1. Executive Summary
The United States Department of Defense is currently executing a historical and structural expansion of its unmanned aerial systems capabilities. Driven by strategic initiatives such as Replicator 1, which focuses on fielding thousands of autonomous systems, and Replicator 2, which aims to counter adversary small uncrewed aerial systems, the department is committing substantial capital toward autonomous warfare.1 Alongside a broader investment portfolio dedicated to existing drone and counter-drone technologies, this hardware-centric procurement strategy is designed to achieve tactical overmatch through mass and attrition.5 However, while the acquisition of physical platforms addresses the immediate requirement for tactical versatility in modern conflict, this intense fixation on the platforms themselves masks a severe, systemic vulnerability: the impending intelligence data deluge.
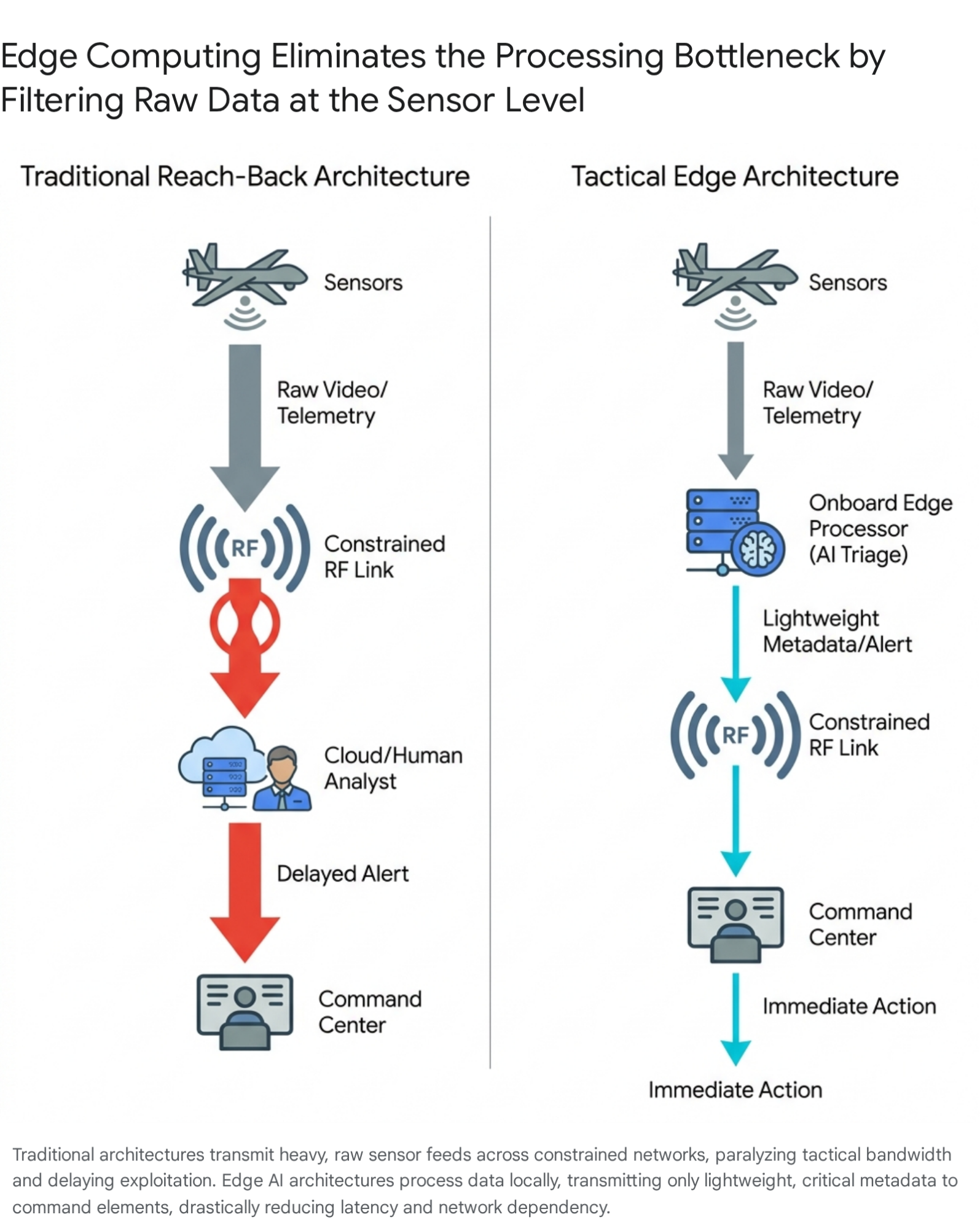
Deploying thousands of Intelligence, Surveillance, and Reconnaissance (ISR) sensors virtually guarantees a systemic bottleneck in Processing, Exploitation, and Dissemination (PED) operations.6 The legacy architecture of military intelligence relies on a reach-back model, streaming raw data—specifically high-definition full-motion video and high-fidelity sensor telemetry—from the tactical edge back to centralized command nodes for human analysis.8 In a paradigm featuring mass sensor deployments, this model is mathematically and physically unsustainable. It paralyzes tactical networks through bandwidth exhaustion, overwhelms human analysts, and ultimately decelerates the Observe-Orient-Decide-Act (OODA) loop rather than accelerating it.7
To successfully enable warfighters and achieve the objectives of(https://www.boozallen.com/insights/jadc2/solving-the-hidden-challenges-of-jadc2.html) (JADC2), leadership must pivot from traditional hardware procurement metrics to a comprehensive evolution of the intelligence infrastructure. This strategic assessment examines the critical, often overlooked systemic requirements for mass drone deployments across the entire lifecycle: design, build, operate, and evolve. It outlines the necessity of transitioning from centralized cloud processing to localized edge computing, the required implementation of automated data triage, the realities of maintaining Machine Learning Operations (MLOps) in Denied, Degraded, Intermittent, and Limited (DDIL) environments, and the foundational data governance required to maintain decision dominance in modern warfare.
