1. Executive Summary
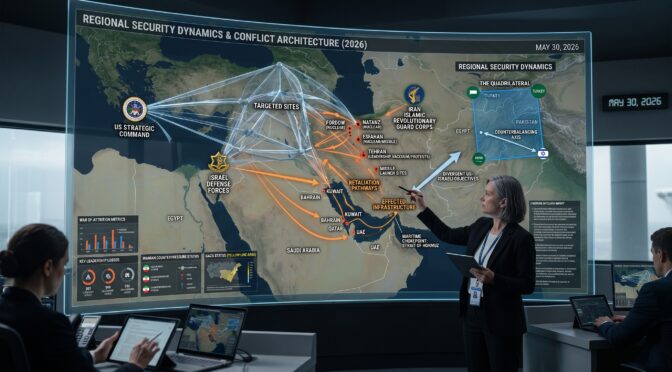
As of late May 2026, the geopolitical and tactical environment surrounding the United States and Israeli conflict with the Islamic Republic of Iran remains highly volatile, functioning as a sustained war of attrition rather than a concluded military operation. While the Executive Branch of the United States has publicly signaled the successful completion of “Operation Epic Fury,” declaring victory over the Iranian security apparatus, operational intelligence and regional kinetic activities directly contradict the cessation of hostilities.1 The conflict has entered a protracted, asymmetrical phase characterized by Iranian infrastructural resilience, maritime extortion, and strategic leadership fragmentation.
The core inquiries guiding this assessment reveal a stark strategic reality regarding the disposition of the adversaries. First, Iran’s current domestic and military state is severely degraded but highly operational in its asymmetric capacities. Following the February 28 decapitation strike that eliminated Supreme Leader Ali Khamenei, the Iranian command structure fractured.3 Operational control has largely coalesced under Islamic Revolutionary Guard Corps (IRGC) Commander-in-Chief Major General Ahmad Vahidi, who is enforcing a brutal domestic crackdown and operating as the primary decision-maker amidst the physical and political isolation of the newly appointed Supreme Leader, Mojtaba Khamenei.4
Second, the Strait of Hormuz has been formally and permanently weaponized. Iran has institutionalized its maritime blockade through the establishment of the Persian Gulf Strait Authority (PGSA), functioning as a bureaucratic protection racket that enforces a tiered toll system on global shipping.7 This has triggered severe cascading economic effects, impacting international energy markets, global fertilizer supply chains, and digital asset valuations.7
Finally, assessing whether Iranian leadership desires an end to the conflict yields a definitive negative regarding the hardline faction currently in control of the state apparatus. While US leadership actively seeks a diplomatic off-ramp—evidenced by ongoing negotiations for a 60-day memorandum of understanding (MoU) and efforts to expand the Abraham Accords—Iranian hardliners like Vahidi view sustained hostilities and absolute control over the Strait of Hormuz as non-negotiable existential leverage.6 This intent to escalate rather than concede was explicitly demonstrated by a direct Iranian ballistic missile strike on the Ali Al Salem Air Base in Kuwait on May 30, directly undermining ceasefire negotiations.13 The prevailing assessment indicates that the conflict will persist through asymmetric gray-zone warfare, maritime disruption, and localized kinetic strikes for the foreseeable future, demanding a recalibration of US strategic expectations.
2. Historical Antecedents and Pre-War Strategic Environment
To accurately contextualize the operational decisions driving the current 2026 conflict, it is essential to trace the geopolitical throughline that culminated in Operation Epic Fury. The strategic calculus of both Washington and Tehran is deeply anchored in decades of systemic distrust, periodic military escalation, and a fundamental incompatibility of regional security architectures. The current conflict is not an isolated event but the acute manifestation of a chronic geopolitical struggle.
2.1 The Roots of Bilateral Hostility
The foundational animosity between the United States, Israel, and the Islamic Republic of Iran is historically tethered to the 1953 coup d’état. Orchestrated by the Central Intelligence Agency (CIA) and British intelligence, this intervention ousted Iran’s democratically elected Prime Minister, Mohammad Mosaddegh, in order to install and prop up the increasingly unpopular Pahlavi monarchy.3 This structural intervention established a permanent grievance narrative within Iranian domestic politics. This narrative was ultimately operationalized during the 1979 Islamic Revolution and the subsequent hostage crisis, transitioning Iran into a theocratic republic structurally and constitutionally opposed to US and Israeli regional hegemony.3
Over the following decades, this ideological opposition materialized into highly calculated, multibillion-dollar investments in the “Axis of Resistance.” This network of proxy militias—spanning Hezbollah in Lebanon, various Popular Mobilization Forces in Iraq, elements in Syria, and the Houthi movement in Yemen—was designed to project Iranian power across the Middle East while maintaining a veil of plausible deniability, allowing Tehran to bleed its adversaries without triggering a conventional state-on-state war.3
2.2 The Collapse of the Nuclear Consensus and the 2024 Escalation
The diplomatic architecture designed to contain Iran’s most threatening strategic asset—its nuclear program—collapsed entirely in the years preceding the current conflict. The 2015 Joint Comprehensive Plan of Action (JCPOA), which temporarily constrained Iranian nuclear enrichment, unraveled following the unilateral US withdrawal in 2018. Subsequent efforts to renegotiate the parameters of the agreement in 2025 and early 2026 consistently faltered, primarily due to irreconcilable differences over verification protocols and sanctions relief.3
In the absence of a diplomatic framework, the region experienced severe destabilization during the 2024 Israel-Hamas War. During this period, Israeli military intelligence systematically targeted and degraded Iran’s proxy network. The most significant tactical achievement of this period was the decapitation of Hezbollah’s senior leadership in Lebanon between September and November 2024.3 This disruption caused a ripple effect across the Axis of Resistance, ultimately facilitating the December 2024 overthrow of pro-Iran Syrian President Bashar al-Assad by Ahmed al-Sharaa.3 The loss of the Syrian node severely eroded Iran’s regional land bridge, isolating its remaining proxies and forcing Tehran into a defensive posture.
2.3 The 12-Day War of 2025 and Strategic Miscalculations
Direct kinetic confrontation became normalized during the “12-Day War” in June 2025. Provoked by the collapse of proxy deterrents and the acceleration of Iranian nuclear enrichment, Israel launched direct strikes against Iranian military and nuclear facilities.16 The United States actively participated in this engagement, deploying heavy ordnance, specifically GBU-57 A/B bunker-buster munitions, against deeply buried, fortified nuclear sites located in Fordow, Natanz, and Isfahan.3
While a ceasefire temporarily halted the 2025 conflict, the engagement laid the analytical groundwork for 2026. US and Israeli intelligence communities concluded that Iran—weakened by years of suffocating economic sanctions, sweeping domestic protests that challenged the regime’s legitimacy, and the degradation of its proxy shield—presented a unique structural vulnerability.3 In early 2026, Israeli Prime Minister Benjamin Netanyahu presented intelligence assessments to US President Donald Trump, actively lobbying for a joint, decisive decapitation strike aimed squarely at Iranian regime leadership, arguing that the regime was brittle and a forceful strike could precipitate its collapse.3 This intelligence assessment ultimately served as the catalyst for the events of late February.
3. Operation Epic Fury: Tactical Execution and Political Declarations
On February 28, 2026, the United States military, acting upon direct presidential authorization and coordinating deeply with the Israeli Defense Forces (IDF), launched Operation Epic Fury.3 The operation’s stated objectives were absolute and maximalist: destroy Iranian offensive missile capabilities, dismantle military production infrastructure, neutralize the Iranian navy, and definitively end Iran’s nuclear weapons program.15 The scale of the operation marked a departure from proportional deterrence, representing a massive attempt at forced regime alteration through overwhelming kinetic application.
3.1 The Opening Salvo and Leadership Decapitation
The initial phase of Operation Epic Fury was defined by an unprecedented volume of coordinated fire across the Iranian landmass. In the first twelve hours alone, US and Israeli forces executed nearly 900 precise strikes.3 The campaign targeted integrated air defense systems, command and control centers, and high-value leadership compounds.
