Executive Summary
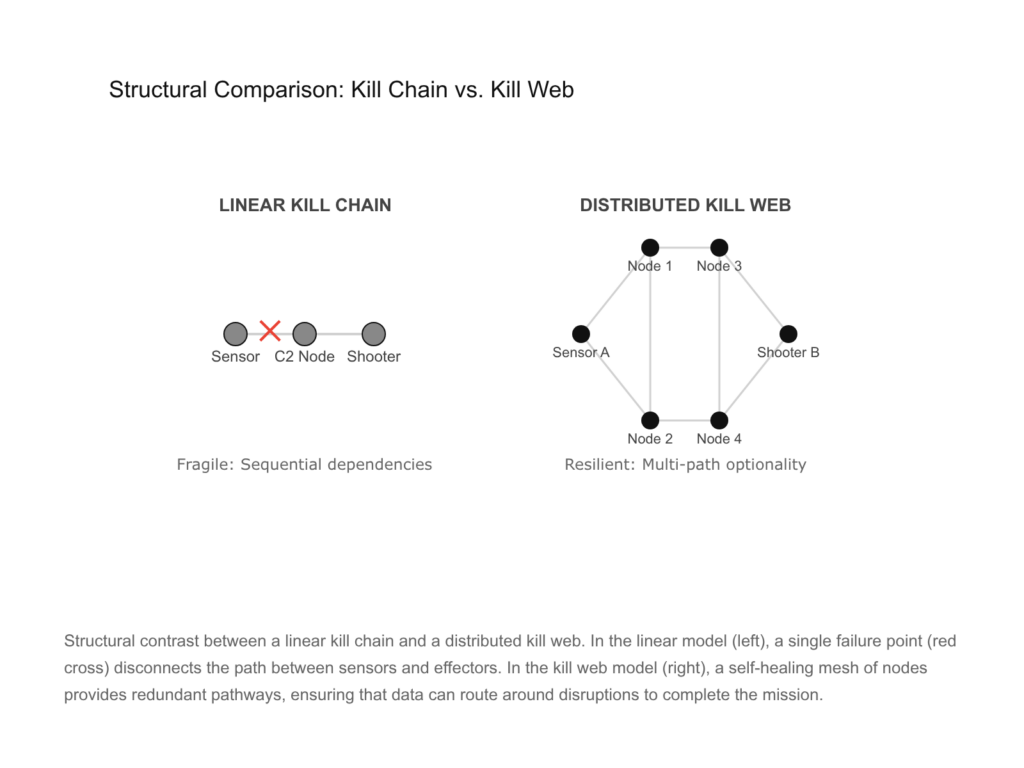
The fundamental character of modern warfare is undergoing a rapid transformation, shifting from a focus on individual, high-value platforms to a decentralized, network-centric architecture known as the kill web. Historically, the United States military relied on the “kill chain,” a linear and sequential process summarized by the find-fix-track-target-engage-assess (F2T2EA) model. While effective in permissive environments, this linear structure is inherently brittle; the disruption of a single node or data link can cause the entire chain to collapse. In response to the sophisticated anti-access/area denial (A2/AD) capabilities of peer competitors like China and Russia, the Department of Defense is transitioning toward a kill web. This concept, born from DARPA’s Mosaic Warfare research, replaces the single, fragile chain with a self-healing mesh of sensors, shooters, and command nodes.
Operating within a kill web requires a cognitive revolution for the individual warfighter, who evolves from a platform operator into a “node of command” or a “quarterback,” managing multiple simultaneous information streams and directing effects across land, sea, air, space, and cyberspace. Conversely, operating as a kill web involves the systemic emergence of the force as a single, integrated organism. This systemic operation is characterized by a “capability marketplace” where AI-driven algorithms match the optimal effector to a specific target in real-time, leveraging the latent capacity of the entire joint force. This report analyzes the technical enablers of this shift—including Joint All-Domain Command and Control (JADC2), edge computing, and artificial intelligence—while addressing the mathematical modeling of resilience and the profound legal and moral implications of machine-interceded agency on the battlefield.
