during-Starmer-s-visit-1KlFF4j5RFS/p.html
- China grants 30-day visa-free travel to UK nationals as 2 sides move to combat illegal immigration, accessed January 31, 2026, https://www.aa.com.tr/en/asia-pacific/china-grants-30-day-visa-free-travel-to-uk-nationals-as-2-sides-move-to-combat-illegal-immigration/3814188
- China Weighs Visa-Free Travel for U.K. Citizens, Cuts Whiskey Tariffs, accessed January 31, 2026, https://www.caixinglobal.com/2026-01-30/china-weighs-visa-free-travel-for-uk-citizens-cuts-whiskey-tariffs-102409486.html
- China, UK sign 4 economic, trade outcome documents, with efforts in goods trade, services trade, building of economic and trade mechanism: MOFCOM spokesperson – Global Times, accessed January 31, 2026, https://www.globaltimes.cn/page/202601/1354524.shtml
- BetOlimp Highlights Key Developments in Japan-South Korea Ties and Regional Security – 2026 Update, accessed January 31, 2026, https://www.weareiowa.com/article/news/local/plea-agreement-reached-in-des-moines-murder-trial/524-3069d9d4-6f9b-4039-b884-1d2146bd744f?y-news-27175579-2026-01-13-betolimp-highlights-key-developments-in-japan-south-korea-ties-2026-update
- Korea Pursues Strategic Reset With China While Deepening Cooperation With Japan in State Visits – BowerGroupAsia, accessed January 31, 2026, https://bowergroupasia.com/korea-pursues-strategic-reset-with-china-while-deepening-cooperation-with-japan-in-state-visits/
- Amid China-Japan Spat, Both Countries Court South Korea – Time Magazine, accessed January 31, 2026, https://time.com/7345772/china-japan-south-korea-relations-export-controls-taiwan/
- 2025–2026 China–Japan diplomatic crisis – Wikipedia, accessed January 31, 2026, https://en.wikipedia.org/wiki/2025%E2%80%932026_China%E2%80%93Japan_diplomatic_crisis
- China and Japan, uneasy neighbors in East Asia, are at odds again – The Durango Herald, accessed January 31, 2026, https://www.durangoherald.com/articles/a-familiar-refrain-as-china-and-japan-uneasy-neighbors-in-east-asia-begin-2026-at-odds-again/
- Japan, South Korea vow stronger ties amid China challenge – Global News, accessed January 31, 2026, https://globalnation.inquirer.net/305618/japan-south-korea-vow-stronger-ties-amid-china-challenge
- Diplomatic Schedule_Ministry of Foreign Affairs of the People’s Republic of China, accessed January 31, 2026, https://www.fmprc.gov.cn/eng/xw/wsrc/
- Foreign Ministry Spokesperson Guo Jiakun’s Regular Press …, accessed January 31, 2026, https://un.china-mission.gov.cn/eng/fyrth/202601/t20260129_11847373.htm
- Foreign Ministry Spokesperson Guo Jiakun’s Regular Press Conference on January 28, 2026, accessed January 31, 2026, https://losangeles.china-consulate.gov.cn/eng/confenrence/202601/t20260128_11846545.htm
- Chinese drill near Taiwan seen as test run for blockade, message to US – Defense News, accessed January 31, 2026, https://www.defensenews.com/global/asia-pacific/2026/01/08/chinese-drill-near-taiwan-seen-as-test-run-for-blockade-message-to-us/
- Taiwan Spotlights Invasion Defense Lines During Chinese Drills – Naval News, accessed January 31, 2026, https://www.navalnews.com/naval-news/2026/01/taiwan-spotlights-invasion-defense-lines-during-chinese-drills/
- China & Taiwan Update, January 9, 2026 | ISW, accessed January 31, 2026, https://understandingwar.org/research/china-taiwan/china-taiwan-update-january-9-2025/
- China’s military parade reveals new hypersonic missiles, drone submarines and ICBMs – Sentinel Colorado, accessed January 31, 2026, https://sentinelcolorado.com/uncategorized/chinas-military-parade-reveals-new-hypersonic-missiles-drone-submarines-and-icbms/
- China marks a key breakthrough in semiconductor self-reliance – Chinadaily.com.cn, accessed January 31, 2026, https://www.chinadaily.com.cn/a/202601/18/WS696c938ea310d6866eb34588.html
- Chinese chipmakers go public as self-sufficiency push expands – Semafor, accessed January 31, 2026, https://www.semafor.com/article/01/22/2026/chinese-chipmakers-go-public-as-self-sufficiency-push-expands