The strategic highlight of this opening wave was the successful targeting of Supreme Leader Ali Khamenei, who was killed alongside dozens of senior regime officials before they could successfully relocate to subterranean bunkers.3 However, the intensity of the bombardment also resulted in severe collateral damage, most notably when a missile—assessed to be targeting an adjacent IRGC naval base—struck a girls’ school in Minab, east of Bandar Abbas, resulting in the deaths of approximately 170 civilians.3
3.2 Political Declarations of Victory
By early April, the White House declared the operation a resounding tactical and strategic success. Press Secretary Karoline Leavitt stated that the core military objectives were achieved and exceeded within a 38-day window.1 Administration officials cited the functional neutralization of the Iranian air force, noting that pre-war daily flight operations of 30 to 100 sorties had been reduced to zero.1 The sheer statistical volume of the campaign was heavily publicized to reinforce the narrative of total victory.
| Operation Epic Fury Target Matrices (Claimed by US Administration) | Quantified Impact |
| Total Air Sorties Flown | > 10,200 |
| Total Targets Struck | > 13,000 |
| Command and Control Targets Destroyed | > 2,000 |
| Defense and Industrial Base Targets Destroyed | > 1,450 |
| Air Defense Targets Destroyed | > 1,500 |
| Attack Drone Targets Destroyed | ~ 800 |
| Naval Targets Destroyed | > 600 |
| Ballistic Missile Targets Destroyed | > 450 |
| Incoming Drone Threats Intercepted | > 1,000 |
| Incoming Ballistic Missile Threats Intercepted | > 700 |
Data source: Official White House statements on Operation Epic Fury metrics.1
A temporary ceasefire was instituted on April 7-8, brokered heavily by Pakistan and influenced by last-minute diplomatic pressure from the People’s Republic of China, which sought to stabilize global energy markets.3 This pause in operations allowed US leadership to declare an end to the acute phase of the war.
3.3 The Reality of the Kinetic Missile Fight
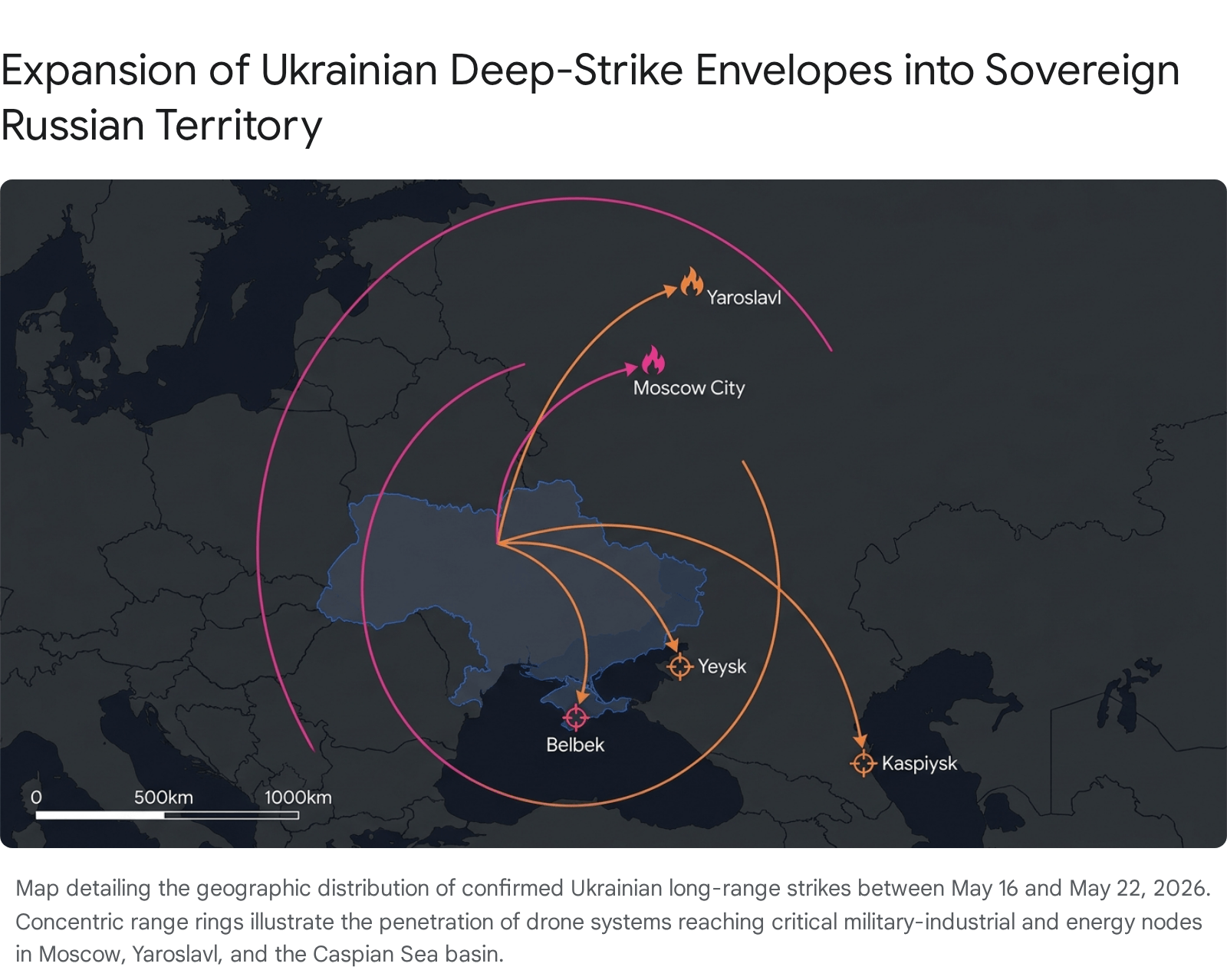
Despite the political declarations of victory emanating from Washington, operational realities on the ground indicate that Epic Fury has merely transitioned into a new, highly dangerous phase of asymmetrical warfare. Defense analysts characterize the current paradigm as a “Kinetic Missile Fight,” a localized war of attrition dependent on deep subterranean supply caches rather than traditional air superiority.19
Intelligence assessments reveal that despite the intense bombardment, Iran has demonstrated remarkable infrastructural resilience. The concept of Iranian military devastation appears to have been overstated. Tehran has rapidly reconstituted its missile and drone arsenals, successfully restoring operational access to 30 of its 33 underground missile sites located in Granite mountain bases along the Strait of Hormuz.2 While the broader ballistic missile production program has suffered qualitative degradation, the operational force retains the capacity to launch massed barrages, preserving Iran’s ability to wage an extended war of attrition.19
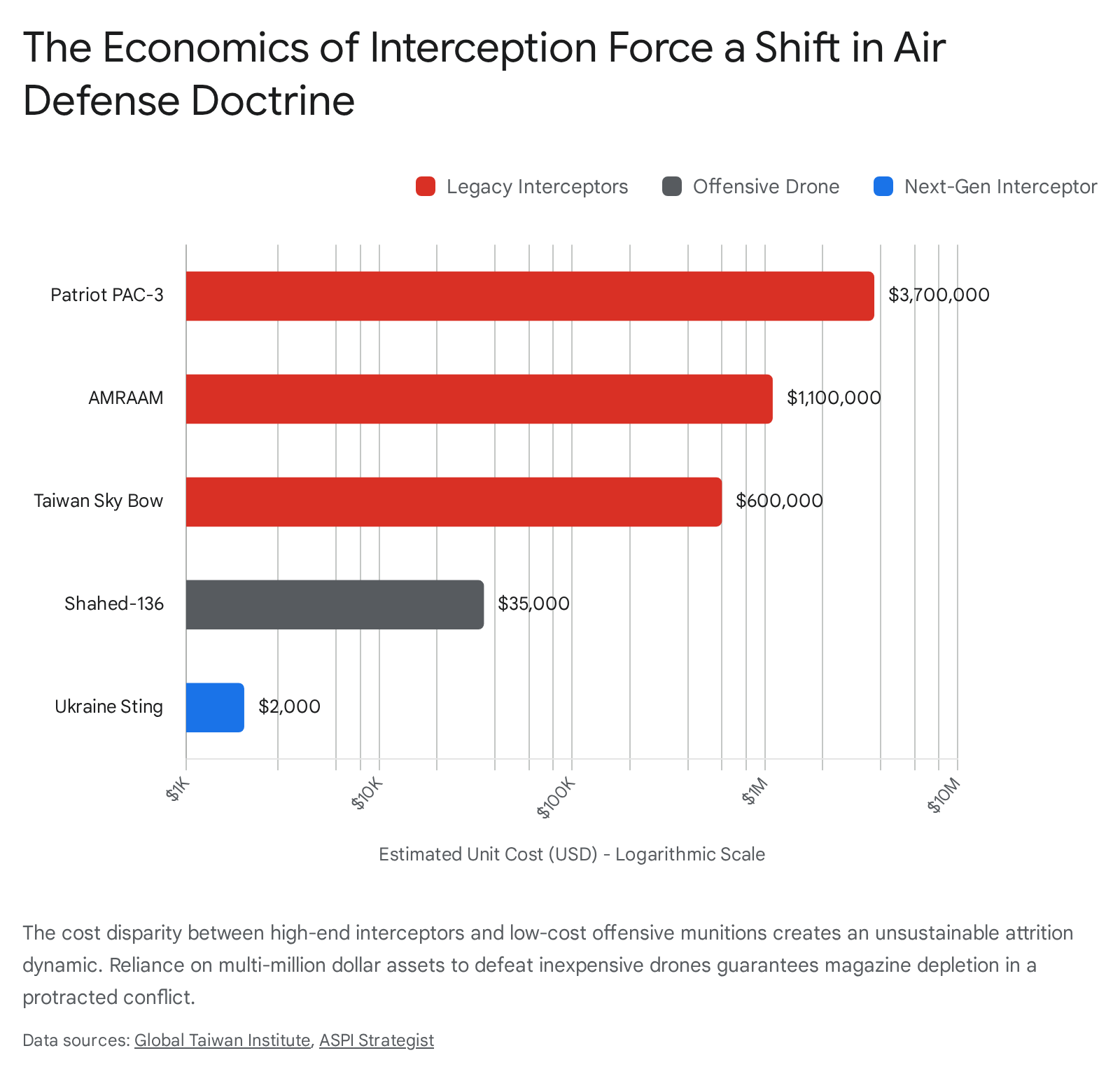
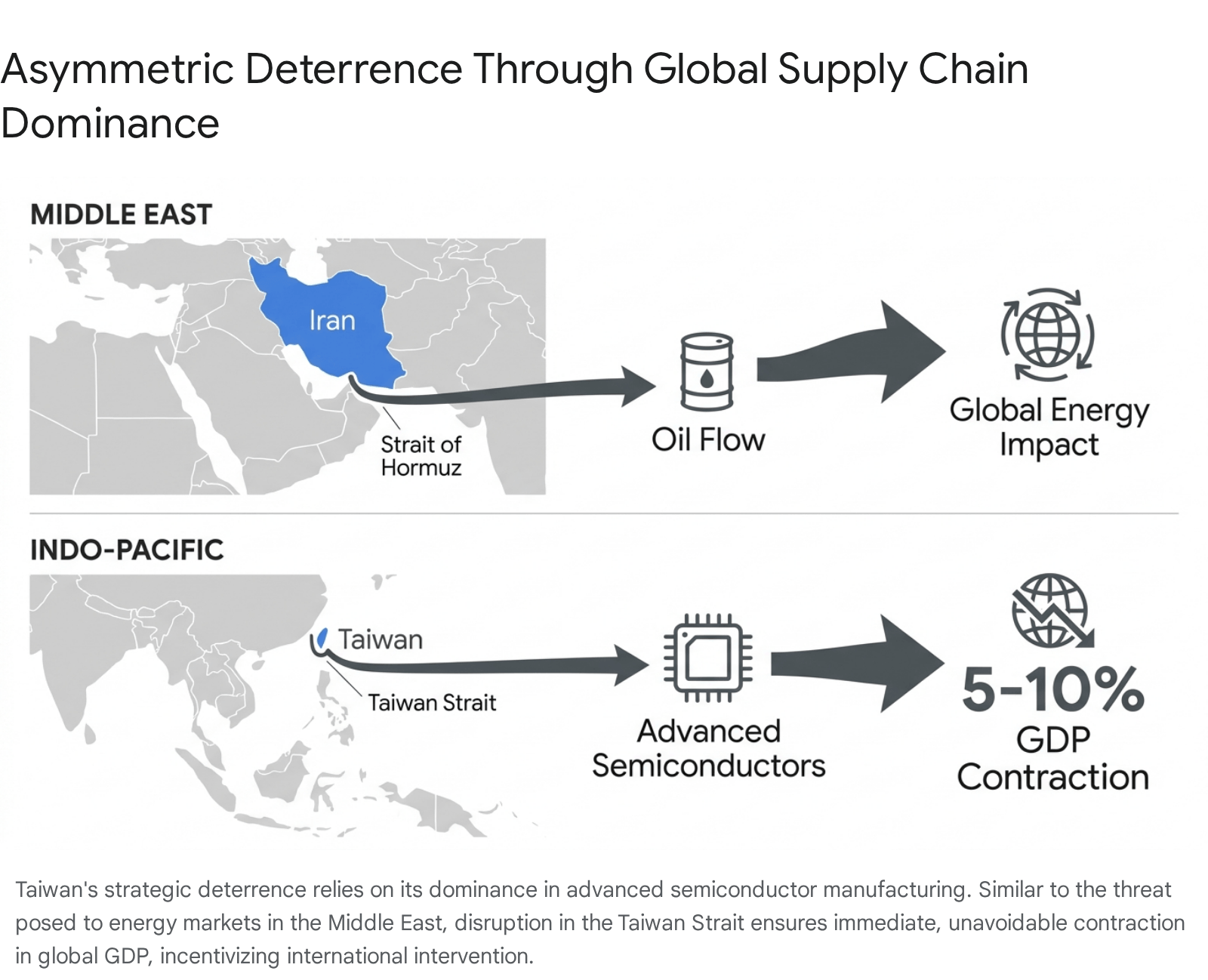