2. The Strategic Context: Replicator, Mass Sensors, and the Acquisition Illusion
The defense establishment’s rapid acquisition strategies correctly identify mass as a critical component of deterrence and combat efficacy. The establishment of Joint Interagency Task Force 401 and the advancement of Replicator 2 underscore a clear policy directive: the United States must field innovative capabilities at the speed of relevance.3 Observations from the ongoing conflict in Ukraine demonstrate that high-volume, low-cost drone deployments fundamentally alter the economics of warfare and provide unprecedented situational awareness.12 According to assessments of the theater, the introduction of small, difficult-to-detect drones has disrupted traditional force projection, validating a new perspective on the targetability matrix where low-cost systems produce outsized operational effects.12
However, the physical deployment of an autonomous platform is only the first phase of its operational lifecycle. The “acquisition illusion” occurs when the procurement of physical platforms outpaces the capacity of the underlying command, control, and intelligence networks to support them. Historically, the United States military has collected far more aerial ISR data than it can effectively exploit.15 Even prior to the advent of swarm technology, as the unmanned aerial system fleet grew exponentially from roughly 163 aircraft in 2003 to over 7,400 by 2012, the Department of Defense faced persistent, structural shortages of personnel capable of processing and disseminating the overwhelming amount of collected information.15
A standard military PED workflow involves collecting vast amounts of data from drones, applying human cognitive analysis or early-stage software to extract actionable intelligence, and securely distributing that intelligence to decision-makers.6 When the sensor count multiplies by orders of magnitude through initiatives like Replicator, the linear scaling of human intelligence analysts becomes impossible.16 Therefore, the metric of success for modern defense initiatives cannot simply be the sheer number of attritable systems fielded by a specific deadline.2 Instead, the metric must encompass the ratio of actionable intelligence generated per sensor deployed, measured against the latency of its delivery to the tactical edge. Without a commensurate investment in the infrastructure required to design, build, operate, and evolve these data systems, the acquisition of thousands of drones will yield a logistical burden rather than a strategic advantage.
3. The Mathematics of the Processing, Exploitation, and Dissemination Bottleneck
The Processing, Exploitation, and Dissemination cycle is the fundamental transformation mechanism that turns raw collection data into usable combat information.7 To understand the vulnerability of mass sensor deployments, it is necessary to deconstruct this cycle and examine the mathematical constraints that govern it. The current bottleneck within this cycle manifests across three distinct failure points when subjected to a mass-sensor environment.
3.1 Processing Vulnerabilities and Data Saturation
Processing involves the automated or human-driven conversion of collected raw data into a usable format.7 Modern ISR platforms utilize a complex and overlapping array of sensors, including electro-optical cameras, thermal imaging, acoustic arrays, seismic sensors, and multi-spectral systems.15 In traditional operational architectures, this raw data is transmitted continuously from the platform to a receiving station. The integration of advanced commercial technologies and persistent ISR drones has resulted in a massive, exponential increase in the sheer volume of data generated at the tactical edge.11
A single high-definition video feed generates gigabytes of data per hour. When multiplied by hundreds or thousands of simultaneous flight operations, the volume creates an immediate saturation point. The storage arrays, network switches, and preliminary filtering systems are physically overwhelmed before the exploitation phase can even begin. The National Geospatial-Intelligence Agency has noted that over the next five to ten years, the defense enterprise will experience a potential tripling of geospatial intelligence data, creating a deluge that traditional processing frameworks cannot accommodate.21
3.2 Exploitation and the Human Cognitive Limitation
Exploitation requires the refinement of processed data to provide operational context and actionable targeting information.7 Historically, this phase has relied almost exclusively on human analysts sitting in centralized facilities, reviewing hours of high-resolution video to differentiate between mundane civilian activities and hostile actions.22 For example, analysts must determine whether an individual on the ground is holding a shovel or a weapon, or whether a vehicle trajectory indicates a routine patrol or an impending ambush.23
Even with highly capable legacy platforms like the MQ-9 Reaper, the primary manpower requirement has always been the PED teams.23 The cognitive load on these analysts is immense. With the introduction of swarming tactics, collaborative autonomous systems, and mass drone deployments, the visual and electromagnetic data influx far exceeds human cognitive limits. An analyst cannot effectively monitor twenty simultaneous video feeds, nor can they mentally fuse acoustic data with thermal imaging in real-time. Without the integration of automated object detection, classification, and tracking at the point of collection, critical threat indicators remain buried in the noise, rendering the collected data useless.
3.3 Dissemination Delays and Latency Risks
Dissemination is the distribution of relevant, synthesized information to commanders, staff, and tactical elements on the ground.7 If the processing and exploitation phases are delayed by data saturation and human cognitive overload, the resulting intelligence products suffer from severe latency. In highly dynamic combat scenarios, latent intelligence is often equivalent to no intelligence at all. By the time a human analyst reviews a video feed, identifies a mobile missile launcher, and disseminates the coordinates back to the tactical unit, the target has likely moved. Furthermore, the traditional reach-back model assumes continuous, high-bandwidth connectivity to transmit these intelligence products back to the front lines, an assumption that frequently collapses in contested environments.9
4. Operational Realities: The DDIL Environment and Bandwidth Physics
A core systemic requirement for operating a modern autonomous fleet is designing for the realities of the electromagnetic spectrum. The assumption that continuous, high-bandwidth communication infrastructure will be available in a near-peer conflict is a critical vulnerability that endangers the force.9 The modern battlespace is explicitly characterized by Denied, Degraded, Intermittent, and Limited (DDIL) environments.8
Adversaries have invested heavily in electronic warfare capabilities designed specifically to jam radio frequency communications and degrade satellite uplinks.8 When a swarm of tactical drones attempts to stream live video, transmit acoustic signatures, and relay precise spatial coordinates over a contested radio frequency network, the network strains under the sheer physics of bandwidth demands.25 The physics of data transmission dictate that limited spectrum simply cannot support the simultaneous high-definition streams of thousands of sensors.
