Executive Summary (BLUF)
The contemporary operational environment for law enforcement and tactical units is increasingly defined by the convergence of digital data streams and physical kinetic actions. Open-Source Intelligence (OSINT) and Social Media Intelligence (SOCMINT)—historically utilized as slow-moving, post-incident investigative tools—have evolved into mission-critical, real-time assets. When properly filtered, analyzed, and disseminated, social media data provides deployed forces with unprecedented situational awareness, enabling pre-mission environment shaping, real-time threat detection, and dynamic tactical adjustments during high-risk operations.
In the highly volatile realm of global security, criminal networks, terrorist organizations, and hostile crowds have mastered the use of ubiquitous digital platforms to advance their goals, communicate intent, and orchestrate physical movements. To counter these technologically enabled asymmetric threat vectors, law enforcement agencies must transition their intelligence apparatus from a state of passive historical collection to active, real-time exploitation. This transformation requires a highly technical architecture that aggressively filters the infinite noise of the internet, extracts verified threat indicators using artificial intelligence, and pushes concise, geolocated intelligence directly to the tactical edge without overwhelming the operator’s cognitive load.
This comprehensive analysis examines the technical data pipelines, operational workflows, and hardware procurement strategies required to transform vast, unstructured public data into actionable intelligence for tactical elements. The report details the transition of data from cloud-based multi-platform scrapers and AI-driven signal-to-noise filters, through the centralized command hub of a Real-Time Crime Center (RTCC), and ultimately to the operator at the tactical edge via the Android Tactical Assault Kit (ATAK) and mesh-networked End User Devices. Through the examination of operational case studies encompassing civil unrest, hostage rescues, and fugitive apprehension, this white paper demonstrates that the integration of OSINT into the tactical Common Operational Picture drastically reduces the latency between intelligence collection and kinetic execution. Furthermore, the analysis provides command staff and procurement officers with vendor landscape evaluations, pricing models, and strategic recommendations for legally compliant, technologically robust intelligence frameworks.
1.0 Introduction: The Evolution of Tactical OSINT and SOCMINT
The proliferation of ubiquitous internet connectivity, smartphone penetration, and social media engagement has fundamentally altered the landscape of law enforcement intelligence.1 Open-source intelligence—defined strictly within the intelligence community as intelligence derived exclusively from publicly or commercially available information that addresses specific intelligence priorities, requirements, or gaps—now accounts for the vast majority of actionable data utilized by the defense and law enforcement sectors.2 According to historical assessments by the Defense Intelligence Agency, OSINT provides roughly ninety percent of the information used by the broader intelligence community, rendering it an indispensable pillar of modern security operations.3 Within this broader domain, Social Media Intelligence provides unique, real-time insights into suspect movements, organizational structures, public sentiment, and immediate physical threats.4
Historically, OSINT was primarily a strategic, investigative asset. Analysts would spend days or weeks manually aggregating public records, forum posts, news articles, and financial data to build long-term criminal network profiles or assess the historical trajectory of threat actors.6 This methodology traces its roots back to the Second World War, where intelligence agencies monitored enemy radio broadcasts and propaganda to gauge troop morale and strategic intent without requiring clandestine border crossings.8 However, the transformation of the internet from a read-only Web 1.0 environment to a user-generated Web 2.0 ecosystem heralded a new era of intelligence.9 The modern threat matrix is now characterized by flash mobs, highly organized civil unrest, live-streamed active shooter events, and the rapid, decentralized movement of fugitives. This environment demands a tactical application of OSINT. Tactical OSINT requires the near-instantaneous collection, verification, and dissemination of data to ground force commanders and operators actively engaged in a mission, providing them with near-real-time information critical to split-second decision-making.3
The critical challenge facing law enforcement command staff today is no longer data scarcity, but rather data overload.10 Over forty-one percent of the global population has access to smartphones, creating a continuous stream of uploaded images, videos, opinions, and geospatial metadata.1 During a crisis, the sheer volume, velocity, and variety of unstructured data generated across the internet can quickly paralyze an intelligence unit.11 Therefore, maximizing the use of social media for OSINT relies on establishing a highly technical, automated data pipeline. This infrastructure must aggressively filter noise, extract relevant threat indicators via advanced artificial intelligence, and push concise, geolocated intelligence directly to the tactical edge.13
2.0 Technical Architecture of Real-Time OSINT Data Pipelines
To make OSINT actionable for deployed forces, agencies must implement a structured, automated intelligence architecture. Relying on manual searches across disparate social media platforms using standard web browsers is a lethal vulnerability in fast-paced kinetic environments, leading to unacceptable latency and the risk of missing critical links hidden within vast digital silos.10 The modern pipeline consists of automated ingestion, artificial intelligence filtering, and precise geospatial anchoring.
2.1 Data Ingestion and Multi-Platform Scraping
The foundation of the tactical OSINT pipeline is the continuous, automated ingestion of data from the surface web, deep web, and dark web. Modern OSINT platforms utilize Application Programming Interfaces (APIs) and advanced web scraping tools to monitor target vectors across hundreds of platforms simultaneously, transforming unstructured chaos into a unified, real-time intelligence layer.10
