Executive Summary
The history of military innovation is often viewed through the lens of technological advancement—the longbow, the tank, the atomic bomb. However, the most profound revolutions in warfare are frequently organizational and conceptual. The F3EAD targeting cycle—Find, Fix, Finish, Exploit, Analyze, and Disseminate—represents one such revolution. Emerging from the chaotic, high-pressure crucible of counter-insurgency (COIN) operations in Iraq and Afghanistan, F3EAD fundamentally altered the operational rhythm of the United States military and its allies. It marked a decisive shift from the linear, attrition-based models of 20th-century industrial warfare to a dynamic, intelligence-driven ecosystem designed to dismantle clandestine networks at a velocity that exceeds their ability to regenerate.
This comprehensive report provides an exhaustive examination of the F3EAD cycle. It traces its inception within the Joint Special Operations Command (JSOC) under the leadership of General Stanley McChrystal, analyzing the specific operational failures that necessitated its creation and the organizational transformations required to implement it. The report dissects the intricate mechanics of each phase, arguing that the true innovation of F3EAD lies not in the kinetic “Finish,” but in the elevation of “Exploitation” and “Analysis” to the status of main effort. By transforming every tactical action into a strategic intelligence-gathering opportunity, F3EAD creates a self-sustaining feedback loop of target generation that collapses the traditional silos between operations and intelligence.
Furthermore, this analysis extends beyond the battlefield of the Global War on Terror (GWOT). It explores the adaptation of the F3EAD methodology across diverse domains, including domestic law enforcement, where it informs strategies for policing violent criminal networks, and the cyber domain, where it serves as a foundational framework for Cyber Threat Intelligence (CTI) and offensive operations.
Finally, the report offers a critical evaluation of the strategic paradoxes inherent in this model. It addresses the criticism that F3EAD encourages a “tactical perfection, strategic failure” dynamic, where efficient targeting masks the lack of progress toward broader political objectives. It also assesses the viability of F3EAD in an era of Great Power Competition (GPC), examining how the cycle must evolve to function against peer adversaries capable of contesting the electromagnetic and physical domains upon which the methodology relies.
1. The Crucible of Inception: From Industrial to Networked Warfare
To understand the mechanics of F3EAD, one must first understand the operational crisis that birthed it. The initial phases of Operation Iraqi Freedom in 2003 were characterized by a conventional military dominance that shattered the Iraqi state’s formal army. However, as the conflict transitioned into an insurgency, the Coalition forces found themselves facing an adversary—Abu Musab al-Zarqawi and Al-Qaeda in Iraq (AQI)—that operated on fundamentally different principles than the state-based foes the US military was designed to defeat.1
1.1 The Intelligence Gap and the Crisis of Efficiency
In the early years of the conflict, the US military machine was, by all industrial metrics, efficient. It possessed overwhelming firepower, superior logistics, and advanced technology. Yet, it was losing. The problem was not a lack of capability but a disparity in organizational adaptability. The US military operated as a hierarchy: a rigid, top-down structure designed for the slow, deliberate maneuvering of large formations. Intelligence collection was a stovepiped process where agencies like the National Security Agency (NSA), Central Intelligence Agency (CIA), and Defense Intelligence Agency (DIA) collected data in isolation. This data was then sent to headquarters for analysis—a process that could take days or weeks—before being disseminated to the operators on the ground in the form of a target package.
Against a decentralized, networked enemy like AQI, this latency was fatal. AQI operated as a “scale-free” network, a constellation of semi-autonomous cells connected by key hubs but capable of independent action. They could plan, execute, and disperse in the time it took a conventional US unit to request permission to move. General Stanley McChrystal, upon taking command of JSOC, famously observed that while his forces won every individual firefight, they were losing the war because they could not dismantle the network faster than it could regenerate.1 The enemy’s decision cycle—the OODA loop (Observe, Orient, Decide, Act)—was turning faster than the Coalition’s.
1.2 Task Force 714 and the Transformation of Targeting
The solution was not better weapons, but a fundamental restructuring of the relationship between operations and intelligence. This transformation, centered on Task Force 714 (TF714), sought to create a “network to defeat a network”.3 The objective was to increase the velocity of the targeting cycle to a point where the insurgency could no longer adapt.