Consider a forward operating base running a host of internet-of-things edge devices to simulate a smart battlefield.25 During military exercises, the introduction of overhead drones streaming live video, combined with ground vehicles relying on remote commands, quickly saturates available tactical Wi-Fi or radio links. Satellite links, while useful for strategic reach-back, introduce noticeable latency and can be easily disrupted by weather patterns or adversary jamming.25 If an operation relies on this streaming data for situational awareness, intermittent video feeds and lagging updates will result in severe operational failures, potentially costing lives in a combat situation.25
To counter this, the intelligence infrastructure must shift its operational perspective regarding information mobility. Instead of moving massive amounts of data to the computing power, the computing power must be moved to the data.10
| Network Condition | Characteristic Challenges | Impact on Traditional PED Operations | Edge Computing Mitigation Strategy |
| Denied | Complete loss of external connectivity via active jamming or physical infrastructure destruction. | Total operational blindness; drones cannot transmit feeds; centralized human analysts receive zero data. | Drones execute pre-programmed autonomous missions; onboard AI logs threats for later transmission or initiates kinetic action if pre-authorized. |
| Degraded | High latency, substantial packet loss, and severe bandwidth throttling due to electronic interference. | Unusable video feeds; corrupted sensor telemetry; severe OODA loop delays rendering targeting impossible. | Transmission is restricted entirely to essential metadata (e.g., target coordinates, classification tags) requiring minimal bandwidth. |
| Intermittent | Sporadic connection availability; unpredictable drops and reconnections over variable terrain. | Incomplete intelligence pictures; disrupted track maintenance for moving targets; dropped communication handshakes. | Edge processors buffer high-priority alerts and burst-transmit metadata only during verified connection windows. |
| Limited | Insufficient bandwidth to support the total volume of deployed sensor nodes concurrently. | Network saturation; critical threat indicators are queued behind routine, low-value surveillance data. | Automated data triage prioritizes specific threat signatures (e.g., surface-to-air missile sites) over baseline terrain mapping. |
5. Designing the Infrastructure: Edge Computing and Hardware Imperatives
The systemic requirement to design drones for the realities of the DDIL environment necessitates a transition to edge computing. Edge computing is the foundational technological architecture required to manage the intelligence data deluge. It involves deploying miniaturized compute servers and ruggedized processors directly onto the sensor platforms—such as the drones themselves, autonomous ground vehicles, and soldier-borne devices—or at forward operating bases immediately adjacent to the point of collection.10
5.1 Hardware Miniaturization and SWaP Constraints
The operationalization of edge computing on attritable platforms requires specialized hardware that meets stringent Size, Weight, and Power (SWaP) constraints.10 In the past, the computational power required to run complex neural networks and computer vision models was confined to massive, climate-controlled data centers. Today, commercial and defense sector developments have yielded next-generation, miniaturized AI-powered edge processors capable of integration into small, tactical drones.28
For example, commercial systems currently undergoing military testing, such as the(https://safeprogroup.com/safe-pro-launches-next-gen-ai-powered-node-x-miniaturized-edge-processing-for-drone-footage-at-u-s-army-exercise/), utilize real-time AI inference on edge compute servers designed as backpack kits or onboard modules.28 These ruggedized systems can process drone imagery to generate 3D maps, digital surface models, and detect specific threats like unexploded ordnance entirely off-grid, without the need for external connectivity.28 This level of processing power enables forces to achieve “terrain dominance” without relying on continuous human monitoring.18
5.2 Real-Time Decision Making at the Source
The true tactical advantage of edge processing lies in its immediacy. By performing inference directly on the device, the latency introduced by transmitting data to distant servers is entirely eliminated.30 Systems designed for the tactical edge can process multiple sensor streams simultaneously, cross-referencing visual data with radar or acoustic inputs.31 When an operator on a reconnaissance mission utilizes a drone equipped with onboard AI, the system can instantly detect and classify movement—distinguishing between friendly forces, adversary combatants, and local fauna—before passing only the critical alerts up the chain of command.10 This local processing accelerates the Observe-Orient-Decide-Act loop to machine speeds, generating instant intelligence exactly where it is needed most.10