Enterprise platforms such as ShadowDragon’s SocialNet and Fivecast ONYX provide investigators with access to over two hundred distinct online data sources.20 These systems consolidate social media posts, messaging app communications on platforms like Telegram and WhatsApp, domain records, financial transactions, and dark web breach data into a single operational interface.18 Crucially, this ingestion is not limited to text-based analysis; it encompasses multimodal data, including high-resolution images, live-streamed video, audio files, and embedded geospatial metadata.17
For tactical teams, this ingestion must be hyper-local and chronologically immediate. Analysts utilize digital profiling and geofencing technologies to draw a digital perimeter around a target building, a planned protest route, or a hostage stronghold.17 This localized ingestion captures all public social media activity originating within that specific physical space, allowing the intelligence cell to identify the presence of non-combatants, the establishment of suspect fortifications, or the arrival of hostile reinforcements prior to a dynamic breach.23 Furthermore, advanced tools allow analysts to use advertising intelligence (ADINT) to track device movements and identifiers across multiple ad networks, providing an alternative vector for location tracking when standard social media signals are obfuscated.17
2.2 Signal-to-Noise Reduction and AI-Enabled Filtering
The fundamental mathematical and operational challenge of OSINT is optimizing the Signal-to-Noise Ratio. During a highly publicized event, such as a major riot or a terrorist attack, the exponential increase in public social media posting creates massive data noise. Manual processing latency increases proportionally, effectively reducing the value of the intelligence to zero before the tactical element can act upon it.8
To solve this latency, law enforcement agencies must deploy Artificial Intelligence and Machine Learning algorithms directly at the ingestion layer.13 These technologies serve as the primary filter, allowing human analysts to focus on verification rather than discovery. Modern platforms utilize several distinct AI vectors. Natural Language Processing scans unstructured text in over one hundred languages to identify specific threat indicators, criminal slang, or mentions of weaponry, bridging critical linguistic gaps during transnational investigations.11 Computer Vision algorithms analyze massive volumes of uploaded images and video to automatically identify specific objects—such as firearms, explosive precursors, or tactical gear—as well as logos or specific individuals via facial recognition overlays.14 Additionally, Sentiment Analysis monitors the emotional tone of a crowd’s digital footprint. A sudden algorithmic detection of a shift from peaceful rhetoric to violent coordination on platforms like X or Telegram can serve as an invaluable early warning indicator for deployed riot control units.3
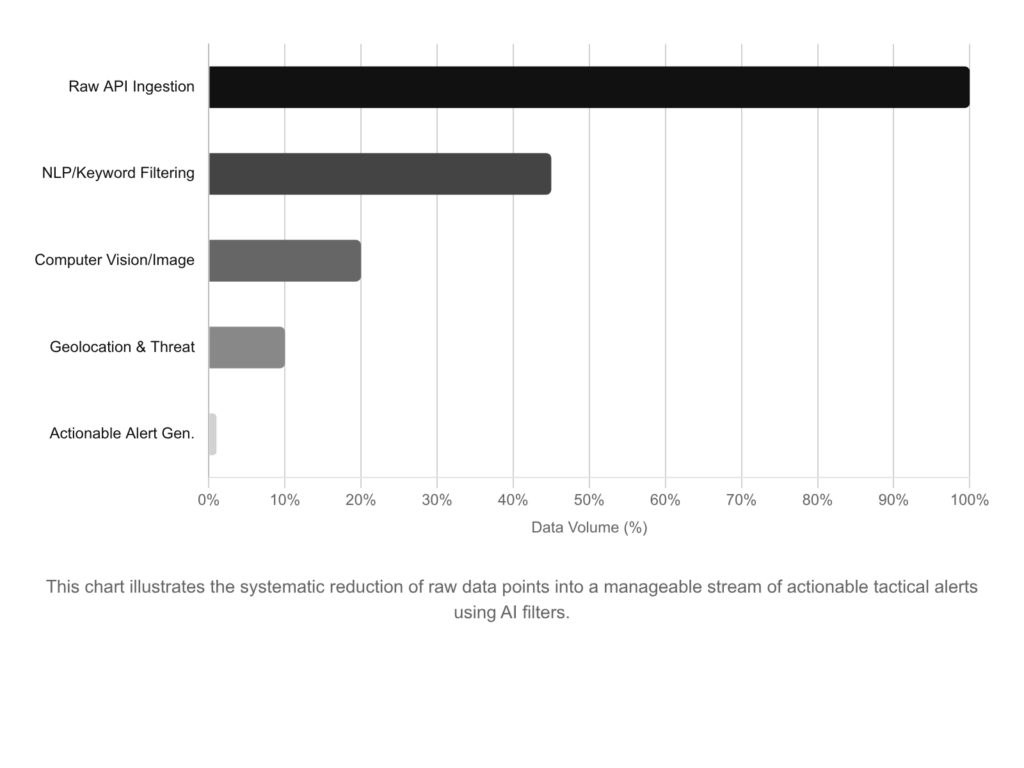
The following visual representation illustrates the critical impact of AI filtering on the data pipeline, demonstrating how millions of raw data points are systematically reduced into a manageable stream of tactical alerts suitable for field dissemination.
CHART 1.0: OSINT DATA FUNNEL AND AI SIGNAL-TO-NOISE REDUCTION
2.3 Advanced Visual Geolocation and Chronolocation Techniques
Intelligence is tactically useless if it cannot be mapped to physical space. Determining the exact physical location of a suspect, victim, or hostile crowd based on their digital footprint is the most critical step in translating OSINT into kinetic action.19 While the digital environment is vast, every action leaves a trace that can be anchored to the physical world through rigorous analytical techniques.
Analysts employ multiple technical methods to extract and verify location data. The most direct method involves extracting Geotags and Metadata, specifically the Exchangeable Image File Format data embedded within digital photographs, which frequently contains exact Global Positioning System coordinates detailing where the device was located when the image was captured.4 However, sophisticated threat actors routinely scrub metadata before posting. In these instances, analysts pivot to Visual Geolocation and landmark identification. This technique involves analyzing visual clues within the media, such as architectural styles, unique vegetation, street signs, or infrastructure patterns.25 AI-driven tools like Picarta.ai, GeoSpy, and Google’s Cloud Vision API (Gvision) assist analysts by cross-referencing these visual features against global databases like Google Street View and OpenStreetMap to predict the location with high accuracy.26
Furthermore, analysts utilize Chronolocation—often referred to as shadow analysis—to verify the exact timeline of a target’s movements. By utilizing tools like SunCalc, investigators can analyze the angle, direction, and length of shadows cast by objects in a photograph or video.25 By calculating the sun’s position relative to the visually identified geographic coordinates, analysts can determine the exact time of day the media was captured, proving whether an image is a live representation of a threat or a recycled piece of disinformation.25 Finally, IP Address tracing and the analysis of network traffic patterns provide an approximate geographical radius of a device, narrowing the search field for subsequent visual analysis.26
When combined, these techniques create a robust digital breadcrumb trail.6 For example, a target may post an image without a geotag, but visual analysis identifies a specific intersection in the background, and chronolocation verifies the image was taken within the last ten minutes. This multidimensional verification allows command staff to adjust the deployment of containment perimeters or direct tactical teams with absolute confidence.4
3.0 Command and Control: The Real-Time Crime Center Ecosystem
The most sophisticated OSINT collection is rendered obsolete if it remains trapped on an analyst’s desktop inside headquarters. The intelligence must be pushed securely, rapidly, and legibly to the operators in the field, who are often operating in chaotic, low-bandwidth, or hostile environments.29 The bridge between the digital intelligence cloud and the physical tactical edge is the Real-Time Crime Center.
