Key Takeaways
- Philosophical Shift: Traditional military force design is transitioning from a “puzzle” of high-cost, monolithic platforms to a “mosaic” of low-cost, attritable, and modular “tiles” that can be rapidly recomposed for mission-specific effects.1
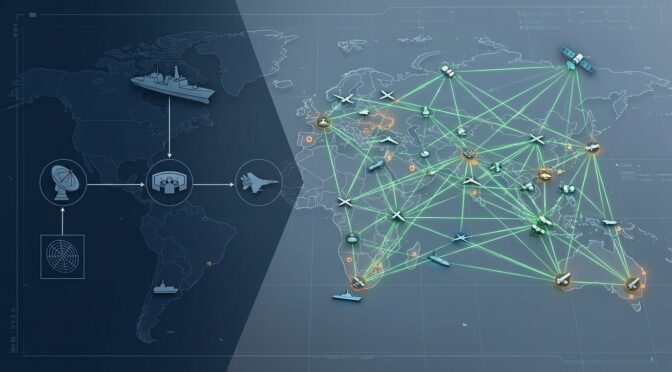
- The Kill Web Advantage: The shift from linear “kill chains” to multi-path “kill webs” creates self-healing mesh networks. This ensures that the destruction of a single node—whether a sensor or a shooter—does not collapse the entire mission.4
- Asymmetric Adaptation: Iran’s “Mosaic Defense” doctrine serves as a masterclass in resilience, decentralizing command into 31 autonomous provincial corps designed to survive decapitation strikes and maintain high-intensity operations without central coordination.6
- Software-Defined Warfare: Platforms like Anduril’s Lattice and Ukraine’s Delta system utilize AI and edge computing to fuse data from thousands of sensors, effectively compressing the sensor-to-shooter timeline from hours to minutes.8
- Localized Manufacturing Revolution: Additive manufacturing (3D printing) and Electrochemical Machining (ECM) are enabling “battlefield foraging” and the production of functional firearms (e.g., FGC-9) and munitions in austere environments, bypassing traditional supply chains.11
- Democratization of OSINT: Tools like ATAK and Meshtastic are empowering civilian and irregular forces with military-grade situational awareness, turning the local populace into a pervasive “sensor mesh” for total defense.13
Table of Contents
- The Death of the Monolith: Defining the Mosaic Paradigm
- Evolution of the Kill Chain: From Linear Strings to Distributed Webs
- The Iranian Doctrine: Regional Autonomy and Survivability
- Software as the Primary Weapon: AI Nodes and Command at the Tactical Edge
- Engineering the Resistance: 3D Printing, ECM, and Decentralized Armories
- The OSINT Revolution: Civilian Tactical Preparedness and Situational Awareness
- Technical Specifications: Attritable Platforms and Edge Computing Hardware
- Strategic Synthesis: The Future of Global Conflict
The Death of the Monolith: Defining the Mosaic Paradigm
The historical reliance on “exquisite” military platforms—multibillion-dollar aircraft carriers, stealth fighters, and monolithic satellite constellations—has reached a point of diminishing returns. DARPA’s Strategic Technology Office (STO) recognizes that the global proliferation of high-tech components has eroded the traditional technological asymmetric advantage enjoyed by the United States.2 In this new reality, a small number of expensive systems creates a “brittle” force architecture. If an adversary manages to neutralize a few key assets, the entire strategic framework can collapse. Mosaic Warfare is the doctrinal answer to this fragility.1
The fundamental concept, pioneered by former DARPA STO director Tom Burns and Dan Patt, is to treat military capabilities like tiles in a mosaic rather than pieces of a puzzle.1 In a puzzle, each piece is uniquely engineered to fit into a specific slot; if one piece is missing, the picture is incomplete. In a mosaic, thousands of small, interchangeable tiles can be arranged to create an effect. If a few tiles are destroyed, the overall image remains recognizable and functional.1 This shift demands a move away from multi-role, highly integrated platforms toward “attritable” systems—unmanned units that are inexpensive enough to be lost without strategic impact.1
This evolution is not merely about hardware; it is about complexity as a weapon. By flooding the battlespace with a heterogeneous mix of sensors, decoys, and shooters, a commander can impose a level of cognitive load on an adversary that prevents effective decision-making.2 While the Cold War focused on “massing forces,” Mosaic Warfare focuses on “massing effects” through distributed networks.1 This allows a force to be dispersed and difficult to target while remaining lethal and coordinated.1