5.3 Bandwidth Optimization through Metadata Extraction
Perhaps the most vital systemic benefit of edge computing is its ability to salvage tactical networks. When edge AI algorithms classify threats before the data ever leaves the node, they transform heavy, unwieldy raw data into lightweight, actionable metadata.32 Instead of attempting to transmit gigabytes of high-definition full-motion video over a degraded RF link, the drone transmits only a few kilobytes of text and coordinate data.31 This metadata might include a vehicle’s trajectory, its speed, a specific behavior pattern, or a definitive object classification.31 This aggressive selective transmission strategy drastically reduces bandwidth requirements, preventing operator overload and ensuring that tactical networks remain functional even when populated by thousands of autonomous systems operating in concert.30
6. Building the Triage Logic: Automated Intelligence and Sensor Fusion
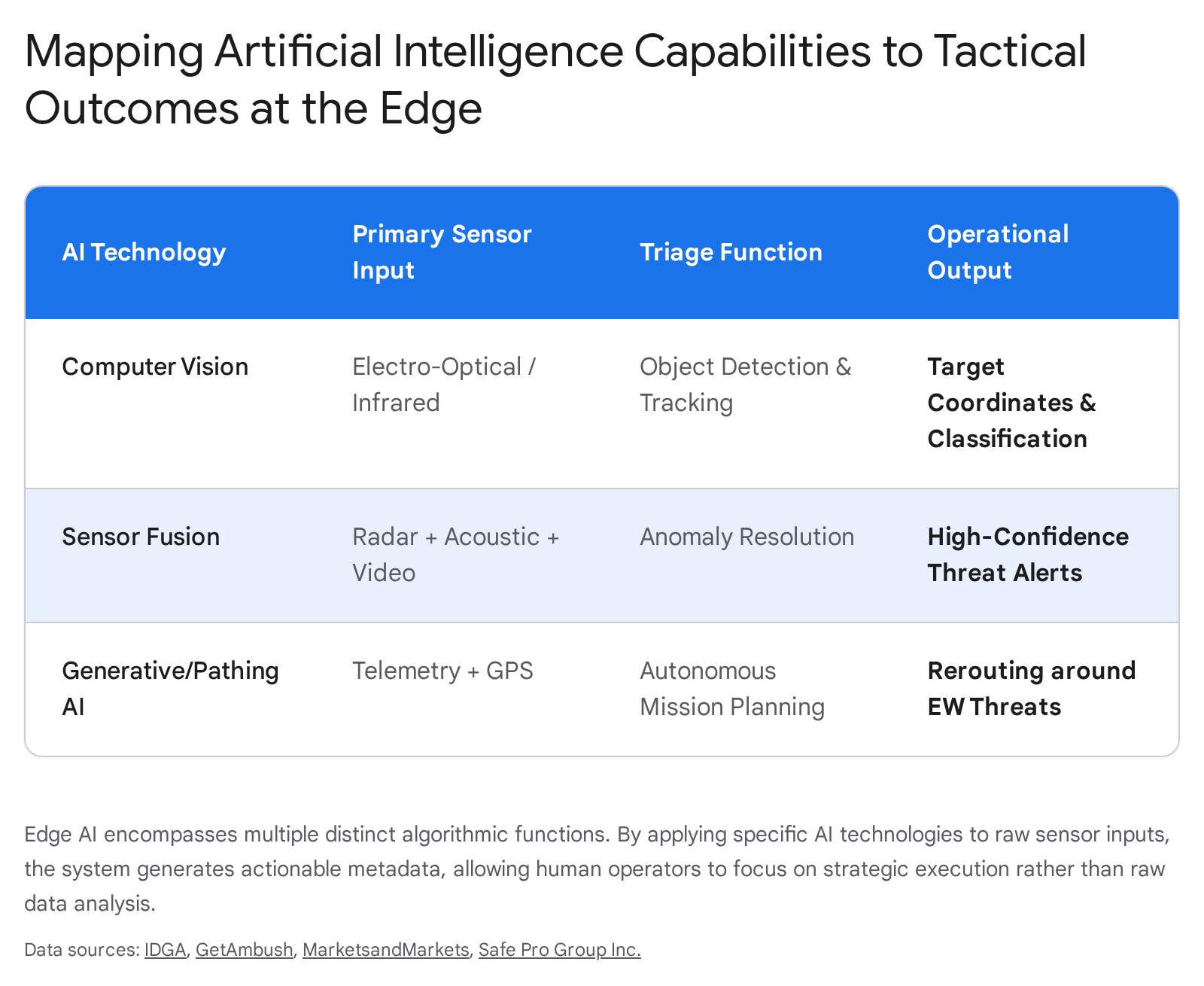
While edge computing provides the necessary physical hardware infrastructure, artificial intelligence and machine learning (AI/ML) algorithms provide the triage logic that makes the hardware useful. The systemic requirement to build intelligent systems involves shifting the operational paradigm from a passive “collect and review” methodology to an active “detect and alert” posture.
6.1 Project Maven and the Evolution of Algorithmic Warfare
The Department of Defense has recognized the necessity of algorithmic triage since the inception of the(https://en.wikipedia.org/wiki/Project_Maven), commonly known as Project Maven, in 2017.33 Initially conceptualized to centralize and automate the analysis of massive amounts of aerial imagery using computer vision, Maven demonstrated the clear capacity of AI to flag potential targets, extract features, and significantly decrease the time required for analysts to sift through raw data.21
The maturation of these machine learning technologies now allows them to be pushed out of centralized nodes and deployed directly down to the tactical edge.16 Predictive analytics, precise object detection, and complex behavior pattern recognition can now operate locally on the sensor platform.31 By establishing mathematical baselines of normal environmental behavior, AI systems can automatically filter out mundane activity, alerting human operators only when anomalies or specific target signatures are detected.35
6.2 The Mechanics of Sensor Fusion Algorithms
A single sensor modality is rarely sufficient in complex, contested environments where adversaries employ advanced camouflage, concealment, and deception tactics. Advanced AI deployed at the edge executes multi-sensor data fusion, combining inputs from electro-optical cameras, infrared sensors, acoustic arrays, and radar to create a comprehensive, multi-dimensional awareness picture.18
Heterogeneous fusion algorithms leverage the complementary strengths of different sensors. For instance, an algorithm may use radar to detect a concealed target through light foliage, cue a thermal imaging sensor to verify the heat signature of an engine, and utilize acoustic data to confirm the specific engine type.19 This process provides a dramatically higher confidence level than any individual sensor could achieve alone. Furthermore, fusion allows for the mathematical filtering of environmental noise and the resolution of conflicting evidence through probabilistic models. Techniques such as Kalman filtering combine noisy measurements with predictive models to estimate target trajectories, while Dempster-Shafer theory manages uncertainty across conflicting sensor inputs.19
6.3 Automated Pathing and Generative Avoidance
Beyond simply identifying targets, the triage logic built into modern drones must include autonomous navigation and survival capabilities. In environments where GPS is jammed and communications are severed, drones must utilize AI-driven terrain mapping and visual odometry to navigate.36 Generative AI and pathing algorithms enable drones to create new mission paths dynamically, analyzing telemetry mid-flight to route around newly detected electronic warfare threats or physical obstacles.37 This ensures that the platform survives long enough to gather intelligence and return to a communication window where it can burst-transmit its findings.