3.1 Centralized Data Fusion and Software Integration
Real-Time Crime Centers serve as the centralized nervous system for modern law enforcement operations.30 These specialized public safety units function as hubs where criminal information and intelligence analysis are fused into a cohesive operational picture. RTCCs ingest the AI-filtered OSINT from platforms like ShadowDragon and Fivecast and fuse it with a multitude of other proprietary data streams. These internal streams include computer-aided dispatch (CAD) data, fixed closed-circuit television cameras, automated license plate readers, municipal drone feeds, and body-worn camera transmissions.31
Platforms such as Axon Fusus provide the critical single-pane-of-glass interface required by the RTCC analyst.31 The workflow is highly integrated: when a social media threat is detected and geolocated by an OSINT platform, the RTCC analyst receives an immediate alert.20 The analyst can then utilize the Fusus map-based interface to pull up the nearest public or registered private security cameras to physically verify the digital threat in real time.34 Once verified, the RTCC acts as the dissemination node, packaging the intelligence—such as target photos, exact coordinates, known associates, and building floor plans—and pushing it directly to the tactical teams navigating to the objective.23
3.2 Regional Hubs and Information Sharing
The efficacy of an RTCC relies on regional interoperability and information sharing. The Michigan State Police provide a premier example of this architecture through the Michigan Intelligence Operations Center, a fusion center that provides continuous statewide information sharing among local, state, and federal public safety agencies.36 Regional Communication Centers across Michigan, such as those in Dimondale, Detroit, and Gaylord, provide direct operational support to specialty teams, integrating live highway camera feeds and intelligence data to support real-time decision-making.37
At the county level, interoperability is achieved through shared public safety software. For instance, the Berrien County Board of Commissioners in Michigan recently supported the implementation of a Mobile CAD program to expand access to real-time dispatch information, mapping, and resource data across forty-seven distinct first responding agencies within the county.38 This technological expansion, supported by strategic partnerships with software providers like Mark43 and Mi-Case, ensures that even smaller, resource-constrained municipal departments have the situational awareness necessary to coordinate seamlessly with county sheriffs and federal entities like the FBI during complex, multi-jurisdictional operations.40
4.0 Tactical Edge Dissemination: ATAK and the Common Operational Picture
To receive real-time OSINT at the point of impact, deployed forces increasingly utilize the Android Team Awareness Kit, an advanced geospatial infrastructure and military-grade situational awareness application originally developed by the Department of Defense.15 ATAK provides a Common Operational Picture, ensuring that the tactical commander, the RTCC analysts, and every individual operator in the stack share the exact same interactive map and intelligence overlay.29
4.1 Cursor on Target and Plugin Infrastructure
ATAK operates on a protocol known as Cursor on Target, a standardized XML-based schema designed to communicate the what, when, and where of any entity or event across disparate software systems.43 The power of ATAK lies in its open-source standard, allowing developers to create highly specialized plugins that integrate external intelligence feeds directly into the operator’s display.47
OSINT feeds are seamlessly integrated into ATAK via aggregator plugins like TrakBridge, which converts external location APIs and open-source intelligence feeds—such as the DeepStateMap live feed—into CoT format.48 When an RTCC analyst identifies a critical OSINT update, such as a hostage taker posting a live stream from a specific room within a stronghold, the analyst drops a CoT marker on their interface. Instantly, every operator on the entry team receives the update on their device. They can view the target building mapped out, with a red hostile icon indicating the suspect’s exact location, complete with an attached screenshot extracted from the social media live stream.15
This visual integration is revolutionary for tactical operations. It prevents the fatal funnel of traditional radio communication, where complex descriptions of suspect clothing, building layouts, or precise coordinate data are frequently misunderstood over crackling, congested, and high-stress radio traffic. Instead, operators receive high-fidelity, visual intelligence that requires minimal cognitive processing to understand.49 Furthermore, Unmanned Aerial Systems (UAS) plugins integrate commercial drones directly into the network, projecting the drone’s map position, sensor field of view, and live video feed onto the ATAK screens of ground personnel.43
4.2 Weapon-Mounted Displays and Visual Augmentation
The integration of OSINT and situational awareness does not stop at the handheld device; it extends directly to the operator’s weapon system and optics. Engaging with a handheld screen during a kinetic firefight degrades an operator’s readiness. To mitigate this, advanced optical systems like the Enhanced Clip-on Thermal Viewer (ECOTI) and the Enhanced Clip-on SWIR Imager (ECOSI) integrate directly with ATAK.50
These visual augmentation systems attach to standard night vision devices, providing a long-wave infrared thermal overlay.50 Crucially, the ECOTI acts as a Heads-Up Display for ATAK. The augmented reality capability connects to the application and projects CoT markers, navigation waypoints, and identified threat locations directly into the operator’s field of view.50 This allows an operator to look down a dark hallway and see a digital augmented reality waypoint indicating the OSINT-derived location of a threat behind a specific door, facilitating entirely hands-free operation while keeping their primary weapon oriented toward the threat.50
5.0 Hardware Procurement for the Denied Environment
Delivering OSINT via ATAK requires robust, specialized hardware. Consumer-grade smartphones are entirely insufficient for tactical kinetic environments due to their physical fragility, inadequate battery life under heavy GPS loads, and fatal reliance on commercial cellular towers. During mass casualty events, natural disasters, or large-scale civil unrest, commercial networks frequently crash due to user overload, physical destruction, or deliberate geographic shutdowns.43
5.1 Tactical End User Devices and Tablets
Procurement officers must invest in ruggedized End User Devices. Devices utilized by tactical teams must be root-enabled Android architectures, allowing them to run ATAK and associated security plugins without the interference of commercial bloatware or forced operating system updates that could compromise the software environment.52 Devices such as the GoTAK EUD V2 and the GoTAK Pro Tab offer MIL-STD-810G compliance, guaranteeing resistance to drops, water, dust, and extreme temperature fluctuations, alongside massive battery capacities.52
Similarly, Samsung Galaxy Tactical Editions provide enhanced GPS chipsets for precise location tracking in dense urban environments and utilize Knox encryption to protect the transmission of classified intelligence.54 For vehicle-mounted command elements, crash scene investigators, or mobile RTCC units, larger rugged tablets provide the necessary screen real estate for complex OSINT mapping and multi-feed video monitoring.
The following Markdown table details the technical specifications of standard ruggedized tablets utilized within law enforcement procurement channels to support tactical situational awareness:
| Tablet Specification | Panasonic Toughpad FZ-G1 | iX104C5 DMSR LTE Tablet | xTablet T1200 |
| Ingress Protection | IP65 (Dust tight, water jets) 55 | IP67 (Dust tight, immersion) 55 | IP65 55 |
| Operating Temp Range | 14°F to 122°F 55 | -30°F to 140°F 55 | -4°F to 140°F 55 |
| Impact Resistance | Drop tested to 4 feet 55 | 26 drops operating from 4 feet 55 | Drop tested 55 |
| Battery Runtime | 8.0 hours continuous 55 | 6.5 hours continuous 55 | 11.5 hours continuous 55 |
| Key Features | Auto-brightness, responsive touch 55 | Physical keypad, integrated biometrics 55 | High battery capacity 55 |
To ensure that these devices remain accessible during operations, tactical teams utilize specialized mounting solutions. End User Devices are typically mounted directly to the operator’s plate carrier via chest mounts manufactured by companies like Juggernaut.Case or Kagwerks. These mounts allow the operator to quickly hinge the device downward to view the ATAK map and OSINT feeds, then fold it flat and secure against their ballistic armor, keeping both hands free for weapon manipulation.56
5.2 Tactical Mesh Networking Platforms
To maintain the flow of OSINT and ATAK data when traditional cellular infrastructure is degraded or denied, law enforcement agencies utilize Tactical Mesh Networks. Mesh networking creates a decentralized, peer-to-peer communication system. Instead of relying on a centralized cell tower, each individual radio acts as a node, bouncing encrypted data—such as CoT markers, text messages, and low-bandwidth images—from operator to operator until it reaches the intended recipient.15 This architecture is self-healing; if one node moves out of range or is destroyed, the network automatically calculates a new routing path without disrupting the overall operation.15
The following Markdown table outlines the technical specifications of two dominant mesh networking hardware platforms critical for OSINT dissemination in off-grid environments:
| Hardware Specification | goTenna Pro X2 | Persistent Systems MPU5 |
| Primary Use Case | Low-cost UHF/VHF data, location tracking, text. | High-bandwidth MANET, live video streaming. |
| Operating Frequencies | VHF (142 to 175 MHz), UHF (445 to 480 MHz). | Modular bands (L-Band, S-Band, C-Band). |
| Physical Weight | 100 grams (ultra-lightweight). | Approximately 800+ grams (with battery). |
| Power Output Settings | 0.5W, 1.0W, 2.0W, 5.0W (User Selectable). | Up to 6.0W transmission power. |
| Battery Life / Power | Up to 9 hours nominal (30+ hours standby). | 10 to 12 hours depending on module. |
| Integration | Connects to EUD via Bluetooth/USB; ATAK plugin. | Native Kinesis/Wave Relay integration. |
6.0 Operational Case Studies and Tactical Application
The theoretical architecture of OSINT is validated by its application in real-world kinetic environments. The following operational parameters demonstrate how the fusion of digital intelligence and tactical hardware directly alters law enforcement decision-making.