1. The Paradigm Shift: From Asymmetric Advantage to Decision Superiority
The strategic environment facing the United States has shifted from a period of uncontested dominance to one defined by great-power competition. For decades, American military superiority was predicated on a “Second Offset” strategy, which utilized airborne sensors and precision-guided munitions to overcome numerical disadvantages.1 This paradigm matured into the Air-Land Battle concept, which proved triumphant during Operation Desert Storm.1 However, the proliferation of advanced technologies has democratized these advantages. Peer adversaries have developed “system destruction” strategies specifically designed to exploit the vulnerabilities of the traditional American way of war.3
1.1 The Erosion of Traditional Asymmetries
Legacy military power is concentrated in monolithic, multi-capability platforms such as aircraft carriers, stealth bombers, and advanced satellites.2 These platforms are exceptionally capable but represent single points of failure. The loss of a single F-35 or an Arleigh Burke-class destroyer is not only a significant loss of combat power but also a massive financial and strategic blow.2 Adversaries have optimized their forces to target these specific nodes using long-range anti-ship missiles, electronic warfare, and cyber attacks.3
The conventional kill chain is the mechanism by which these platforms are employed. It is a “sensor-to-shooter” path that must remain unbroken to achieve an effect.5 In a contested environment, the adversary’s goal is to “snap” this chain.5 If they can jam the link between a drone and its controller, or destroy the radar station providing coordinates to a missile battery, they have successfully neutralized the threat without necessarily having to destroy every weapon system.3
1.2 The Shift to Decision-Centric Warfare
Military analysts now recognize that the next conflict will be won by the side that can achieve “decision superiority”—the ability to sense, make sense, and act at a speed and scale that the adversary cannot match.6 This is the core principle of Mosaic Warfare. Instead of packing every tool into one elite system, the military is disaggregating capabilities across multiple smaller platforms.2
This shift moves the center of gravity from the platform to the network. The objective is to present the enemy with a “mosaic” of thousands of diverse, fluid pieces that can be rapidly composed and recomposed into a battle plan.1 This complexity is intended to overwhelm the opponent’s decision-making cycle (the OODA loop), forcing them to respond to a wide front of parallel attacks rather than a predictable, linear strike.1
2. Deconstructing the Kill Web
The term “kill web” describes the lethal application of fused data from a highly scalable and resilient battle network.9 It is the technical and operational evolution of the kill chain, designed to preserve the ability to strike even when parts of the system are destroyed or degraded.3
2.1 Defining the Architectural Shift
A kill web is a non-linear, networked approach that unites forces, commanders, and technologies across all domains.10 While a chain is a sequence, a web is a mesh.3 The following comparison clarifies these differences:
Table 1: Comparison of Linear Kill Chains and Kill Webs
| Feature | Linear Kill Chain | Kill Web |
| Core Philosophy | Sequential and platform-centric | Distributed and network-centric |
| Node Interdependency | High; one failure stops the sequence | Low; multiple paths to completion |
| Domain Integration | Often “stovepiped” by service | Inherently cross-domain (All-Domain) |
| Decision Logic | Centralized C2 | Decentralized/Distributed C2 |
| Resiliency | Brittle; easy to target key nodes | Self-healing; redundant and adaptive |
| Scalability | Difficult and rigid | High; “plug-and-play” capability |
2
The transition to a kill web permits the military to operate like a “single organism,” with units moving and acting in concert against numerous objectives.10 This is made possible by advanced sensing technologies that provide a common operational picture (COP) actionable across the full spectrum of operations.10
2.2 The Non-Linearity of F2T2EA
In a kill web, the six tactical functions of the kill chain—Find, Fix, Track, Target, Engage, and Assess—are no longer bound to a single platform or a specific sequence.1 Instead, they are distributed functions that can be executed by any capable node in the network.12
