The evolution of modern warfare has precipitated a fundamental paradigm shift in how the United States military conceptualizes, plans, and executes combat operations. For decades, the United States military relied upon a linear, sequential process known formally as the kill chain, a systematic methodology designed to find, fix, track, target, engage, and assess enemy forces.1 While this linear construct secured battlefield dominance in uncontested environments and asymmetric conflicts against non-peer adversaries, the resurgence of great power competition has rendered the traditional kill chain dangerously fragile.1 Pacing threats, most notably the People’s Republic of China, have meticulously analyzed the American way of war and developed sophisticated countermeasures engineered to sever these linear chains at their most vulnerable links.1
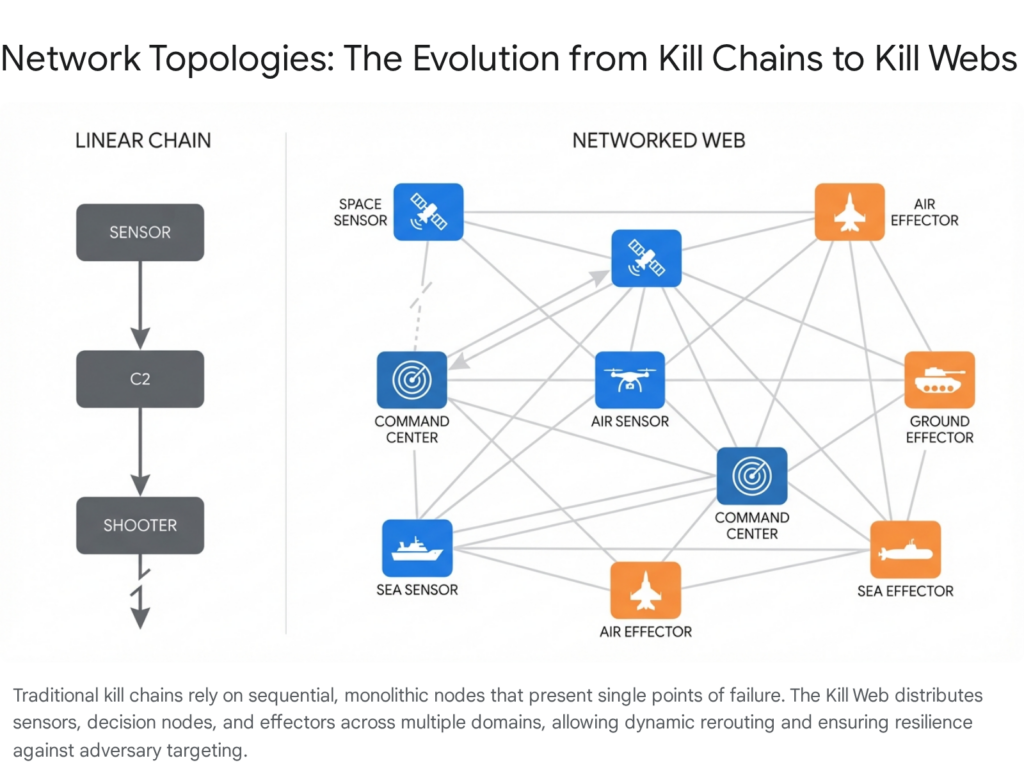
In response to these emerging vulnerabilities, the Department of Defense has transitioned toward a vastly more complex, resilient, and adaptive operational construct known as the kill web.5 Where a kill chain represents a static, two-dimensional sequence of events intrinsically tied to monolithic platforms, a kill web is a dynamic, six-dimensional network that seamlessly integrates the air, land, maritime, space, cyberspace, and electromagnetic spectrum domains.5 By networking diverse sensors, command and control nodes, and effectors across all branches of the armed forces and allied nations, the kill web enables any sensor to provide targeting data to any appropriate shooter, guided by advanced artificial intelligence and machine learning algorithms.5
This comprehensive research report provides an exhaustive analysis of the strategic rationale underpinning the kill web doctrine. It meticulously examines the technical architecture that comprises the web, its manifestation across the military services through the Combined Joint All-Domain Command and Control initiative, the algorithmic engines driving its execution, the logistical frameworks required to sustain it, and the profound implications it holds for operational vulnerabilities and military command philosophy.
The Strategic Imperative: Countering System Destruction Warfare
The impetus for the kill web doctrine is inextricably linked to the strategic posture and capability advancements of peer adversaries. Following the overwhelming success of United States forces in operations such as Desert Storm, adversaries recognized the futility of engaging the United States in symmetric, platform-on-platform attrition warfare.4 Historically, the United States military relied on an operational paradigm that shifted in the early 1980s from Active Defense to AirLand Battle, a doctrine that provided enhanced maneuverability, increased tempo, and embraced offensive combined arms.10 However, the contemporary strategic environment necessitates a shift of equal magnitude to counter localized adversary advantages. The People’s Republic of China has developed a sophisticated Anti-Access/Area Denial strategy, specifically designed to keep United States and allied forces outside of the first and second island chains in the Indo-Pacific theater by creating an interconnected minefield of sensors, shooters, and command elements.3
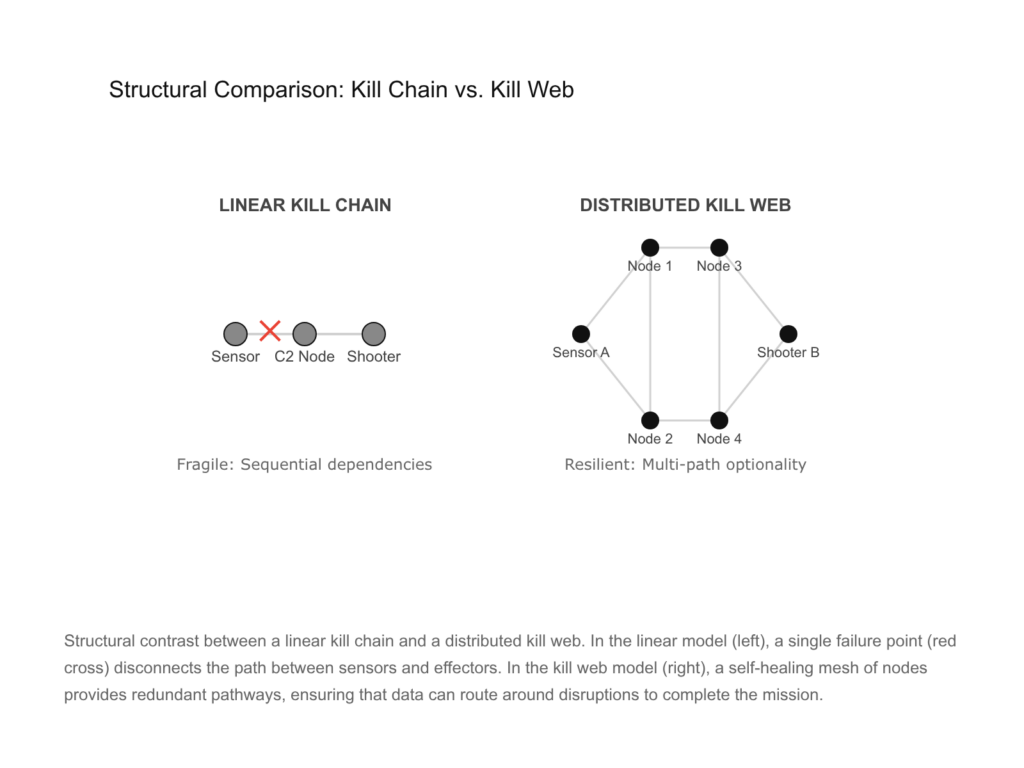
The Fragility of the Linear Kill Chain
The traditional United States kill chain is characterized by highly capable but limited monolithic platforms, such as an E-3 Airborne Warning and Control System aircraft communicating directly with a strike-fighter.12 This architecture inherently creates single points of failure. The military doctrine of the People’s Republic of China, often termed System Destruction Warfare, specifically targets these critical nodes rather than attempting to engage in platform-versus-platform attrition.1 According to translated military doctrine, the People’s Liberation Army aims to collapse the overarching operational architecture by targeting high-value intelligence, surveillance, and reconnaissance assets, communication satellites, and command centers through both kinetic strikes and non-kinetic electronic warfare, termed “information soft kills”.1
If an adversary can successfully jam a satellite link, destroy a forward radar station, or neutralize a localized command center, the linear kill chain collapses entirely.1 Furthermore, the sheer scale and scope of a potential Pacific conflict introduce unparalleled complexities. Projections indicate that up to eighty percent of targets may be mobile or quickly relocatable in the early phases of an invasion scenario.1 The United States military must be prepared to close kill chains against these dynamic, fleeting targets at a scale unseen since the Cold War, operating across thousands of miles of ocean.1 A traditional linear process simply cannot accommodate the volume and speed of targeting required for such an endeavor.