7. Operating the Autonomous Fleet: Transforming the Analyst Workflow
The systemic requirement to operate a fleet of thousands of drones demands a fundamental restructuring of the human workforce that supports them. As AI assumes the burden of initial data processing and object detection, the role of the military intelligence analyst must undergo a profound transformation.
7.1 From Video Viewers to Anomaly Managers
The traditional intelligence collection model required human analysts to act as the primary filter for raw data. In an AI-enabled collection environment, this process is inverted. Automation and machine learning models are tasked with establishing baselines of normal behavior and executing routine surveillance tasks.35 When the AI detects a deviation from this baseline—such as the sudden aggregation of vehicles in a typically empty sector—it generates an alert.
The human analyst is therefore elevated from a manual video reviewer to an anomaly manager and strategic decision-maker.35 Instead of searching for targets, the analyst validates high-confidence alerts generated by the system, assessing the broader operational context to determine the appropriate response. This shift requires intelligence professionals to blend enduring tradecraft with entirely new technical skillsets, integrating cross-disciplinary knowledge to manage complex machine outputs rather than raw inputs.35
7.2 Human-Machine Teaming in High-Speed Engagements
Operating mass sensor networks effectively requires the implementation of advanced human-machine teaming concepts. This is particularly critical in counter-UAS (C-UAS) operations, where the timeline between detection and necessary interception is measured in seconds.38 Defense against drone swarms requires computational capacity to rapidly detect, track, and target myriads of threats simultaneously.39
A highly integrated command and control interface must connect sensors to defeat mechanisms, allowing the AI to present the human operator with a prioritized list of threats and recommended weapon pairings.38 The operator remains “in the loop” or “on the loop” to authorize kinetic action, but the machine handles the complex calculus of targeting and tracking.38 By employing algorithms to achieve convergence at machine speeds, the military shifts the traditional “sensor-to-shooter” paradigm into a continuous “sensor-to-shooter-to-sensor” feedback loop.40
7.3 Mitigating the Risks of Automation
While operating these systems, leadership must also remain cognizant of the psychological and operational risks inherent in automated warfare. There is a documented danger that reducing the complexities of human conflict to sterile data points and AI-generated alerts could desensitize operators to the realities of kinetic action.41 Furthermore, analysts must be trained to recognize and counter “automation bias,” the tendency to blindly trust machine outputs even when contextual clues suggest an algorithmic error. Robust training paradigms, potentially utilizing advanced simulation environments and synthetic data, are required to ensure that human operators maintain critical oversight over automated systems.37
8. Evolving the Force: MLOps and Model Adaptation at the Edge
A critical and often entirely overlooked component of designing, building, and operating military technology is the continuous lifecycle of the machine learning models themselves. The operational environment is never static. An algorithm perfectly trained on adversary vehicle signatures from 2024 will likely experience severe “model drift” and become obsolete against an adversary employing novel camouflage, new electronic signatures, or adapted movement tactics in 2026. Therefore, the systemic requirement to evolve dictates that the models operating at the tactical edge must be continuously updated.
8.1 The MLOps Challenge in DDIL Environments
Machine Learning Operations (MLOps) encompasses the complete lifecycle of developing, testing, deploying, and continuously monitoring AI models.42 In commercial enterprise environments, MLOps is relatively straightforward, relying on stable, high-speed fiber-optic internet connections to seamlessly push gigabytes of updates to edge devices. In the military context, updating an AI model on a drone operating in a contested DDIL environment presents profound technical and logistical challenges.9
If a deployed swarm encounters a new type of enemy unexploded ordnance, a novel counter-drone jamming vehicle, or a disguised command post, the local edge AI may fail to classify it accurately. To maintain operational dominance, the intelligence architecture must capture this new data signature, transmit it back to a secure environment, retrain the model to recognize the new threat, and push the updated mathematical parameters back to the deployed edge nodes.28
8.2 Distributed Architectures and Delta Updates
To manage MLOps at the tactical edge, the Department of Defense must implement sophisticated distributed domain-driven architectures.44 This involves utilizing hybrid cloud systems where Small Language Models (SLMs) and highly compressed computer vision models operate locally on the drone hardware, ensuring core functionality is maintained even during periods of total network isolation.29
Crucially, when intermittent communication windows open, the system must not attempt to transmit full datasets or complete model replacements. Such actions would instantly saturate the limited bandwidth. Instead, the architecture must utilize techniques such as federated learning or highly optimized delta updates. In this model, the system transmits only the new mathematical weights or the specific anomalous data signatures back to a secure command node. The central hub then retrains the model and pushes a micro-update back to the swarm.36 Software suites designed for the tactical edge must be capable of slashing AI update times from weeks to minutes, allowing the system to rapidly adapt to adversary behavior while remaining forward-deployed and mission-ready.36
| MLOps Phase | Commercial Enterprise Baseline | Military Tactical Edge Requirement (DDIL) |
| Data Collection | Continuous streaming of massive datasets to centralized cloud servers. | Selective transmission of anomalous signatures only; localized storage of routine data. |
| Model Training | Centralized, resource-intensive training on massive GPU clusters. | Centralized training combined with federated learning techniques across dispersed nodes. |
| Model Deployment | Pushing massive software containers via high-bandwidth fiber connections. | Transmitting highly compressed delta updates (weights only) during brief communication windows. |
| Monitoring | Real-time telemetry and performance dashboards available continuously. | Asynchronous performance logging; burst transmission of error rates when connectivity allows. |
9. Data Governance and JADC2 Integration: The Systemic Foundation
The technological solutions of edge computing and automated triage cannot exist in a vacuum. They must be underpinned by a rigorous, enterprise-wide framework for data management. The(https://www.boozallen.com/insights/jadc2/solving-the-hidden-challenges-of-jadc2.html) (JADC2) initiative represents the visionary approach to linking sensors and shooters across all armed services into a unified, interoperable network.45 The success of JADC2 is fundamentally dependent on resolving the intelligence data deluge through modernized governance.