| Feature | Monolithic Warfare (Traditional) | Mosaic Warfare (Emerging) |
| System Cost | High-cost, multi-role platforms | Low-cost, specialized “tiles” |
| Integrator | Single prime contractor | Rapid machine-to-machine composition |
| Interoperability | Rigid, pre-defined standards | Just-in-time, “loose coupling” |
| Resilience | Low (Single points of failure) | High (Redundancy through numbers) |
| Lifecycle | Decades to develop and field | Continuous rapid acquisition |
| Force Design | “Puzzle” pieces (static) | “Mosaic” tiles (fluid) |
The transition toward Mosaic Warfare also reshapes the acquisition process. Instead of spending decades building a single “exquisite” system, the military can buy mosaic “tiles” at a rapid, continuous pace, adapting to new threats as they emerge.2 This approach leverages the DARPA program CASCADE (Complex Adaptive System Composition And Design Environment) to address how new and legacy systems can be dynamically integrated into mission-specific packages.2
Evolution of the Kill Chain: From Linear Strings to Distributed Webs
The core of all military operations is the “kill chain,” a process formally defined as Find, Fix, Track, Target, Engage, and Assess (F2T2EA).5 For decades, the U.S. military has relied on its ability to close this chain faster than any adversary. However, traditional kill chains are linear and hierarchical. Information flows up from a sensor to a commander, who then sends an order down to a shooter.4 This sequential process is vulnerable to disruption at every link.5
The Fragility of Linearity
In a linear kill chain, the loss of a single node—such as a specific radar site or a command-and-control (C2) vehicle—breaks the entire process.5 Adversaries have exploited this by targeting the “joints” of the chain, using electronic warfare to jam datalinks or precision strikes to eliminate command nodes.5 As the Department of Defense moves toward Combined Joint All-Domain Command and Control (CJADC2), the objective is to transform these brittle chains into “kill webs”.4
A kill web operates as a self-healing mesh network. Instead of a single path from sensor to shooter, a kill web offers hundreds of redundant pathways.4 If one sensor is jammed, another (perhaps on a different domain like a satellite or a submarine) can provide the necessary data. If a primary communications link is severed, the network automatically reroutes the information.5 This is functionally similar to a “self-healing” mesh network found in civilian IT environments, but it is applied to the delivery of kinetic and non-kinetic effects.5
Mathematical Resilience of the Web
The shift to kill webs can be viewed through a mathematical lens. In a linear model, the probability of mission success (Pm) is the product of the reliability of each individual link (Pl):
Pm = P_find * P_fix * P_track * P_target * P_engage * P_assess
If any single Pl is reduced by enemy action, the overall Pm drops precipitously.22 In a kill web, however, we introduce multiple parallel paths (k). The probability of failure for a specific stage becomes the product of the failure rates of all redundant nodes in that stage:
P(success)_stage = 1 – [ (1 – Pl,1) * (1 – Pl,2) *… * (1 – Pl,k) ]
This redundancy ensures that even if individual “tiles” or nodes have relatively low survivability, the collective web maintains a high probability of mission success.2
Programmatic Enablers: ACK and ABMS
The DARPA program “Adapting Cross-Domain Kill-Webs” (ACK) is a primary driver of this evolution.23 ACK acts as a decision aid for mission commanders, helping them identify and select the best assets across the Army, Navy, Air Force, and Space Force to strike a target.23 It functions as a “Capability Marketplace” where providers (suppliers) offer assets in terms of the effects they can provide, without exposing sensitive technical details to every other node.23