This required two radical shifts in doctrine:
- The Fusion of Ops and Intel: Historically, the intelligence community (IC) and the special operations community were distinct tribes. Intelligence professionals produced “products” for operators to execute. Under the nascent F3EAD model, intelligence analysts were embedded directly with assault forces. This created “operational intimacy,” where the analyst who identified the target was often physically present or directly connected to the team conducting the raid. This proximity allowed for real-time updates and ensured that the nuances of the intelligence—the “why”—were understood by the “who” executing the mission.3
- The “Unblinking Eye”: The transformation demanded persistent Intelligence, Surveillance, and Reconnaissance (ISR) coverage. By fusing signals intelligence (SIGINT) from the NSA with continuous drone video feeds, TF714 could maintain a “pattern of life” on targets. This allowed the force to move from “finding” a target to “fixing” them with unprecedented precision, shifting from broad area search to specific, individualized targeting.3
The implementation of F3EAD resulted in a dramatic, almost exponential increase in operational tempo. In August 2004, TF714 executed approximately 18 raids a month. By fully implementing the F3EAD cycle and fusing interagency capabilities, this number skyrocketed to over 300 raids per month by August 2006.4 This was not merely an increase in volume; it was an increase in systemic pressure. The high tempo allowed the Task Force to reach inside AQI’s decision loop, hitting targets faster than the insurgents could vet new leaders, secure their communications, or move their logistics. The network, unable to cope with the speed of its own dismantling, eventually began to “collapse in upon itself”.4
2. Anatomy of the Cycle: Operational Mechanics
The F3EAD cycle is distinct from previous targeting methodologies (such as the traditional Intelligence Cycle or the D3A model) because of its circularity and its emphasis on the post-kinetic phases. In traditional warfare, the mission often ends when the target is destroyed. In F3EAD, the “Finish” is merely a collection opportunity designed to drive the next cycle. The cycle operates as a continuous engine: the output of one operation (Exploitation and Analysis) becomes the direct input for the next (Find).
2.1 Phase 1: FIND – The Intelligence Funnel
The Find phase creates the starting point for intelligence collection. It is the identification of a potential target—a person, a facility, or a digital node—that fits within the commander’s intent and priority intelligence requirements (PIRs). This phase is a multi-discipline hunt that functions as a funnel, narrowing the vast noise of the battlefield into specific, actionable leads.6
The targeting process in this phase is governed by strict methodology to ensure resources are focused on the most impactful nodes of the enemy network. Operators often employ the CARVER matrix to score potential targets:
- Criticality: How essential is this target to the enemy’s operations?
- Accessibility: Can the target be reached with available forces?
- Recuperability: How long will it take the enemy to replace or repair this target?
- Vulnerability: Is the target susceptible to the available attack methods?
- Effect: What are the cascading strategic or operational effects of neutralizing this target?
- Recognizability: Can the target be identified clearly to avoid collateral error? 8
The “Find” is generated through the fusion of multiple intelligence disciplines:
- HUMINT (Human Intelligence): Source reports, debriefings of detainees, and local informants provide the contextual “seed” information—a name, a meeting place, or a courier route.
- SIGINT (Signals Intelligence): The interception of communications and the analysis of metadata are crucial for mapping the social network of the adversary. This might involve contact chaining (who calls whom) to identify the central nodes in a terrorist cell.9
- Financial Intelligence: Following money trails is often a more durable way to identify logistics nodes than tracking individuals, who may be interchangeable.8
The output of the Find phase is a “candidate target” or a “lead.” It moves a specific entity from the background noise into the active targeting queue, initiating the rigorous process of verification.8
2.2 Phase 2: FIX – Verification and Pattern of Life
The Fix phase is the rigorous verification of the target. It answers the critical operational questions: “Is this the right target?” and “Is this the right time?”.6 In counter-insurgency and precision operations, the cost of error—striking the wrong house or detaining the wrong person—is strategically catastrophic. Therefore, the Fix phase is an exercise in risk reduction.