Furthermore, the operational tempo has heavily strained US military logistics. The Department of Defense is facing a critical, long-term munitions shortage. The campaign has severely depleted stockpiles of precision-guided munitions and high-end interceptors, including Tomahawk land-attack missiles, JASSM-ER cruise missiles, Patriot PAC-3s, Terminal High Altitude Area Defense (THAAD) interceptors, and SM-3 Block IIA systems.21 Washington-based strategic analysis indicates that the US military would require at least three years to fully refill the stock of three key weapon systems expended during the February and March campaigns.22 This depletion limits US operational flexibility globally, raising significant concerns regarding readiness for potential concurrent conflicts, particularly regarding deterrence postures in the Indo-Pacific region concerning China.19
The human and material cost to US forces, while statistically lower than adversary losses, remains present. The latest casualty reports for Operation Epic Fury list 14 American deaths and 409 injuries.21 Material losses include the destruction of a KC-135 tanker aircraft over Iraq on March 12, resulting in the deaths of all four crew members, alongside multiple unmanned aerial assets.18 Competing defense analyses suggest Iran may have successfully wiped out up to 42 US military aircraft during the broader campaign, though these figures remain heavily contested.19
3.4 Contingency Planning for Resumption
Recognizing the fragility of the April ceasefire and the continued operational capacity of the IRGC, the Pentagon has actively drafted plans for the resumption of Epic Fury.2 Secretary of Defense Pete Hegseth confirmed at the Shangri-La Dialogue in Singapore that the US remains “more than capable” of restarting the conflict, maintaining that global munitions management allows for sustained operations despite stockpile concerns.23
Contingency planning includes high-risk scenarios. Pentagon officials have prepared options for deploying several hundred US Special Operations forces—who have already been forward-deployed to the Middle East—to execute ground operations aimed at physically securing highly enriched uranium believed to be stored in subterranean facilities in Isfahan.2 Military officials acknowledge that such an operation carries an exceptionally high risk of mass US casualties and would necessitate thousands of support troops, highlighting the extreme difficulty of achieving the operation’s nuclear objectives strictly through aerial bombardment.2
4. The Iranian Domestic State: Leadership Vacuum and Hardline Consolidation
The operational effectiveness and strategic posture of the Iranian state is currently defined by the massive leadership vacuum created on February 28. The decapitation strike fundamentally altered the internal balance of power in Tehran. Rather than precipitating the collapse of the regime as Israeli intelligence suggested, the strike eliminated the pragmatic and balancing elements of the state, elevating hardline IRGC commanders who favor total militarization, domestic repression, and sustained conflict over diplomatic statecraft.6
4.1 The Isolation of Mojtaba Khamenei
Following the death of Ali Khamenei, the regime moved swiftly to prevent an institutional collapse. His son, Mojtaba Khamenei, was rapidly elevated to the position of Supreme Leader by regime loyalists, signaling a continuity of the ideological state.3 However, his assumption of power has been shrouded in physical and political instability.
