Executive Summary
The joint military campaign executed by the United States and Israel on February 28, 2026, officially designated Operation Epic Fury by the United States Central Command, has fundamentally altered the global geopolitical security environment. The targeted decapitation of the Iranian regime senior leadership, including Supreme Leader Ayatollah Ali Khamenei and top commanders within the Islamic Revolutionary Guard Corps, represents an existential threat to the Islamic Republic of Iran. Consequently, the deterrence calculus that previously restrained Tehran from activating embedded operative networks within the United States homeland has largely evaporated. This report provides a comprehensive national security assessment of the probability that Iranian sleeper cells, including Islamic Revolutionary Guard Corps affiliates and proxy organizations such as Hezbollah, will initiate kinetic and cyber operations within the United States.
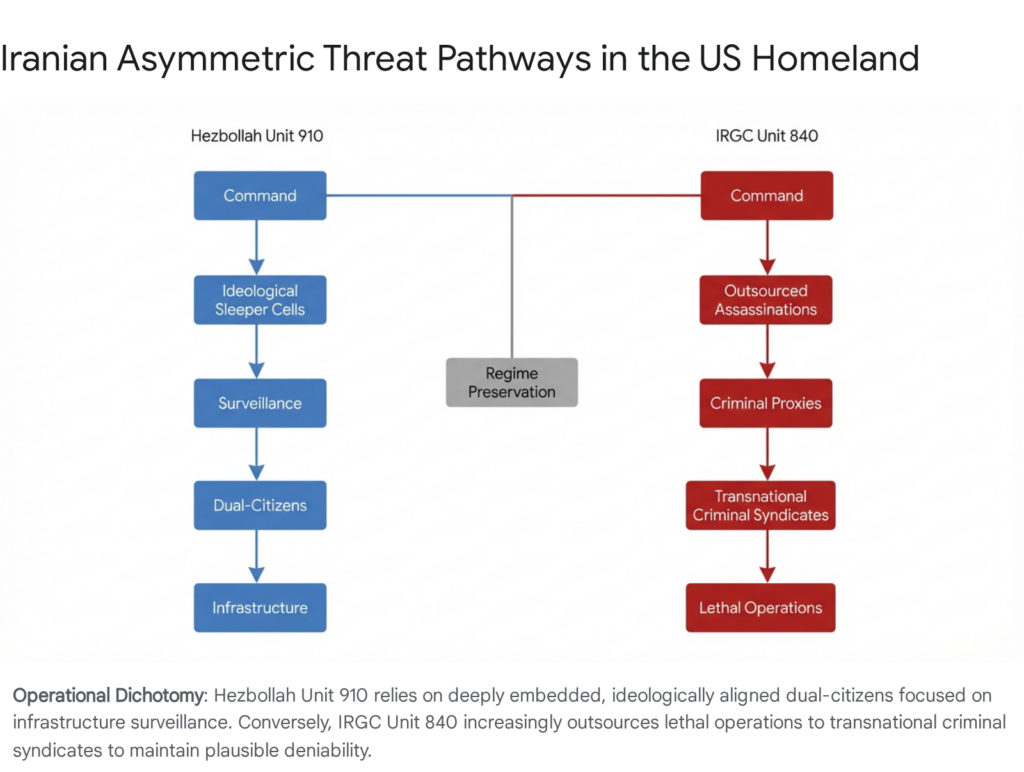
The probability of sleeper cell activation is currently assessed as exceptionally high. Iran possesses a documented, decades long history of asymmetric warfare and has methodically cultivated a homeland option for retaliatory contingencies. Intelligence indicates that these networks operate through a dual track methodology. The first track involves highly disciplined, long term operatives belonging to the Lebanese Hezbollah External Security Organization, commonly known as Unit 910 or the Islamic Jihad Organization. These individuals are deeply embedded within American communities, hold legitimate identification, and focus heavily on pre operational surveillance of critical infrastructure and military nodes. The second track involves the Islamic Revolutionary Guard Corps Quds Force Unit 840, which increasingly outsources lethal operations to transnational criminal syndicates to maintain plausible deniability.
This assessment identifies a strategic concentration of these networks within major United States metropolitan areas. Primary operational hubs remain in New York City, Washington District of Columbia, Chicago, Los Angeles, Detroit, and Houston. However, adversarial counter surveillance adaptations have prompted the dispersion of operatives into secondary logistical nodes, notably Portland in Oregon and Louisville in Kentucky, to evade federal monitoring. Target sets have expanded beyond prominent political figures and dissidents to include energy grids, transit hubs, and the defense industrial base, indicating a shift from symbolic retaliation to systemic economic disruption.
Current countermeasures executed by the Department of Homeland Security, the Federal Bureau of Investigation, and the Department of Justice face severe operational headwinds. While Joint Terrorism Task Forces remain on high alert nationwide, structural vulnerabilities within the domestic security apparatus threaten interagency effectiveness. Recent administrative dismissals within the Federal Bureau of Investigation CI-12 counterintelligence unit have degraded human intelligence networks specific to Iran. Concurrently, funding lapses and personnel reductions at the Cybersecurity and Infrastructure Security Agency have complicated the detection of hybrid cyber physical threats. Furthermore, the March 2026 mass shooting in Austin, Texas, illustrates the severe supplementary threat of lone actor mobilization driven by foreign state propaganda. The convergence of these institutional strains, combined with a highly motivated adversary facing regime collapse, presents an unprecedented challenge to the security of the United States homeland.
1. Strategic Context of Operation Epic Fury and Geopolitical Escalation
The strategic landscape shifted permanently in late February 2026 when United States and Israeli forces initiated a massive preemptive military campaign against the Islamic Republic of Iran. The offensive, codenamed Operation Epic Fury by the United States and Operation Roaring Lion by Israel, was designed to achieve total regime disruption and neutralize the Iranian nuclear and ballistic missile programs.1 This section outlines the parameters of the operation and the immediate geopolitical fallout that contextualizes the current domestic threat environment.