Similarly, the Air Force’s Advanced Battle Management System (ABMS) is designed to connect large numbers of distributed nodes into a resilient network.5 ABMS moves beyond proprietary, siloing standards toward open architectures that allow for rapid sensor-to-shooter integration across all domains—land, air, sea, space, and cyber.5
The Iranian Doctrine: Regional Autonomy and Survivability
While DARPA develops high-tech kill webs, the Islamic Revolutionary Guard Corps (IRGC) has spent decades perfecting a low-tech, asymmetric version known as “Mosaic Defense” (دفاع موزاییکی).6 This doctrine was born from the “historical trauma” of the 2003 U.S. invasion of Iraq.7 Iranian strategists observed that Saddam Hussein’s highly centralized command structure collapsed instantly once communication between the central palace and the generals was severed.6
Structural Decentralization
In 2008, under General Mohammad Ali Jafari, the IRGC restructured its command architecture into 31 separate provincial corps.7 The country was literally “divided into defensive mosaics”.7 Each province operates as a self-contained, semi-autonomous military entity with its own:
- Intelligence and Counter-Intelligence Units: Tasked with local monitoring and threat detection.7
- Independent Weapon Stockpiles: Thousands of pre-positioned munitions, including ballistic missiles and rockets, often stored in hardened underground facilities.6
- Logistics Chains: Designed to sustain prolonged guerrilla warfare even if the national infrastructure is destroyed.7
- Paramilitary Integration: Each corps manages local Basij units, providing deep human infrastructure for surveillance and population control.7
Pre-Delegated Authority and Decapitation Survival
The defining technical feature of the Iranian Mosaic Defense is “pre-delegated authority.” In the event of a total communications blackout or the loss of senior leadership (a “decapitation strike”), provincial commanders have standing orders to act independently.6 They do not need to check with Tehran to launch retaliatory strikes or initiate insurgent-style ambushes.6
This was rigorously tested in early 2026 during “Operation Epic Fury,” which saw the loss of senior Iranian commanders.6 Rather than collapsing, the provincial commands continued to function, launching “mosquito fleet” naval swarms and localized missile strikes based on pre-set instructions.6 The “Fourth Successor” protocol ensures that every critical leadership position has three to seven pre-identified replacements, preventing any vacuum in command.7
| IRGC Unit Type | Role in Mosaic Defense | Configuration |
| Imam Ali Units | Internal Security | Focused on urban control and counter-insurgency 26 |
| Imam Hossein Units | Defensive Military | Conventional military tasks within a province 26 |
| Beit al-Moqaddas | Rapid Response | Highly mobile units for sudden threat response 26 |
| Ashura / Al-Zahra | Reserve Formations | Locally recruited men and women for support 26 |
Geographic and Tactical Advantages
The Iranian doctrine utilizes the natural geography of the country—the Zagros and Alborz mountains—to create “natural fortresses”.27 Provincial units specialize in the terrain of their specific region, using cave systems and narrow passes to lure invaders into protracted ambushes.27 This “Forward Defense” extends to proxies like Hezbollah and the Houthis, who act as external “tiles” in the broader Iranian mosaic, often making decisions based on local regional calculus rather than direct orders from Tehran.6
Software as the Primary Weapon: AI Nodes and Command at the Tactical Edge
The efficacy of a mosaic force relies entirely on its ability to process information at the “tactical edge.” In modern combat, the environment is often Denied, Disconnected, Intermittent, and Limited (D-DIL).28 Relying on a high-bandwidth connection to a centralized cloud server is a recipe for disaster in a near-peer conflict where electronic warfare (EW) is pervasive.28