Intelligence suggests that Mojtaba Khamenei was severely injured during the February 28 strikes on the leadership compound.5 He was reportedly transferred to the intensive care unit at Sina Hospital. While official regime communications insist his injuries are superficial, credible local intelligence and hospital sources indicate he remains largely incapacitated, with rumors circulating in Tehran that the regime is preparing to announce his impending death.5 This physical isolation has translated into profound political isolation, rendering the new Supreme Leader entirely dependent on a tight circle of security officials to govern.25
4.2 The Ascendancy of Major General Ahmad Vahidi
The primary beneficiary of this leadership vacuum is Major General Ahmad Vahidi, a seasoned security strategist and fundamentalist ideologue. Appointed as Deputy Commander-in-Chief of the IRGC on December 31, 2025, Vahidi was elevated to Commander-in-Chief following the death of his predecessor, Mohammad Pakpour, in the opening strikes of the war.4 Vahidi possesses immense credibility across the IRGC and holds significant weight within the security establishment.6
Vahidi is a hardliner with a brutal history of suppressing domestic dissent. He utilized his previous experience suppressing the 2022 “Woman Life Freedom” movement to oversee a swift internet shutdown and a violent crackdown on nationwide protests in late December 2025, resulting in the arrest, injury, and death of tens of thousands of Iranians across all 31 provinces.6 Under the current wartime conditions, he operates as the de facto primary decision-maker in Tehran.4
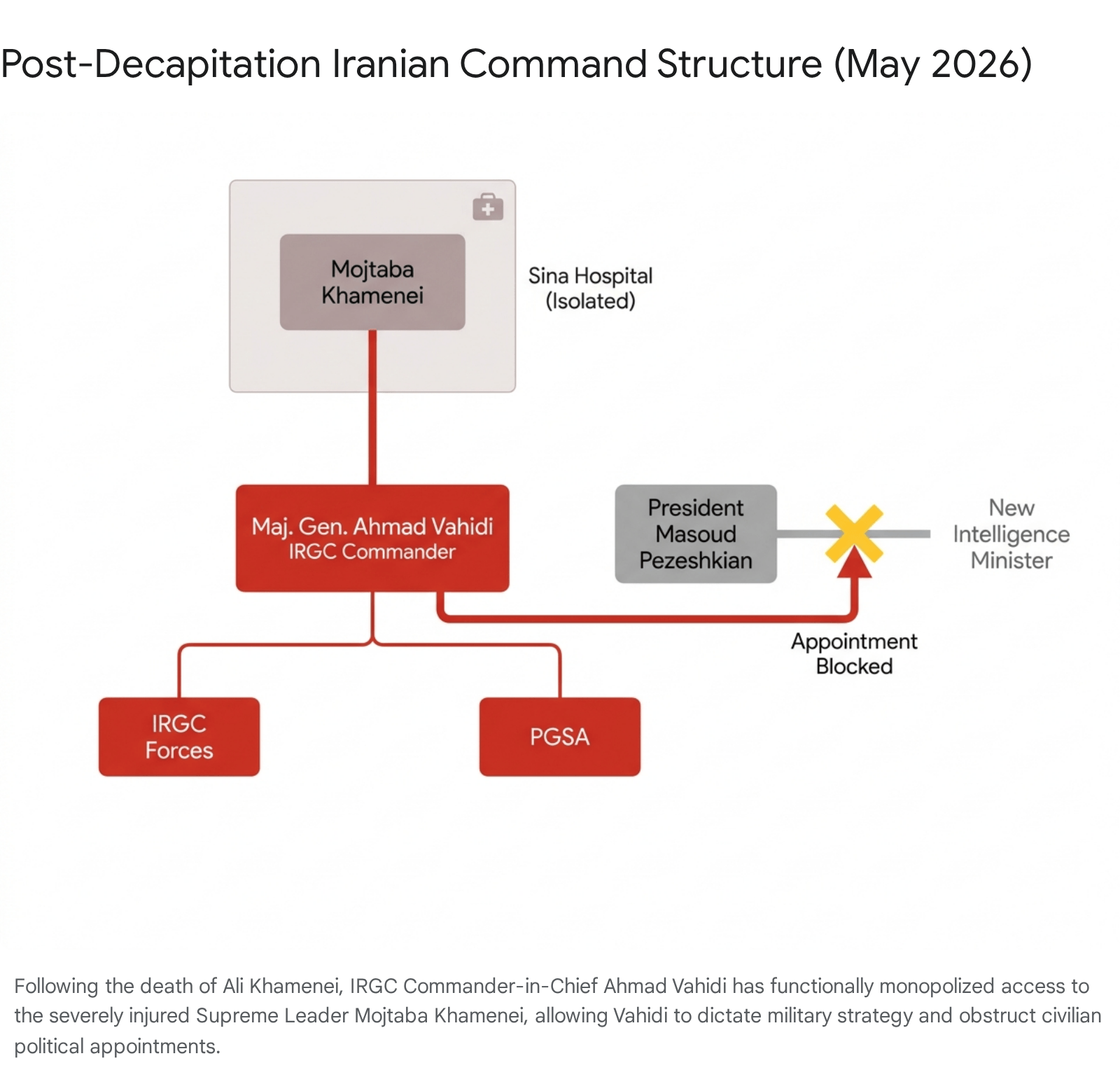
Vahidi’s authority is expansive and increasingly dictatorial. He is reportedly the only senior official capable of securing direct audiences with Mojtaba Khamenei, establishing an exclusive pipeline of communication that entirely bypasses traditional political structures.4 Vahidi has leveraged this unique position to actively undermine the civilian government led by President Masoud Pezeshkian. Following the March 18 Israeli strike that killed Intelligence Minister Esmail Khatib, Vahidi systematically blocked Pezeshkian from appointing a civilian replacement.6 Furthermore, Vahidi has heavily pressured the presidency to install his loyalist, Mohammad Bagher Zolghadr, as Secretary of the Supreme National Security Council (SNSC), attempting to fully militarize the state’s intelligence and diplomatic apparatus.6
This internal consolidation directly answers the critical question regarding Tehran’s intent to end the conflict. Vahidi and his cadre of hardline IRGC officers are fundamentalists who strongly advocate for the complete militarization of the Islamic Republic of Iran.6 They perceive absolute control over the Strait of Hormuz and the preservation of the nuclear program as non-negotiable existential imperatives. Consequently, the prevailing assessment is that Iranian decision-makers, under Vahidi’s direction, do not share the US desire for immediate de-escalation. They prefer instead to absorb tactical military losses while inflicting unsustainably high economic costs on the international community, believing that time and economic attrition favor Tehran.9
5. Weaponization of the Maritime Domain: Institutionalizing the Strait of Hormuz Crisis
The most globally disruptive vector of the 2026 conflict is the ongoing crisis in the Strait of Hormuz. Following the initial strikes in late February, Tehran executed a strategy of horizontal escalation, utilizing its geographic advantage to transform the vital maritime chokepoint into an economic weapon against the US, Israel, and their global allies.3 This transition from conventional warfare to maritime economic terrorism represents the core of Iran’s retaliatory strategy.