- Pattern of Life (POL) Analysis: This is the most critical component of fixing a target. Analysts track the target over time to establish routines, identify bed-down locations (BDLs), and map associations. This requires “stacking” assets—for example, using a drone (GEOINT) to watch a house while SIGINT monitors the active handsets inside to confirm the target’s presence. POL analysis allows commanders to predict when the target will be isolated and vulnerable.8
- Triangulation: A single data point is rarely sufficient for a lethal finish. The Fix phase requires triangulation from multiple independent sources. A standard of “dual-verification” might be required: a HUMINT source confirms the target is in the building, and SIGINT geolocates his phone to the same coordinate. This cross-referencing minimizes the risk of deception or error.6
- The Window of Opportunity: The ultimate goal of the Fix phase is to determine the precise window where the target is vulnerable and collateral damage can be minimized. This phase transforms a “suspect” into a clear, actionable “target,” effectively locking the crosshairs onto the objective.7
2.3 Phase 3: FINISH – The Kinetic and Non-Kinetic Intervention
The Finish phase is the execution of the operation. While often associated with lethal force, such as a drone strike or a Special Operations raid, the “finish” can take many forms depending on the operational objective and the domain.6
- Kinetic Operations: In a counter-terrorism context, this often involves a raid by SOF or a precision air strike. The primary goal is to neutralize the threat. However, in the F3EAD model, the preference is often for a raid over an airstrike because a raid allows for the capture of the individual and the seizure of materials—enabling the subsequent “Exploit” phase.7
- Non-Lethal Operations: In law enforcement or stability operations, the “finish” is an arrest or detention. In cyber operations, it might be the isolation of an infected host, the patching of a vulnerability, or the blocking of a malicious IP address.6
- Evidence Preservation: Crucially, in the F3EAD model, the finish force is not merely an execution squad; they are intelligence collectors. The assault force is trained to conduct “Tactical Site Exploitation” (TSE) immediately upon securing the objective. This involves securing hard drives, phones, paper documents, and pocket litter before they can be destroyed or contaminated. The “Finish” is not the end of the operation; it is the beginning of the intelligence harvest.11
2.4 Phase 4: EXPLOIT – The Engine of the Cycle
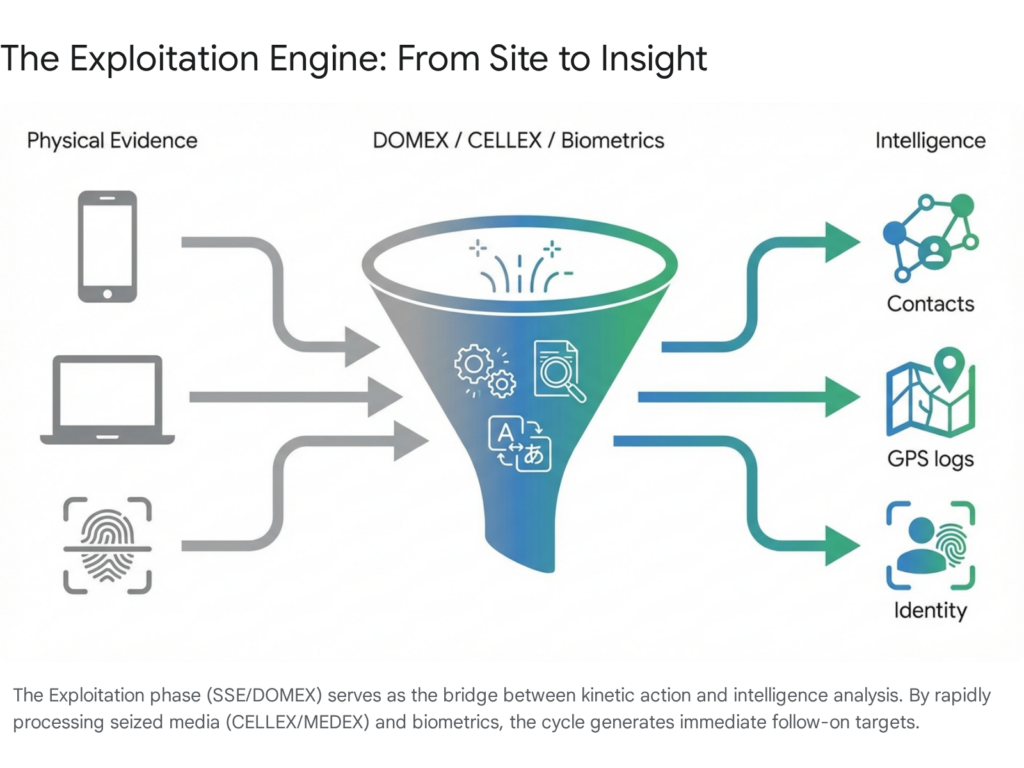
This phase is arguably the Main Effort of the F3EAD cycle.7 It is the differentiator that separates F3EAD from attrition-based models. The objective is to extract every possible grain of information from the materials and persons secured during the Finish phase.
- Sensitive Site Exploitation (SSE): This involves the forensic recovery of material from the target location. It includes “pocket litter” (receipts, notes), computers, cell phones, maps, and biometric data (fingerprints, iris scans, DNA). In the context of TF714, this capability was pushed to the tactical edge, with operators carrying handheld scanners and forensic kits.13
- DOMEX (Document and Media Exploitation): Captured digital devices are often intelligence goldmines. A single captured laptop can contain the names, locations, emails, and plans of hundreds of other operatives. The speed at which this media is processed is critical. “Flash” exploitation is performed on-site or at the forward base to identify immediate threats or fleeting opportunities (e.g., “The target is meeting his financier in one hour”).8
- Tactical Questioning and Interrogation: Immediate debriefing of detainees can yield perishable intelligence. This “human exploitation” complements the technical data, providing context to the digital files.11
- The “Dirty” to “Clean” Pipeline: A major challenge in this phase is the rapid processing of raw material (“dirty intel”) into usable information (“clean intel”). This requires a robust technical infrastructure to translate documents, decrypt files, and upload data into the centralized intelligence database accessible to analysts worldwide.8
2.5 Phase 5: ANALYZE – Fusion and Sense-Making
The Analyze phase fuses the raw data extracted during the Exploit phase with the broader intelligence picture to create new targeting leads.6 This is where the dots are connected.