1.1. Execution and Objectives of the Military Campaign
Commencing at approximately 0115 Eastern Standard Time on February 28, 2026, the United States Central Command applied a comprehensive air campaign to shape the battlespace.3 The initial phases prioritized the degradation of integrated air defenses, command networks, and missile nodes. The operation involved over one thousand seven hundred strike sorties by American forces, successfully prosecuting more than one thousand two hundred and fifty Iranian targets within the first forty eight hours of the conflict.1
Most critically, the operation achieved immediate strategic decapitation. Precision strikes on a leadership compound in Tehran successfully eliminated Supreme Leader Ayatollah Ali Khamenei. The strikes also killed a significant portion of the national security architecture, including Defense Minister Aziz Nasirzadeh, Islamic Revolutionary Guard Corps Commander in Chief Mohammad Pakpour, and Military Council head Admiral Ali Shamkhani.4 The rapid elimination of the regime command and control structure triggered an immediate succession crisis and devolved military launch authority to mid level Islamic Revolutionary Guard Corps commanders.6
The stated objectives of the Trump administration centered on defending the American people by eliminating imminent threats, completely destroying the Iranian ballistic missile infrastructure, annihilating Iranian naval capabilities, and permanently crippling the nuclear program.2 While regime change was not formally declared as a statutory goal, the scale of the decapitation strikes indicates that the ultimate ambition of the campaign is the complete collapse of the current Islamic Republic framework.1
| Phase of Operation | Target Categories | Strategic Objective | Operational Impact |
| Phase One (Initial Salvo) | Supreme Leader Compound, IRGC Headquarters, Defense Ministry | Strategic Decapitation | Elimination of Ayatollah Khamenei and top IRGC generals; disruption of centralized command and control.4 |
| Phase Two (Air Superiority) | Radar installations, Surface-to-Air Missile batteries, Early Warning Systems | Battlespace Shaping | Neutralization of Iranian air defenses; establishment of uninhibited airspace for allied bomber fleets.3 |
| Phase Three (Infrastructure) | Ballistic missile silos, nuclear research sites, naval bases | Capability Destruction | Long term degradation of Iranian force projection and nuclear weaponization capabilities.1 |
1.2. The Iranian Retaliatory Doctrine and Regional Escalation
The Iranian response to this existential threat was immediate, coordinated, and region wide, demonstrating a pre planned multi domain retaliation framework. Rather than capitulating, the surviving elements of the Islamic Revolutionary Guard Corps implemented layered responses combining kinetic attacks, cyber disruption, and proxy activation to impose maximum costs on the United States and its regional allies.7
Iran launched hundreds of ballistic missiles and suicide drones against Israeli territory and United States military installations across the Persian Gulf. Confirmed targets included Al Udeid Air Base in Qatar, Naval Support Activity Bahrain, Ali Al Salem Air Base in Kuwait, and Al Dhafra Air Base in the United Arab Emirates.7 By treating the United States basing network as a unified operational system rather than discrete entities, Iran signaled that the entire regional posture of the United States remains vulnerable despite the decapitation of leadership.7
Furthermore, Iran activated its Axis of Resistance network. Hezbollah initiated rocket attacks from southern Lebanon into northern Israel, while Houthi forces in Yemen resumed aggression against commercial shipping in the Red Sea.9 In a drastic measure to maintain internal security and prevent intelligence leaks regarding the locations of surviving regime figures, the Iranian government imposed a near total internet blackout, dropping national connectivity to approximately one percent of standard levels.10
1.3. Shift in the Asymmetric Deterrence Calculus
The most significant consequence of Operation Epic Fury for the United States homeland is the fundamental shift in the Iranian deterrence calculus. Historically, Iran has utilized its external intelligence apparatus to gather information, silence dissidents, and prepare contingency plans while carefully avoiding catastrophic actions that would provoke a full scale conventional war with the United States.11 This restraint was rooted in a foundational desire for regime preservation.
Following the events of February 28, that restraint has vanished. A regime in its death throes loses the deterrent logic that previously kept its sleeper cells in reserve. Because the regime views its survival as already compromised by the allied military campaign, it possesses nothing left to preserve by withholding its most devastating asymmetric assets.11 Consequently, the homeland option, a network of embedded operatives cultivated over decades, transitions from a theoretical contingency to an active operational priority.
2. Probability Assessment of Sleeper Cell Activation
The probability of Iranian sleeper cells conducting physical or cyber operations within the United States is currently assessed as exceptionally high. This assessment is grounded in the historical operational patterns of Iranian intelligence, the recent volume of disrupted plots on American soil, and the removal of the aforementioned strategic restraints.
2.1. Historical Precedents and the Homeland Option
The United States intelligence community has long recognized the commitment of the Iranian regime to developing a homeland option. Intelligence generated by the Central Intelligence Agency and the Federal Bureau of Investigation indicates that Iran has sustained embedded networks within the United States for decades. These units function as a strategic contingency, conducting intelligence gathering, targeted killings, and forging alliances with local criminal elements.12
A watershed moment in recognizing this domestic threat occurred in 2011 when federal authorities disrupted an Islamic Revolutionary Guard Corps Quds Force plot to assassinate the Saudi Arabian ambassador at a restaurant in Washington District of Columbia.12 This brazen scheme, which involved attempting to hire members of a Mexican drug cartel, reshaped federal assessments of state sponsored domestic terrorism and demonstrated the willingness of Tehran to bring kinetic conflict to the American homeland.12
2.2. Disrupted Plots and Procurement Networks (2020 to 2026)
Since 2020, following the United States military strike that eliminated Quds Force Commander Qasem Soleimani, the operational tempo of Iranian networks within the United States has increased significantly. Federal law enforcement has disrupted at least seventeen Iranian linked plots in the homeland over the past six years.13 These unsealed indictments reveal a persistent, highly resourced effort to target former United States officials, journalists, and regime dissidents.12
Prominent examples include disrupted murder for hire schemes targeting former National Security Advisor John Bolton, former Secretary of State Mike Pompeo, and former President Donald Trump, which Iranian operatives explicitly framed as retaliation for the death of Soleimani.12 Additionally, federal prosecutors charged an operative of the Islamic Revolutionary Guard Corps and two United States based individuals with plotting to surveil and assassinate Iranian American journalist Masih Alinejad in Brooklyn, New York.12
Beyond lethal operations, Iranian linked networks have maintained a robust presence on American soil for the purpose of illicit procurement. These networks actively seek to acquire sensitive dual use technology, software, and high tech equipment to support the Iranian military industrial complex and circumvent international sanctions.15 The sheer volume of these thwarted operations indicates a highly capable, deeply entrenched network that is already operational and possesses the logistical frameworks necessary to execute attacks upon receiving authorization.