- Find: Ubiquitous sensors (satellites, drones, acoustic sensors, cyber monitors) provide the initial detection.10
- Fix: Cross-domain data fusion determines the target’s precise location, often using different sensing modalities to overcome enemy deception.10
- Track: A target identified by an Air Force jet can be tracked by a Navy ship or a ground-based radar, ensuring continuity even if the original sensor must move or is jammed.5
- Target: AI-enabled matchmaking tools evaluate every available weapon system in the theater to choose the most efficient option.15
- Engage: The selected effector—whether a kinetic missile, a cyber-payload, or an electronic jammer—is directed to the target.5
- Assess: The results are immediately fed back into the web to determine if further action is needed.13
This non-linearity means that a mission does not “restart” if a link is broken; it simply reroutes through the next available node.5
3. DARPA and the Mosaic Warfare Construct
Mosaic Warfare is the conceptual foundation for the kill web. Developed by DARPA, this approach seeks to achieve complex effects through the coordination of many small, diverse, and simple systems.1
3.1 Quantization of Combat Power
Mosaic Warfare relies on the “fractionation” or “quantization” of capabilities.4 In the traditional model, an F-35 is a “monolithic” platform that must find, fix, and target an enemy aircraft itself. In a Mosaic construct, the “find” function might be performed by a swarm of small, inexpensive drones, the “fix” by a distant high-altitude platform, and the “engage” by a missile launched from a cargo plane miles away.1
This quantization allows the military to:
- Increase the number of targets the enemy must engage.1
- Reduce the cost of individual losses.2
- Mass firepower without having to mass forces physically.1
- Rapidly compose a set of needed capabilities for a specific mission.4
3.2 The Logic of the Rhizome
In organizational theory, Mosaic Warfare represents a shift from a “hierarchical” structure to a “rhizome” form.7 A hierarchy is a tree-like structure with a central trunk; if the trunk is severed, the branches die. A rhizome is a decentralized, interconnected network—like a root system or the internet.7 This form is inherently more resilient to targeted disruptions because it lacks a perceivable center or primary point of vulnerability.7
4. Technological Enablers: JADC2 and the Advanced Battle Management System
The realization of the kill web requires a robust digital infrastructure. This is being pursued through the Joint All-Domain Command and Control (JADC2) initiative, which aims to produce a warfighting capability to sense, make sense, and act at all levels and phases of war.17
4.1 ABMS: The Internet of Military Things
The Air Force’s contribution to JADC2 is the Advanced Battle Management System (ABMS).19 ABMS is not a single platform but a “network of networks” or an “internet of military things” (IoMT).17 It provides the digital architecture needed to link sensors and shooters across all domains.8
Key components tested in ABMS “on-ramp” exercises include:
- Cloud-at-the-Edge: Deploying computing systems (supported by vendors like AWS) to process AI algorithms at the tactical front, rather than in distant data centers.22
- Mesh Networking: Using software-defined systems to maintain connectivity across air, land, sea, and space.23
- Airborne Edge Nodes: Specialized platforms designed to bridge communication gaps between incompatible legacy systems, such as the F-22 and F-35, which use different data links.17
4.2 Project Convergence and Project Overmatch
While the Air Force develops the “backbone” via ABMS, the Army and Navy have their own integrated efforts. The Army’s “Project Convergence” focuses on using AI to analyze information and streamline C2 to meet fast-paced threats.19 This program has successfully tested AI-driven tools like “Firestorm,” which can reduce the sensor-to-shooter timeline from hours to minutes.24
The Navy’s “Project Overmatch” is focused on fleet-wide distributed lethality, ensuring that carrier strike groups can operate as a powerful node within a wider web, where any ship’s radar can cue any other ship’s missile.14
5. Operating Within a Kill Web: The Tactical Node
To “operate within” a kill web means that an individual warfighter or platform no longer acts as an isolated player but as an integrated node within a larger system.12
5.1 The Human in the Loop: Cognitive Revolution