- Link Analysis: Analysts use advanced software to visualize connections between the newly captured data and existing databases. If a captured phone contains a number that was also seen on a phone captured two weeks ago in a different city, a link is established. This network analysis can reveal the hidden hierarchy of the insurgency, identifying couriers, financiers, and commanders who do not participate in direct combat.10
- All-Source Fusion: This phase brings together experts from all disciplines (SIGINT, GEOINT, HUMINT). They assess the credibility of the new intel, cross-reference it with other reporting, and determine its significance. This fusion prevents “single-source” errors and builds a comprehensive picture of the adversary’s intent and capability.
- Targeting Packets: The output of analysis is not just a report for the archives; it is a new “Find.” The analysis identifies the next target, creating a new lead that restarts the cycle. In a high-tempo environment, the analysis phase for one target is often the find phase for the next three.15
2.6 Phase 6: DISSEMINATE – Closing the Loop
The final phase, Disseminate, ensures that the processed intelligence reaches the right people at the right time to enable action.
- Flattening the Hierarchy: In the JSOC model, dissemination was not a slow climb up the chain of command to be approved and then passed down. Intelligence was pushed laterally to everyone who needed it. A finding by an analyst in Washington D.C. could be pushed directly to a platoon leader in Baghdad or a pilot in the air.5
- Actionable Intelligence: The goal is to provide intelligence that is immediately usable. This might be a “Be On the Look Out” (BOLO) report for a checkpoint, a new target packet for a strike force, or a strategic assessment for policymakers. The dissemination must be tailored to the consumer—tactical details for the shooter, strategic context for the general.8
- The Feedback Loop: Effective dissemination closes the loop, triggering the “Find” phase for the next operation. It creates a rhythm of operations where each raid generates the intelligence for the next three raids, creating a compounding effect that overwhelms the adversary.5
3. The Organizational Engine: Structure Behind the Speed
The F3EAD cycle is not merely a set of steps; it is an operational culture that requires a specific organizational architecture to function. The hierarchical structures of the Cold War, with their rigid chains of command and siloed information, were incapable of sustaining the velocity F3EAD requires. The successful implementation of the cycle depended on the creation of cross-functional teams and flattened communication structures.
3.1 The Joint Inter-Agency Task Force (JIATF) Model
The structural foundation of F3EAD within JSOC was the Joint Inter-Agency Task Force (JIATF). Championed by Admiral William McRaven and General McChrystal, the JIATF model sought to break down the walls between the various arms of the US government.
- Co-location and Integration: The JIATF brought together previously siloed agencies—CIA, NSA, FBI, NGA, and DIA—into a single physical workspace. By physically placing a SIGINT analyst from the NSA next to a Delta Force operator and a CIA case officer, the friction of distance and bureaucracy was eliminated. Questions that previously took days to answer via official inter-agency memos could now be resolved in seconds over a shoulder tap.3
- Empowerment and Decentralized Execution: These representatives were not just passive liaisons; they were empowered to make decisions and task their parent agencies’ assets. This “decentralized execution” within a “centralized strategy” was key to the model’s success. It allowed the Task Force to bring the full weight of national intelligence capabilities to bear on a tactical problem without the delay of seeking permission from headquarters.3
3.2 The Operations and Intelligence (O&I) Meeting
If the JIATF was the body of the organization, the daily Operations and Intelligence (O&I) meeting was its heartbeat.
- Global Synchronization: Conducted via secure video teleconference, this 90-minute daily forum connected thousands of participants across the globe, from forward operating bases in Iraq and Afghanistan to headquarters in Washington D.C.
- Shared Consciousness: The O&I was not a traditional briefing where subordinates reported to commanders. It was a forum for solving problems in real-time and sharing information laterally. It created a “shared consciousness” where everyone understood the commander’s intent and the current intelligence picture. This allowed disparate units to self-synchronize their actions without waiting for explicit orders, dramatically increasing the speed of the F3EAD cycle.1
- Radical Transparency: General McChrystal used the O&I to force transparency, even when it was uncomfortable. This culture of openness fostered trust between the “tribes” of the special operations and intelligence communities, breaking down the “need to know” culture and replacing it with a “need to share” mindset.17
3.3 Liaison Officers (LNOs) and “Operational Intimacy”
A critical, often overlooked component of the F3EAD engine was the extensive network of Liaison Officers. TF714 embedded LNOs in every relevant partner agency and allied nation.