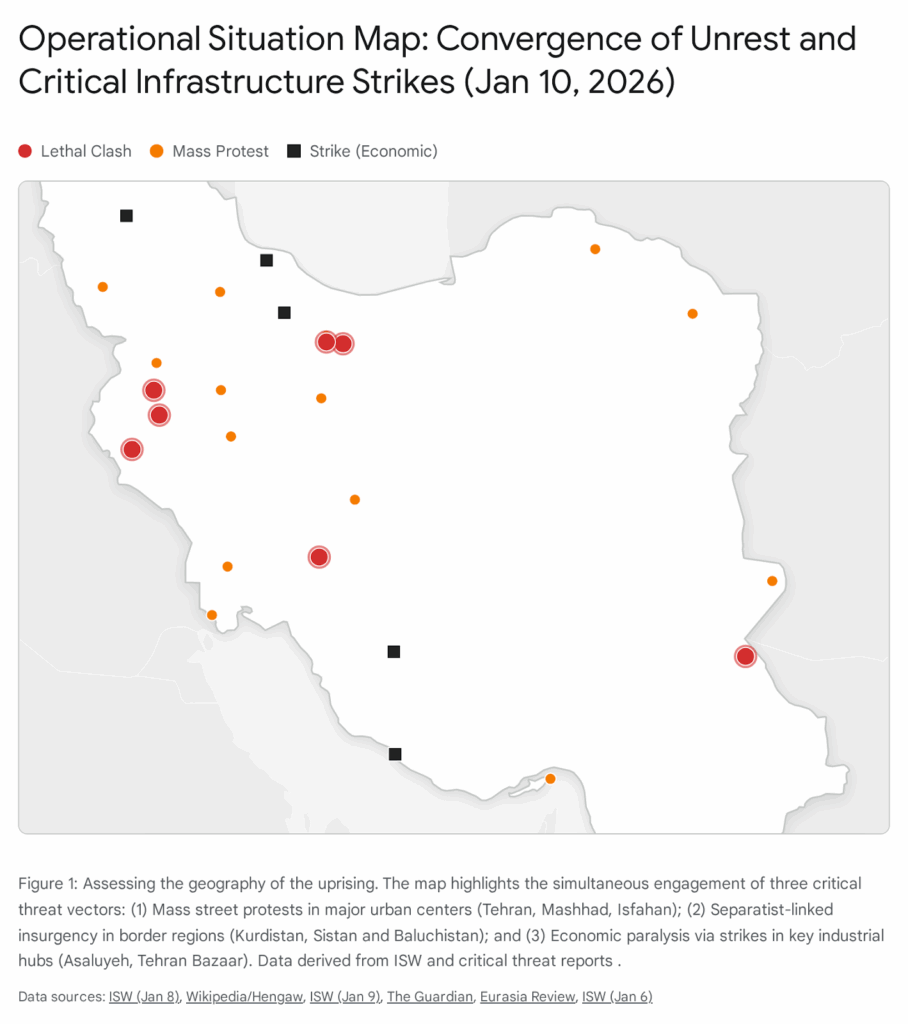
6.1 Civil Unrest, Riots, and Public Demonstrations
During civil unrest, large crowds utilize social media to organize, maneuver, and overwhelm law enforcement containment lines. Adversaries use platforms like Telegram, X, and localized mapping applications to track police movements in real time, executing flash mob tactics or targeted vandalism.3 A poignant example occurred during the 2019 to 2020 Hong Kong protests, where demonstrators utilized the HKMap Live application to crowdsource the composition and disposition of police forces. This allowed untrained noncombatants to communicate intent and mass manpower at times and places of their choosing, effectively outmaneuvering traditional police deployments.3 Similarly, the organization surrounding the events at the U.S. Capitol on January 6, 2020, relied heavily on open digital networks to direct members toward specific geographic objectives.61
By applying AI-driven sentiment analysis and keyword tracking, an RTCC can monitor the digital buildup to a protest, identifying specific nodes of agitation and potential flashpoints for violence before they materialize physically.23 During the event, SOCMINT provides minute-by-minute intelligence regarding the crowd’s size, demeanor, and intended route.23 If OSINT scrapers detect a sudden spike in keywords relating to incendiary devices geographically clustered around a specific intersection, the RTCC can instantly push a warning to the mobile field force commander via ATAK.24 The commander, viewing the common operational picture on a ruggedized tablet, can proactively maneuver armored assets and riot control formations to that exact intersection to deter the escalation. Furthermore, advanced visual analysis of crowd live streams can identify primary instigators or individuals carrying concealed firearms within the group, allowing snatch-and-grab arrest teams to execute precise, targeted removals without engaging the broader, peaceful crowd.61
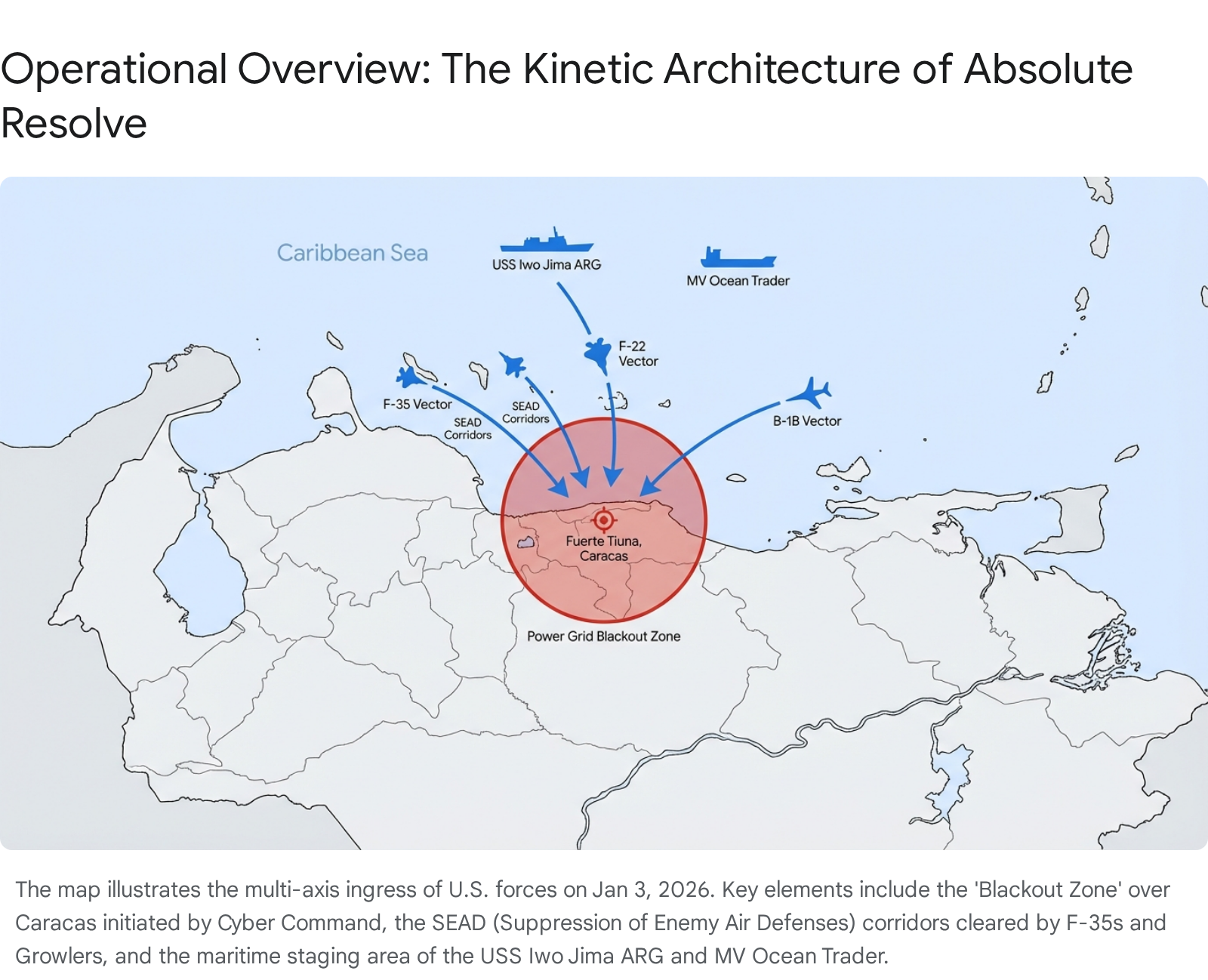
6.2 Hostage Rescues and Active Shooter Interventions
In hostage barricade or active shooter scenarios, time is the ultimate friction. Traditional intelligence gathering—relying on post-incident witness interviews or prolonged negotiations—is often too slow to prevent casualties. Suspects frequently broadcast their actions, demands, or grievances via social media live streams or manifestos posted immediately prior to the event, creating a real-time digital intelligence footprint.63
When a barricaded subject initiates a standoff, off-site OSINT analysts immediately begin scraping the suspect’s digital presence. If the suspect is live-streaming, analysts perform rapid visual geolocation of the interior background. They analyze the layout of the room, the placement of the suspect’s primary weapon, the presence of improvised explosive devices, and the condition of the hostages.23 This intelligence is fed directly to the SWAT commander and the entry team stacked at the breach point. For example, if OSINT confirms via a social media post that the suspect has heavily fortified the primary door and established a fatal funnel, the tactical team will adjust their approach, opting for an explosive breach on a secondary wall or a coordinated multi-port window assault.