Edge AI and Autonomous Decisions
To maintain “decision dominance,” militaries are transitioning to a distributed Edge Artificial Intelligence architecture.29 This requires shifting the “brain” of the operation from the rear headquarters to the frontline sensors and shooters.29
Key demands for Tactical Edge AI:
- Autonomous Operation: Storage and processing must function independently for days or weeks without connectivity.28
- Model Compression: Algorithmic models must be small enough to run on ruggedized hardware with limited Size, Weight, and Power (SWaP).29
- Low Latency: Real-time video feeds from drones must be processed locally to identify threats in seconds.28
- Resilience: The system must tolerate the loss of individual computing nodes while maintaining the integrity of the local data mesh.9
Anduril Lattice: The Operating System for Autonomy
Anduril Industries has pioneered the “software-defined weapon” with its Lattice platform.9 Lattice is an AI-powered battle management system that integrates thousands of sensors and effectors into a single common operating picture (COP).9 Unlike legacy systems, Lattice is an open architecture that exposes REST and gRPC APIs, allowing third-party sensors and drones to “plug in” to the mesh.31
In field exercises like “Ivy Sting 5,” Lattice Mesh demonstrated its ability to operate in a totally degraded communications environment.10 Even when satellite and commercial links were eliminated, the local mesh allowed a special operations unit to pass target data to a Marine Corps HIMARS unit entirely digitally, reducing targeting timelines from hours to minutes.10
Ukraine’s Delta System
Ukraine’s “Delta” system is a real-world implementation of the mosaic software logic. Developed by the NGO “Aerorozvidka” and the Ukrainian Ministry of Defense, Delta is a cloud-native situational awareness platform that fuses data from drones, satellite imagery, and human intelligence.33
One of Delta’s most significant subsystems is “Vezha,” which aggregates live drone feeds.8 By September 2024, the “Avengers” AI platform was reportedly analyzing these feeds to identify up to 12,000 pieces of enemy equipment per week.8 This allows Ukrainian units to log sightings and share them in near real-time across a user-friendly digital map, enabling small, decentralized teams to achieve massed effects.8
Engineering the Resistance: 3D Printing, ECM, and Decentralized Armories
One of the most disruptive aspects of Mosaic Warfare is the decentralization of manufacturing. Traditionally, if a unit ran out of spare parts or weapons, they were at the mercy of a long, vulnerable supply chain.11 Additive Manufacturing (AM), or 3D printing, is fundamentally changing this dynamic, enabling “battlefield foraging” and local production.11
Battlefield Foraging and Frontline Repair
The U.S. Marine Corps is actively deploying 3D printers and CNC (Computer Numerical Control) mills to the frontline.11 This allows Marines to manufacture mission-critical components, such as repair parts for the Joint Light Tactical Vehicle or medical casts, directly in the combat zone.11 By printing parts on-demand, units can bypass the “iron mountains” of traditional logistics and remain agile in contested environments like the Indo-Pacific.11
Additive manufacturing is also being used for Maintenance, Repair, and Overhaul (MRO) of legacy systems. If an original equipment manufacturer (OEM) no longer produces a part for a 40-year-old howitzer, AM can be used to produce a one-off replacement in situ.35
The FGC-9 and the Rise of “Ghost” Weaponry
In the asymmetric arena, the FGC-9 (Feed Guidance Control 9mm) has become a symbol of decentralized lethality.12Engineered by a designer known as JStark180, the FGC-9 is a semi-automatic carbine that requires zero regulated firearm parts.12This is a massive leap over early “novelty” prints like the Liberator.