9.1 The Shift from Net-Centricity to Data-Centricity
JADC2 requires the military to undergo a paradigm shift from a net-centric mindset to a data-centric methodology.40 This means that the intrinsic value lies in the data itself, which must be accessible, discoverable, and secure regardless of the specific platform or network that originated it.45 If thousands of Replicator drones are successfully deployed, but their sensor data is locked within proprietary, vendor-specific silos that cannot communicate with Army artillery networks or Navy targeting systems, the JADC2 framework will fail catastrophically. To operate at the high speeds required by modern conflict, JADC2 demands extensive machine-to-machine transactions, automatically extracting, consolidating, and processing data directly from the sensing infrastructure without the friction of manual data wrangling.40
9.2 The DoD Data Strategy and the “Data Decrees”
The 2026 Artificial Intelligence Strategy for the Department of War emphasizes the aggressive enforcement of the “DoD Data Decrees”.48 These critical directives, overseen by the Chief Digital and AI Office (CDAO), mandate that all military departments and components establish, maintain, and update federated data catalogs.48 These catalogs must expose system interfaces, data assets, and access mechanisms across all classification levels, allowing algorithms to discover and utilize data enterprise-wide.48
Furthermore, the strategy insists on transforming the cultural approach to data governance. The traditional concept of “data ownership,” which historically isolated valuable intelligence within functional, branch-specific silos, must be entirely reoriented toward a model of “data stewardship”.45 Data is declared a strategic asset, and collective stewardship ensures that datasets—particularly those essential for AI training and algorithmic model refinement—are securely brokered and made available to authorized entities across the enterprise.46
By adopting a decentralized data management paradigm, supported by frameworks such as the DoD Data Mesh Reference Architecture, the DoD can ensure that authoritative data is shared securely at the speed of the mission.44 This requires abandoning rigid structural ownership in favor of an enterprise-level methodology defined by modular, open-systems approaches (MOSA), where program managers acquire AI capabilities that enforce open interfaces, allowing for seamless third-party integration.45 In parallel, initiatives like the(https://www.war.gov/News/Releases/Release/Article/4314411/department-of-war-announces-new-cybersecurity-risk-management-construct/) (CSRMC) ensure that security is dynamically embedded across all five phases of the lifecycle, moving away from static compliance checklists toward automated, continuous monitoring.51
10. Lessons from Contemporary Theaters and Agile Acquisition
The theoretical imperatives of edge computing, data triage, and data centricity are not abstract concepts; they are currently being validated in active combat zones. The ongoing war in Ukraine has served as a profound accelerator for modern warfare concepts, providing critical lessons regarding the drone development lifecycle and the necessity of rapid adaptation.52
10.1 The Velocity of Innovation and Bottom-Up Requirements
Ukraine successfully adapted its drone acquisition and operational lifecycle by aligning it with agile, commercial technology development processes.53 Faced with urgent wartime demands and the clear failure of legacy procurement systems to keep pace, traditional, rigid top-down forecasting was abandoned. Instead, Ukrainian authorities shifted to a bottom-up, problem-driven approach rooted in immediate battlefield realities.53 Technical specifications are no longer issued as massive, static documents; rather, they are articulated as operational problems by the end-users themselves. This fosters a close partnership between government and the commercial sector, utilizing hackathons and direct engagement to encourage rapid prototyping, testing, and iterative refinement.53
The Department of Defense must absorb this critical lesson: the intelligence infrastructure supporting mass sensors cannot be a static, multi-year monolith. The software dictating edge processing and object classification must be as attritable, adaptable, and easily replaceable as the physical drones themselves. Initiatives like the AI Rapid Capabilities Cell (AI RCC), backed by the CDAO and the Defense Innovation Unit, are beginning to infuse the military with this agile mindset, taking the most capable commercial AI systems and rapidly moving them into the hands of operators.54 The Department must continue to foster an ecosystem where algorithms are tested against military-grade data sets and rapidly deployed to the field, aggressively bypassing legacy acquisition delays.41
10.2 The Reality of Mass and Attrition
Furthermore, contemporary conflicts conclusively demonstrate that expensive, medium-altitude long-endurance (MALE) drones—such as the Bayraktar TB2—while highly valuable in permissive environments early in a conflict, are highly vulnerable to sophisticated, integrated air defense systems.14 The strategic shift toward low-cost, one-way attack drones and pre-programmed loitering munitions confirms the fundamental validity of the Replicator initiative’s focus on mass.14 However, because a massive percentage of these attritable systems may be intercepted or jammed, their strength lies entirely in overwhelming volume.14
Managing the intelligence data from a high-attrition swarm requires systems that do not rely on the continuous survival of any single node. Intelligence gathering must be highly distributed. The loss of a drone must instantly trigger the automated offloading of its final, critical intelligence metadata to neighboring nodes within the swarm before its physical destruction, ensuring that the situational awareness picture remains intact even as individual platforms are attrited.