3. Operational Profiles of Iranian Proxy Networks
The asymmetric threat posed by Iran within the United States is primarily executed through two distinct, yet complementary, operational pathways. The first involves the highly disciplined, ideologically aligned operatives of Lebanese Hezbollah. The second involves the transactional, outsourced operations of the Islamic Revolutionary Guard Corps Quds Force. Understanding the divergent methodologies of these two entities is critical for effective counterterrorism resource allocation.
3.1. The Threat Profile of Hezbollah Unit 910
Lebanese Hezbollah operates as the most capable and trusted proxy of the Iranian regime. Within Hezbollah, the External Security Organization, widely known as the Islamic Jihad Organization or Unit 910, serves as the clandestine black operations branch responsible for overseas terrorism.16 Historically led by Imad Mughniyeh and currently overseen by Talal Hamiyah, Unit 910 operates under the direct supervision of Iranian intelligence and the Islamic Revolutionary Guard Corps Quds Force.17
Unit 910 operatives deployed to North America exhibit a highly sophisticated level of intelligence tradecraft. They are typically recruited from the Lebanese diaspora and are highly valued if they possess dual citizenship and authentic Western passports, which facilitate unfettered international travel and border crossing.16 These individuals are rigorously trained to assimilate seamlessly into American society. Handlers instruct operatives to shave their beards, avoid attending mosques, and present a secular lifestyle to evade the behavioral scrutiny of local law enforcement and federal intelligence agencies.16
The operational history of Unit 910 within the United States reveals a deliberate focus on pre operational surveillance of critical infrastructure and law enforcement nodes. The 2017 arrests of Ali Kourani in New York and Samer el-Debek in Michigan exposed the depth of this methodology. Kourani, who explicitly described himself to federal agents as a sleeper operative belonging to Unit 910, conducted extensive reconnaissance on John F. Kennedy International Airport, the Federal Bureau of Investigation headquarters at 26 Federal Plaza, United States Secret Service facilities, and local military armories.18
Similarly, in 2019, the Department of Justice indicted Alexei Saab, a naturalized American citizen who operated as a sleeper agent for over a decade. Saab surveilled numerous structural targets, including the Port Authority Bus Terminal, Grand Central Terminal, and the New York Stock Exchange.19 Furthermore, intelligence indicates that Unit 910 operatives have actively sought to procure and stockpile explosive precursors. One documented case involved a Hezbollah operative in Texas who successfully purchased three hundred pounds of ammonium nitrate.20 The primary objective of Unit 910 is to prepare the operational groundwork over years or decades so that a catastrophic strike can be launched rapidly upon receiving a signal from Tehran.21
3.2. The Threat Profile of IRGC Quds Force Unit 840
While Hezbollah Unit 910 focuses on long term embedding and strict ideological loyalty, the Islamic Revolutionary Guard Corps Quds Force Unit 840 employs a fundamentally different tactical approach. Unit 840 is an elite, covert operational unit specifically responsible for conducting assassinations, kidnappings, and punitive missions against dissidents and foreign targets abroad.22 Under the leadership of figures such as Yazdan Mir, Unit 840 has increasingly adopted a strategy of outsourcing its lethal operations to transnational criminal syndicates.22
This strategic shift toward criminal surrogates is driven by the desire to maintain plausible deniability and insulate the Iranian state from direct diplomatic or military repercussions. By hiring local gang members, drug traffickers, and independent criminals to execute attacks, Iranian intelligence officers shield themselves from direct attribution and mitigate the risk of losing highly trained, ideologically pure assets.25
In Europe, this strategy has manifested through partnerships with organized crime networks. The Swedish Security Service confirmed that Iran uses criminal networks, specifically the Foxtrot network led by Rawa Majid, to carry out violent acts against Israeli and Jewish sites.26 Within the United States, federal prosecutors have uncovered similar mechanisms, where Iranian intelligence officers have contracted members of the criminal underworld to surveil and plot the assassination of dissidents.15 This methodology significantly complicates the counterterrorism mission of the Federal Bureau of Investigation, as the perpetrators of the violence may have no ideological connection to radical Islam or the Iranian regime, rendering traditional watchlists and behavioral indicators entirely ineffective.27
| Operational Characteristic | Hezbollah Unit 910 | IRGC Quds Force Unit 840 |
| Asset Profile | Ideologically aligned, dual citizens, deep cover | Transnational criminals, gang affiliates, mercenaries |
| Primary Motivation | Religious and political allegiance | Financial compensation, transactional contracts |
| Operational Timeline | Years or decades of patient embedding | Rapid mobilization upon contract agreement |
| Target Preference | Critical infrastructure, military bases, mass transit | Specific individuals, dissidents, former officials |
| Detection Difficulty | High (due to assimilation and clean records) | High (due to lack of ideological indicators) |
4. The Lone Actor Paradigm and the Austin Texas Incident
Beyond the structured operations of Unit 910 and Unit 840, the convergence of geopolitical escalation and digital propaganda has dramatically increased the risk of lone wolf attacks. Following the launch of Operation Epic Fury, foreign state narratives and emotionally charged calls for retaliation have permeated digital ecosystems. These narratives possess the capacity to activate personal grievances among individuals with no formal ties to terrorist organizations, providing a domestic radicalization pipeline that transforms international events into local violence.12
4.1. The Austin Shooting as a Case Study in Inspired Terrorism
The March 1, 2026, mass shooting in Austin, Texas, serves as a critical case study illustrating this hybrid threat paradigm. Ndiaga Diagne, a fifty three year old naturalized United States citizen originally from Senegal, opened fire at a crowded nightlife venue on Sixth Street, killing three individuals and wounding fourteen others.28 Diagne was subsequently neutralized by local law enforcement officers.