The Transition to Decision-Centric Warfare
The kill web serves as the technological and doctrinal answer to System Destruction Warfare and Anti-Access/Area Denial strategies. By distributing capabilities across a vast network of disaggregated systems, the kill web removes single points of failure, rendering the architecture exponentially more survivable.1 This structural shift facilitates a fundamental transition from attrition-centric warfare, which focuses on physically destroying the enemy’s mass, to decision-centric warfare.15
Decision-centric warfare seeks to weaponize complexity. By possessing a networked web of assets that can be rapidly composed and recomposed into unpredictable force packages, the United States military can impose multiple, overlapping dilemmas upon an adversary simultaneously.13 This capability disrupts the enemy’s Observe, Orient, Decide, Act loop, effectively collapsing their decision-making cycle and paralyzing their operational tempo.5
| Doctrinal Characteristic | Traditional Kill Chain | Advanced Kill Web |
| Architectural Structure | Linear, sequential, and static | Dynamic, omnidirectional, and mesh-based |
| Asset Dependency | Highly dependent on monolithic, multi-role platforms | Disaggregated, utilizing single-function and multi-function nodes |
| Vulnerability Profile | High risk of single points of failure | Highly resilient; destruction of a node prompts automated rerouting |
| Primary Objective | Platform-on-platform attrition | Decision superiority and cognitive overload of the adversary |
| Domain Integration | Typically single or dual-domain (e.g., Air-to-Ground) | Omni-domain (Air, Land, Sea, Space, Cyber, Electromagnetic) |
| Data Processing | Human-intensive, localized analysis | Machine-speed analysis, AI-driven sensor fusion, automated deconfliction |
Conceptual Foundations: Mosaic Warfare and Convergence
The foundational operational principle of the kill web is convergence. Military doctrine defines convergence as the process of collecting massive volumes of data from highly distributed sensors, rapidly analyzing it to discern critical tactical information, transmitting that intelligence securely to relevant operators, and optimally responding with the right munition, from the right platform, at the precise moment of maximum impact.5 Achieving convergence requires an increasingly integrated and interoperable joint force that maintains a continuous, shared understanding of the common operating environment, enabling commanders to auction off targets to platforms best postured within the web.5
The Defense Advanced Research Projects Agency and Mosaic Warfare
The technological and conceptual manifestation of convergence is heavily informed by the Defense Advanced Research Projects Agency’s Mosaic Warfare strategy.12 Traditional military procurement focuses on highly complex, multi-role platforms that require decades to develop, are exorbitantly expensive to build, and represent catastrophic losses if destroyed in combat. Mosaic warfare, conversely, treats individual warfighting platforms—whether they are manned aircraft, unmanned autonomous swarms, or non-kinetic electronic warfare pods—as individual tiles in a broader, infinitely configurable mosaic.4
Combatant commanders can rapidly select these individual force elements and tile them together to create tailored force packages designed for a specific, immediate mission.17 Because the systems are disaggregated and highly interoperable, they can mass firepower and effects unpredictably without necessarily massing physical forces in a vulnerable geographic location.13 This approach grants the joint force an asymmetric advantage, making it exceedingly difficult for adversaries to ascertain intent, identify critical vulnerabilities, or predict avenues of attack.13 Analysts note that the human immune system, which has evolved to exhibit mosaic-like properties of resilience, adaptability, and distributed response, serves as a biological analog for this warfighting construct.19
Enabling Technologies: ACK and STITCHES
To operationalize Mosaic Warfare and enable force composability directly at the warfighter level, the Defense Advanced Research Projects Agency has developed critical software architectures, most notably the Adapting Cross-Domain Kill-Webs program and the System-of-systems Technology Integration Tool Chain for Heterogeneous Electronic Systems.12
The Adapting Cross-Domain Kill-Webs program functions as a novel, highly advanced decision-aid software designed explicitly for mission commanders. It analyzes thousands of complex variables and available assets across organizational and service boundaries to recommend optimal sensor-to-shooter combinations.12 Rather than relying on rigid, pre-planned responses, the software generates actionable plays for the commander. During demonstrations, the software successfully analyzed immense volumes of data to form cross-domain webs, ultimately sending commands to applications like the Command and Control Incident Management Emergency Response Application and ground-based integrated fire control systems to scramble interceptors.12
Crucially, the System-of-systems Technology Integration Tool Chain for Heterogeneous Electronic Systems serves as the vital middleware making these rapid connections possible. It is a software-only, fully government-owned integration toolchain designed to rapidly connect heterogeneous systems across any domain.12 It circumvents traditional interoperability bottlenecks by auto-generating extremely low-latency, high-throughput middleware between systems without forcing a common interface standard or requiring massive hardware upgrades.12 This breakthrough allows legacy radar systems deployed over forty years ago to seamlessly share targeting data with modern electronic equipment, creating adaptive kill webs in a matter of days rather than the years typically required to accredit and host software on secure military networks.12
Architectural Composition: The Triad of the Kill Web
The kill web is not a single piece of hardware but a system of systems sustained by a triad of interconnected functional grids: the omni-domain sensor grid, the command and control nexus, and the effector grid.