The pilot of a fifth-generation fighter jet operating within a kill web undergoes a “cognitive revolution”.12 Their role shifts from executing predefined roles within a linear chain to making distributed, autonomous decisions within an adaptive web.12
Table 2: Evolution of the Combat Aviator’s Role
| Legacy Platform Operator | Modern Kill Web Node |
| Focus: Individual platform proficiency | Focus: Integrated force effectiveness |
| Mindset: Tactical performer executing a mission | Mindset: Strategic decision-maker |
| Inputs: Onboard sensors and voice comms | Inputs: Multi-source sensor fusion and AI analytics |
| Decision Space: Myopic/Local | Decision Space: Holistic/Battlespace Awareness |
| Responsibility: Executing a pre-planned role | Responsibility: Orchestrating effects across the web |
12
This “Quarterback in the Cockpit” must process simultaneous information streams and assess a dynamic battlespace populated with friendly and enemy forces across all six domains (air, land, sea, space, cyber, and electromagnetic spectrum).12
5.2 Live, Virtual, and Constructive (LVC) Training
Preparing warfighters to operate within this complexity requires new training environments. Integrated LVC environments combine real people in real systems (Live), real people in simulated systems (Virtual), and computer-generated forces (Constructive).12 This allows pilots and commanders to practice the “distributed lethality” of the kill web at a scale and complexity that would be impossible—and too expensive—to replicate in purely live exercises.12
6. Operating As the Kill Web: Systemic Emergence
Operating “as” a kill web is a systemic phenomenon where the entire force acts as a complex adaptive system. This goes beyond simple coordination; it is about “convergence”—the ability of the system to self-organize and produce emergent effects that cannot be achieved by individual parts.25
6.1 Algorithmic Bidding and the Capability Marketplace
One of the most disruptive elements of operating as a kill web is the transition of C2 from a manual, hierarchical process to a machine-enabled “capability marketplace”.6 Programs like DARPA’s Adapting Cross-Domain Kill-Webs (ACK) utilize algorithms adapted from commercial e-commerce to manage this complexity.16
The mechanism works as follows:
- Consumer Requirement: A commander identifies a target and the desired effect (e.g., “neutralize radar site”).16
- Bid and Offer: Every available sensor and shooter in the web—regardless of service or domain—”bids” on the task.6
- Valuation: The bid’s quality depends on the platform’s proximity, speed, material condition, success likelihood, and efficiency.6
- Selection: A “Virtual Liaison” selects the best option and tasks the asset, balancing the load across the entire force.16
This process allows the force to operate at “combat speed,” capitalizing on latent capacity that would be missed in a traditional, manual C2 structure.16
6.2 Emergent Complexity and Strategic Surprise
When a military operates as a kill web, it becomes a “non-linear system”.25 The interactions between thousands of sensors, shooters, and AI agents produce “emergent” behaviors that are unpredictable to the enemy.1 This makes the force “operationally and tactically unpredictable,” a key advantage in deteriorating strategic environments.18
By attacking in parallel and using different engagement modalities (e.g., a cyber attack followed by a kinetic strike and an electronic jam), the web forces the adversary to solve multiple distinct problems simultaneously.14 This creates “information-driven shock,” fracturing the adversary’s perception of control and injecting uncertainty into their own decision-making loops.9
7. Mathematical and Probabilistic Foundations
To analyze the effectiveness of a kill web, military analysts utilize various mathematical frameworks. These models help quantify the resilience of a web versus the fragility of a chain.26
7.1 Modeling Chain Fragility
The traditional kill chain is modeled as a Bernoulli process, where each step (m) is a binary event: 1 for success, 0 for failure.26 The probability of the entire chain succeeding (P_Success) is the product of the probabilities of each individual step:
P_Success = p_find * p_fix * p_track * p_target * p_engage * p_assess
In a sequential chain, if each of the six steps has a success probability of 0.9, the overall probability of success is:
0.9 * 0.9 * 0.9 * 0.9 * 0.9 * 0.9 = 0.531 (approximately 53 percent).