5.1 The Improvised Blockade and the Failure of Project Freedom
Initially, Iran simply closed the strait to all non-aligned traffic, launching retaliatory attacks against commercial shipping and oil infrastructure across the Gulf, demanding that transiting ships obtain Tehran’s approval and pay impromptu tolls.3 In response, the US instituted a counter-blockade of Iran’s southern ports on April 13, attempting to choke off the regime’s import capabilities.7
Seeking to break the Iranian stranglehold, the US launched “Project Freedom” on May 4, attempting to establish an air defense umbrella over Omani territorial waters to securely escort commercial vessels.7 This operation was a rapid failure. Iran immediately attacked multiple participating vessels in response, proving that aerial dominance could not secure maritime surface transit against asymmetric swarm tactics and coastal missile batteries.7 The US was forced to swiftly abandon the operation under intense pressure from Gulf Arab allies, who feared massive retaliatory strikes against their own domestic infrastructure.7
5.2 The Persian Gulf Strait Authority (PGSA)
Capitalizing on the failure of Project Freedom, Iran rapidly institutionalized its control over the waterway. They pivoted from a chaotic, kinetically enforced blockade to a highly organized bureaucratic protection racket.7 On May 5, the Iranian government officially formed the Persian Gulf Strait Authority (PGSA) to manage, regulate, and tax all transit through the strait.8 By mid-May, Iran expanded its definition of the strait’s boundaries—enforcing claims from Qeshm Island to the UAE’s port of Fujairah, and eastward to Jask—enforcing compliance by sinking and seizing non-compliant vessels.7 On May 18, the PGSA launched a new mandatory insurance scheme called “Hormuz Safe” to formalize the transit fees.7
The PGSA operates an explicit tiered passage system designed to fracture international consensus. Ships from “friendly” states, such as the Russian Federation and the People’s Republic of China, face minimal restrictions and delays.7 States maintaining diplomatic relations with Tehran, such as India and Pakistan, negotiate passage bilaterally.7 All other non-hostile vessels are subjected to private transit agreements requiring the purchase of the “Hormuz Safe” insurance, alongside direct toll payments to the PGSA that frequently reach up to $150,000 per ship, plus a supplementary $1 toll per barrel of oil for loaded tankers.7 Vessels linked in any capacity to the United States and Israel remain strictly barred from transit and are subject to immediate seizure or destruction.7
5.3 Sanctions Architecture and Retaliatory Defiance
In an attempt to dismantle this protection racket without resorting to further kinetic escalation, the US Treasury Department’s Office of Foreign Assets Control (OFAC) officially designated and sanctioned the PGSA on May 27, citing its role in materially supporting the IRGC’s terrorism networks.9 US Treasury Secretary Scott Bessent issued severe warnings that any international actor, specifically including the government of Oman, that cooperates with the PGSA’s toll system directly or indirectly would face crippling secondary sanctions.9
The PGSA swiftly dismissed the sanctions. In a public statement on May 30, the authority mocked the US designation, declaring it a badge of honor to be sanctioned by a nation “whose leader takes pride in piracy”.28 The PGSA reiterated its intent to continue issuing transit permits uninterrupted, emphasizing that the US cannot secure through economic sanctions what it definitively failed to achieve through naval warfare and diplomacy.29
6. Global Economic Contagion and Supply Chain Disruption
The weaponization of the Strait of Hormuz has triggered cascading, severe disruptions across global supply chains. The conflict has bypassed localized military attrition and metastasized into a global economic contagion, severely impacting energy markets, agricultural food security, and international financial stability. Simultaneously, the domestic Iranian economy is buckling under the dual pressures of war and US blockades.
6.1 Vulnerability of Alternative Hydrocarbon Corridors
The Strait of Hormuz is the most critical energy chokepoint on the globe, handling approximately 25 percent of the world’s crude oil and 20 percent of its liquefied natural gas (LNG). The PGSA’s toll system and the general threat of destruction have forced global importers—particularly heavily reliant East Asian states like China, India, Japan, and South Korea—to drastically draw down strategic reserves and reroute logistics to North American exporters, spiking global freight costs.7