The Omni-Domain Sensor Grid
A kill web is entirely dependent upon persistent, resilient, and multi-modal battlespace awareness. In a modern conflict prioritizing precision strikes, the quality, quantity, and survivability of sensors are often more decisive than the explosive yield of the weapons they guide.21 The sensor grid ingests data from a dizzying array of sources: space-based early warning systems, high-altitude unmanned aerial vehicles, advanced fifth-generation aircraft like the F-35 acting as forward data-collection nodes, and terrestrial radars.22
Modern sensor infrastructure, such as the AN/TPS-80 Ground/Air Task Oriented Radar, provides unambiguous views of highly cluttered, contested environments, passing that data directly into the web.23 Furthermore, to secure the ultimate high ground, the United States Space Force, through the Space Development Agency, is rapidly deploying the Proliferated Warfighter Space Architecture.24 This architecture establishes a dedicated Custody Layer utilizing visible, infrared, synthetic aperture radar, and multispectral payloads to maintain continuous, all-weather tracking of time-sensitive and mobile targets.26 This multi-modal approach ensures that if an adversary employs electronic warfare to jam a specific radar frequency, optical or infrared sensors can seamlessly maintain target custody, preserving the integrity of the kill web.26 Additionally, geographic high-latitude sensor placements, such as those in Greenland, are recognized as critical nodes for early detection and sensor fusion, compressing decision timelines for commanders across multi-domain networks and preventing reactive delays against threats emerging over the pole.28
The Command and Control Nexus
The deluge of data generated by the omni-domain sensor grid vastly exceeds human cognitive capacity. The command and control nexus acts as the central nervous system of the kill web, filtering noise and transforming raw data into actionable, targeting-grade intelligence.5 This nexus relies on an integrated data fabric, secure transport layers, and advanced edge computing to ensure information parsimony—delivering only the precise information required, to the right person or machine, at the exact moment it is needed.5 The Space Development Agency’s Transport Layer forms the backbone of this nexus in space, providing low-latency, high-bandwidth data transport that links the tracking data from the Custody Layer directly to the warfighter on the ground, enabling beyond line-of-sight tactical operations.26
The Effector Grid
The effector grid encompasses the platforms and munitions that ultimately act upon the decisions generated within the command and control nexus. In a kill web construct, effectors are not strictly kinetic, such as hypersonic missiles, long-range artillery, or precision-guided bombs. The web seamlessly integrates non-kinetic effectors, including specialized electronic warfare assets designed to execute soft kills by blinding adversary sensors, jamming communications networks, or launching offensive cyber operations.1
Furthermore, the integration of Collaborative Combat Aircraft—highly autonomous uncrewed drones flying in tandem with manned fighters—vastly expands the magazine depth and operational reach of the effector grid.31 The Collaborative Combat Aircraft program validates a modular, open-systems approach designed to operate within established command structures while extending the effectiveness of crewed aircraft, allowing manned platforms to remain outside the densest threat rings while directing uncrewed systems to sense, shield, and strike targets in highly contested environments.31
Joint and Allied Integration: The CJADC2 Ecosystem
To actualize the theoretical concepts of the kill web, the Department of Defense is aggressively pursuing the Combined Joint All-Domain Command and Control initiative. This initiative is not a monolithic procurement program, but rather an overarching strategic vision and set of rigorous data standards ensuring that the independent tactical networks developed by the respective military branches can interoperate seamlessly.36 The explicit inclusion of the Combined prefix underscores the mandatory integration of international mission partners and allied nations, particularly the Five Eyes alliance comprised of the United States, United Kingdom, Canada, Australia, and New Zealand.39
| Service Branch | Primary Kill Web Initiative | Core Operational Focus and Architecture |
| U.S. Army | Project Convergence | Integrating sensor-to-shooter webs for Large-Scale Combat Operations using AI/ML targeting algorithms. |
| U.S. Navy | Project Overmatch | Delivering the Naval Operational Architecture to enable Distributed Maritime Operations and massed sea-based fires. |
| U.S. Air Force | Advanced Battle Management System | Developing cloud environments and advanced data links to optimize kill chains for speed and survivability. |
| U.S. Marine Corps | Project Dynamis | Modernizing command and control to enable Expeditionary Advanced Base Operations and Stand-in Forces. |
| U.S. Space Force | Proliferated Warfighter Space Architecture | Deploying a massive LEO satellite constellation for low-latency transport and continuous target custody. |
Army Capabilities: Project Convergence
The United States Army’s specific contribution to the kill web is driven by Project Convergence, a persistent campaign of learning and field experimentation designed to dramatically accelerate target acquisition and engagement frameworks in Large-Scale Combat Operations.42 Project Convergence seeks to evolve the Army’s legacy linear processes into true sensor-to-shooter webs by combining advanced network capabilities with cutting-edge artificial intelligence.43
During landmark Project Convergence demonstrations at installations like Yuma Proving Ground, the Army successfully integrated sensors from the space domain with ground-based effectors, routing targeting data across thousands of miles. By linking space-based sensors directly to ground artillery units and Marine Corps F-35 aircraft, the Army effectively showcased how ground forces can strike deep into adversarial territory using off-board, multi-domain sensor data, replacing post-delivery interdependence with pre-requirement integration.7
Naval Capabilities: Project Overmatch and the Naval Operational Architecture
The Department of the Navy’s implementation of the combined joint all-domain concept is Project Overmatch. This high-priority initiative aims to deliver the robust Naval Operational Architecture by the middle of this decade, explicitly enabling Distributed Maritime Operations, Littoral Operations in a Contested Environment, and Expeditionary Advanced Base Operations.47 The maritime domain requires naval forces to operate over vast oceanic distances while projecting synchronized lethal and non-lethal effects, necessitating a resilient web of persistent sensors, command nodes, and weapons.47