The engineering breakthroughs of the FGC-9 ecosystem include:
- Electrochemical Machining (ECM): Using a 3D-printed jig, a bucket of saltwater, and a simple power source (like a battery), a user can chemically “etch” rifling into a piece of ordinary hydraulic tubing, creating a high-pressure-capable barrel.12
- Material Science: Modern builds utilize high-strength polymers like Polylactic Acid Plus (PLA+) and carbon fiber blends, which can withstand thousands of rounds of live fire.12
- Hybrid Design: The firearm uses 3D-printed receivers paired with easily sourced “hardware store” components like bolts, nuts, and springs.12
This technology has been successfully utilized by the People’s Defence Forces in Myanmar, who have established “jungle workshops” to produce these weapons in significant quantities.12 This digital insurgency model ensures that even if traditional arms markets are interdicted, the resistance can continue to arm itself using only a laptop and a consumer-grade 3D printer.12
The OSINT Revolution: Civilian Tactical Preparedness and Situational Awareness
The mosaic logic is not limited to state actors; it is rapidly being adopted by the civilian OSINT (Open-Source Intelligence) and tactical preparedness communities. This has led to a “democratization of situational awareness” that was previously the sole domain of nation-states.13
ATAK-Civ: The Civilian Tactical Operating System
The Android Team Awareness Kit (ATAK), originally developed for Air Force Special Operations, is now available in a civilian-use variant (ATAK-Civ).14 ATAK-Civ transforms an ordinary smartphone into a sophisticated geospatial tool.15
Civilian capabilities of ATAK-Civ include:
- Position Location Information (PLI): Real-time tracking of team members on a digital map.15
- Cursor-on-Target (CoT): A standardized data format that allows for the sharing of target markers and situational alerts.14
- Offline Mapping: High-resolution imagery and topographical maps can be stored locally for use when the internet is unavailable.15
- Plugin Architecture: Developers can add features like biometric monitoring or integration with thermal sensors.14
Meshtastic: Off-Grid Resilience
One of the most critical developments for the DIY community is the integration of ATAK-Civ with Meshtastic, an open-source mesh networking system built on low-cost LoRa (Long Range) radio modules.15 Meshtastic allows for the creation of an ad-hoc communication network without any dependence on cellular towers or satellites.15
A LoRa-based mesh network provides:
- Line-of-Sight Range: 5-10 km between nodes, with messages automatically hopping through the network to reach distant teammates.15
- Low Electronic Signature: LoRa operates at very low power, making it difficult for adversaries to detect using standard electronic warfare tools.15
- Encryption: End-to-end encryption ensures that all team awareness data remains secure.15
Total Defense: Turning Citizens into Sensors
The war in Ukraine has highlighted the “Total Defense” framework, where the civilian population is integrated into national defense planning.13 By weaponizing smartphones and social media, Ukraine has essentially turned every citizen into a sensor node in their kill web.13 Citizens use digital tools to report Russian troop movements in real-time, which are then geolocated and mapped within systems like Delta to cue military strikes.13 This creates an environment of “near-total transparency” where the adversary’s movements are constantly exposed.13
Technical Specifications: Attritable Platforms and Edge Computing Hardware
The mosaic concept is brought to life through a diverse array of hardware “tiles.” Below are the technical specifications for representative systems in both the US and asymmetric/civilian contexts.
The Raytheon Coyote Family (US Attritable UAS)