If the probability of any single step drops to 0.5 (for example, due to enemy jamming), the entire chain’s success probability drops to roughly 5 percent.26
7.2 Quantifying Web Resilience
A kill web introduces “redundancy” and “multi-path optionality”.3 Analysts use graph-theoretic methods and reinforcement learning to find the optimal path through the web.26
If the “find” step can be performed by three different sensors (A, B, and C), each with a 0.5 probability of success, the probability of the “find” step succeeding in a web is the probability that at least one sensor succeeds:
P_Find_Web = 1 – ( (1 – pA) * (1 – pB) * (1 – pC) )
P_Find_Web = 1 – (0.5 * 0.5 * 0.5) = 0.875 (87.5 percent).
By providing multiple paths for every step of the F2T2EA process, the kill web maintains a high probability of mission success even when individual nodes have a high failure rate.3
2
8. Infrastructure at the Edge
The “connective tissue” of the kill web must be able to function in “denied or degraded” environments where central command links are severed.2
8.1 Edge AI and Latency Optimization
“Edge AI” refers to running artificial intelligence inference directly on the devices where data is generated—drones, sensors, and soldier-worn computers.27 This offers several critical advantages:
- Latency Reduction: Decisions happen in milliseconds, which is critical for intercepting missiles or maneuvering drone swarms.27
- Bandwidth Preservation: Only essential insights are transmitted upstream, preventing the network from being saturated by raw video data.27
- Operational Resilience: Autonomous units can continue to operate and coordinate with nearby partners even if their link to the central cloud is cut.27
Table 3: Comparison of Cloud AI vs. Edge AI for the Kill Web
| Metric | Cloud-Based AI | Tactical Edge AI |
| Compute Power | High (Data Centers) | Moderate (Ruggedized Chips) |
| Latency | High (Round-trip to HQ) | Near-Zero (On-device) |
| Connectivity Requisite | Continuous high-bandwidth | Intermittent or None |
| Security | Vulnerable at transmission | Local data remains isolated |
| Application | Strategic planning | Real-time targeting/navigation |
27
8.2 Security, Zero Trust, and Bandwidth as Terrain
In the kill web, “data is ammunition”.31 Protecting this data requires a shift to “Zero Trust” architectures, where every device must be constantly authenticated.32 Furthermore, military leaders must now “fight for bandwidth” as they once fought for hills.31 If the electromagnetic spectrum is dominated by the adversary, the web’s nodes cannot communicate, reverting the force back into a collection of isolated, less-effective platforms.18
9. Ethical, Legal, and Moral Dimensions of Autonomy
The transition to a machine-enabled kill web introduces profound challenges to the traditional concepts of responsibility and accountability.25
- Legal Causation: Traditional legal tests for “causation” break down in emergent systems. If an AI “bidding” system selects an effector that causes unintended collateral damage, identifying whether the commander, the software developer, or the sensor operator is responsible becomes a complex legal problem.25
- Traceability of Agency: As machine autonomy intercedes on human agency, it becomes “problematic” to identify where a human’s intent ends and a machine’s logic begins.25
- Moral Responsibility: The speed of kill web operations may outpace the ability of humans to exercise “meaningful human control” in every individual strike, requiring a shift in how we ascribe moral weight to combat actions.25
10. Conclusions: Maintaining the Competitive Edge
The development of the kill web is not merely a technical upgrade; it is a strategic necessity to counter the “system destruction” capabilities of peer adversaries. By transitioning from a linear, platform-centric force to a distributed, network-centric mosaic, the United States can achieve decision superiority—the ultimate high ground of 21st-century warfare.