Project Overmatch is built upon four foundational technical pillars: Networks, Infrastructure, Data Architecture, and Tools and Analytics.47 It prioritizes the deployment of Software Defined Networks to provide transport-agnostic connectivity specifically engineered to survive in severely denied environments.47 It utilizes DevSecOps principles, rapid delivery of containerized applications to the fleet, and a robust data fabric to abstract data from legacy applications, making it available as a secure service across diverse platforms.47 To bypass the sluggish pace of traditional defense acquisition, Overmatch heavily leverages platforms like Open DAGIR—Data and Applications Government-owned Interoperable Repositories—to rapidly procure, validate, and integrate commercial-off-the-shelf artificial intelligence and data analytics tools directly into fleet operations.48
Marine Corps Integration: Project Dynamis and Distributed Operations
The United States Marine Corps operates as a critical connective tissue within the naval and joint kill web through initiatives like Project Dynamis, which accelerates the modernization of command, control, communications, and computers portfolio.49 Modern Marine Corps operations rely heavily on the Marine Air Control Group, specifically units like MACG-38, which represents a fundamental shift in aviation capabilities.50 Rather than viewing aviation through individual platform types, the control group functions as the dial for force configuration, encompassing integrated air defense, tactical air control, and the communications backbone necessary to assemble tailored packages that close kill webs.50 This infrastructure directly supports Expeditionary Advanced Base Operations, where highly mobile Stand-in Forces operate within an adversary’s weapon engagement zone to sense targets and cue long-range naval and joint fires.6
The Combined Mandate: Coalition Integration and the Mission Partner Environment
The z-axis of the combined joint all-domain strategy is comprehensive allied integration.40 History demonstrates that the United States rarely engages in major conflicts alone; however, coalition operations have historically been severely hindered by disparate security protocols, incompatible waveforms, and isolated national networks.53 The modern kill web directly incorporates the Mission Partner Environment and the Secret and Below Releasable Environment framework.55 By utilizing advanced data-centric security architectures—protecting the individual data elements rather than just the perimeter network—these environments enable rapid, secure information sharing, effectively integrating foreign partners into the United States kill web to drastically cut the decision-making timeline across multinational commands.55
Recent massive wargames, such as the Indo-Pacific Valiant Shield 2024 exercise, have rigorously validated these integration concepts.58 Valiant Shield served as a premier proving ground for the combined architecture, demonstrating how joint and coalition forces can share targeting data at breakneck speeds, resulting in a highly successful sinking exercise of a decommissioned vessel utilizing precise, multi-axis, multi-domain effects.58 The primary lesson derived from these exercises is that foundational interoperability has been largely achieved; the operational focus across the Department of Defense has now shifted toward actively harnessing that resulting connectivity and visibility to apply it directly to warfighting capabilities and net-enabled weapons.61
The Algorithmic Engine: Artificial Intelligence and Autonomy
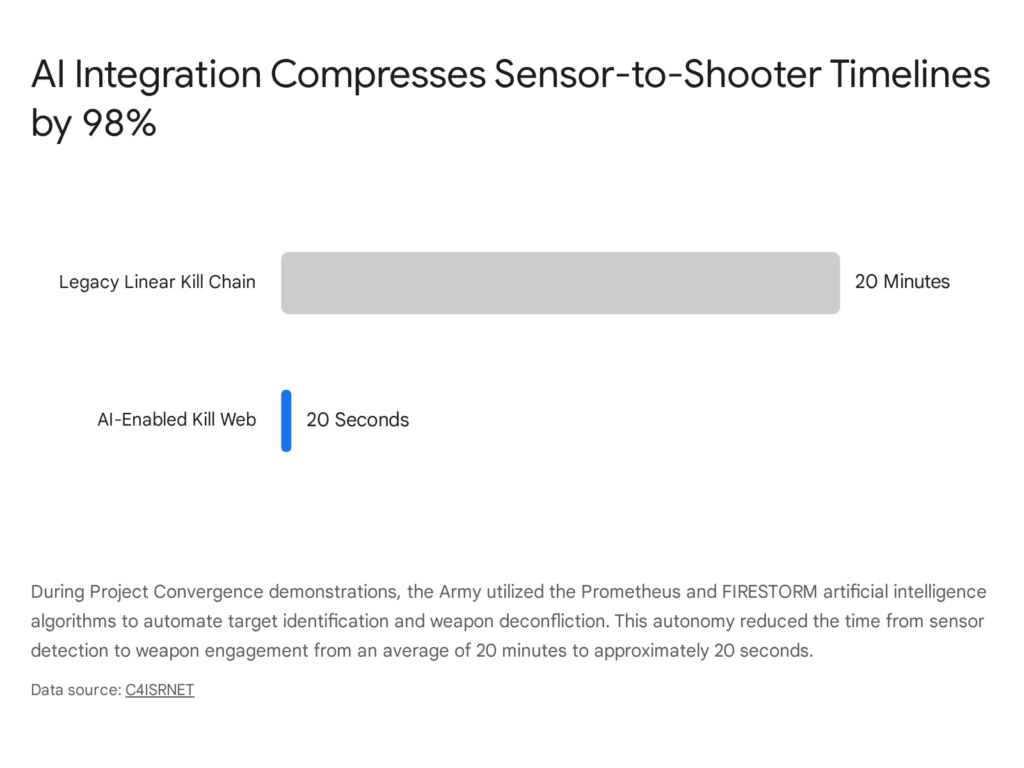
The velocity required to execute offensive and defensive operations within a modern kill web vastly outpaces human cognitive and manual processing power. Consequently, artificial intelligence and machine learning serve as the indispensable algorithmic engines of the web, drastically compressing the sensor-to-shooter timeline and enabling true decision superiority.16
Prometheus and FIRESTORM Execution
The Army’s Project Convergence effectively demonstrated the transformative power of specialized artificial intelligence algorithms, specifically the synergistic use of Prometheus and FIRESTORM.7 Prometheus functions as a highly advanced automated target identification system. It ingests massive quantities of fused sensor data—such as high-resolution satellite imagery downloaded to tactical ground stations—and utilizes machine learning to autonomously identify, classify, and geolocate enemy threats across all domains in a matter of seconds.7
Once targets are securely identified, the targeting data is instantly fed into FIRESTORM, which serves as the tactical computer brain within the assault network.7 FIRESTORM processes a multitude of variables simultaneously, evaluating complex terrain characteristics, the proximity of available friendly weapon systems, and total threat density.7 It then autonomously recommends the optimal shooter to engage the target. Crucially, FIRESTORM automates target deconfliction, ensuring that multiple friendly units do not redundantly expend munitions on the same threat—a process that historically required time-consuming radio coordination and manual deconfliction matrices.7
Enterprise Intelligence: Project Maven and Commercial Integration
At the strategic and operational levels, the Department of Defense relies heavily on Maven, originally launched as Project Maven in 2017 to accelerate the adoption of machine learning for military intelligence workflows.62 Maven integrates massive data feeds from drones, satellites, and other sensors to automatically flag potential targets, present findings to human analysts, and relay decisions to operational systems.62
This capability is being rapidly scaled through deep commercial partnerships. The Maven Smart System, powered by the commercially developed Palantir Platform, serves as an enterprise mission command interface, integrating large-scale operational data to accelerate human decision-making across joint intelligence and fires missions.63 The Department of Defense recently expanded the Maven Smart System contract significantly to prepare for an influx of demand from military users.64 Concurrently, software platforms like Anduril’s Lattice provide edge-based mission autonomy, integrating directly with robotic systems to orchestrate air defense and reconnaissance.65 The marriage of these advanced commercial systems represents the technological integration necessary to process data at the unprecedented speed of modern combat.48
The Command Philosophy Paradox: Human in the Loop versus On the Loop
The integration of highly autonomous systems within the kill web forces a critical reevaluation of established military command philosophy.16 Specifically, the capabilities of the web create severe friction with the foundational doctrine of Mission Command.