During the attack, Diagne wore a hoodie bearing the phrase Property of Allah over a shirt depicting the Iranian flag.29 While initial investigations by the Joint Terrorism Task Force suggest Diagne was a lone actor without direct communication links or financial ties to Iranian handlers, his social media history revealed deep pro Iranian regime sentiments and a hatred for American and Israeli leadership.28 Authorities noted he had a history of encounters with state agencies regarding mental health episodes.30
4.2. Strategic Implications of Stochastic Violence
The Austin incident highlights the profound danger of inspired terrorism, often referred to as stochastic terrorism. In this model, the sheer volume of geopolitical friction and state sponsored digital rhetoric acts as a catalyst for vulnerable individuals to independently mobilize and execute low complexity, high impact attacks on soft targets.12
This dynamic provides a massive strategic benefit to the Iranian regime. It serves as a force multiplier, generating public fear and political pressure within the United States without requiring any logistical investment, financial transfer, or operational direction from Tehran. Because these actors radicalize rapidly and operate independently of formal organizational structures, they exist in the gap between individuals of concern and those who can be legally charged with criminal conspiracy, making them exceptionally difficult for federal authorities to preempt.13
5. National Geographic Concentration and Strategic Nodes
Iranian intelligence networks and proxy operatives are not distributed evenly across the United States. Instead, they are strategically concentrated in geographic areas that offer distinct logistical, demographic, and operational advantages. Providing a national level assessment of these concentrations is essential for deploying limited counterterrorism and infrastructure protection resources effectively.
5.1. Primary Metropolitan Concentrations
Historical arrest records, unsealed Department of Justice indictments, and intelligence patterns reveal that Hezbollah and Islamic Revolutionary Guard Corps networks heavily favor major metropolitan centers. The vast majority of documented network activity is concentrated in New York City, Washington District of Columbia, Chicago, Los Angeles, Detroit, and Houston.20
These urban environments provide several critical operational benefits. First, they offer the necessary demographic density for operatives to blend into large diaspora populations, providing cover for their activities. Second, these cities feature massive international transit infrastructure, including major airports and seaports, facilitating the movement of personnel, illicit funds, and procured materials. Finally, proximity to global financial centers enables the complex money laundering operations required to fund the broader Axis of Resistance.
5.2. Tactical Dispersion and Evasion Hubs
As federal surveillance capabilities within these primary hubs have intensified over the past two decades, Iranian proxies have demonstrated significant tactical adaptation. Former intelligence officials have noted that, upon realizing the extent of Federal Bureau of Investigation monitoring and the density of Joint Terrorism Task Forces in cities like New York and Detroit, Hezbollah deliberately began placing sleeper operatives in secondary metropolitan areas.20
Specifically, intelligence assessments have identified cities such as Portland in Oregon and Louisville in Kentucky as deliberate evasion hubs.20 These mid sized metropolitan areas provide a lower law enforcement profile, allowing operatives to establish deep roots, integrate into local commercial sectors, and maintain their sleeper status with a substantially reduced risk of detection by federal counterintelligence units.20 This geographic dispersion strategy forces federal agencies to dilute their monitoring resources across a much wider geographic expanse.
5.3. Strategic Infrastructure and Target Selection Methodology
The target selection methodology of Iranian sleeper cells encompasses both symbolic retaliation and systemic economic disruption. In the event of a directed attack, intelligence assessments indicate that operatives would likely prioritize critical infrastructure nodes designed to inflict maximum psychological and economic friction on the American public.
The energy and financial sectors remain prime targets. The cyber physical convergence of modern infrastructure means that physical sabotage by a sleeper cell against a regional power substation or a liquefied natural gas terminal can exponentially amplify the effects of a coordinated Iranian cyberattack.32 Operatives have historically conducted extensive surveillance on major transit hubs, including the Port Authority Bus Terminal and local airports in the New York area.19
Furthermore, the defense industrial base is highly vulnerable. Facilities associated with the research and manufacturing of advanced aerospace systems, munitions, and satellite technologies, particularly those with corporate ties to Israeli defense firms, are assessed as high priority strategic nodes.33 The destruction of these facilities not only provides retaliatory satisfaction but also practically degrades the supply chains supporting the ongoing military operations in the Middle East.
| Metropolitan Area | Strategic Significance | Assessed Threat Vector |
| New York City / Washington DC | High density of government, financial, and symbolic targets. | Unit 910 surveillance; Unit 840 targeted assassinations. |
| Detroit / Chicago | Large diaspora populations facilitating deep cover and logistical support. | Financial laundering; procurement rings; sleeper cell embedding. |
| Houston / Gulf Coast | Concentration of critical energy infrastructure and petrochemical refining. | Physical sabotage of pipelines and energy grids; cyber physical attacks. |
| Portland / Louisville | Lower counterterrorism footprint; tactical evasion hubs. | Long term staging; weapons caching; operational planning. |
| Silicon Valley / California | High concentration of advanced technology and defense contractors. | Cyber espionage; theft of trade secrets; sabotage of defense base.34 |
6. Current Countermeasures and Intelligence Operations
In response to the unprecedented escalation in the Middle East and the corresponding domestic threat environment following Operation Epic Fury, the United States government has mobilized its counterterrorism apparatus. However, these efforts are currently hindered by severe institutional friction, debilitating funding deficits, and recent personnel upheavals within critical intelligence divisions.