11. Strategic Recommendations for DoD Leadership
The aggressive procurement of physical drone hardware represents only a fraction of the capability required to achieve true military dominance in the modern era. An over-fixation on platform metrics obscures the reality that data is the ammunition of twenty-first-century warfare. To prevent the collapse of tactical networks, manage the impending data deluge, and empower warfighters with immediately actionable intelligence, leadership is advised to implement the following strategic directives:
- Mandate Edge Compute as a Baseline Procurement Requirement: Future procurement of ISR drones, autonomous systems, and counter-UAS platforms must specify robust onboard edge processing capabilities as a non-negotiable requirement.28 Platforms must possess the necessary SWaP capacity to host localized AI inference models capable of transforming heavy, raw sensor data into lightweight metadata before transmission.
- Prioritize MLOps Infrastructure for DDIL Environments: Financial and structural investment must be redirected toward the software infrastructure required to continuously update and maintain AI models in contested, degraded environments.9 The ability to securely push algorithmic delta updates to a deployed swarm over intermittent, low-bandwidth connections is strategically just as critical as the performance of the physical hardware itself.
- Enforce Strict Data Stewardship and Open Standards: Program managers must rigorously enforce the DoD Data Decrees, ensuring that all procured systems utilize open application programming interfaces and adhere to modular open systems architectures.46 Vendor lock-in regarding proprietary intelligence data streams must be actively dismantled to enable true machine-to-machine interoperability essential for JADC2 success.40
- Fundamentally Restructure the Intelligence Workforce: The role of the military intelligence analyst must rapidly evolve from manual data processing (e.g., passively viewing full-motion video feeds) to strategic oversight and anomaly resolution.21 Training doctrines must comprehensively integrate human-machine teaming concepts, where human operators define the strategic parameters of the AI, and the AI manages the overwhelming volume of the tactical data.38
- Decentralize Capability Development and Adopt Agile Feedback Loops: The Department must adopt agile, iterative development cycles modeled on successful commercial software practices and lessons learned from the Ukrainian theater.42 Allow tactical units to provide direct, rapid feedback regarding algorithm performance, establishing an unbroken and accelerated feedback loop from the warfighter at the tactical edge directly to the data scientist in the development hub.53
The United States Department of Defense possesses the industrial resources, the technological capability, and the strategic vision to design, build, operate, and evolve the most advanced autonomous systems in human history. However, these systems will only yield a decisive military advantage if the underlying intelligence infrastructure is meticulously designed to triage, process, and exploit data at the speed of modern algorithmic warfare. The future of combat dominance relies not on which force can collect the most raw data, but on which force possesses the systemic architecture to understand and act upon that data the fastest.8
Please share the link on Facebook, Forums, with colleagues, etc. Your support is much appreciated and if you have any feedback, please email us in**@*********ps.com. If you’d like to request a report or order a reprint, please click here for the corresponding page to open in new tab.
Sources Used
- Pentagon Counter-Drone Priority Meets Defense AI: Video Intelligence Joins the RF Sensing Stack – PR Newswire, accessed April 24, 2026, https://www.prnewswire.com/news-releases/pentagon-counter-drone-priority-meets-defense-ai-video-intelligence-joins-the-rf-sensing-stack-302748471.html
- Replicator and beyond: The future of drone warfare | Brookings, accessed April 24, 2026, https://www.brookings.edu/events/replicator-and-beyond-the-future-of-drone-warfare/
- Joint Interagency Task Force Announces First Replicator 2 Purchase to Counter Homeland Drone Threats – Department of War, accessed April 24, 2026, https://www.war.gov/News/News-Stories/Article/Article/4377021/joint-interagency-task-force-announces-first-replicator-2-purchase-to-counter-h/
- DOD Innovation Official Discusses Progress on Replicator > Department of Defense Manufacturing Technology Program > News Display, accessed April 24, 2026, https://www.dodmantech.mil/News/News-Display/Article/3999474/dod-innovation-official-discusses-progress-on-replicator/
- DOD moves to make its largest-ever investment in drones and anti-drone weapons, accessed April 24, 2026, https://defensescoop.com/2026/04/21/dod-plans-largest-ever-investment-drones-anti-drone-weapons/
- Defense PED (Processing, Exploitation & Dissemination) Technology Providers, accessed April 24, 2026, https://www.defenseadvancement.com/suppliers/processing-exploitation-and-dissemination/
- Modeling Intelligence Ped With FOCUS: A Tactical-Level ISR Simulation – DSIAC, accessed April 24, 2026, https://dsiac.dtic.mil/articles/modeling-intelligence-ped-with-focus-a-tactical-level-isr-simulation/
- From Data to Dominance at the Tactical Edge – MinIO, accessed April 24, 2026, https://www.min.io/blog/from-data-to-dominance-at-the-tactical-edge