Mission Command is the prevailing command and control philosophy of the joint force, predicated on the absolute necessity of decentralized execution.66 Commanders provide clear, overarching intent but deliberately delegate authority to subordinates to exercise initiative and make tactical decisions in complex, chaotic environments where communications may be denied.66
However, the kill web’s reliance on algorithmic warfare introduces a technological paradox.16 The sheer volume of data processed by artificial intelligence provides higher-echelon commanders with an unprecedented, near-perfect common operating picture in real-time.16 This immense situational awareness, coupled with the ability of machines to orchestrate complex strikes globally, introduces a powerful temptation toward centralized control.16 If a four-star commander sitting in a maritime operations center can view the exact tactical layout via a Maven Smart System, the traditional necessity for decentralized execution diminishes, potentially leading to micromanagement and an erosion of subordinate trust.16
Furthermore, the speed of modern effectors, such as hypersonic weapons and autonomous drone swarms, dictates that human operators must increasingly transition from being in the loop—where artificial intelligence proposes an action and a human must explicitly authorize every step—to being on the loop, where the system operates autonomously within pre-defined parameters, and the human only intervenes to override or correct.7 Current Department of Defense policy continues to emphasize the necessity of appropriate human judgment over the use of force, but as the battlespace timeline compresses to milliseconds, maintaining a human in every individual tactical loop becomes physically impossible, necessitating profound ethical and doctrinal shifts regarding how lethal force is authorized within the web.7
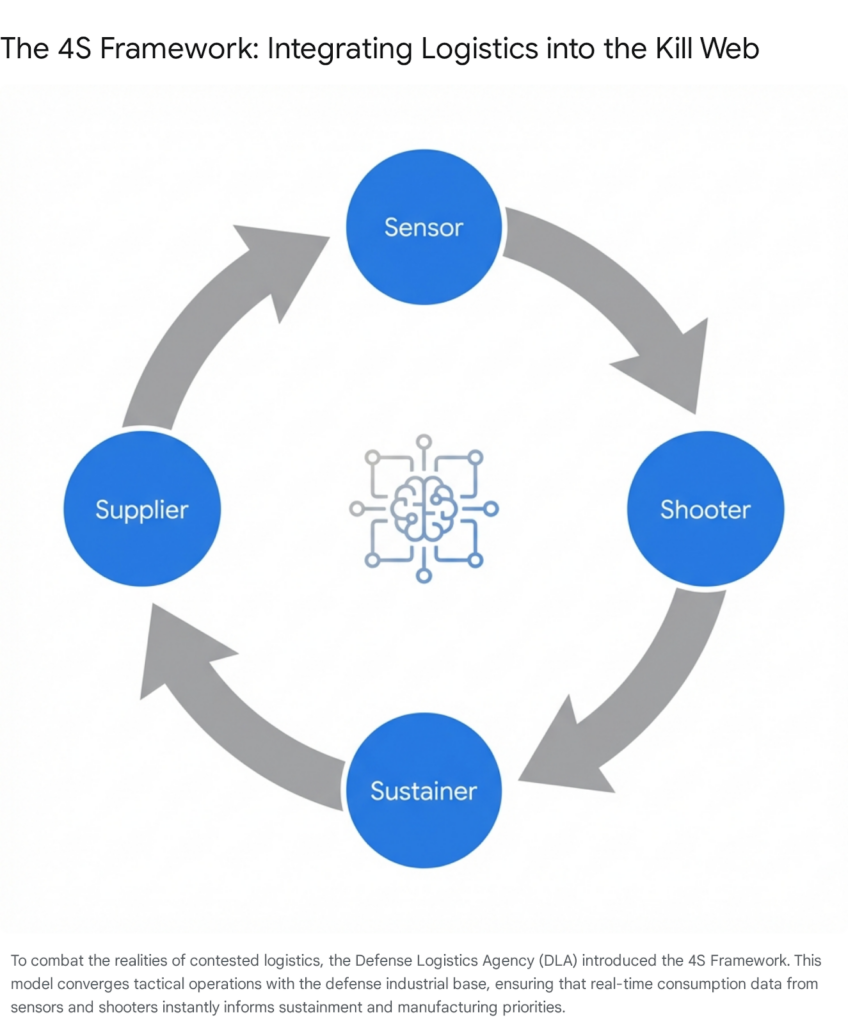
Sustaining the Web: Contested Logistics and the 4S Framework
A kill web, regardless of its technological sophistication, is only as lethal as its logistics tail. While immense focus is placed on advanced sensors and precision shooters, the United States military explicitly recognizes that a major conflict in the Pacific theater will be characterized by severely contested logistics.75 Adversaries possess the long-range precision fires required to aggressively target supply lines, fuel depots, port facilities, and transportation nodes to starve the dispersed web of its necessary resources.75
Operations such as the Marine Corps’ Expeditionary Advanced Base Operations rely entirely on inserting small, lethal forces deep within an adversary’s weapon engagement zone to close kill webs.6 However, these highly distributed forces are astonishingly logistics-intensive.77 Recent exercises, such as Steel Knight 25, tested various force projection scenarios and revealed significant capability gaps in sustaining these distributed nodes under contested conditions, highlighting critical shortages in heavy-lift assets like the CH-53K King Stallion, MV-22 Ospreys, and C-130 aircraft.61 The traditional assumption of operating within permissive logistics environments once forces are ashore has completely collapsed.75
To address this existential vulnerability, the Defense Logistics Agency is revolutionizing defense logistics by converging commercial supply chains with combat kill chains through the implementation of the 4S Framework: Sensor to Shooter to Sustainer to Supplier.79
In this highly integrated model, the logistical enterprise is hardwired directly into the digital infrastructure of the kill web.79 When a sensor identifies a threat, or a shooter expends a precision munition, that consumption data flows seamlessly and instantaneously back to the sustainer, and ultimately, to the defense industrial base acting as the supplier.79 By utilizing artificial intelligence, machine learning algorithms, digital twins of the supply chain, and automated agentic data-bots, the 4S framework provides predictive logistics, ensuring that dispersed forces receive fuel, munitions, and repair parts proactively rather than reactively.79 In a contested environment where primary supply routes are threatened or destroyed, these automated systems can instantaneously reroute supplies or reposition logistics nodes to ensure the uninterrupted survivability of the force.78
Vulnerabilities, Friction Points, and Cyber Threats
Despite its theoretical superiority and immense lethality, the kill web introduces new, profound operational vulnerabilities. By its very definition, a networked, decentralized system relies absolutely on the integrity, bandwidth, and security of its underlying data transport layers. If the connective tissue of the web is severed, the distributed forces devolve into isolated, uncoordinated units vulnerable to defeat in detail.