6.1. The Posture and Vulnerabilities of the Department of Homeland Security
The Department of Homeland Security is the primary agency responsible for coordinating the national defense against physical and cyber threats. Following previous military engagements with Iran, the Department of Homeland Security promptly issued National Terrorism Advisory System bulletins, explicitly warning the public about the heightened risk of cyberattacks and violence driven by Iranian retaliation.32
Currently, Secretary of Homeland Security Kristi Noem has publicly stated that the department is in direct coordination with federal and local law enforcement partners to monitor and thwart potential threats.35 However, as of early March 2026, the Department of Homeland Security has conspicuously failed to issue an updated National Terrorism Advisory System alert regarding Operation Epic Fury.32 This critical breakdown in public threat communication is directly attributable to a lapse in federal funding caused by a partial government shutdown. The National Terrorism Advisory System website currently displays a notice indicating that it is not being actively managed due to a lack of appropriations.32
This funding crisis extends deeply into the operational capabilities of the Cybersecurity and Infrastructure Security Agency. Tasked with protecting the nation from the exact types of Iranian cyber operations that are currently escalating, the Cybersecurity and Infrastructure Security Agency is operating with sharply reduced staffing levels and has experienced a massive reduction in its workforce over the past year due to administration policy shifts.36 This limitation severely degrades the ability of the federal government to provide timely, actionable cyber threat intelligence to private sector partners operating vulnerable energy grids and financial networks.36
Border security represents an additional layer of severe vulnerability. United States Customs and Border Protection data indicates that over one thousand seven hundred and fifty Iranian nationals illegally crossed into the United States between 2021 and 2024.12 The persistence of unknown got aways traversing the border presents a critical security gap, as counterterrorism officials caution that elite Islamic Revolutionary Guard Corps operatives could easily exploit these illicit pathways to embed themselves within the homeland.12 In response to broader immigration concerns, Immigration and Customs Enforcement has initiated Operation Metro Surge, a massive interior enforcement operation. While officially aimed at undocumented immigrants, the operation acts as a sweeping domestic dragnet with counterterrorism implications, evidenced by the recent arrest of an illegal alien in Minnesota identified as a former member of the Islamic Revolutionary Guard Corps.37
6.2. Federal Bureau of Investigation Counterintelligence Constraints
The Federal Bureau of Investigation serves as the primary domestic intelligence agency tasked with neutralizing foreign operative networks. In the wake of Operation Epic Fury, Director Kash Patel has transitioned the bureau to a definitive war footing. Joint Terrorism Task Forces across all field offices have been instructed to operate continuously on high alert, mobilizing all necessary security assets to monitor Iran associated figures, conduct enhanced surveillance, and disrupt potential proxy retaliation.13 The Department of Justice continues to aggressively pursue unsealed indictments to dismantle Iranian procurement rings and publicly expose state sponsored cyber actors attempting to infiltrate United States networks.38
However, the capacity of the Federal Bureau of Investigation to preemptively dismantle Iranian sleeper cells has been severely compromised by internal administrative turmoil. Just days prior to the commencement of Operation Epic Fury, Director Patel executed the abrupt dismissal of over a dozen senior agents and staff members from CI-12, an elite Washington based counterintelligence unit.39 Unit CI-12 specializes specifically in monitoring espionage threats from foreign adversaries in the Middle East, with a profound, specialized focus on Iran and its proxy networks.39
The dismissals were reportedly retribution for the prior involvement of the agents in investigations regarding the retention of classified documents at the Mar a Lago estate.40 By gutting this highly specialized unit, the bureau lost decades of compounded institutional knowledge and critical human intelligence networks. Agents within CI-12 manage delicate relationships with confidential informants embedded deep within the Iranian American diaspora and local communities. The abrupt termination of these handlers effectively severs these vital intelligence arteries, blinding the Federal Bureau of Investigation to subterranean network movements at the exact moment the threat of Iranian sleeper cell activation is at its absolute zenith.41
7. The Cyber Physical Threat Convergence
The modern asymmetric threat landscape requires an assessment of how Iranian proxies will integrate physical sabotage with cyber warfare. Iranian cyber actors have historically aligned their activity with broader strategic objectives to increase pressure on targets including energy, critical infrastructure, finance, telecommunications, and healthcare.10
The immediate risk window involves a surge in retaliatory operations aimed at psychological effect and political signaling, such as website defacements and distributed denial of service attacks.32 However, Iranian actors actively hunt for vulnerabilities in unpatched internet facing systems and weakly secured operational technology edge devices. A coordinated attack involving a localized physical strike by a sleeper cell on a power substation, paired simultaneously with a destructive wiper malware attack on the regional energy grid software, would create catastrophic cascading economic effects and immediate public anxiety.32 Given the degraded posture of the Cybersecurity and Infrastructure Security Agency, private sector entities must rapidly fortify their network architecture against this blended threat methodology.
8. Strategic Conclusion and Threat Trajectory
The United States homeland currently faces an unprecedented convergence of threat vectors. The prosecution of Operation Epic Fury has pushed the Iranian regime to the brink of collapse, stripping away the geopolitical constraints that previously held its vast network of global sleeper cells in check. The probability that Hezbollah Unit 910 operatives, or criminal syndicates contracted by the Islamic Revolutionary Guard Corps Unit 840, will attempt retaliatory strikes on American soil is exceptionally high.
These networks are not abstract concepts; they are well entrenched, geographically dispersed across major metropolitan centers and secondary evasion hubs, and highly trained in modern tradecraft. They possess the capability to execute complex cyber physical attacks against critical infrastructure or launch targeted kinetic operations against high profile individuals. Concurrently, the proliferation of state sponsored digital propaganda guarantees an elevated risk of lone wolf violence, as tragically evidenced by the events in Austin, Texas.
The ability of the United States to detect and preempt these threats is currently in a state of perilous fragility. The ongoing government shutdown has crippled the public advisory systems of the Department of Homeland Security and degraded the defensive posture of the Cybersecurity and Infrastructure Security Agency. Simultaneously, political retaliation within the Federal Bureau of Investigation has decimated the specific counterintelligence unit tasked with monitoring Iranian espionage. To mitigate the impending risk, it is imperative that federal agencies rapidly restore funding to cybersecurity infrastructure, immediately reconstitute human intelligence networks within the Iranian diaspora, and foster seamless, real time intelligence integration with local law enforcement to harden soft targets and secure strategic nodes across the nation.
Appendix: Analytical Methodology
The findings in this report were generated utilizing a combination of established structured analytic techniques, primarily relying on the CARVER Matrix methodology and the Analysis of Competing Hypotheses framework.
The CARVER Matrix, which evaluates targets based on Criticality, Accessibility, Recuperability, Vulnerability, Effect, and Recognizability, was employed to assess the likely target selection priorities of Iranian sleeper cells within the United States. Originally developed by the United States military for special operations targeting, CARVER is highly effective for evaluating domestic vulnerabilities.42 By applying this matrix to the known modus operandi of Hezbollah Unit 910 and Islamic Revolutionary Guard Corps Unit 840, analysts can quantitatively estimate which critical infrastructure nodes present the highest strategic value to an adversary seeking asymmetric retaliation.43 This methodology underpins the assessment that operatives will prioritize targets that yield compounding economic friction and psychological impact over purely symbolic violence.