While regional alternative bypass pipelines exist, they are structurally insufficient to replace Hormuz and are highly vulnerable to IRGC strikes.
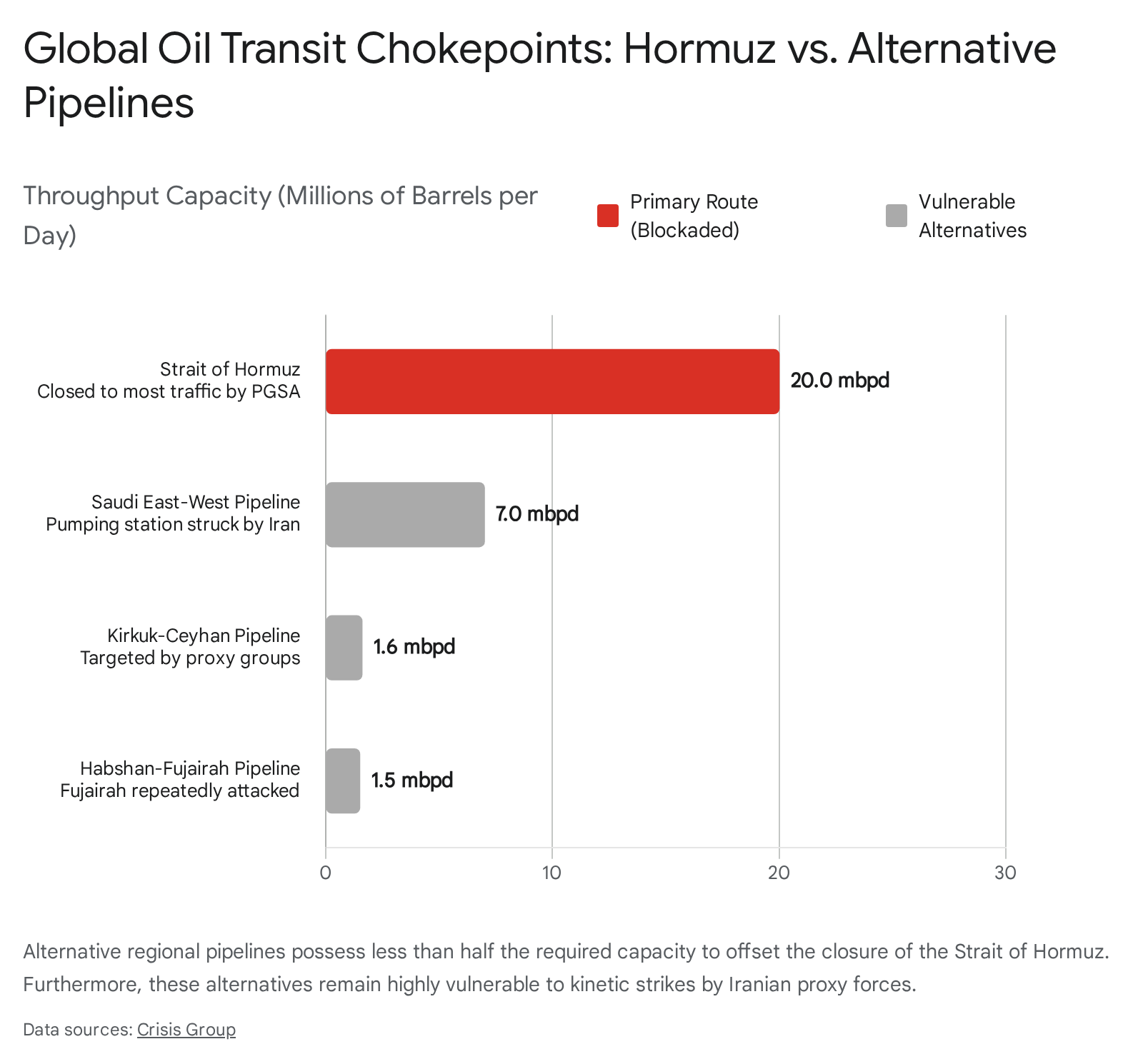
| Pipeline Route | Official Capacity | Operational Status / Vulnerabilities |
| Saudi East-West Pipeline | 7.0 million barrels per day | Pumping station struck by Iran in April 2026, temporarily disabling 700,000 bpd. 7 |
| UAE Habshan-Fujairah | 1.5 million barrels per day | Fujairah port repeatedly attacked; well within range of Iranian coastal weapons. 7 |
| Iraq Kirkuk-Ceyhan | 1.6 million barrels per day | Operating well below capacity due to attacks by Iranian proxy militias in Iraq. 7 |
6.2 Agricultural and Financial Shockwaves
The maritime disruption extends far beyond hydrocarbons, striking at the core of global food security. A substantial portion of the global trade in synthetic fertilizers, specifically urea and phosphate types, transits the Strait. The conflict has essentially halted this flow, which constitutes one-third of the global fertilizer trade, driving global urea prices up by 40 percent in global markets by mid-April.7 US Agriculture Secretary Brooke Rollins warned that these disruptions expose critical vulnerabilities in domestic agricultural supply chains, noting that the US currently relies on imports for 50 percent of its fertilizer.10 The resulting agricultural constraints pose severe risks to planting seasons worldwide and threaten to trigger mass starvation events in heavily import-reliant, vulnerable nations like Sudan.7
Financial markets are increasingly sensitive to the conflict’s tactical developments. On May 30, following an Iranian ballistic missile strike on a US base in Kuwait, digital asset markets experienced a severe flash crash. Bitcoin valuations dropped below $73,000 within hours, triggering nearly $1 billion in leveraged crypto position liquidations across the market.30 The broader conflict has wiped an estimated $80 billion from digital asset market values, reflecting the high anxiety and deleveraging embedded in geopolitical risk assessments across speculative assets.11
6.3 Iranian Domestic Economic Attrition and Evading US Sanctions
Domestically, Iran is facing an unprecedented economic crisis, though the regime appears willing to absorb the pain. Inflation surged to a staggering 67 percent in April 2026, accompanied by massive unemployment as millions of citizens lost their jobs.7 While the US blockade of southern Iranian ports has severely restricted food and commodity imports—threatening a localized food price crisis and the total collapse of the Iranian livestock sector—Tehran is actively mitigating these effects by leveraging alternative terrestrial networks.7 Utilizing the International North-South Transportation Corridor, which involves Caspian Sea maritime routes and rail connections to Russia, Pakistan, and China, Iranian intelligence services assess that approximately 40 percent of the country’s total trade has been successfully rerouted away from the blocked southern ports.7
To further asphyxiate the regime’s revenue generation, the US Treasury Department launched a new wave of targeted sanctions on May 28, aimed specifically at the military’s illicit oil trade.31 The sanctions explicitly target Sepehr Energy Jahan Nama Pars Company, the official oil sales arm of the Iranian Armed Forces General Staff.20 OFAC designated a vast network of front companies and commercial intermediaries operating in Hong Kong, the UAE, India, and Liberia. For instance, entities such as Worth Seen Energy Limited in Hong Kong were identified as procuring refined petroleum products for the National Iranian Oil Company on behalf of Sepehr Energy, loading hundreds of thousands of barrels in the UAE for transport to Bandar Abbas.33 Despite these enforcement efforts, Chinese President Xi Jinping recently affirmed Beijing’s intent to continue purchasing Iranian oil, providing Tehran with critical financial lifelines via floating storage and mortgages on future, unextracted oil sales.7
7. The Illusion of Diplomacy: Ceasefire Negotiations and the 60-Day MoU
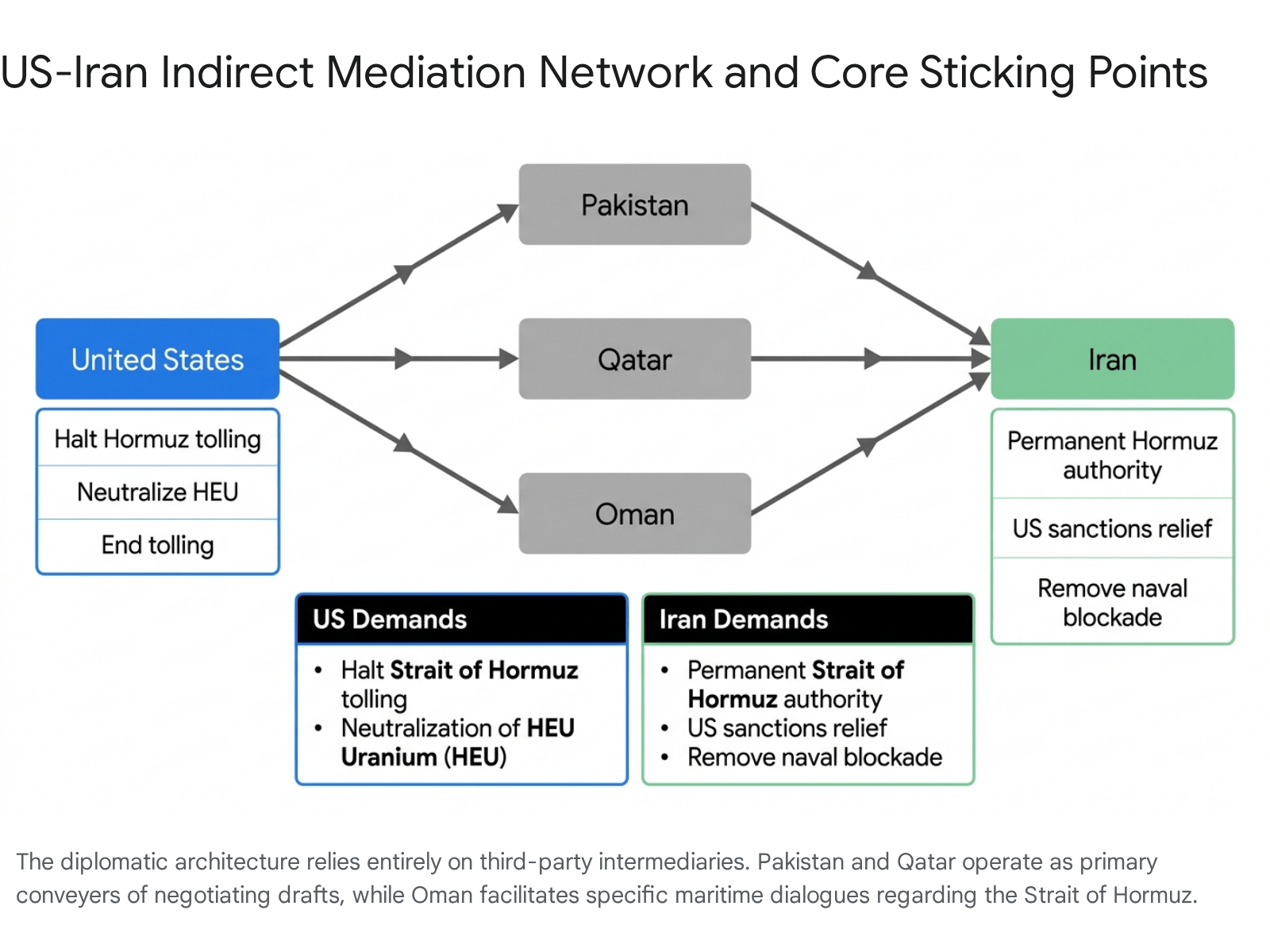
Diplomatic efforts to formalize an end to the conflict have yielded a tentative framework, but the implementation of any lasting peace remains highly improbable given the entrenched positions of both belligerents. Western intelligence sources leaked the existence of a 60-day Memorandum of Understanding (MoU) drafted by US and Iranian negotiators in late May.9 The proposed terms highlight a vast chasm in strategic objectives.