The Coyote is the benchmark for modular, tube-launched “tiles” that can be rapidly recomposed for various missions.44
| Specification | Coyote Block 1 (ISR/Strike) | Coyote Block 2 (C-UAS) | Coyote Block 3 (Swarm Defeat) |
| Propulsion | Electric motor / Pop-out wings | Solid-fuel booster + Turbojet | Rocket launch / Jet powered |
| Cruising Speed | 102 km/h (55 knots) | Up to 555 km/h | ~555 km/h |
| Endurance | > 1 hour | ~4 minutes (Loiter) | Extended / Recoverable |
| Weight | 5.9 kg (13 lb) | ~22 kg | (Larger format) |
| Warhead | Kinetic / ISR Payload | Proximity-fragmentation | Non-kinetic (HPM) |
| Range (Comms) | 130 km (80 miles) | ≥ 15 km | Multi-engagement |
Edge Computing Nodes (Software-Defined Command)
To power AI-driven platforms like Lattice and Delta, specialized edge hardware is required to process massive amounts of data in the field.28
| Model | Application | Capabilities |
| Parsons SN 3100 | Tactical Backpack Node | Flexible edge workloads in a portable case 46 |
| Parsons SN 5100 | High-Power Edge Server | 84 cores, PCIe Gen5 for GPU-accelerated AI 46 |
| Parsons GN 7000 | Analytics Node | Optimized specifically for AI/ML at the edge 46 |
| Anduril Voyager | Distributed Data Layer | Vehicle-mounted node for Lattice Mesh 10 |
3D-Printed Firearm Classification (DIY Engineering)
Firearms engineers in the OSINT community classify 3D-printed weaponry based on the percentage of printed vs. commercial components.39
- Fully 3D-Printed (F3DP): Almost entirely printed, including the barrel (non-rifled). Usually single-shot or limited-use (e.g., Liberator, Washbear).39
- Hybrid Firearms: Primarily 3D-printed but integrate “hardware store” materials like steel tubing for barrels and bolts for pins. These can be semi-automatic and are highly durable (e.g., FGC-9, Urutau).12
- Parts-Kit Completions (PKC): Utilize a 3D-printed receiver/frame but use commercial factory-made slides, barrels, and trigger groups. These are indistinguishable from commercial firearms in performance (e.g., 3D-printed Glock-style frames).39
Strategic Synthesis: The Future of Global Conflict
The strategic evolution of Mosaic Warfare and distributed kill webs represents a move toward “emergence” as a military principle. Advantage no longer belongs to the actor with the most powerful single platform, but to the actor who can most rapidly integrate disparate, low-cost nodes into a cohesive, adaptive whole.2
For the modern warfighter and the tactical enthusiast, the lessons are clear:
- Redundancy is Resilience: In both network design and hardware, single points of failure must be eliminated. The kill web philosophy should be applied to communications, supply chains, and power systems.5
- Software is the Force Multiplier: The ability to fuse data from thousands of sensors—be they military-grade radars or smartphone cameras—is the decisive factor in modern situational awareness.8
- Local Manufacturing is Strategic Depth: The ability to produce replacement parts and defense articles in situ, using 3D printing and ECM, reduces vulnerability to interdiction and ensures continuity of operations.11
As we move toward a future of “near-total transparency” and “algorithmic command,” the mosaic approach allows for a fluid, decentralized, and infinitely adaptable form of warfare that is as effective in the hands of a superpower as it is in the hands of a local resistance.12 The traditional “Air-Land Battle” has given way to a multi-domain, software-defined mosaic of lethality.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Works cited
- DARPA Tiles Together a Vision of Mosaic Warfare, accessed April 18, 2026, https://www.darpa.mil/news/features/mosaic-warfare
- Strategic Technology Office Outlines Vision for “Mosaic Warfare” – DARPA, accessed April 18, 2026, https://www.darpa.mil/news/2017/sto-mosaic-warfare