Simultaneously, the Analysis of Competing Hypotheses was utilized to evaluate the nature of recent domestic incidents, specifically the March 2026 shooting in Austin, Texas. Analysis of Competing Hypotheses requires analysts to identify all possible alternative explanations for an event, such as a directed proxy attack, inspired lone wolf terrorism, or unrelated criminal violence, and subsequently evaluate the available intelligence to disconfirm, rather than confirm, these hypotheses.44 By systematically applying the evidence surrounding the shooter profile, tactical execution, and digital footprint, the Analysis of Competing Hypotheses framework determined that the Austin incident most strongly aligns with an inspired, lone actor mobilization exacerbated by geopolitical tension, rather than a directed operation by a formalized sleeper cell. This structured methodology mitigates cognitive bias and ensures that threat assessments remain grounded strictly in the available evidentiary record.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Sources Used
- Defense Update: Operation Epic Fury – https://defense-update.com/20260303_epic-fury.html
- The White House: Peace Through Strength – https://www.whitehouse.gov/articles/2026/03/peace-through-strength-president-trump-launches-operation-epic-fury-to-crush-iranian-regime-end-nuclear-threat/
- Aerospace Global News: Operation Epic Fury US Israel Air Campaign Iran – https://aerospaceglobalnews.com/news/operation-epic-fury-us-israel-air-campaign-iran/
- Iran International: US, Israel Launch Major Combat Operations in Iran – https://www.iranintl.com/en/202603016611
- DebugLies: Iran in Transition: Strategic Intelligence Assessment – https://debuglies.com/2026/03/01/iran-in-transition-strategic-intelligence-assessment-post-khamenei-succession-crisis-retaliatory-doctrine-regional-escalation-calculus/
- FDD Action: Operation Epic Fury: Battle Damage Assessment – https://www.fddaction.org/secure-line-readout/2026/03/02/operation-epic-fury-battle-damage-assessment-and-strategic-outlook/
- HS Today: Iran Responds to Operation Epic Fury – https://www.hstoday.us/subject-matter-areas/counterterrorism/iran-responds-to-operation-epic-fury-with-layered-military-cyber-and-proxy-strategy-amid-escalation-constraints/
- CBS News: Israel, US Attack Iran; Trump Says Major Combat Operations – https://www.cbsnews.com/live-updates/israel-us-attack-iran-trump-says-major-combat-operations/
- CloudSEK: Middle East Escalation: Israel, Iran, US Cyber War 2026 – https://www.cloudsek.com/blog/middle-east-escalation-israel-iran-us-cyber-war-2026
- Industrial Cyber: US-Israeli Campaign Triggers Iranian Counteroffensive – https://industrialcyber.co/industrial-cyber-attacks/us-israeli-campaign-triggers-iranian-counteroffensive-targeting-gulf-energy-critical-infrastructure/
- Middle East Forum: Iran Strike Scenarios: Retaliation, Transition, and the Path Forward – https://www.meforum.org/mef-reports/iran-strike-scenarios-retaliation-transition-and-the-path-forward
- HS Today: Escalating Risks of Iranian Retaliation on American Soil – https://www.hstoday.us/subject-matter-areas/counterterrorism/escalating-risks-of-iranian-retaliation-on-american-soil-following-epic-fury-campaign/
- The Economic Times: America is not just fighting the Iran war in the Gulf – https://m.economictimes.com/news/defence/america-is-not-just-fighting-the-iran-war-in-the-gulf/articleshow/129017775.cms
- The Soufan Center: IntelBrief: Western Nations Condemn Iranian Intelligence Operations – https://thesoufancenter.org/intelbrief-2025-august-15/
- GWU Extremism Tracker: Propaganda, Procurement, and Lethal Operations – https://extremism.gwu.edu/propaganda-procurement-and-lethal-operations-irans-activities-inside-america
- Grey Dynamics: Unit 910: Hezbollah’s Covert Action Unit – https://greydynamics.com/unit-910-hezbollahs-covert-action-unit/
- Wikipedia: Unit 910 – https://en.wikipedia.org/wiki/Unit_910
- Washington Institute: Inside Hezbollah’s American Sleeper Cells – https://www.washingtoninstitute.org/policy-analysis/inside-hezbollahs-american-sleeper-cells-waiting-irans-signal-strike-us-and-israeli
- Taylor & Francis Online: Hezbollah’s Operations and Networks in the United States – https://www.tandfonline.com/doi/full/10.1080/1057610X.2020.1759487
- Combating Terrorism Center at West Point: Tehran’s Homeland Option – https://ctc.westpoint.edu/tehrans-homeland-option-terror-pathways-for-iran-to-strike-in-the-united-states/
- Washington Institute: Hezbollah Isn’t Just in Beirut, It’s in New York, Too – https://www.washingtoninstitute.org/policy-analysis/hezbollah-isnt-just-beirut-its-new-york-too
- Wikipedia: Unit 840 – https://en.wikipedia.org/wiki/Unit_840
- Iran International: Sanctions Target IRGC Quds Force Unit 840 – https://www.iranintl.com/en/202602035806
- Washington Institute: Iranian External Operations in Europe: The Criminal Connection – https://www.washingtoninstitute.org/policy-analysis/iranian-external-operations-europe-criminal-connection
- ICCT: Iranian External Operations in Europe: The Criminal Connection – https://icct.nl/publication/iranian-external-operations-europe-criminal-connection
- Wikipedia: Iranian External Operations – https://en.wikipedia.org/wiki/Iranian_external_operations
- HS Today: U.S.-Israel Attacks on Iran Fuel Complex Domestic Radicalization – https://www.hstoday.us/subject-matter-areas/counterterrorism/u-s-israel-attacks-on-iran-fuel-complex-domestic-radicalization-and-counterterrorism-challenges/
- The Guardian: Austin bar shooting investigated as potential terrorism – https://www.theguardian.com/us-news/2026/mar/02/austin-bar-shooting-investigation-potential-terrorism
- TIME: Austin Shooting Suspect and Potential Terrorism Investigation – https://time.com/7382024/austin-shooting-suspect-victims-investigation-reactions-potential-terrorism-iran-shirt/