Under the proposed terms, the US seeks the total reopening of the Strait of Hormuz without tolls or PGSA interference, and demands that Iran physically destroy or transfer its highly enriched uranium (HEU) stockpiles to the United States.20 President Trump has also introduced a sweeping, maximalist geopolitical prerequisite, demanding that Iran and other regional states formally sign onto a widened version of the Abraham Accords to permanently recognize the state of Israel.12 This demand is fundamentally incompatible with Iran’s state ideology, which explicitly calls for the eradication of Israel.12
The MoU has failed to gain traction because neither state’s principal decision-makers will authorize the necessary concessions. In Washington, Congressional leaders, including Senators Ted Cruz and Roger Wicker, have heavily criticized the rumored ceasefire. They argue that lifting sanctions or allowing Iran to retain de facto control over the Strait of Hormuz would invalidate the tactical gains of Operation Epic Fury, resulting in a regime flush with billions of dollars capable of re-enriching uranium.12 Concurrently, in Tehran, Mojtaba Khamenei and Major General Ahmad Vahidi have implicitly rejected the terms. Khamenei’s public statements indicate an absolute refusal to yield sovereignty over maritime transit or to dismantle the nuclear program.9
8. Regional Proliferation and Kinetic Sabotage
While the primary theater of Epic Fury centered on the Iranian mainland and the Persian Gulf, the conflict relies heavily on horizontal escalation across multiple regional fronts. The current status of the broader war is characterized by stalled diplomacy, active proxy engagements, and deliberate acts of sabotage aimed at ensuring the conflict persists.
8.1 The Northern Front: Lebanon and Hezbollah
Despite the decapitation of Hezbollah leadership in late 2024, the proxy group continues to function as a lethal extension of Iranian foreign policy. In direct response to the initiation of Operation Epic Fury, Hezbollah launched massive drone and missile barrages into northern Israel on March 2.3 Consequently, Israel initiated a major ground invasion of southern Lebanon on March 17.3
As of late May 2026, the IDF continues to push deeper into Lebanese territory, issuing mass evacuation orders for villages in the south, forcing more than 1.1 million Lebanese civilians to flee.3 Israeli Defense Minister Israel Katz has stated explicit intentions to militarily occupy southern Lebanon up to the Litani River, tying the cessation of operations in the Levant strictly to a finalized, overarching peace agreement with Tehran.3 Meanwhile, Hezbollah continues to fire rockets at northern Israeli towns like Kiryat Shmona, ensuring the northern front remains highly active.34
8.2 Tactical Sabotage: The May 30 Strike on Kuwait
The Iranian hardliner faction’s rejection of the ceasefire was violently and explicitly demonstrated on May 30, exactly three days after the conclusion of White House-hosted negotiations regarding the MoU.13 Acting to deliberately sabotage the diplomatic track, the IRGC launched a Fateh-110 short-range ballistic missile directly from Iranian territory, targeting the Ali Al Salem Air Base in Kuwait.13
While Kuwaiti air defense systems intercepted the projectile, falling debris tore through the base’s flight line, injuring five American personnel—including active-duty service members and contractors.13 The strike successfully neutralized critical US intelligence assets, destroying one MQ-9 Reaper drone outright and severely damaging a second, resulting in immediate hardware losses exceeding $60 million.11 US Central Command explicitly condemned the launch as an egregious violation of the nominal, fragile ceasefire.11 The deliberate nature of this strike—launched directly from the Iranian homeland rather than via a deniable proxy militia operating in Iraq or Syria—signals an explicit, undeniable message from Vahidi’s command: the IRGC retains both the capability and the intent to inflict continuous, localized kinetic damage on US forces across the Middle East until US negotiators capitulate to Iranian demands regarding regional security architecture and unconditional sanctions relief.
9. Strategic Mitigation and Trajectory Assessment
The US-Israel conflict with Iran has evolved from a concentrated, high-intensity decapitation campaign into a protracted, multi-domain war of attrition. Based on the intelligence synthesized in this report, several strategic trajectories and requirements for mitigation emerge for the near-to-medium term.
First, the United States must operate under the foundational assumption that the Iranian central command, under the absolute influence of Major General Ahmad Vahidi, prefers prolonged conflict over capitulation. The Iranian strategy leverages the belief that the international community—facing severe disruptions in energy flows, agricultural outputs, and global supply chains—will exert immense pressure on Washington to concede to Iran’s maritime and nuclear prerequisites. Diplomatic off-ramps based on traditional deterrence logic will fail because the current Iranian leadership perceives absolute resistance as an ideological and political imperative.
Second, the PGSA represents a permanent intended shift in the governance of the Persian Gulf. By transitioning from a military blockade to a bureaucratic, tiered toll system, Iran is attempting to legitimize its control over international waters, establishing a new norm in maritime law. Relying solely on secondary sanctions against facilitators like Oman or non-compliant shipping companies will be highly complex and likely insufficient, given the reliance of massive Asian economies on these trade routes and their willingness to circumvent US edicts. Without a renewed, sustained naval coalition willing to aggressively escort vessels and engage IRGC fast-attack craft—a strategy previously abandoned after the failure of Project Freedom—the PGSA’s extortion matrix will likely stand as a permanent feature of global trade.
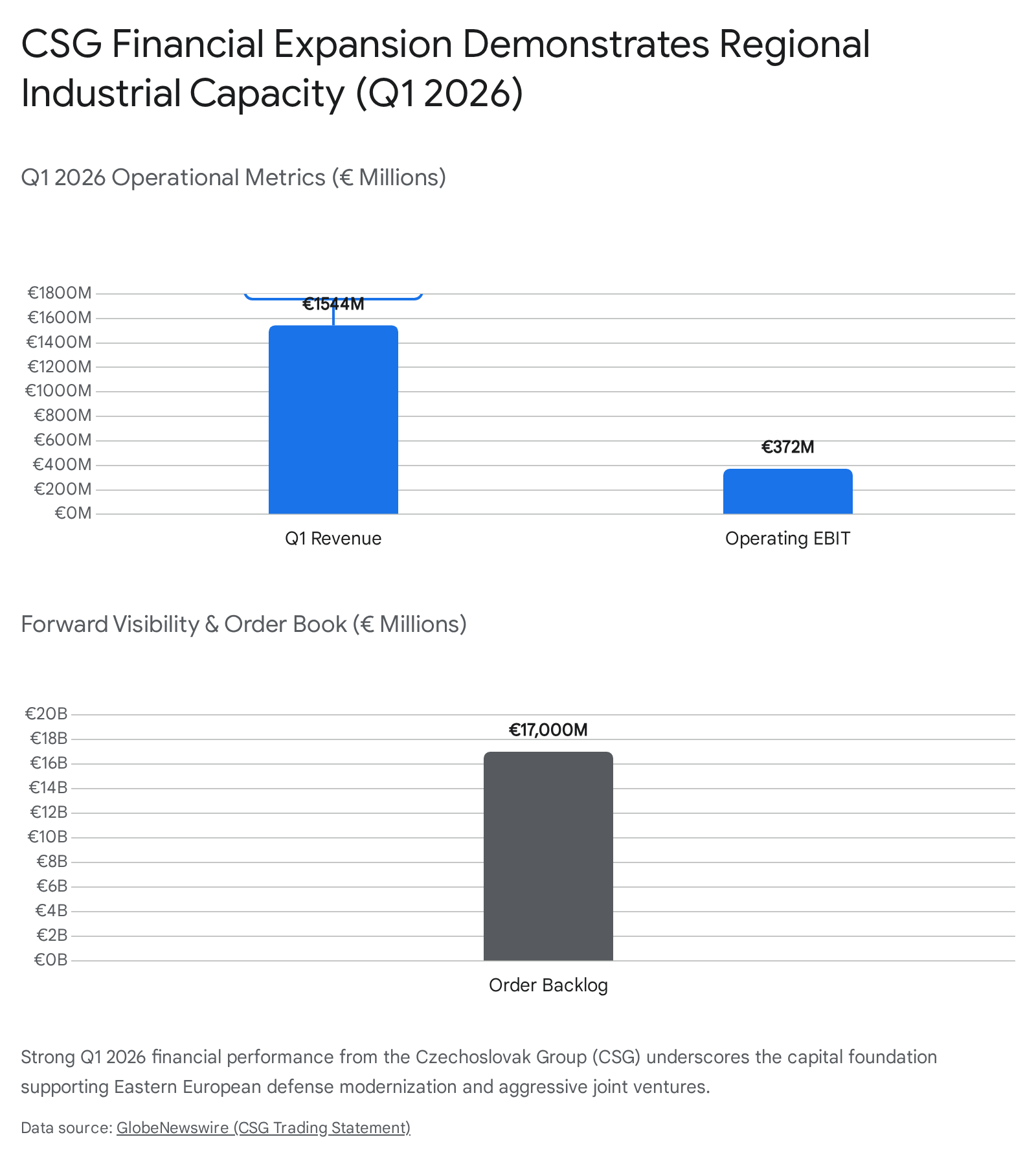
Finally, the US military must immediately address the structural vulnerabilities exposed by the conflict. The rapid depletion of critical precision-guided munitions and advanced interceptors, coupled with the exposure of static regional bases like Ali Al Salem to advanced Iranian ballistic missiles, dictates an urgent requirement for dispersed basing architectures and accelerated, robust procurement pipelines. Operation Epic Fury may have successfully eliminated the traditional hierarchy of the Iranian regime, but the resulting fragmentation has empowered a highly aggressive, risk-tolerant military cadre capable of sustaining systemic regional instability. The United States must prepare for a long-term posture of active containment and periodic kinetic engagement, as the era of negotiated containment with the Islamic Republic has definitively ended.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Works cited