- Human Connectivity: These LNOs were selected for their charisma, competence, and credibility. Their job was to “grease the wheels” of interagency cooperation, ensuring that when the Task Force needed support (e.g., a specific satellite collecting over a specific house), the request was prioritized by the parent agency.3
- Trust Networks: The LNOs built personal relationships that transcended institutional rivalry. They acted as the connective tissue that knitted the “core” special operations machine to the “periphery” of the broader US government and coalition partners, ensuring that the F3EAD cycle was fed by the widest possible network of sensors and sources.3
4. Comparative Analysis of Targeting Methodologies
To fully appreciate the innovation of F3EAD, it is necessary to compare it with other prevailing military targeting cycles. Each methodology is designed for a specific type of warfare and operational tempo.
4.1 F3EAD vs. D3A (Decide, Detect, Deliver, Assess)
D3A is the standard US Army doctrine for conventional forces. It is primarily a deliberate planning tool designed for optimizing resources over longer timelines.
- Focus: D3A prioritizes the “Decide” phase—the deliberate planning of what to target based on the commander’s objectives and the allocation of limited assets.
- Limitation: It often lacks the agility for the rapid, dynamic retasking required in counter-insurgency. It assumes a more linear progression and is less focused on the immediate exploitation of the strike to generate new targets. It is a “planning-centric” model.12
- Contrast: F3EAD is an execution tool. While D3A is excellent for planning a 72-hour artillery bombardment of fixed positions, F3EAD is superior for a nightly raid cycle where the target list changes every few hours based on new intelligence. F3EAD assumes the plan will change and builds the mechanism to adapt to that change.18
4.2 F3EAD vs. F2T2EA (Find, Fix, Track, Target, Engage, Assess)
F2T2EA is an air-centric model used primarily by the US Air Force for dynamic targeting (e.g., striking a moving convoy or a fleeting target).
- Focus: It emphasizes the “Track” and “Target” phases—maintaining custody of a moving target with sensors and ensuring the strike meets complex legal and Rules of Engagement (ROE) criteria.
- Limitation: The final phase is “Assess” (Battle Damage Assessment—did the bomb hit the target?). The cycle conceptually ends with the kinetic effect.
- Contrast: F3EAD replaces “Assess” with “Exploit, Analyze, Disseminate.” In F2T2EA, the cycle ends with the explosion. In F3EAD, the explosion is just the mechanism to get to the “Exploit” phase (the pocket litter, the phone, the detainee). F3EAD values the intelligence gained from the target more than the physical destruction of the target itself.19

5. Domain Adaptation: Beyond the Battlefield
The success of F3EAD in the high-stakes environment of Iraq and Afghanistan led to its adaptation across other operational domains. Its core logic—rapidly cycling through finding, neutralizing, and learning from threats—has proven universally applicable to adversarial networks, whether they are digital, criminal, or irregular.
5.1 Cyber Warfare: The “Alternative Intelligence Cycle”
In the cyber domain, F3EAD has been adapted for both Cyber Threat Intelligence (CTI) and Offensive Cyberspace Operations (OCO). The speed of cyber warfare makes the traditional intelligence cycle too slow, necessitating the rapid “OODA loop” style of F3EAD.
- Find: Identifying the adversary’s presence. This could be finding malware beacons, anomalous network traffic, or detecting a phishing campaign. This is the “hunting” phase of cybersecurity.6
- Fix: Triangulating the threat to specific infected hosts or verifying the attribution of the actor. This involves digital forensics to confirm that the anomaly is indeed a threat and locating its extent within the network.
- Finish: The “kill” in cyber is often non-lethal—blocking an IP address, isolating an infected host from the network, patching a vulnerability, or seizing a command-and-control server. In offensive operations, it might be the deployment of a cyber effect to disrupt an enemy system.7
- Exploit: This phase is critical in CTI. It involves deconstructing the malware (reverse engineering) to find “Indicators of Compromise” (IOCs) like hardcoded IP addresses, compiler signatures, or specific coding quirks.
- Analyze: Linking these IOCs to known Advanced Persistent Threat (APT) groups. Analysts determine if this attack is part of a broader campaign by a state actor or a criminal enterprise.
- Disseminate: Sharing the signatures with the broader community or pushing updates to firewalls and intrusion detection systems. The speed of F3EAD is perfectly suited to “cyber speed,” where threats propagate in milliseconds.6
5.2 Law Enforcement: “Policing the Power Few”
Domestic law enforcement agencies have adopted F3EAD to combat gang violence and organized crime, shifting from reactive policing to intelligence-led targeting.
- The Logic: Criminological research suggests that a small percentage of offenders (the “Power Few”) commit a disproportionate amount of violent crime. F3EAD allows police to focus resources on these chronic offenders rather than broad, indiscriminate policing strategies that alienate communities.23
- Implementation:
- Find/Fix: Using data analysis (crime mapping, social network analysis) to identify the most violent individuals and tracking their patterns (e.g., social media activity, parole status).
- Finish: Conducting targeted arrests, often for outstanding warrants or parole violations, to remove these specific individuals from the street.