- Washington Post: Authorities investigate if Austin bar shooter was motivated by Iran campaign – https://www.washingtonpost.com/national-security/2026/03/01/iran-attack-austin-bar-shooting/
- GWU Extremism Tracker: Hezbollah’s Operations and Networks in the United States -(https://extremism.gwu.edu/sites/g/files/zaxdzs5746/files/Hezbollah’s_Operations_and_Networks_in_the_United_States_June30_2022.pdf)
- HS Today: Iran Strike Operation Epic Fury Underway – https://www.hstoday.us/perspective/iran-strike-operation-epic-fury-underway-why-has-dhs-not-issued-an-ntas-alert/
- CISA: Iranian Cyber Actors May Target Vulnerable US Networks – https://www.cisa.gov/resources-tools/resources/iranian-cyber-actors-may-target-vulnerable-us-networks-and-entities-interest
- Iran International: Silicon Valley Engineers Charged with Stealing Trade Secrets – https://www.iranintl.com/en/202602208661
- CTV News: Intelligence assessment warns of Iranian attacks on US following Khamenei’s death – https://www.ctvnews.ca/world/mideast-conflict/article/intelligence-assessment-warns-of-iranian-attacks-on-us-following-khameneis-death/
- GovTech: Iran Strikes May Test U.S. Cybersecurity Strategy Abroad – https://www.govtech.com/security/iran-strikes-may-test-u-s-cybersecurity-strategy-abroad
- Center for Immigration Studies: Operation Midnight Hammer and the Threat of Iranian Sleeper Cells -(https://cis.org/Arthur/Operation-Midnight-Hammer-and-Threat-Iranian-Sleeper-Cells)
- Department of Justice: Three IRGC Cyber Actors Indicted – https://www.justice.gov/archives/opa/pr/three-irgc-cyber-actors-indicted-hack-and-leak-operation-designed-influence-2024-us
- MS Now: Kash Patel’s latest firings ousted agents with expertise in Iran – https://www.ms.now/news/kash-patels-latest-firings-ousted-agents-with-expertise-in-iran
- The Independent: Patel fired key members of FBI spy group that monitors Iran threats – https://www.the-independent.com/news/world/americas/us-politics/kash-patel-fbi-firings-agents-iran-b2931141.html
- CBS News: Most of the FBI agents fired by Kash Patel worked on counterintelligence – https://www.cbsnews.com/news/fbi-agents-patel-fired-counterintelligence-including-iran/
- Special Eurasia: CARVER Matrix in Intelligence – https://www.specialeurasia.com/2026/01/06/carver-matrix-intelligence/
- SMI Consultancy: CARVER Target Analysis – https://www.smiconsultancy.com/carver-target-analysis
- CIA: Tradecraft Primer: Structured Analytic Techniques -(https://www.cia.gov/resources/csi/static/Tradecraft-Primer-apr09.pdf)
Works cited
- OPERATION EPIC FURY / ROARING LION – Defense Update:, accessed March 4, 2026, https://defense-update.com/20260303_epic-fury.html
- Peace Through Strength: President Trump Launches Operation Epic Fury to Crush Iranian Regime, End Nuclear Threat – The White House, accessed March 4, 2026, https://www.whitehouse.gov/articles/2026/03/peace-through-strength-president-trump-launches-operation-epic-fury-to-crush-iranian-regime-end-nuclear-threat/
- Operation Epic Fury: How the US & Israeli attack on Iran unfolded – Aerospace Global News, accessed March 4, 2026, https://aerospaceglobalnews.com/news/operation-epic-fury-us-israel-air-campaign-iran/
- Iran sleeper cell fears rise after Austin shooting, Canada gym attack | Iran International, accessed March 4, 2026, https://www.iranintl.com/en/202603016611
- IRAN IN TRANSITION: STRATEGIC INTELLIGENCE ASSESSMENT – Post-Khamenei Succession Crisis, Retaliatory Doctrine & Regional Escalation Calculus – https://debuglies.com, accessed March 4, 2026, https://debuglies.com/2026/03/01/iran-in-transition-strategic-intelligence-assessment-post-khamenei-succession-crisis-retaliatory-doctrine-regional-escalation-calculus/
- Operation Epic Fury: Battle Damage Assessment and Strategic Outlook – FDD Action, accessed March 4, 2026, https://www.fddaction.org/secure-line-readout/2026/03/02/operation-epic-fury-battle-damage-assessment-and-strategic-outlook/
- Iran Responds to Operation Epic Fury with Layered Military, Cyber, and Proxy Strategy Amid Escalation Constraints – HSToday, accessed March 4, 2026, https://www.hstoday.us/subject-matter-areas/counterterrorism/iran-responds-to-operation-epic-fury-with-layered-military-cyber-and-proxy-strategy-amid-escalation-constraints/
- U.S. and Israel launch another round of strikes on Iran following Khamenei’s killing – CBS News, accessed March 4, 2026, https://www.cbsnews.com/live-updates/israel-us-attack-iran-trump-says-major-combat-operations/
- Situation Report: Middle East Escalation (February 27–1st March, 2026) | CloudSEK, accessed March 4, 2026, https://www.cloudsek.com/blog/middle-east-escalation-israel-iran-us-cyber-war-2026
- US-Israeli campaign triggers Iranian counteroffensive targeting Gulf energy, critical infrastructure – Industrial Cyber, accessed March 4, 2026, https://industrialcyber.co/industrial-cyber-attacks/us-israeli-campaign-triggers-iranian-counteroffensive-targeting-gulf-energy-critical-infrastructure/
- Iran Strike Scenarios: Retaliation, Transition, and the Path Forward – Middle East Forum, accessed March 4, 2026, https://www.meforum.org/mef-reports/iran-strike-scenarios-retaliation-transition-and-the-path-forward
- Escalating Risks of Iranian Retaliation on American Soil Following Epic Fury Campaign, accessed March 4, 2026, https://www.hstoday.us/subject-matter-areas/counterterrorism/escalating-risks-of-iranian-retaliation-on-american-soil-following-epic-fury-campaign/
- America is not just fighting the Iran war in the Gulf, accessed March 4, 2026, https://m.economictimes.com/news/defence/america-is-not-just-fighting-the-iran-war-in-the-gulf/articleshow/129017775.cms
- Could Iran Seek to Attack the U.S. Homeland? – The Soufan Center, accessed March 4, 2026, https://thesoufancenter.org/intelbrief-2025-august-15/
- Propaganda, Procurement and Lethal Operations: Iran’s Activities Inside America | Program on Extremism | The George Washington University, accessed March 4, 2026, https://extremism.gwu.edu/propaganda-procurement-and-lethal-operations-irans-activities-inside-america