Operating within a kill web demands a more cognitively agile force, where every warfighter is a node of strategic consequence. Operating as a kill web allows the military to leverage the full, latent capacity of its diverse assets, creating a self-healing and unpredictable system-of-systems. While technical hurdles in AI, edge computing, and secure communications remain, the primary challenge is cultural: the military must move away from legacy mindsets that prioritize the individual platform over the integrated network. In the age of decision-centric warfare, victory will belong to the side that can most effectively sense, make sense, and act as a unified, lethal web.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Sources Used
- DARPA Tiles Together a Vision of Mosaic Warfare, accessed February 16, 2026, https://www.darpa.mil/news/features/mosaic-warfare
- Mosaic Warfare: DARPA’s Answer to Combating America’s Advanced Foes, accessed February 16, 2026, https://www.airandspaceforces.com/mosaic-warfare-darpas-answer-to-combating-americas-advanced-foes/
- MITCHELL INSTITUTE Policy Paper – Mitchell Institute for …, accessed February 16, 2026, https://www.mitchellaerospacepower.org/app/uploads/2023/05/Scale_Scope_Speed_Survivability_-KillChain_-Policy_Paper_40-New.pdf
- Findings on Mosaic Warfare from a Colonel Blotto Game – DTIC, accessed February 16, 2026, https://apps.dtic.mil/sti/trecms/pdf/AD1119628.pdf
- Kill Web – UNordinary Group, accessed February 16, 2026, https://www.unordinarygroup.com/home/services/kill-web
- MOSAIC WARFARE – CSBA, accessed February 16, 2026, https://csbaonline.org/uploads/documents/Mosaic_Warfare_Web.pdf
- Aligning Emerging Concepts and Capabilities With Mosaic Warfare, accessed February 16, 2026, https://ciasp.scholasticahq.com/article/127303-aligning-emerging-concepts-and-capabilities-with-mosaic-warfare.pdf
- Quantum Optimization for CJADC2: Enhancing Multi-Domain Command and Control, accessed February 16, 2026, https://www.davidson-tech.com/post/quantum-optimization-for-cjadc2-enhancing-multi-domain-command-and-control
- Operational Art in the Age of Battle Networks – CSIS, accessed February 16, 2026, https://www.csis.org/analysis/chapter-4-operational-art-age-battle-networks
- Sensing: Evolving from Kill Chain to Kill Web in Target Engagement – Sumaria Blog, accessed February 16, 2026, https://blog.sumaria.com/sensing
- A method for kill web operational viewpoint design based on Inf-ProA – SPIE Digital Library, accessed February 16, 2026, https://www.spiedigitallibrary.org/conference-proceedings-of-spie/13442/1344229/A-method-for-kill-web-operational-viewpoint-design-based-on/10.1117/12.3053045.full
- The Kill Web Imperative: A Strategic Analysis of the Paradigm Shift in Combat Pilot Training – Second Line of Defense – SLDinfo.com, accessed February 16, 2026, https://sldinfo.com/2025/11/the-kill-web-imperative-a-strategic-analysis-of-the-paradigm-shift-in-combat-pilot-training/
- Mapping Artificial Intelligence to the Naval Tactical Kill Chain, accessed February 16, 2026, https://nps.edu/documents/10180/142489929/NEJ+Hybrid+Force+Issue_Mapping+AI+to+The+Naval+Kill+Chain.pdf
- How AI-Empowered Kill Webs Enhance Carrier Operations | Defense.info, accessed February 16, 2026, https://defense.info/maritime-dynamics/2025/12/how-ai-empowered-kill-webs-enhance-carrier-operations/
- 133 – Kill webs and super swarms – building survivable CPs for decision superiority | The Principles of War Podcast, accessed February 16, 2026, https://theprinciplesofwar.com/podcast/133-kill-webs-and-super-swarms-building-survivable-cps-for-decision-superiority/