The kinetic value of immediate intelligence gathering is starkly illustrated by international operations. During the Israeli Yamam counter-terrorism unit’s daytime rescue of four hostages in the Nuseirat neighborhood of Gaza, operations were heavily supported by massive intelligence and IDF data integration. While the high casualty rate of the extraction underscores the extreme violence of such operations in dense urban terrain, the ability to pinpoint hostage locations in a hostile environment demonstrates the absolute necessity of fused intelligence before operators cross the threshold.65 On the domestic front, failures to rapidly synthesize and communicate intelligence during active shooter events, such as the tragic incident at Robb Elementary in Uvalde, Texas, highlight the catastrophic consequences of disjointed command and control and the failure to establish a unified operational picture.66
Furthermore, OSINT is crucial in combating the rise of swatting—the false reporting of a hostage or active shooter situation designed to provoke a lethal SWAT response against an innocent target.63 Real-time OSINT analysis can quickly cross-reference the target address, the caller’s digital footprint, and local social media chatter to determine if the threat is a verified emergency or a malicious hoax, preventing unnecessary kinetic engagement and preserving community trust.63
6.3 Fugitive Apprehension and Human Trafficking Syndicates
Tracking high-value fugitives or dismantling human trafficking networks requires meticulous pre-mission intelligence. Modern criminal syndicates operate across encrypted applications, utilizing multiple digital aliases, cryptocurrency transactions, and sophisticated counter-surveillance techniques.67
Platforms like ShadowDragon enable investigators to rapidly resolve aliases, map digital connections, and identify the physical locations of transient fugitives without tipping off the target.68 By combining breach data, domain registration records, and social media geotags, an analyst can generate a comprehensive target profile in minutes.28 In a notable counter-terrorism and fugitive apprehension case study, analysts utilized a combination of social media analysis, deep web breach data, and public fitness tracking applications. By identifying the target’s public Strava account, analysts mapped the fugitive’s exact cycling routes, daily routines, and frequent physical locations.28 This digital intelligence was then cross-referenced with deep web leak data originating from a Malaysian database breach to confirm the suspect’s passport numbers and physical addresses.28
For the deployed apprehension team, this OSINT translates directly into actionable operational planning. The tactical commander knows the suspect’s exact routine, the vehicles they use, and their known associates. The arrest can be timed to occur when the suspect is in transit or away from fortified strongholds, minimizing the risk of an armed standoff. This methodology is heavily utilized in child exploitation cases. Investigators deploy advanced technical skills to analyze deeply buried digital breadcrumbs to dismantle the highly curated personas and digital universes created by predators to target children, bringing perpetrators to justice through rigorous open-source correlation.6 The integration of modern OSINT methodologies, encrypted app tracing, and traditional intelligence provides a holistic view of the operational environment, akin to the multi-disciplinary intelligence fusion that eventually led to the capture of high-profile cartel leaders like El Chapo.67
7.0 Legal, Ethical, and Policy Frameworks
The immense power of tactical OSINT is counterbalanced by strict legal, constitutional, and ethical limitations. Law enforcement command staff must ensure that intelligence collection does not violate civil liberties, specifically Fourth Amendment protections against unreasonable search and seizure, and First Amendment rights regarding peaceful assembly and expression.70
7.1 Constitutional Boundaries and Warrant Requirements
While OSINT inherently relies on publicly available information, the aggregation, persistent monitoring, and algorithmic profiling of citizens can cross the legal threshold into unlawful surveillance.8 Civil rights organizations and legal scholars frequently challenge the use of automated social media scrapers, particularly during protests associated with political movements.70 The core legal concern is that covert surveillance via automated bots infringes upon the penumbras of privacy established by Supreme Court precedent in landmark cases such as Griswold v. Connecticut, which recognized privacy rights existing within the shadows of the protections provided by the Bill of Rights.71 Further scrutiny has been applied to federal agencies; for instance, the Department of Homeland Security and Immigration and Customs Enforcement have faced significant backlash over the procurement of OSINT tools like ShadowDragon to compile dossiers on advocates and journalists.70
Therefore, agencies must operate under the principle that while an individual social media post may be public, the persistent, targeted monitoring of a specific individual’s comprehensive digital life over time often requires judicial oversight. In jurisdictions like the United Kingdom, the Investigatory Powers Act 2016 provides a strict legal framework requiring law enforcement and intelligence agencies to obtain appropriate warrants and undergo judicial approval before conducting bulk data collection or targeted SOCMINT operations.5 United States agencies must continuously consult with local prosecutors to determine the exact threshold at which open-source observation transitions into a Fourth Amendment search requiring a warrant.
7.2 Standard Operating Procedures and Auditability
To protect the agency from civil liability and ensure the admissibility of OSINT-derived evidence in criminal court, departments must implement rigorous Standard Operating Procedures.74
Analysts must mathematically verify the authenticity of all digital evidence. Because metadata can be spoofed and generative AI can create highly convincing deepfakes, analysts must cross-reference data points and meticulously document the chain of custody for digital evidence, including capturing timestamps, URLs, and generating cryptographic hash values of downloaded media to prove it has not been altered.11
Furthermore, OSINT software platforms must maintain unalterable, automated audit logs detailing exactly what data was queried, which analyst queried it, and the legal justification or case number associated with the search.21 This infrastructure prevents the misuse of powerful intelligence tools for unauthorized personal searches or political targeting, ensuring adherence to ethical boundaries.8 Finally, agencies must maintain clear, publicly accessible policies regarding how they utilize social media monitoring. For example, Berrien County, Michigan, publicly outlines its social media monitoring guidelines and terms of service, actively managing public expectations regarding privacy, data retention, and government interaction on digital platforms.77
8.0 Vendor Landscape and Procurement Economics
For procurement officers, command staff, and defense contractors, the OSINT market offers a wide spectrum of solutions ranging from pure data aggregators to comprehensive AI analysis suites. Procurement requires balancing municipal or federal budget constraints with the absolute operational necessity for high-fidelity, real-time tactical support. Deploying OSINT to the tactical edge requires heavy, sustained investment in both the Real-Time Crime Center software infrastructure and the ruggedized hardware carried by operators.