- AI Trends and Prospects for Application in the Manufacturing Industry in the Last Week of January 2026 | Amiko Consulting, accessed January 31, 2026, https://amiko.consulting/en/ai-trends-and-prospects-for-application-in-the-manufacturing-industry-in-the-last-week-of-january-2026/
- Administration Policies on Advanced AI Chips Codified, with Reverberations Across AI Ecosystem | Insights | Mayer Brown, accessed January 31, 2026, https://www.mayerbrown.com/en/insights/publications/2026/01/administration-policies-on-advanced-ai-chips-codified
- Cybersecurity Firms React to China’s Reported Software Ban – SecurityWeek, accessed January 31, 2026, https://www.securityweek.com/cybersecurity-firms-react-to-chinas-reported-software-ban/
- Trump Admin Targets Advanced AI Semiconductors, Defers Broader Tariffs, accessed January 31, 2026, https://www.pillsburylaw.com/en/news-and-insights/trump-advanced-ai-semiconductors-actions.html
- US Chipmaking Tool Exports to China Get Annual Approval … – eeNews Europe, accessed January 31, 2026, https://www.eenewseurope.com/en/china/
- China: Amended Cybersecurity Law Takes Effect – The Library of Congress, accessed January 31, 2026, https://www.loc.gov/item/global-legal-monitor/2026-01-08/china-amended-cybersecurity-law-takes-effect/
- CHINA: Amendments to Cybersecurity Law Effective 1 January 2026 | Privacy Matters, accessed January 31, 2026, https://privacymatters.dlapiper.com/2025/11/china-amendments-to-cybersecurity-law-effective-1-january-2026/
- China Amends Cybersecurity Law and Incident Reporting Regime to Address AI and Infrastructure Risks | Global Policy Watch, accessed January 31, 2026, https://www.globalpolicywatch.com/2025/10/china-amends-cybersecurity-law-and-incident-reporting-regime-to-address-ai-and-infrastructure-risks/
- China Approves Major Amendments to Cybersecurity Law, Effective 1 January 2026, accessed January 31, 2026, https://www.reedsmith.com/articles/china-approves-major-amendments-to-cybersecurity-law/
- China says it is testing quantum cyber weapons in military missions – Perplexity, accessed January 31, 2026, https://www.perplexity.ai/page/china-develops-quantum-warfare-83YRwoeoTg.2qDZSEFUU4Q
- The 2026 Global Critical Tech Race: Analyzing China’s Lead in 66 of 74 Technologies (Complete List) – Intelligent Living, accessed January 31, 2026, https://www.intelligentliving.co/critical-tech-race-chinas-lead-66-of-74/
- 2026-0112: China’s Digital Coercion Against Taiwan’s Lawmaker; Escalated Cyberattacks on Taiwan’s Critical Infrastructure – Formosan Association for Public Affairs, accessed January 31, 2026, https://fapa.org/2026-0112-chinas-digital-coercion-against-taiwans-lawmaker-escalated-cyberattacks-on-taiwans-critical-infrastructure/
- Human Rights & China: January 13, 2026 – Domino Theory, accessed January 31, 2026, https://dominotheory.com/human-rights-china-january-13-2026/
- At least 2 sailors dead after cargo ship sinks in disputed South China Sea – Al Jazeera, accessed January 31, 2026, https://www.aljazeera.com/news/2026/1/23/cargo-ship-capsizes-in-disputed-area-of-south-china-sea
- At least two dead after cargo ship capsizes near disputed islands in South China Sea – Yahoo News Singapore, accessed January 31, 2026, https://sg.news.yahoo.com/least-two-dead-cargo-ship-061505111.html
- China’s presence at Scarborough Shoal in South China Sea ‘unprecedented’ in 2025: report, accessed January 31, 2026, https://amp.scmp.com/news/china/diplomacy/article/3341822/chinas-presence-scarborough-shoal-south-china-sea-unprecedented-2025-report
- Philippine, US hold joint military drill at disputed South China Sea shoal – WIMZ, accessed January 31, 2026, https://wimz.com/2026/01/26/philippines-u-s-hold-joint-sail-in-disputed-south-china-sea-shoal/
- Chinese military slams Philippines for disrupting peace, stability in South China Sea, accessed January 31, 2026, http://en.people.cn/n3/2026/0127/c90000-20419381.html