- CHIPS Articles: Strategic Technology Office Outlines Vision for “Mosaic Warfare”, accessed April 18, 2026, https://www.doncio.navy.mil/chips/ArticleDetails.aspx?ID=9305
- Sensing: Evolving from Kill Chain to Kill Web in Target Engagement – Sumaria Blog, accessed April 18, 2026, https://blog.sumaria.com/sensing
- MITCHELL INSTITUTE Policy Paper – Mitchell Institute for …, accessed April 18, 2026, https://www.mitchellaerospacepower.org/app/uploads/2023/05/Scale_Scope_Speed_Survivability_-KillChain_-Policy_Paper_40-New.pdf
- Iran’s ‘Mosaic Defense’ Strategy: Decentralization as Resilience Factor – The Soufan Center, accessed April 18, 2026, https://thesoufancenter.org/intelbrief-2026-march-9a/
- Iran’s Mosaic Defense Faces Its Real Test, accessed April 18, 2026, https://jiss.org.il/en/grinberg-irans-mosaic-defense-faces-its-real-test/
- The Heart of War: Ukraine’s Key Battlefield System – CEPA, accessed April 18, 2026, https://cepa.org/article/the-heart-of-war-ukraines-key-battlefield-system/
- Command & Control – Anduril, accessed April 18, 2026, https://www.anduril.com/lattice/command-and-control
- Scaling Next-Generation Command and Control from Prototype to Fight – Anduril, accessed April 18, 2026, https://www.anduril.com/news/scaling-next-generation-command-and-control-from-prototype-to-fight
- Forging the Future: How Advanced Manufacturing Is Revolutionizing …, accessed April 18, 2026, https://www.marines.mil/News/News-Display/Article/3549430/forging-the-future-how-advanced-manufacturing-is-revolutionizing-marine-corps-l/
- From Filament to Firepower: 3D Printing’s Impact on Warfare, accessed April 18, 2026, https://warontherocks.com/from-filament-to-firepower-3d-printings-impact-on-warfare/
- Total Defense and OSINT: The Role of Citizens in Modern Warfare – Small Wars Journal, accessed April 18, 2026, https://smallwarsjournal.com/2026/03/26/total-defense-osint-citizens-modern-warfare/
- Android Team Awareness Kit – Wikipedia, accessed April 18, 2026, https://en.wikipedia.org/wiki/Android_Team_Awareness_Kit
- ATAK & Meshtastic for Next-Generation Field Intelligence – SpecFive LLC, accessed April 18, 2026, https://specfive.com/blogs/whitepapers/atak-meshtastic-for-next-generation-field-intelligence
- Acquiring a Mosaic Force: Issues, Options, and Trade-Offs – RAND, accessed April 18, 2026, https://www.rand.org/content/dam/rand/pubs/research_reports/RRA400/RRA458-3/RAND_RRA458-3.pdf
- Mosaic Warfare In Ukraine – The Defence Horizon Journal, accessed April 18, 2026, https://tdhj.org/blog/post/mosaic-warfare-ukraine/
- Mosaic Warfare: The March Towards Interconnectivity in US, UK and European Air Power, accessed April 18, 2026, http://theairpowerjournal.com/mosaic-warfare-information-interconnectivity-airpower/
- Timothy Grayson – Mosaic Warfare – SPIE, accessed April 18, 2026, https://spie.org/news/dcs-plenary—mosaic-warfare
- MITCHELL INSTITUTE Policy Paper, accessed April 18, 2026, http://www.yanwuzhiku.com/userfiles/upload/file/80b54bb66c702b976666b29090b6898c.pdf
- Greenland and the High Ground of the Kill Web: Why the Arctic Matters for Fighting at the Speed of Light | Defense.info, accessed April 18, 2026, https://defense.info/defense-decisions/2026/02/greenland-and-the-high-ground-of-the-kill-web-why-the-arctic-matters-for-fighting-at-the-speed-of-light/
- Probabilistic Models for Military Kill Chains – MDPI, accessed April 18, 2026, https://www.mdpi.com/2079-8954/13/10/924
- ACK: Adapting Cross-Domain Kill-Webs – DARPA, accessed April 18, 2026, https://www.darpa.mil/research/programs/adapting-cross-domain-kill-webs
- MOSAIC WARFARE AS A NEW ART OF WAR? – The Review of International Affairs, accessed April 18, 2026, https://thereviewofinternationalaffairs.rs/wp-content/uploads/RI/2025/1195/RI-2025-1195-article-3.pdf
- accessed April 18, 2026, https://en.wikipedia.org/wiki/IRGC_Provincial_Corps#:~:text=Under%20Iran’s%20concept%20of%20%22mosaic,the%20loss%20of%20senior%20leadership.