8.1 Software Licensing Models and Infrastructure Costs
The enterprise OSINT software market operates predominantly on Software-as-a-Service (SaaS) and tiered licensing models based on data volume, feature access, and the number of user seats.
| OSINT Platform / Vendor | Primary Capability Focus | Key Technical Features | Representative Pricing / Est. Cost |
| ShadowDragon (SocialNet / Horizon) 20 | Identity resolution, alias tracking, dark/deep web correlation. | API access, Kaseware integration, Link Analysis, over 200 data sources. | Enterprise licensing. (e.g., ICE contract: approx. $900k; DEA contract: approx. $29M for unlimited queries).73 |
| Fivecast ONYX 21 | AI-driven threat detection, multimodal analysis, mass data ingestion. | Customizable risk detectors, image/text/video AI analysis, multilingual support. | Proprietary quote based on data volume and seat licenses. |
| Flashpoint Ignite 82 | Cyber threat intelligence, vulnerability monitoring, illicit community tracking. | Dark web search, ransomware correlation, managed attribution (anonymous browsing). | Tiered SaaS. Approx. $100,000/yr for Cyber Threat Intel; Approx. $80,000/yr for Physical Security Intel.82 |
| Axon Fusus (RTCC Platform) 85 | RTCC video fusion, CAD integration, live mapping. | Unified map interface, AI camera alerts, drone feed integration. | SaaS subscription. Core Lite: approx. $350 initial. Core Elite AI: approx. $7,300+ annually.85 |
Beyond the recurring software licensing costs, agencies must account for the physical hardware required. Supplying a SWAT team with ATAK capabilities involves purchasing End User Devices (such as the GoTAK EUD V2 at approximately $600 to $1000 per unit), tactical chest mounts (ranging from $150 to $300 per unit), and tactical mesh radios (such as the goTenna Pro X2, which can cost in excess of $1000 per unit depending on government contract pricing).52 This does not include the massive capital expenditure required to physically build out the RTCC, which involves procuring video walls, secure servers, and specialized workstations.87
9.0 Strategic Directives for Command Staff
To successfully maximize the use of social media and open-source intelligence in real-time tactical operations, law enforcement command staff must transition their agencies from reactive data consumers to proactive intelligence exploiters. This requires adopting the following strategic directives:
First, agencies must establish a dedicated Tactical OSINT Desk within the Real-Time Crime Center. Command cannot rely on patrol officers or tactical operators to conduct their own digital intelligence gathering on standard smartphones while deployed. Agencies must assign dedicated, highly trained intelligence analysts to operate advanced platforms like Fivecast ONYX or ShadowDragon. These analysts must be trained not just in digital scraping techniques, but in tactical terminology, close-quarters battle concepts, and operational priorities, allowing them to rapidly filter out noise and push only critical, actionable data to the field.23
Second, the agency must standardize on the Android Team Awareness Kit for intelligence dissemination. Transitioning tactical teams away from voice-only radio descriptions of targets and locations is a critical safety imperative. By implementing ATAK as the standard Common Operational Picture, command ensures that all OSINT feeds, drone video, and RTCC alerts are converted into Cursor on Target format, providing operators with an instantly understandable, shared visual map of the battlespace.43
Third, procurement must invest heavily in resilient communications infrastructure. Command must assume that commercial cellular networks will fail, be compromised, or be deliberately shut down during a major critical incident. Equipping entry teams, mobile field forces, and crisis negotiators with tactical mesh radios ensures that the flow of OSINT data and live location tracking remains uninterrupted in off-grid or electronically denied environments.15
Finally, agencies must prioritize AI-enabled filtering solutions during software acquisition. The limiting factor in modern intelligence is human cognitive capacity. Artificial intelligence must handle the bulk sorting, natural language processing, and initial image recognition of the data pipeline so that human analysts can focus exclusively on threat verification, ethical oversight, and tactical coordination.10 By pairing robust algorithmic filtering with strict, judicially compliant standard operating procedures, law enforcement agencies can securely harness the digital domain, ensuring that operators cross the threshold with decisive, real-time intelligence.
Appendix: Methodology & Data Sources
The intelligence generated within this white paper was aggregated utilizing an Open-Source Intelligence framework, simulating the methodologies discussed herein. Data was acquired through structured queries targeting specialized B2B defense sector publications, government procurement databases, legal policy repositories, and technical documentation from primary vendors in the intelligence and tactical hardware space, including Axon, ShadowDragon, Fivecast, goTenna, and Juggernaut.Case. Search parameters included Boolean logic operators combining terms such as “Law Enforcement,” “Tactical OSINT,” “Real-Time Crime Center (RTCC),” “Android Team Awareness Kit (ATAK),” “Mesh Networking,” and “Social Media Intelligence (SOCMINT).” Cross-source validation was utilized to confirm technical specifications, legal precedents, and procurement pricing models across independent industry reports, academic literature, and official government press releases. The analysis focuses explicitly on the intersection of digital intelligence aggregation and physical kinetic application.