Interoperability and Legacy Infrastructure Integration
The most immediate and persistent technical hurdle facing the kill web is foundational interoperability.54 The United States military currently operates thousands of legacy platforms—including older aircraft, surface ships, and ground vehicles—designed and procured decades before the advent of the combined joint all-domain concept.36 Ensuring that a tactical data link from the 1970s can securely receive artificial intelligence-processed targeting data from a 2026-era cloud environment requires extensive middleware, translation nodes, and application programming interface integration.47
As noted in extensive assessments of allied integration, attempting to mandate a single, universal data standard across all military services and coalition partners is practically impossible due to conflicting acquisition cycles and proprietary technologies.47 Therefore, the technological focus must remain on real-time data translation and highly portable data fabrics.47 Defense contractors are actively developing systems like the Unity Adapter, which functions as an open-standards interface to unlock proprietary data sets and connect disparate systems across the battlespace, alongside emerging protocols for space strategic multicast connectivity.61
The Electromagnetic and Cyber Contests
The kill web is highly susceptible to electromagnetic interference and offensive cyber operations. In a high-end conflict against a peer adversary, forces will be subjected to massive, power-based jamming designed to drown out radio frequency communications and sever the fragile links between remote sensors and their command nodes.82 The strategic importance of jamming is immense; the United States Space Force has actively deployed Remote Modular Terminals specifically designed to block adversarial aerospace satellites from transmitting targeting data, though these jammers themselves become high-value targets for anti-radiation munitions.27
Furthermore, the proliferation of space-based assets makes global satellite constellations prime targets for cyber warfare. While the Space Development Agency relies on low earth orbit proliferation for resilience, satellite modems and ground stations remain uniquely vulnerable to sophisticated cyberattacks.82 A stark, historical example of this threat occurred during the initial phase of the Russia-Ukraine conflict, when attackers deployed a wiper malware known as AcidRain.82 This highly coordinated cyberattack successfully disabled thousands of Viasat satellite modems, cutting internet access for military users and permanently blinding communications infrastructure across the region.82 Similar distributed denial of service attacks against the mesh networks underpinning the kill web could paralyze the system, forcing a dangerous reversion to localized, degraded operations.85
To aggressively mitigate these existential risks, the Department of Defense is implementing Zero-Trust security architectures, secure routing protocols, multi-factor authentication for ground stations, and post-quantum encryption standards within its transmission systems.84 Furthermore, relying on Blue A2/AD—utilizing the same geographic constraints against the adversary by establishing resilient, hardened sensor nodes in austere, highly defensible locations like Greenland or the First Island Chain—provides vital localized redundancy when global space links are jammed or compromised.28
The transition from the linear kill chain to the multi-domain kill web represents the most significant, structural evolution in United States military operational design since the inception of the AirLand Battle doctrine. Driven by the absolute strategic imperative to counter System Destruction Warfare and Anti-Access/Area Denial strategies, the kill web weaponizes information, complexity, and sheer speed. Through the robust integration of omni-domain sensors, automated algorithmic command engines like Prometheus and FIRESTORM, and highly distributed kinetic and non-kinetic effectors, the kill web fully realizes the transformative principles of Mosaic Warfare. It enables an operational posture where the joint force—alongside its critical international coalition partners—can rapidly compose unpredictable, highly lethal force packages capable of collapsing an adversary’s decision cycle. However, realizing this vision demands a flawless, highly secure data transport layer capable of surviving in the most hostile electronic and cyber environments ever conceived, alongside a revolution in contested logistics and a profound reckoning within military command philosophy regarding the shifting boundary between human oversight and machine autonomy. Ultimately, prevailing in future conflicts will not belong solely to the military possessing the most exquisite individual platforms, but to the force that can seamlessly orchestrate its diverse, distributed assets across the most resilient, intelligent, and lethal web.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Sources Used
- Winning the Kill Chain Competition – Mitchell Institute for Aerospace Studies, accessed February 26, 2026, https://www.mitchellaerospacepower.org/app/uploads/2023/05/Scale_Scope_Speed_Survivability_-KillChain_-Policy_Paper_40-New.pdf
- How does the ‘kill chain’ actually work? : r/CredibleDefense – Reddit, accessed February 26, 2026, https://www.reddit.com/r/CredibleDefense/comments/1gbbqc1/how_does_the_kill_chain_actually_work/
- Air and Missile Defense and Point Defense in Near-Peer Conflict: A Joint Doctrine and ACE Imperative – Small Wars Journal, accessed February 26, 2026, https://smallwarsjournal.com/2025/12/11/air-missile-defense-near-peer-conflict/
- Mosaic Warfare | Air & Space Forces Magazine, accessed February 26, 2026, https://www.airandspaceforces.com/article/mosaic-warfare/
- Joint All-Domain Kill Webs – Marine Corps Association, accessed February 26, 2026, https://www.mca-marines.org/wp-content/uploads/Pavlak-Oct23.pdf
- CHIPS Articles: Revealing the hidden: The role of sensing in completing the kill web, accessed February 26, 2026, https://www.doncio.navy.mil/Chips/ArticleDetails.aspx?ID=16714
- Inside the Army’s futuristic test of its battlefield artificial intelligence in …, accessed February 26, 2026, https://www.c4isrnet.com/artificial-intelligence/2020/09/25/the-army-just-conducted-a-massive-test-of-its-battlefield-artificial-intelligence-in-the-desert/
- Joint All-Domain Command and Control (JADC2) – Missile Defense Advocacy Alliance, accessed February 26, 2026, https://www.missiledefenseadvocacy.org/defense-systems/joint-all-domain-command-and-control-jadc2/
- Meeting the Anti-Access and Area-Denial Challenge – CSBA, accessed February 26, 2026, https://csbaonline.org/uploads/documents/2003.05.20-Anti-Access-Area-Denial-A2-AD.pdf
- Shortening the “competition kill chain” Through irregular Warfare Campaigning. – Line of Departure, accessed February 26, 2026, https://www.lineofdeparture.army.mil/Journals/Special-Warfare/Spring-2024/Shortening-the-competition-kill-chain/
- The Challenge of Dis-Integrating A2/AD Zone: How Emerging Technologies Are Shifting the Balance Back to the Defense – NDU Press, accessed February 26, 2026, https://ndupress.ndu.edu/Media/News/News-Article-View/Article/2106488/the-challenge-of-dis-integrating-a2ad-zone-how-emerging-technologies-are-shifti/
- Creating Cross-Domain Kill Webs in Real Time – DARPA, accessed February 26, 2026, https://www.darpa.mil/news/2020/cross-domain-kill-webs
- MOSAIC WARFARE – CSBA, accessed February 26, 2026, https://csbaonline.org/uploads/documents/Mosaic_Warfare_Web.pdf