- Exploit/Analyze: Debriefing suspects, analyzing their phones, and mapping their associates to understand the gang hierarchy and solve other open cases.
- Case Studies: Cities like Las Vegas have used this targeted approach to significantly reduce gun-related crime. Similarly, Brazil’s Federal Police have adapted F3EAD to combat transnational organized crime, using the cycle to dismantle complex illicit supply chains and money laundering networks.23
6. Strategic Critiques and Limitations
Despite its tactical brilliance and widespread adoption, F3EAD is not without significant strategic flaws. The very features that make it effective—speed, focus, and efficiency—can become liabilities if not managed with strategic oversight.
6.1 The “Tactical Perfection, Strategic Failure” Paradox
Critics argue that F3EAD encourages a “Whack-a-Mole” mindset. The cycle is so efficient at generating and finishing targets that organizations can become addicted to the “raid.”
- The Trap: Units may focus entirely on dismantling the network (the symptoms) while ignoring the root causes of the insurgency or crime (political grievances, economics, social instability). A unit can execute 300 perfect raids, capture 300 terrorists, and yet the insurgency grows because the underlying drivers remain unaddressed. This is the paradox of “winning every battle but losing the war”.8
- Short-Termism: The cycle rewards short-term disruption. Strategic success, which requires long-term stabilization, governance, and nation-building, is harder to measure and often neglected in favor of the immediate, quantifiable metrics of “captures and kills”.8 The “metrics of effectiveness” become circular: the success of the cycle is measured by the speed of the cycle, rather than the political outcome.
6.2 Legal and Ethical Risks
The compression of the targeting cycle places immense pressure on the legal and ethical frameworks governing the use of force.
- Blurring Lines: F3EAD collapses the distance between the intelligence collector and the lethal operator. While efficient, this can erode the traditional checks and balances designed to ensure independent verification of targets. The “operational intimacy” can lead to groupthink or confirmation bias.8
- Drone Warfare: In “signature strikes” (targeting based on a pattern of life rather than positive identification of a specific individual), the “Fix” phase relies heavily on metadata and algorithms. If the analysis is flawed, the risk of civilian casualties increases. Civilian casualties create strategic blowback that can undermine the entire political mission, providing the enemy with a potent recruiting tool.10
7. The Future Fight: F3EAD in Great Power Competition
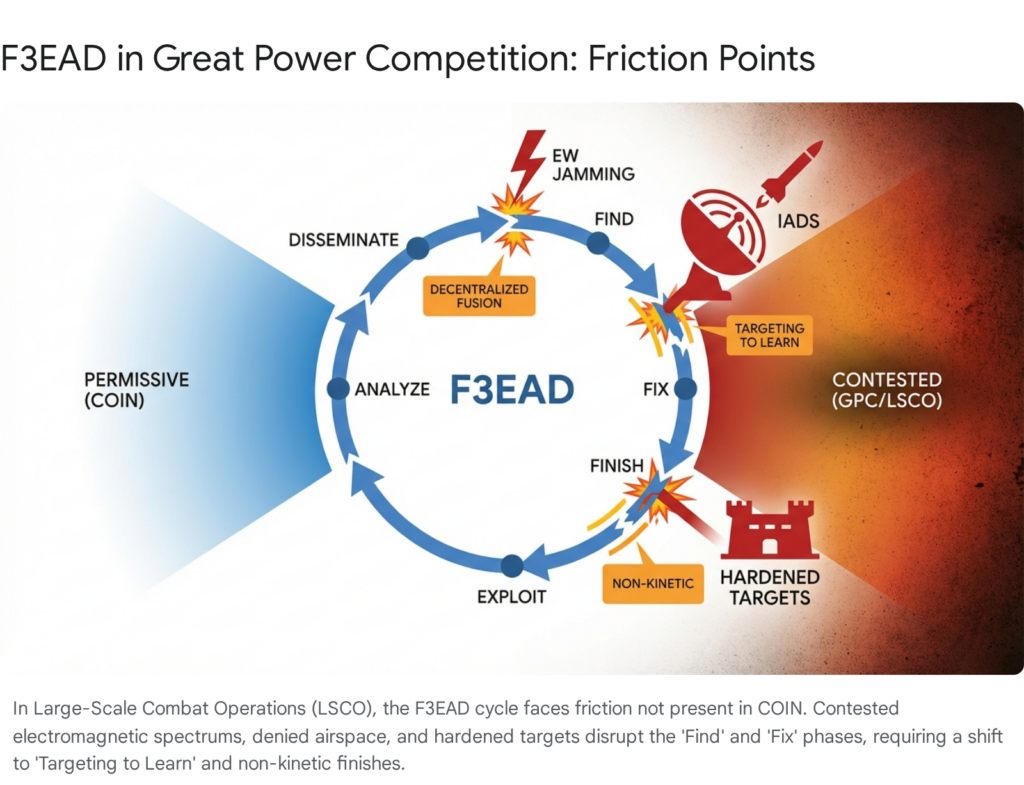
As the US military and its allies shift focus from counter-terrorism to Great Power Competition (GPC) against peer adversaries like China and Russia, the applicability of F3EAD is being vigorously debated. The permissive environments of Iraq and Afghanistan are gone.