- Peace Through Strength: Operation Epic Fury Crushes Iranian Threat as Ceasefire Takes Hold – The White House, accessed May 30, 2026, https://www.whitehouse.gov/releases/2026/04/peace-through-strength-operation-epic-fury-crushes-iranian-threat-as-ceasefire-takes-hold/
- Operation Epic Fury to resume? Donald Trump weighs fresh Iran …, accessed May 30, 2026, https://timesofindia.indiatimes.com/world/us/operation-epic-fury-to-resume-donald-trump-weighs-fresh-iran-strikes-after-china-visit-report/articleshow/131131463.cms
- 2026 Iran war | Explained, United States, Israel, Strait of Hormuz …, accessed May 30, 2026, https://www.britannica.com/event/2026-Iran-war
- Inside Iran’s Fragmented Decision-Making Structure, accessed May 30, 2026, https://www.meforum.org/mef-online/inside-irans-fragmented-decision-making-structure
- Does Mojtaba Khamenei’s leadership have a future? – analysis, accessed May 30, 2026, https://www.jpost.com/middle-east/iran-news/article-897750
- Ahmad Vahidi: Commander-in-Chief of the IRGC | UANI, accessed May 30, 2026, https://www.unitedagainstnucleariran.com/ahmad-vahidi-commander-chief-of-irgc
- The State of the Strait: What Might Come Next in Hormuz, accessed May 30, 2026, https://www.crisisgroup.org/visual-explainers/hormuz/
- Persian Gulf Strait Authority – Wikipedia, accessed May 30, 2026, https://en.wikipedia.org/wiki/Persian_Gulf_Strait_Authority
- Iran Update Special Report, May 28, 2026 | ISW, accessed May 30, 2026, https://understandingwar.org/research/middle-east/iran-update-special-report-may-28-2026/
- Trump enters Situation Room to make ‘final determination’ on Iran, accessed May 30, 2026, https://www.foxnews.com/live-news/iran-war-news-trump-strait-hormuz-blockade-ceasefire-peace-deal-may-29
- Iran missile strike injures five US personnel at Kuwait base, rattling crypto markets already on edge, accessed May 30, 2026, https://cryptobriefing.com/iran-missile-strike-kuwait-crypto-markets/
- As new Iran deal faces sharp criticism, Trump seeks to widen Abraham Accords, accessed May 30, 2026, https://www.washingtonpost.com/world/2026/05/25/trump-seeks-widen-abraham-accords-new-iran-deal-faces-sharp-criticism/
- Several Americans hurt in missile attack on Kuwaiti air base as Iran ceasefire talks collapse, accessed May 30, 2026, https://cryptobriefing.com/americans-hurt-missile-attack-kuwait-air-base/
- Iran missile strike at Kuwait base damages US drones, injures Americans: Report, accessed May 30, 2026, https://timesofindia.indiatimes.com/world/middle-east/iran-missile-strike-at-kuwait-base-damages-us-drones-injures-americans-report/articleshow/131407551.cms
- Operation Epic Fury and International Law – United States Department of State, accessed May 30, 2026, https://www.state.gov/releases/office-of-the-legal-adviser/2026/04/operation-epic-fury-and-international-law
- 2026 Iran war – Wikipedia, accessed May 30, 2026, https://en.wikipedia.org/wiki/2026_Iran_war
- Operation Epic Fury (OEFU) – Defense Casualty Analysis System, accessed May 30, 2026, https://dcas.dmdc.osd.mil/dcas/app/conflictCasualties/oefu
- U.S. Central Command | Operation Epic Fury, accessed May 30, 2026, https://www.centcom.mil/OPERATIONS-AND-EXERCISES/EPIC-FURY/
- Iran Wiped Out 42 U.S. Military Aircraft in Operation Epic Fury — and …, accessed May 30, 2026, https://nationalsecurityjournal.org/iran-wiped-out-42-u-s-military-aircraft-in-operation-epic-fury-and-its-just-getting-started/
- Iran Update Special Report, May 29, 2026 – Institute for the Study of War, accessed May 30, 2026, https://understandingwar.org/research/middle-east/iran-update-special-report-may-29-2026/
- Iranian strike to Kuwait injured Americans and destroyed Reaper drones: Report, accessed May 30, 2026, https://www.turkiyetoday.com/region/iranian-strike-to-kuwait-injured-americans-and-destroyed-reaper-drones-report-3220937
- US weapons stockpile depleted after Iran strikes, rebuilding could take 3 years: Report, accessed May 30, 2026, https://indianexpress.com/article/world/us-military-munitions-shortage-operation-epic-fury-iran-china-conflict-risk-10711198/
- US ‘more than capable’ of resuming war against Iran, Pete Hegseth says, accessed May 30, 2026, https://www.theguardian.com/world/2026/may/30/us-more-than-capable-of-resuming-war-against-iran-pete-hegseth-says
- Live Coverage of the Iran–U.S.–Israel Conflict / May 30, accessed May 30, 2026, https://wanaen.com/live-coverage-of-the-iran-u-s-israel-conflict-may-30/
- Meet Ahmad Vahidi, Commander-in-Chief of IRGC | Is He Running Iran? | Vantage on Firstpost | 4K, accessed May 30, 2026, https://www.youtube.com/watch?v=C1uiGQ_EECw
- US adds Persian Gulf Strait Authority to sanctions list, Treasury website shows, accessed May 30, 2026, https://www.al-monitor.com/originals/2026/05/us-adds-persian-gulf-strait-authority-sanctions-list-treasury-website-shows
- Iran-related Designation; Counter Terrorism Designation | Office of Foreign Assets Control, accessed May 30, 2026, https://ofac.treasury.gov/recent-actions/20260527_33
- US declares new sanctions on Iran, PGSA condemns efforts in Hormuz, accessed May 30, 2026, https://www.jpost.com/international/article-897778
- PGSA Dismisses US Sanctions – Politics news – Tasnim News Agency, accessed May 30, 2026, https://www.tasnimnews.ir/en/news/2026/05/30/3603615/pgsa-dismisses-us-sanctions
- Several Americans hurt in missile attack on Kuwaiti air base as Bitcoin drops below $73K, accessed May 30, 2026, https://cryptobriefing.com/missile-attack-kuwait-bitcoin-drops/
- US sanctions 16 companies, Indian national and eight tankers over Iranian oil network, accessed May 30, 2026, https://en.portnews.ru/news/392175/
- The U.S. has imposed new sanctions on Iranian oil exports — Associated Press, accessed May 30, 2026, https://ua.news/en/world/ssha-zaprovadili-novi-sanktsiyi-proti-eksportu-iranskoyi-nafti-associated-press
- From Watchlist Updates to Early Risk Signals: What OFAC’s Latest Iran Sanctions Show About Modern Screening – Sigma360, accessed May 30, 2026, https://www.sigma360.com/ofac-sanctions-target-irans-military-oil-sales/
- Israel-Iran war LIVE: Israeli army issues evacuation orders for seven south Lebanon villages, accessed May 30, 2026, https://www.thehindu.com/news/international/iran-israel-war-live-strait-of-hormuz-trump-peace-deal-updates-on-may-30-2026/article71040085.ece