- Unit 910: Hezbollah´s Covert Action Unit – Grey Dynamics, accessed March 4, 2026, https://greydynamics.com/unit-910-hezbollahs-covert-action-unit/
- Unit 910 – Wikipedia, accessed March 4, 2026, https://en.wikipedia.org/wiki/Unit_910
- Inside Hezbollah’s American Sleeper Cells: Waiting for Iran’s Signal to Strike U.S. and Israeli Targets | The Washington Institute, accessed March 4, 2026, https://www.washingtoninstitute.org/policy-analysis/inside-hezbollahs-american-sleeper-cells-waiting-irans-signal-strike-us-and-israeli
- Iran and Hezbollah’s Pre-Operational Modus Operandi in the West – Taylor & Francis, accessed March 4, 2026, https://www.tandfonline.com/doi/full/10.1080/1057610X.2020.1759487
- Tehran’s Homeland Option: Terror Pathways for Iran to Strike in the United States, accessed March 4, 2026, https://ctc.westpoint.edu/tehrans-homeland-option-terror-pathways-for-iran-to-strike-in-the-united-states/
- Hezbollah Isn’t Just in Beirut. It’s in New York, Too. | The Washington Institute, accessed March 4, 2026, https://www.washingtoninstitute.org/policy-analysis/hezbollah-isnt-just-beirut-its-new-york-too
- Unit 840 – Wikipedia, accessed March 4, 2026, https://en.wikipedia.org/wiki/Unit_840
- Iran says Hatef-3 satellite launch likely by March, tests under way, accessed March 4, 2026, https://www.iranintl.com/en/202602035806
- Iranian External Operations in Europe: The Criminal Connection | The Washington Institute, accessed March 4, 2026, https://www.washingtoninstitute.org/policy-analysis/iranian-external-operations-europe-criminal-connection
- Iranian External Operations in Europe: The Criminal Connection | International Centre for Counter-Terrorism – ICCT, accessed March 4, 2026, https://icct.nl/publication/iranian-external-operations-europe-criminal-connection
- Iranian external operations – Wikipedia, accessed March 4, 2026, https://en.wikipedia.org/wiki/Iranian_external_operations
- U.S.–Israel Attacks on Iran Fuel Complex Domestic Radicalization and Counterterrorism Challenges, accessed March 4, 2026, https://www.hstoday.us/subject-matter-areas/counterterrorism/u-s-israel-attacks-on-iran-fuel-complex-domestic-radicalization-and-counterterrorism-challenges/
- Authorities investigate mass shooting at Austin bar as potential act of terrorism, accessed March 4, 2026, https://www.theguardian.com/us-news/2026/mar/02/austin-bar-shooting-investigation-potential-terrorism
- What to Know About the Shooting in Austin | TIME, accessed March 4, 2026, https://time.com/7382024/austin-shooting-suspect-victims-investigation-reactions-potential-terrorism-iran-shirt/
- FBI probing whether Iran attack motivated Austin shooter who killed 2, accessed March 4, 2026, https://www.washingtonpost.com/national-security/2026/03/01/iran-attack-austin-bar-shooting/
- HEZBOLLAH’S OPERATIONS AND NETWORKS IN THE UNITED STATES: TWO DECADES IN REVIEW – The George Washington University, accessed March 4, 2026, https://extremism.gwu.edu/sites/g/files/zaxdzs5746/files/Hezbollah’s_Operations_and_Networks_in_the_United_States_June30_2022.pdf
- Iran Strike Operation Epic Fury Underway: Why Has DHS Not Issued an NTAS Alert?, accessed March 4, 2026, https://www.hstoday.us/perspective/iran-strike-operation-epic-fury-underway-why-has-dhs-not-issued-an-ntas-alert/
- Iranian Cyber Actors May Target Vulnerable US Networks and Entities of Interest – CISA, accessed March 4, 2026, https://www.cisa.gov/resources-tools/resources/iranian-cyber-actors-may-target-vulnerable-us-networks-and-entities-interest
- Three Iranians in Silicon Valley face US trade secrets charges | Iran International, accessed March 4, 2026, https://www.iranintl.com/en/202602208661
- Intelligence assessment warns of Iranian attacks on U.S. following Khamenei’s death, accessed March 4, 2026, https://www.ctvnews.ca/world/mideast-conflict/article/intelligence-assessment-warns-of-iranian-attacks-on-us-following-khameneis-death/
- Iran Strikes May Test U.S. Cybersecurity Strategy Abroad – GovTech, accessed March 4, 2026, https://www.govtech.com/security/iran-strikes-may-test-u-s-cybersecurity-strategy-abroad
- Operation Midnight Hammer and the Threat of Iranian Sleeper Cells, accessed March 4, 2026, https://cis.org/Arthur/Operation-Midnight-Hammer-and-Threat-Iranian-Sleeper-Cells
- Three IRGC Cyber Actors Indicted for ‘Hack-and-Leak’ Operation Designed to Influence the 2024 U.S. Presidential Election – Justice.gov, accessed March 4, 2026, https://www.justice.gov/archives/opa/pr/three-irgc-cyber-actors-indicted-hack-and-leak-operation-designed-influence-2024-us
- Kash Patel’s latest firings ousted agents with expertise in Iran, accessed March 4, 2026, https://www.ms.now/news/kash-patels-latest-firings-ousted-agents-with-expertise-in-iran
- Patel fired key members of FBI spy group that monitors Iran threats days before Trump launched attacks: report, accessed March 4, 2026, https://www.the-independent.com/news/world/americas/us-politics/kash-patel-fbi-firings-agents-iran-b2931141.html
- FBI agents fired by Patel worked in counterintelligence, including on cases involving Iran, sources say, accessed March 4, 2026, https://www.cbsnews.com/news/fbi-agents-patel-fired-counterintelligence-including-iran/
- The CARVER Matrix in Strategic Targeting and Intelligence Assessment – SpecialEurasia, accessed March 4, 2026, https://www.specialeurasia.com/2026/01/06/carver-matrix-intelligence/
- The Fundamentals of CARVER Target Analysis and Vulnerability Assessment Methodology, accessed March 4, 2026, https://www.smiconsultancy.com/carver-target-analysis
- A Tradecraft Primer: Structured Analytic Techniques for Improving Intelligence Analysis Prepared by the US Government March 2009 – CIA, accessed March 4, 2026, https://www.cia.gov/resources/csi/static/Tradecraft-Primer-apr09.pdf