7.1 The Challenge of Scale and Survivability
In COIN, US forces enjoyed air supremacy, uncontested electromagnetic dominance, and secure logistics. In a conflict with a peer adversary, these assumptions vanish.
- Contested Domains: A peer adversary will attack the communication networks that F3EAD relies on. If the O&I meeting cannot happen because satellites are jammed, or if the data link between the drone and the analyst is severed, the cycle breaks.7
- Denied Access: “Finding” and “Fixing” a target deep inside enemy territory protected by integrated air defense systems (IADS) is fundamentally harder than tracking a terrorist in a permissive environment. The “unblinking eye” of the drone may be blinded or shot down.
- Logistics: The “Finish” phase in Large Scale Combat Operations (LSCO) may require massed artillery or long-range fires, which are harder to resupply in a contested logistics environment compared to a small SOF team.25
7.2 From “Targeting to Effect” to “Targeting to Learn”
Despite these challenges, the logic of F3EAD remains vital, but the application must shift.
- Targeting to Learn: In GPC, the “Exploit” and “Analyze” phases become even more critical. Targeting may be used not just to destroy a unit, but to force the enemy to reveal their electronic signature, defensive tactics, or command structure. This “targeting to learn” approach uses the cycle to probe the adversary’s system and gain information superiority, rather than just attrition.12
- Disruption and Follow-Through: Doctrine is evolving to include “Disrupt” and “Follow-through” as explicit phases. In LSCO, you may not be able to “Finish” (destroy) an entire enemy division, but you can “Disrupt” its command and control using cyber effects (an F3EAD adaptation), allowing maneuver forces to exploit the confusion. The “Follow-through” ensures that the temporary advantage is seized upon.27
7.3 Adapting the Machine
For F3EAD to survive in LSCO, it must adapt:
- Decentralized Fusion: Fusion cells must operate at lower echelons (Brigade or Battalion) without reliance on reach-back to national headquarters, allowing them to function even if long-haul communications are cut.
- Resilience: The cycle must function with degraded communications (“digital anchor points”) and intermittent data access.7
- Multi-Domain Finishes: The “Finish” is increasingly likely to be non-kinetic (Cyber, Electronic Warfare) to blind the enemy before the kinetic fight begins.7
Conclusion
The F3EAD targeting cycle stands as one of the most significant innovations in modern military tradecraft. By fusing operations and intelligence into a seamless, high-velocity loop, it solved the intractable problem of targeting dynamic, networked adversaries in the Global War on Terror. Its emphasis on Exploitation—treating every engagement as a source of new intelligence rather than just an end in itself—revolutionized how militaries think about the value of a target and the utility of force.
However, as the strategic landscape shifts toward Great Power Competition, F3EAD faces an existential test. The “industrial” efficiency of the counter-terrorism machine must be adapted for a world where the enemy can shoot back, jam the network, and deny the airspace. The future of F3EAD lies not in the rigid application of its steps, but in the preservation of its core philosophy: that in modern warfare, the speed of learning is the ultimate weapon.