Ronin’s Grips Analytics provides custom, agency-specific data on this topic. Contact us to commission a tailored internal audit or procurement forecast for your department.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Sources Used
- The Tactical Application of Open Source Intelligence (OSINT) – The Cove – Australian Army, accessed March 6, 2026, https://cove.army.gov.au/article/tactical-application-open-source-intelligence-osint
- Open Source Intelligence Strategy – United States Department of State, accessed March 6, 2026, https://2021-2025.state.gov/open-source-intelligence-strategy/
- Event Barraging and the Death of Tactical Level Open-Source Intelligence – Army University Press, accessed March 6, 2026, https://www.armyupress.army.mil/Journals/Military-Review/English-Edition-Archives/January-February-2021/Rasak-Open-Source-Intelligence/
- Social media as an investigative tool: OSINT strategies for law enforcement – Police1, accessed March 6, 2026, https://www.police1.com/investigations/social-media-as-an-investigative-tool-osint-strategies-for-law-enforcement
- Social Media Intelligence (SOCMINT) in Modern Investigations – OSINT Industries, accessed March 6, 2026, https://www.osint.industries/post/social-media-intelligence-socmint-in-modern-investigations
- The Rise Of Open-Source Intelligence in Fighting Human Trafficking | Our Rescue, accessed March 6, 2026, https://ourrescue.org/resources/child-exploitation/the-rise-of-open-source-intelligence-in-fighting-human-trafficking
- Law Enforcement Technology Spotlight – OSINT – Carahsoft, accessed March 6, 2026, https://static.carahsoft.com/concrete/files/8617/5154/6816/Law_Enforcement_Tech_Spotlight_-_OSINT-v2.pdf
- What is OSINT (Open Source Intelligence)? – SentinelOne, accessed March 6, 2026, https://www.sentinelone.com/cybersecurity-101/threat-intelligence/open-source-intelligence-osint/
- The Future of Open Source Intelligence for UK National Security – RUSI, accessed March 6, 2026, https://static.rusi.org/330_OP_FutureOfOpenSourceIntelligence_FinalWeb0.pdf
- The data challenge facing modern law enforcement – Elastic, accessed March 6, 2026, https://www.elastic.co/resources/article
- Osint Geolocation Challenge – Knowlesys, accessed March 6, 2026, https://knowlesys.com/en/osint/osint-geolocation-challenge.html
- 13 OSINT Investigation Challenges: How to Overcome Them – ShadowDragon, accessed March 6, 2026, https://shadowdragon.io/blog/what-are-the-common-struggles-of-osint-investigations/
- Law Enforcement and Policing in the Era of Technological Transformation – ICT, accessed March 6, 2026, https://ict.org.il/era-of-technological-transformation/
- AI-Assisted OSINT/SOCMINT for Safeguarding Borders: A Systematic Review – MDPI, accessed March 6, 2026, https://www.mdpi.com/2078-2489/16/12/1095
- THE POWER OF ATAK + MESH NETWORKS – Sovereign Systems, accessed March 6, 2026, https://sovsys.co/the-power-of-atak-mesh-networks/
- Best Practices for Integrating Open-Source Intelligence (OSINT) into Investigations – Penlink, accessed March 6, 2026, https://www.penlink.com/blog/best-practices-for-integrating-osint-into-investigations/
- Top 15 Free OSINT Tools To Collect Data From Open Sources, accessed March 6, 2026, https://www.recordedfuture.com/threat-intelligence-101/tools-and-technologies/osint-tools
- Advanced OSINT Investigation Solutions for Law Enforcement | Social Links, accessed March 6, 2026, https://sociallinks.io/industries/leas-and-government
- OSINT Techniques: Complete List for Investigators (2026) – ShadowDragon, accessed March 6, 2026, https://shadowdragon.io/blog/osint-techniques/
- Unleashing the power of social media analysis tools in …, accessed March 6, 2026, https://shadowdragon.io/blog/social-media-investigation-tool-kaseware-shadowdragon-partner/
- Fivecast ONYX – Fivecast, accessed March 6, 2026, https://www.fivecast.com/platform-overview/fivecast-onyx/
- Social media OSINT: helping protect victims of exploitation. – CameraForensics, accessed March 6, 2026, https://www.cameraforensics.com/blog/2023/12/06/how-social-media-osint-can-help-safeguard-victims-of-online-exploitation/
- Social Media and Tactical Considerations for Law Enforcement – Agency Portal, accessed March 6, 2026, https://portal.cops.usdoj.gov/resourcecenter/content.ashx/cops-p261-pub.pdf
- Using OSINT in Managing Violent Protests – Fivecast, accessed March 6, 2026, https://www.fivecast.com/blog/violent-protests-and-the-role-of-osint/
- Geolocation Techniques in OSINT Investigations – McAfee Institute, accessed March 6, 2026, https://www.mcafeeinstitute.com/blog/geolocation-techniques-osint-investigations
- Understanding Geolocation OSINT – Medium, accessed March 6, 2026, https://medium.com/@tohkaaryani/understanding-geolocation-osint-4bfb01d2a7eb
- Geolocation 101: image-based OSINT tips and inspiration from unlikely places, accessed March 6, 2026, https://www.authentic8.com/blog/geolocation-101-image-based-tips-and-inspiration-unlikely-places
- OSINT Case Study: Leveraging SOCMINT and Breach Data for Counter-Terrorism, accessed March 6, 2026, https://infosecdad.medium.com/osint-case-study-leveraging-socmint-and-breach-data-for-counter-terrorism-3325d7a12b04
- Common Operating Picture (COP) for Battlefield Visualizations – Simulyze, accessed March 6, 2026, https://www.simulyze.com/common-operating-picture-software
- Building an effective real-time crime center: Tips, tools, and best practices from Texas experts, accessed March 6, 2026, https://peregrine.io/resources/building-an-effective-real-time-crime-center-tips-tools-and-best-practices-from-texas-experts
- The Ultimate Guide to Real-Time Crime Centers – Axon.com, accessed March 6, 2026, https://www.axon.com/resources/real-time-crime-center
- Real-Time Crime Centers: Integrating Technology to Enhance Public Safety, accessed March 6, 2026, https://www.ojp.gov/library/publications/real-time-crime-centers-integrating-technology-enhance-public-safety
- (PDF) Real-Time Crime Centers: Integrating Technology to Enhance Public Safety, accessed March 6, 2026, https://www.researchgate.net/publication/394148162_Real-Time_Crime_Centers_Integrating_Technology_to_Enhance_Public_Safety
- Unified real-time crime center interface – Axon.com, accessed March 6, 2026, https://www.axon.com/products/axon-fusus/unified-interface
- Axon Fusus | Real‑Time Intelligence Platform for Public Safety, accessed March 6, 2026, https://www.axon.com/products/axon-fusus
- Michigan Intelligence Operations Center (MIOC), accessed March 6, 2026, https://www.michigan.gov/msp/divisions/intel-ops/mioc
- Regional Communications Centers – State of Michigan, accessed March 6, 2026, https://www.michigan.gov/msp/divisions/intel-ops/rcc
- Untitled, accessed March 6, 2026, https://www.lctberrien.org/AgendaCenter/ViewFile/Item/2164?fileID=514
- Police in Berrien County hoping to improve dispatch communications with new software, accessed March 6, 2026, https://www.moodyonthemarket.com/police-in-berrien-county-hoping-to-improve-dispatch-communications-with-new-software/
- FBI conducting law enforcement operations in Berrien County – YouTube, accessed March 6, 2026, https://www.youtube.com/watch?v=aI-B5K4oSiE
- FBI conducting law enforcement operations in Berrien County, accessed March 6, 2026, https://www.wsjm.com/2025/11/19/fbi-conducting-law-enforcement-operations-in-berrien-county/
- Mark43 and Mi-Case Announce Partnership to Deliver a Comprehensive Public Safety Platform for Law Enforcement Agencies, accessed March 6, 2026, https://mark43.com/press/mark43-and-mi-case-announce-partnership/