- IRGC Provincial Corps – Wikipedia, accessed April 18, 2026, https://en.wikipedia.org/wiki/IRGC_Provincial_Corps
- (PDF) Iran’s Mosaic Defence: A New Doctrine in Evolving Warfare – ResearchGate, accessed April 18, 2026, https://www.researchgate.net/publication/402975270_Iran’s_Mosaic_Defence_A_New_Doctrine_in_Evolving_Warfare
- From Data to Dominance at the Tactical Edge – MinIO, accessed April 18, 2026, https://www.min.io/blog/from-data-to-dominance-at-the-tactical-edge
- Operationalizing AI at the Tactical Edge – Line of Departure – U.S. Army, accessed April 18, 2026, https://www.lineofdeparture.army.mil/Journals/Warrant-Officer-Journal/Archive/March-2026/Operationalizing-AI-at-the-Tactical/
- Edge AI in Tactical Defense: Empowering the Future of Military and Aerospace Operations, accessed April 18, 2026, https://dedicatedcomputing.com/edge-ai-in-tactical-defense-empowering-the-future-of-military-and-aerospace-operations/
- Anduril Industries — Deep Dive – Medium, accessed April 18, 2026, https://medium.com/buvcg-research/anduril-industries-deep-dive-6949c7dd41c7
- Lattice for Command & Control Reviews in 2026 – SourceForge, accessed April 18, 2026, https://sourceforge.net/software/product/Lattice-for-Command-Control/
- Delta (situational awareness system) – Wikipedia, accessed April 18, 2026, https://en.wikipedia.org/wiki/Delta_(situational_awareness_system)
- Network-centric Warfare in Ukraine: The Delta System – Grey Dynamics, accessed April 18, 2026, https://greydynamics.com/network-centric-warfare-in-ukraine-the-delta-system/
- Additive Manufacturing in Warfare – CNTR Monitor, accessed April 18, 2026, https://monitor.cntrarmscontrol.org/en/2024/additive-manufacturing-in-warfare/
- Force Protection for Distribution Based-Logistics in Asymmetric Warfare – DTIC, accessed April 18, 2026, https://apps.dtic.mil/sti/tr/pdf/ADA436192.pdf
- Additive Manufacturing in the Military Technology Sector: Application and Proliferation of an Emerged Technology, accessed April 18, 2026, https://www.prif.org/fileadmin/Daten/Publikationen/Prif_Reports/2025/PRIF_3_2025_barrierefrei.pdf
- The Next Frontier of Conflict: Why 3D-Printed Weapons Will Demand Attention in 2026, accessed April 18, 2026, https://www.forumarmstrade.org/blog/the-next-frontier-of-conflict-why-3d-printed-weapons-will-demand-attention-in-2026
- 3D-Printed Firearms and Terrorism: Trends and Analysis Pertinent to Far-Right Use – RSIS, accessed April 18, 2026, https://rsis.edu.sg/ctta-newsarticle/3d-printed-firearms-and-terrorism-trends-and-analysis-pertinent-to-far-right-use/
- From Tweets to Tactics: The Transformative Impact of Social Media on Modern Warfare Dynamics – Freeman Spogli Institute for International Studies, accessed April 18, 2026, https://fsi.stanford.edu/sipr/tweets-tactics
- ATAK-CIV (Civil Use) – Apps on Google Play, accessed April 18, 2026, https://play.google.com/store/apps/details?id=com.atakmap.app.civ
- Download – CivTAK / ATAK, accessed April 18, 2026, https://www.civtak.org/download-atak/
- ATAK Plugin – Meshtastic, accessed April 18, 2026, https://meshtastic.org/docs/software/integrations/integrations-atak-plugin/
- Coyote UAS | Raytheon – RTX, accessed April 18, 2026, https://www.rtx.com/raytheon/lang/ro/capabilities/products/counter-uas/effectors/coyote
- Coyote C-UAS | Raytheon – RTX, accessed April 18, 2026, https://www.rtx.com/raytheon/what-we-do/integrated-air-and-missile-defense/coyote
- Tactical Edge Computing Nodes – Parsons Corporation, accessed April 18, 2026, https://www.parsons.com/products/tactical-edge-computing/
- Investigating the availability of 3D-printed firearm designs on the clear web – PMC, accessed April 18, 2026, https://pmc.ncbi.nlm.nih.gov/articles/PMC10630772/
- Printing Violence: Urgent Policy Actions Are Needed to Combat 3D-Printed Guns, accessed April 18, 2026, https://everytownresearch.org/report/printing-violence-urgent-policy-actions-are-needed-to-combat-3d-printed-guns/