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Sources Used
- Gen. Stanley McChrystal: Adapt to Win in the 21st Century, accessed February 9, 2026, https://www.gsb.stanford.edu/insights/gen-stanley-mcchrystal-adapt-win-21st-century
- Rapid and Radical Adaptation in Counterinsurgency: Task Force 714 in Iraq, accessed February 9, 2026, https://mwi.westpoint.edu/rapid-and-radical-adaptation-in-counterinsurgency-task-force-714-in-iraq/
- US Special Forces transformation: post-Fordism and the limits of networked warfare | International Affairs | Oxford Academic, accessed February 9, 2026, https://academic.oup.com/ia/article/98/2/587/6526922
- “The Irreducible Minimum” An Evaluation of Counterterrorism …, accessed February 9, 2026, https://ndupress.ndu.edu/Media/News/News-Article-View/Article/1983604/the-irreducible-minimum-an-evaluation-of-counterterrorism-operations-in-iraq/
- Relentless Strike: The Secret History of Joint Special Operations Command, by Sean Naylor – U.S. Naval War College Digital Commons, accessed February 9, 2026, https://digital-commons.usnwc.edu/cgi/viewcontent.cgi?article=1171&context=nwc-review
- F3EAD: Find, Fix, Finish, Exploit, Analyze and Disseminate – The Alternative Intelligence Cycle – ReliaQuest, accessed February 9, 2026, https://reliaquest.com/blog/f3ead-find-fix-finish-exploit-analyze-and-disseminate-the-alternative-intelligence-cycle/
- Optimizing the Alternate Targeting Methodology F3EAD – Line of Departure – U.S. Army, accessed February 9, 2026, https://www.lineofdeparture.army.mil/Journals/Military-Intelligence/MIPB-January-June-2024/Optimizing-the-Alternate-Targeting-Methodology-F3EAD/
- F3EAD: SOF Specific Targeting in the Intelligence Cycle – SOF Support Foundation, accessed February 9, 2026, https://sofsupport.org/f3ead-sof-specific-targeting-in-the-intelligence-cycle/
- Signals Intelligence (SIGINT) Overview – National Security Agency, accessed February 9, 2026, https://www.nsa.gov/Signals-Intelligence/Overview/
- F3EAD: SOF Specific Targeting in the Intelligence Cycle – Small Wars Journal, accessed February 9, 2026, https://smallwarsjournal.com/2025/12/26/f3ead-targeting-irregular-warfare-lsco/
- Tactical Site Exploitation.pdf – The National Security Archive, accessed February 9, 2026, https://nsarchive2.gwu.edu/NSAEBB/NSAEBB410/docs/Tactical%20Site%20Exploitation.pdf
- F3EA — A Targeting Paradigm for Contemporary Warfare | Australian Army Research Centre (AARC), accessed February 9, 2026, https://researchcentre.army.gov.au/library/australian-army-journal-aaj/volume-10-number-1-autumn/f3ea-targeting-paradigm-contemporary-warfare
- pm – sensitive site exploitation (sse), accessed February 9, 2026, https://ndia.dtic.mil/wp-content/uploads/2022/sofic/Tues_PM-SSE.pdf
- Why Site Exploitation – Marine Corps Association, accessed February 9, 2026, https://www.mca-marines.org/wp-content/uploads/35-Why-Site-Exploitation.pdf
- accessed February 9, 2026, https://sofsupport.org/f3ead-sof-specific-targeting-in-the-intelligence-cycle/#:~:text=F3EAD%3A%20Find%2C%20Fix%2C%20Finish,intelligence%20into%20a%20flexible%20workflow.
- Lessons from a Four-Star General – Auror, accessed February 9, 2026, https://www.auror.co/the-intel/lessons-from-a-four-star-general
- Understanding Team of Teams Phases for Leadership Success, accessed February 9, 2026, https://www.mcchrystalgroup.com/insights/detail/2025/07/08/from-detractor-to-advocate–a-leadership-journey-through-team-of-teams
- The Targeting Process: D3A and F3EAD | Small Wars Journal by Arizona State University, accessed February 9, 2026, https://smallwarsjournal.com/2011/07/16/the-targeting-process-d3a-and-f3ead/
- (PDF) The Targeting Process: D3A and F3EAD – ResearchGate, accessed February 9, 2026, https://www.researchgate.net/publication/235084400_The_Targeting_Process_D3A_and_F3EAD
- Army Targeting – DigitalCommons@UNL, accessed February 9, 2026, https://digitalcommons.unl.edu/cgi/viewcontent.cgi?article=1032&context=usarmyfieldmanuals
- F3EAD Cycle in Cyber Threat Intelligence | by Chad Warner – Medium, accessed February 9, 2026, https://warnerchad.medium.com/f3ead-cycle-for-cti-e15a42194faa
- Methods and Methodology / Cyber Threat Intelligence SIG Curriculum, accessed February 9, 2026, https://www.first.org/global/sigs/cti/curriculum/methods-methodology
- Re-imagining Policing: Using the JSOC/CIA F3EAD Model to Lower …, accessed February 9, 2026, https://mtntactical.com/knowledge/re-imagining-policing-using-the-jsoc-cia-f3ead-model-to-lower-crime/
- Leveraging Intelligence to Optimize Investigations – Police Chief …, accessed February 9, 2026, https://www.policechiefmagazine.org/leveraging-intelligence-to-optimize-investigations/
- Contested Logistics in LSCO, accessed February 9, 2026, https://d34w7g4gy10iej.cloudfront.net/pubs/pdf_70131.pdf
- U.S. Army Learning concept – tradoc, accessed February 9, 2026, https://adminpubs.tradoc.army.mil/pamphlets/TP525-8-2.docx
- accessed February 9, 2026, https://www.armchairsniper.com/blog/find-disrupt-fix-finish-follow-through-kill-chain#:~:text=Army%20tactical%20publications%20now%20reflect,%2C%20cohesion%2C%20and%20targeting%20ability.
- Mastering Disruption: The Evolution of Kill Chain … – Armchair Sniper, accessed February 9, 2026, https://www.armchairsniper.com/blog/find-disrupt-fix-finish-follow-through-kill-chain