- Taiwan’s Layered Air Defence and the Calculus of Deterrence | Center for International Maritime Security, accessed February 26, 2026, https://cimsec.org/the-shield-of-the-strait-taiwans-layered-air-defence-and-the-calculus-of-deterrence/
- MOSAIC WARFARE – CSBA, accessed February 26, 2026, https://csbaonline.org/uploads/documents/Mosaic_Warfare_2.pdf
- Mission (Command) Complete: Implications of JADC2 > National …, accessed February 26, 2026, https://ndupress.ndu.edu/Media/News/News-Article-View/Article/3841502/mission-command-complete-implications-of-jadc2/
- Aligning Emerging Concepts and Capabilities With Mosaic Warfare, accessed February 26, 2026, https://ciasp.scholasticahq.com/article/127303-aligning-emerging-concepts-and-capabilities-with-mosaic-warfare
- DARPA Tiles Together a Vision of Mosaic Warfare, accessed February 26, 2026, https://www.darpa.mil/news/features/mosaic-warfare
- Distributed Kill Chains: Drawing Insights for Mosaic Warfare from the Immune System and from the Navy | RAND, accessed February 26, 2026, https://www.rand.org/pubs/research_reports/RRA573-1.html
- ACK: Adapting Cross-Domain Kill-Webs – DARPA, accessed February 26, 2026, https://www.darpa.mil/research/programs/adapting-cross-domain-kill-webs
- Sensor to Shooter Chains Turn into Kill Webs – European Security & Defence, accessed February 26, 2026, https://euro-sd.com/2022/10/articles/27530/sensor-to-shooter-chains-turn-into-kill-webs/
- C2-Enabled Long-Range Precision Fires for the Army – Booz Allen, accessed February 26, 2026, https://www.boozallen.com/insights/defense/c2-command-and-control/c2-enabled-long-range-precision-fires-for-the-army.html
- Counter Unmanned Aerial Systems (C-UAS) – Northrop Grumman, accessed February 26, 2026, https://www.northropgrumman.com/what-we-do/mission-solutions/counter-unmanned-aerial-systems-c-uas
- Space Development Agency – Increasing Warfighters’ Lethality, Maneuverability, and Survivability, accessed February 26, 2026, https://www.sda.mil/
- SDA Layered Network of Military Satellites now known as “Proliferated Warfighter Space Architecture” > United States Space Force > News, accessed February 26, 2026, https://www.spaceforce.mil/News/Article/3274487/sda-layered-network-of-military-satellites-now-known-as-proliferated-warfighter/
- Custody – Space Development Agency, accessed February 26, 2026, https://www.sda.mil/custody/
- US ‘risks electronic warfare’ with China after unveiling anti-satellite jammer network, accessed February 26, 2026, https://space4peace.org/us-risks-electronic-warfare-with-china-after-unveiling-anti-satellite-jammer-network/
- Greenland and the High Ground of the Kill Web: Why the Arctic Matters for Fighting at the Speed of Light | Defense.info, accessed February 26, 2026, https://defense.info/defense-decisions/2026/02/greenland-and-the-high-ground-of-the-kill-web-why-the-arctic-matters-for-fighting-at-the-speed-of-light/
- Kill Webs: The Wicked Problem of Future Warfighting | The Duck of Minerva, accessed February 26, 2026, https://www.duckofminerva.com/2016/06/kill-webs-the-wicked-problem-of-future-warfighting.html
- SDA Awards Tactical SATCOM Demo Contract – Air & Space Forces Magazine, accessed February 26, 2026, https://www.airandspaceforces.com/space-development-agency-tactical-satcom-demo-contract/
- Air Force validates open architecture, expands Collaborative Combat Aircraft ecosystem, accessed February 26, 2026, https://www.af.mil/News/Article-Display/Article/4405471/air-force-validates-open-architecture-expands-collaborative-combat-aircraft-eco/
- Collaborative Combat Aircraft program progresses through deliberate weapons integration testing > Air Combat Command > Article Display – ACC, accessed February 26, 2026, https://www.acc.af.mil/News/Article-Display/Article/4414428/collaborative-combat-aircraft-program-progresses-through-deliberate-weapons-int/
- Collaborative Combat Aircraft (CCA), US – Airforce Technology, accessed February 26, 2026, https://www.airforce-technology.com/projects/collaborative-combat-aircraft-cca-usa/
- The Need for Collaborative Combat Aircraft for Disruptive Air Warfare – Mitchell Institute for Aerospace Studies, accessed February 26, 2026, https://www.mitchellaerospacepower.org/app/uploads/2024/02/The-Need-For-CCAs-for-Disruptive-Air-Warfare-FULL-FINAL.pdf
- Air Force begins adding weapons to CCA drone flight tests – DefenseScoop, accessed February 26, 2026, https://defensescoop.com/2026/02/24/air-force-cca-drone-captive-carry-tests/
- JADC2 and the Kill Web – Military Embedded Systems, accessed February 26, 2026, https://militaryembedded.com/radar-ew/sigint/jadc2-and-the-kill-web
- Key to the Pentagon’s concept for modern war is standardization – DefenseScoop, accessed February 26, 2026, https://defensescoop.com/2024/08/12/key-pentagon-cjadc2-concept-modern-war-standardization/
- GAO-25-106454, DEFENSE COMMAND AND CONTROL : Further Progress Hinges on Establishing a Comprehensive Framework, accessed February 26, 2026, https://files.gao.gov/reports/GAO-25-106454/index.html
- Return of CJADC2: DoD officially moves ahead with ‘combined’ JADC2 in a rebrand focusing on partners – Breaking Defense, accessed February 26, 2026, https://breakingdefense.com/2023/05/return-of-cjadc2-dod-officially-moves-ahead-with-combined-jadc2-in-a-rebrand-focusing-on-partners/
- Allies Need to Take Part in Services JADC2 Goals – National Defense Industrial Association, accessed February 26, 2026, https://www.ndia.org/policy/research-blog/2023/6/23/allies-need-to-take-part-in-services-jadc2-goals
- Army Suggests Adding Five Eyes Nation Allies in JADC2 | AFCEA International, accessed February 26, 2026, https://www.afcea.org/signal-media/technet-augusta-22-coverage/army-suggests-adding-five-eyes-nation-allies-jadc2
- Project Convergence: Revolutionizing Targeting in Large-Scale Combat Operations, accessed February 26, 2026, https://www.lineofdeparture.army.mil/Journals/Field-Artillery/Field-Artillery-Archive/Field-Artillery-2025-E-Edition/Project-Convergence/
- Army sets sights on 2024 for next Project Convergence – Defense News, accessed February 26, 2026, https://www.defensenews.com/land/2023/02/07/army-sets-sights-on-2024-for-next-project-convergence/
- Project Convergence: Achieving Overmatch by Solving Joint Problems – NDU Press, accessed February 26, 2026, https://ndupress.ndu.edu/Media/News/News-Article-View/Article/2807194/project-convergence-achieving-overmatch-by-solving-joint-problems/
- Project Convergence – DEVCOM Soldier Center, accessed February 26, 2026, https://sc.devcom.army.mil/spotlight/project-convergence/
- Pushing Data ‘From Space To Mud’: Project Convergence – Breaking Defense, accessed February 26, 2026, https://breakingdefense.com/2020/09/pushing-data-from-space-to-mud-project-convergence/
- Project Overmatch Discussion – NDIA-SD.org, accessed February 26, 2026, https://www.ndia-sd.org/wp-content/uploads/2025/02/13-Feb-2025-QBOB-Overmatch-Brief-Nic-Bergeron.pdf
- News – Commercial Tech Partnerships Drive … – DVIDS, accessed February 26, 2026, https://www.dvidshub.net/news/501030/commercial-tech-partnerships-drive-unprecedented-progress-project-overmatch-and-navy-capability
- Project Dynamis – Marines.mil, accessed February 26, 2026, https://www.marines.mil/Project-Dynamis/
- MACG-38: The Command-and-Control Enabler for Marine Corps Distributed Operations, accessed February 26, 2026, https://defense.info/featured-story/2026/02/macg-38-the-command-and-control-enabler-for-marine-corps-distributed-operations/
- Force Design Update – Marines.mil, accessed February 26, 2026, https://www.marines.mil/Force-Design/