- Tactical Awareness Kit (TAK): Ultimate Guide | RECOIL OFFGRID, accessed March 6, 2026, https://www.offgridweb.com/gear/tactical-awareness-kit-tak-ultimate-guide/
- kylesayrs/ATAK_push_cots: Push Cursor on Target messages to TAK clients with attachments and other information – GitHub, accessed March 6, 2026, https://github.com/kylesayrs/ATAK_push_cots
- Command and Control Personal Computer (C2PC) | Northrop Grumman, accessed March 6, 2026, https://www.northropgrumman.com/what-we-do/mission-solutions/command-and-control-personal-computer-c2pc
- ATAK Plugins 2: The TAK Server – RIIS LLC, accessed March 6, 2026, https://www.riis.com/blog/atak-plugins-2-the-tak-server
- Integrations – COTAK, accessed March 6, 2026, https://cotak.gov/pages/integrations
- First public release of TrakBridge : r/ATAK – Reddit, accessed March 6, 2026, https://www.reddit.com/r/ATAK/comments/1m3mhyk/first_public_release_of_trakbridge/
- Snapshot: ATAK increases situational awareness, communication – Homeland Security, accessed March 6, 2026, https://www.dhs.gov/archive/science-and-technology/news/2017/11/17/snapshot-atak-increases-situational-awareness-communication
- ATAK Enabling Technology with ECOTI – Quantico Tactical, accessed March 6, 2026, https://www.quanticotactical.com/atak-enabling-technology-with-ecoti/
- Rugged Tablets for Law Enforcement & First Responders: Built for the Toughest Missions, accessed March 6, 2026, https://dtresearch.com/blog/2025/12/22/rugged-tablets-for-law-enforcement-first-responders-built-for-the-toughest-missions/
- GoTAK EUD V2 – Rugged Android ATAK Device – Guerrilla Dynamics, accessed March 6, 2026, https://getgotak.com/products/gotak-eud-v2
- GoTAK Pro Tab – Rugged ATAK Tablet – Guerrilla Dynamics, accessed March 6, 2026, https://getgotak.com/products/gotak-pro-tab
- Situational Awareness | ATAK Mission Technology | Samsung Business, accessed March 6, 2026, https://www.samsung.com/us/business/solutions/industries/government/situational-awareness/
- Ruggedized Tablets Summary – Homeland Security, accessed March 6, 2026, https://www.dhs.gov/sites/default/files/publications/Rugg-Tablets-SUM_0514-508.pdf
- Tactical Phone Mounts & Radio Mounts – Juggernaut Case, accessed March 6, 2026, https://juggernautcase.com/categories/shop-products/shop-by-category/mount.html
- goTenna Pro X2, accessed March 6, 2026, https://gotennapro.com/products/gotenna-pro-x2
- Getting Started with the goTenna Pro X2, accessed March 6, 2026, https://support.gotennapro.com/s/article/Getting-Started-with-the-goTenna-Pro-X2
- www.avinc.com // © 2025 AeroVironment, its product na, accessed March 6, 2026, https://www.avinc.com/images/uploads/product_docs/2025_ProductCatalog.pdf
- The digital repression of social movements, protest, and activism: A synthetic review – PMC, accessed March 6, 2026, https://pmc.ncbi.nlm.nih.gov/articles/PMC10953837/
- Using OSINT in Times of Social Unrest – Carahsoft, accessed March 6, 2026, https://static.carahsoft.com/concrete/files/9617/3384/0566/Cobwebs_-_Using_OSINT_in_Times_of_Social_Unrest.pdf
- Application of OSINT/SOCMINT techniques for the detection and analysis of terrorist profiles, accessed March 6, 2026, https://www.youtube.com/watch?v=Hq6shH3grRY
- The Escalating Threats of Doxxing and Swatting: An Analysis of Recent Developments and Legal Responses – National Association of Attorneys General, accessed March 6, 2026, https://www.naag.org/attorney-general-journal/the-escalating-threats-of-doxxing-and-swatting-an-analysis-of-recent-developments-and-legal-responses/
- researching public perceptions and swat – Scholars Crossing, accessed March 6, 2026, https://digitalcommons.liberty.edu/cgi/viewcontent.cgi?article=7830&context=doctoral
- Israel – Hamas 2024 Symposium – Israeli Hostage Rescue Mission and Perfidy – Lieber Institute, accessed March 6, 2026, https://lieber.westpoint.edu/israeli-hostage-rescue-mission-perfidy/
- Critical Incident Review: Active Shooter at Robb Elementary School – Agency Portal, accessed March 6, 2026, https://portal.cops.usdoj.gov/resourcecenter/content.ashx/cops-r1141-pub.pdf
- OSINT Case Studies & Investigations, accessed March 6, 2026, https://www.osint.industries/case-studies
- Law Enforcement – ShadowDragon, accessed March 6, 2026, https://shadowdragon.io/use-cases/law-enforcement/
- Harnessing OSINT in Criminal Investigations: A Case Study on the Fugitive Emmanuel Edokpolor – ESPY, accessed March 6, 2026, https://espysys.com/blog/harnessing-osint-in-criminal-investigations-a-case-study-on-the-fugitive-emmanuel-edokpolor/
- Social Media Surveillance by the U.S. Government | Brennan Center for Justice, accessed March 6, 2026, https://www.brennancenter.org/our-work/research-reports/social-media-surveillance-us-government
- Social Media Surveillance of the Black Lives Matter Movement and the Right to Privacy, accessed March 6, 2026, https://www.culawreview.org/journal/social-media-surveillance-of-the-black-lives-matter-movement-and-the-right-to-privacy
- Principles for Social Media Use by Law Enforcement | Brennan Center for Justice, accessed March 6, 2026, https://www.brennancenter.org/our-work/research-reports/principles-social-media-use-law-enforcement
- Brennan Center Files Freedom of Information Act Requests for Information on DHS’s Use of Social Media Monitoring Tools, accessed March 6, 2026, https://www.brennancenter.org/our-work/research-reports/brennan-center-files-freedom-information-act-requests-information-dhss
- Department Policies – State of Michigan, accessed March 6, 2026, https://www.michigan.gov/msp/about-msp/dept-policies
- Standard Operating Procedure (SOP) for Forensic Investigations – TaxTMI, accessed March 6, 2026, https://www.taxtmi.com/article/detailed?id=15459
- SOCIAL MEDIA & OPEN SOURCE INVESTIGATIONS, accessed March 6, 2026, https://www.cjtc.wa.gov/sites/default/files/2024-08/Mukilteo%20WA%20SMOSINT%20Sept%202024.pdf
- Social Media | Berrien County, MI, accessed March 6, 2026, https://www.berriencounty.org/79/Social-Media
- Privacy Policy | Berrien County, MI, accessed March 6, 2026, https://www.berriencounty.org/privacypolicy
- Social Media Community Guidelines – State of Michigan, accessed March 6, 2026, https://www.michigan.gov/som/social-media-pages/social-media-community-guidelines
- DOJ Drug Enforcement Agency signs $29M contract for ShadowDragon Horizon/Socialnet solution | OrangeSlices AI, accessed March 6, 2026, https://orangeslices.ai/doj-drug-enforcement-agency-inks-29m-contract-for-shadowdragon-horizon-socialnet-solution/
- Fivecast: Home, accessed March 6, 2026, https://www.fivecast.com/
- Flashpoint Intelligence Platform – AWS Marketplace, accessed March 6, 2026, https://aws.amazon.com/marketplace/pp/prodview-x2ne64fbs7pww
- Flashpoint Pricing, accessed March 6, 2026, https://go.flashpoint.io/pricing
- Flashpoint Ignite Reviews & Ratings 2026 | Gartner Peer Insights, accessed March 6, 2026, https://www.gartner.com/reviews/product/flashpoint-ignite
- Axon Fusus – AWS Marketplace, accessed March 6, 2026, https://aws.amazon.com/marketplace/pp/prodview-ba2wu4h5tdgu6
- Shop – Anoka County Real Time Crime Center, accessed March 6, 2026, https://connectanokacounty.org/shop/
- Building a Real Time Crime Center the Right Way: Insights from Industry Experts, accessed March 6, 2026, https://www.flocksafety.com/blog/building-a-real-time-crime-center-the-right-way-insights-from-industry-experts
- Fremont Police Department – ORT Prevention Grant Program – CA.gov, accessed March 6, 2026, https://www.bscc.ca.gov/wp-content/uploads/2025/02/Fremont-Police-Department.pdf