- ACK: Adapting Cross-Domain Kill-Webs | DARPA, accessed February 16, 2026, https://www.darpa.mil/research/programs/adapting-cross-domain-kill-webs
- Decision Superiority: ABMS and the USAF’s Digital … – Air University, accessed February 16, 2026, https://www.airuniversity.af.edu/Portals/10/ASOR/Journals/Volume-1_Number-2/Piubeni2.pdf
- Realising a data-centric all-domain kill-web through network-driven system design | Future Forge, accessed February 16, 2026, https://theforge.defence.gov.au/war-college-papers-2022/realising-data-centric-all-domain-kill-web-through-network-driven-system-design
- Mission (Command) Complete: Implications of JADC2 – NDU Press, accessed February 16, 2026, https://ndupress.ndu.edu/Media/News/News-Article-View/Article/3841502/mission-command-complete-implications-of-jadc2/
- Valenzia: ABMS will deliver the “Decision Advantage” > > Display – Airman Magazine, accessed February 16, 2026, https://www.airmanmagazine.af.mil/Features/Display/Article/2634972/valenzia-abms-will-deliver-the-decision-advantage/
- Mosaic Warfare Strategy in Air Power | Information Sharing Nework, accessed February 16, 2026, http://theairpowerjournal.com/mosaic-warfare-information-interconnectivity-airpower/
- Latest ABMS tests break new barriers on AI and edge cloud capabilities | FedScoop, accessed February 16, 2026, https://fedscoop.com/latest-abms-tests-ai-cloud-cybersecurity/
- Military conducts first test of Advanced Battle Management System – Northern Command, accessed February 16, 2026, https://www.northcom.mil/Newsroom/News/Article/Article/2051047/military-conducts-first-test-of-advanced-battle-management-system/
- Project Convergence: Revolutionizing Targeting in Large-Scale Combat Operations, accessed February 16, 2026, https://www.lineofdeparture.army.mil/Journals/Field-Artillery/Field-Artillery-Archive/Field-Artillery-2025-E-Edition/Project-Convergence/
- Joint All-Domain Kill Webs – Marine Corps Association, accessed February 16, 2026, https://www.mca-marines.org/wp-content/uploads/Pavlak-Oct23.pdf
- Probabilistic Models for Military Kill Chains – MDPI, accessed February 16, 2026, https://www.mdpi.com/2079-8954/13/10/924
- Harnessing Edge AI to Strengthen National Security | Strategic Technologies Blog | CSIS, accessed February 16, 2026, https://www.csis.org/blogs/strategic-technologies-blog/harnessing-edge-ai-strengthen-national-security
- Edge AI in Tactical Defense: Empowering the Future of Military and Aerospace Operations, accessed February 16, 2026, https://dedicatedcomputing.com/edge-ai-in-tactical-defense-empowering-the-future-of-military-and-aerospace-operations/
- Artificial Intelligence Applications Military Network Edge – Curtiss-Wright Defense Solutions, accessed February 16, 2026, https://defense-solutions.curtisswright.com/media-center/blog/artificial-intelligence-applications-military-network-edge
- (PDF) A Survey on the Convergence of Edge Computing and AI for UAVs: Opportunities and Challenges – ResearchGate, accessed February 16, 2026, https://www.researchgate.net/publication/360594094_A_Survey_on_the_Convergence_of_Edge_Computing_and_AI_for_UAVs_Opportunities_and_Challenges
- Beyond the Network: The Army Signal Corps and the Future of Warfare, accessed February 16, 2026, https://www.armyupress.army.mil/journals/military-review/online-exclusive/2025-ole/beyond-the-network/
- Advanced Battle Management System (ABMS) Coverage – Breaking Defense, accessed February 16, 2026, https://breakingdefense.com/tag/advanced-battle-management-system/