- Tentative Manual For Expeditionary Advanced Base Operations 2nd Edition – Marines.mil, accessed February 26, 2026, https://www.marines.mil/Portals/1/Docs/230509-Tentative-Manual-For-Expeditionary-Advanced-Base-Operations-2nd-Edition.pdf
- America First but Never Alone: The Critical Need for Coalition Information Sharing, accessed February 26, 2026, https://www.tracesystems.com/america-first-but-never-alone-part-1/
- Interoperability: A Continuing Challenge in Coalition Air Operations – RAND, accessed February 26, 2026, https://www.rand.org/content/dam/rand/pubs/monograph_reports/MR1235/RAND_MR1235.pdf
- Modernizing DOD–Coalition Information Sharing for JADC2 Warfare – SAIC, accessed February 26, 2026, https://www.saic.com/perspectives/jadc2/modernizing-dod-coalition-information-sharing-for-jadc2-warfare
- Mission Partner Environment Cuts Decision Making, Kill Chain – War.gov, accessed February 26, 2026, https://www.war.gov/News/News-Stories/Article/Article/2854238/mission-partner-environment-cuts-decision-making-kill-chain/
- Evaluation of a Line of Effort in the DoD’s Implementation of the Combined Joint All Domain Command and Control (CJADC2) Strategy (Report No. DODIG-2025-126), accessed February 26, 2026, https://www.dodig.mil/reports.html/Article/4250222/evaluation-of-a-line-of-effort-in-the-dods-implementation-of-the-combined-joint/
- Video – Valiant Shield 2024 | Exercise Valiant Shield wraps up – DVIDS, accessed February 26, 2026, https://www.dvidshub.net/video/929576/valiant-shield-2024-exercise-valiant-shield-wraps-up
- Creating a ‘kill web’: Army brings other services, allies together to test new tech for a major fight | The American Legion, accessed February 26, 2026, https://www.legion.org/information-center/news/newsletters/2024/march/creating-a-kill-web-army-brings-other-services-allies-together-to-test-new-tech-for-a-major-fight
- Valiant Shield 2024 Participants Conduct Sinking Exercise – U.S. Pacific Fleet – Navy.mil, accessed February 26, 2026, https://www.cpf.navy.mil/Newsroom/News/Article/3808596/valiant-shield-2024-participants-conduct-sinking-exercise/
- Take lessons learned from joint exercises and turn them into …, accessed February 26, 2026, https://breakingdefense.com/2024/10/take-lessons-learned-from-joint-exercises-and-turn-them-into-capabilities/
- Project Maven – Wikipedia, accessed February 26, 2026, https://en.wikipedia.org/wiki/Project_Maven
- Palantir Expands Maven Smart System AI/ML Capabilities to Military Services, accessed February 26, 2026, https://investors.palantir.com/news-details/2024/Palantir-Expands-Maven-Smart-System-AIML-Capabilities-to-Military-Services/
- ‘Growing demand’ sparks DOD to raise Palantir’s Maven contract to more than $1B, accessed February 26, 2026, https://defensescoop.com/2025/05/23/dod-palantir-maven-smart-system-contract-increase/
- Anduril and Palantir to Accelerate AI Capabilities for National Security, accessed February 26, 2026, https://www.anduril.com/news/anduril-and-palantir-to-accelerate-ai-capabilities-for-national-security
- Understanding mission command | Article | The United States Army, accessed February 26, 2026, https://www.army.mil/article/106872/understanding_mission_command
- The Trouble with Mission Command – NDU Press, accessed February 26, 2026, https://ndupress.ndu.edu/Portals/68/Documents/jfq/jfq-86/jfq-86_94-100_Hill-Niemi.pdf
- MISSION COMMAND – Air Force Doctrine, accessed February 26, 2026, https://www.doctrine.af.mil/Portals/61/documents/AFDP_1-1/AFDP%201-1%20Mission%20Command.pdf
- WILL NEW DOCTRINE FIX MISSION COMMAND? – War Room – U.S. Army War College, accessed February 26, 2026, https://warroom.armywarcollege.edu/articles/new-doctrine-mission-command/
- Human-in-the-loop or AI-in-the-loop? Automate or Collaborate? – arXiv, accessed February 26, 2026, https://arxiv.org/html/2412.14232v1
- Human-in-the-loop in AI workflows: HITL meaning, benefits, and practical patterns – Zapier, accessed February 26, 2026, https://zapier.com/blog/human-in-the-loop/
- Human in the Loop vs Human on the Loop | by VAIOT_LTD | Feb, 2026 – Medium, accessed February 26, 2026, https://vaiotltd.medium.com/human-in-the-loop-vs-human-on-the-loop-880e4538ca65
- Artificial Intelligence and Keeping Humans “in the Loop”, accessed February 26, 2026, https://www.cigionline.org/articles/artificial-intelligence-and-keeping-humans-loop/
- Please Stop Saying ‘Human-In-The-Loop’ – Institute for Future Conflict (IFC), accessed February 26, 2026, https://ifc.usafa.edu/articles/please-stop-saying-human-in-the-loop
- Lessons Learned at Steel Knight 25: Operating Within and as a Kill …, accessed February 26, 2026, https://defense.info/featured-story/2026/02/lessons-learned-at-steel-knight-25-operating-within-and-as-a-kill-web/
- Contested Logistics Environment Defined | Article | The United States Army, accessed February 26, 2026, https://www.army.mil/article/272922/contested_logistics_environment_defined
- Giving Our “Paper Tiger” Real Teeth: Fixing the U.S. Military’s Plans for Contested Logistics Against China – NDU Press, accessed February 26, 2026, https://ndupress.ndu.edu/Media/News/News-Article-View/Article/3942161/giving-our-paper-tiger-real-teeth-fixing-the-us-militarys-plans-for-contested-l/
- Surviving the Kill Web Adapting Army Sustainment to the Precision Strike and Unmanned Threat Era, accessed February 26, 2026, https://www.lineofdeparture.army.mil/Journals/Army-Sustainment/Army-Sustainment-Archive/ASPB-Summer-2025/Surviving-the-Kill-Web/
- Modernizing Defense Logistics: Converging Kill Chains and Supply …, accessed February 26, 2026, https://www.dla.mil/About-DLA/News/News-Article-View/Article/4186321/modernizing-defense-logistics-converging-kill-chains-and-supply-chains/
- Read “Realizing the Potential of C4I: Fundamental Challenges” at NAP.edu, accessed February 26, 2026, https://www.nationalacademies.org/read/6457/chapter/4
- Overcoming Joint Interoperability Challenges > National Defense University Press > Joint Force Quarterly 74, accessed February 26, 2026, https://ndupress.ndu.edu/Joint-Force-Quarterly/Joint-Force-Quarterly-74/Article/577545/overcoming-joint-interoperability-challenges/
- Satellite Cybersecurity: Threats & Impacts – SSH Communications Security, accessed February 26, 2026, https://www.ssh.com/academy/satellite-cybersecurity-threats-impacts
- Cyber Attacks on Space Information Networks: Vulnerabilities, Threats, and Countermeasures for Satellite Security – MDPI, accessed February 26, 2026, https://www.mdpi.com/2624-800X/5/3/76
- What is Cybersecurity in Space? – arXiv, accessed February 26, 2026, https://arxiv.org/html/2509.05496v1
- Cyberwarfare Targeting Undersea Cables and Satellite Mesh Networks – Medium, accessed February 26, 2026, https://medium.com/@aditrizky052/cyberwarfare-targeting-undersea-cables-and-satellite-mesh-networks-1c54ac5949ea
- Impact, Vulnerabilities, and Mitigation Strategies for Cyber-Secure Critical Infrastructure, accessed February 26, 2026, https://pmc.ncbi.nlm.nih.gov/articles/PMC10145335/
- Cybersecurity and the Problem of Interoperability – CSIS, accessed February 26, 2026, https://www.csis.org/analysis/cybersecurity-and-problem-interoperability
- Satellite Infrastructure Is Surprisingly Vulnerable to Cyberattacks – Risk and Resilience Hub, accessed February 26, 2026, https://riskandresiliencehub.com/satellite-infrastructure-is-surprisingly-vulnerable-to-cyberattacks/
- Based, Multi-Domain Anti-Access/Area Denial Forces Play in Deterring or Defeating Aggression? – RAND, accessed February 26, 2026, https://www.rand.org/content/dam/rand/pubs/research_reports/RR1800/RR1820/RAND_RR1820.pdf