- Operationalizing AI at the Tactical Edge – Line of Departure – U.S. Army, accessed April 24, 2026, https://www.lineofdeparture.army.mil/Journals/Warrant-Officer-Journal/Archive/March-2026/Operationalizing-AI-at-the-Tactical/
- Military AI Video Solutions: Real-Time Intelligence at the Tactical Edge – Maris Tech, accessed April 24, 2026, https://www.maris-tech.com/blog/military-ai-video-solutions-real-time-intelligence-at-the-tactical-edge/
- Energizing Data-Driven Operations at the Tactical Edge: Challenges and Concerns (2021) – The Center for Climate & Security, accessed April 24, 2026, https://climateandsecurity.org/wp-content/uploads/2025/01/26183.pdf
- Lessons from the Ukraine Conflict: Modern Warfare in the Age of Autonomy, Information, and Resilience – CSIS, accessed April 24, 2026, https://www.csis.org/analysis/lessons-ukraine-conflict-modern-warfare-age-autonomy-information-and-resilience
- Drones in Modern Warfare: Lessons Learnt from the War in Ukraine – Australian Army Research Centre, accessed April 24, 2026, https://researchcentre.army.gov.au/sites/default/files/241022-Occasional-Paper-29-Lessons-Learnt-from-Ukraine_2.pdf
- The Impact of Drones on the Battlefield: Lessons of the Russia-Ukraine War from a French Perspective | Hudson Institute, accessed April 24, 2026, https://www.hudson.org/missile-defense/impact-drones-battlefield-lessons-russian-ukraine-war-french-perspective-tsiporah-fried
- Amateurs Talk Collection, Professionals Talk PED – Georgetown Security Studies Review, accessed April 24, 2026, https://georgetownsecuritystudiesreview.org/2015/02/25/amateurs-talk-collection-professionals-talk-ped/
- Big Data at War: Special Operations Forces, Project Maven, and Twenty-First-Century Warfare, accessed April 24, 2026, https://mwi.westpoint.edu/big-data-at-war-special-operations-forces-project-maven-and-twenty-first-century-warfare/
- Airborne ISR Market – Intelligence Surveillance and Reconnaissance – Revenue, Size & Share, accessed April 24, 2026, https://www.mordorintelligence.com/industry-reports/airborne-isr-market
- Terrain Dominance Through AI-Powered Surveillance in Modern Military Operations, accessed April 24, 2026, https://www.maris-tech.com/blog/terrain-dominance-through-ai-powered-surveillance-in-modern-military-operations/
- Tactical Edge Sensor Fusion at Scale – Ambush, accessed April 24, 2026, https://www.getambush.com/article/tactical-edge-sensor-fusion-at-scale/
- Persistent ISR (Intelligence, Surveillance, Reconnaissance) – Hoverfly Technologies, accessed April 24, 2026, https://hoverflytech.com/applications/defense/persistent-isr-intelligence-surveillance-reconnaissance-drone-systems/
- GEOINT Artificial Intelligence, accessed April 24, 2026, https://www.nga.mil/news/GEOINT_Artificial_Intelligence_.html
- Operationalizing Intelligence Through Small Unmanned Aircraft Systems – Line of Departure, accessed April 24, 2026, https://www.lineofdeparture.army.mil/Journals/Military-Intelligence/Military-Intelligence-Archive/2025-July-December/Operationalizing-Intelligence/
- Significant MQ-9 Reaper drone AI upgrade opens door to full military autonomy, accessed April 24, 2026, https://www.311institute.com/significant-mq-9-reaper-drone-ai-upgrade-opens-door-to-full-military-autonomy/
- Military & Humanitarian Response – The world’s first device-based AI triage system – ERTRIAGE, accessed April 24, 2026, https://ertriage.com/military-humanitarian/
- Military Networks: Rugged Fiber at the Tactical Edge for Secure, Real-Time Ops – Clearfield, accessed April 24, 2026, https://www.seeclearfield.com/newsroom/military-networks-rugged-fiber-at-tactical-edge-for-secure-ops.html
- Analysis and Proposal of Strategies for the Management of Drone Swarms Through Wi-Fi Technologies – MDPI, accessed April 24, 2026, https://www.mdpi.com/2504-446X/9/8/584
- 5 Ways Edge Servers Improve UAV Military Programs, Applications – Trenton Systems, accessed April 24, 2026, https://www.trentonsystems.com/en-us/resource-hub/blog/5-ways-edge-servers-improve-military-uavs
- Safe Pro Launches Next Gen AI Powered NODE-X Miniaturized …, accessed April 24, 2026, https://safeprogroup.com/safe-pro-launches-next-gen-ai-powered-node-x-miniaturized-edge-processing-for-drone-footage-at-u-s-army-exercise/
- Frozen, Blind, and Air-Gapped: Reconciling Frontier Model Capabilities with Defense Infrastructure Realities – Harvard DASH, accessed April 24, 2026, https://dash.harvard.edu/bitstreams/f8dd3f78-3210-4abe-80b2-2dfc0d572afa/download
- Edge Computing for Drone Data – Processing at the Source – FlytBase, accessed April 24, 2026, https://www.flytbase.com/blog/edge-computing-for-drone-data-processing
- Embedded AI in Military Drones Is Redefining Autonomy and Operations – IDGA, accessed April 24, 2026, https://www.idga.org/government-defense-it-communications/articles/embedded-ai-in-military-drones-is-redefining-autonomy-and-operations
- Persistent ISR at the Tactical Edge – You Need More Than AI to Counter Today’s Threats, accessed April 24, 2026, https://clearalign.com/knowledge-center/id/24/persistent-isr-at-the-tactical-edge–you-need-more-than-ai-to-counter-todays-threats
- Project Maven – Wikipedia, accessed April 24, 2026, https://en.wikipedia.org/wiki/Project_Maven
- Critical Missions in Data & AI – ECS, accessed April 24, 2026, https://ecstech.com/ecs-insight/article/critical-missions-in-data-ai-empowering-federal-agencies-through-innovation/
- The Collection Edge: Harnessing Emerging Technologies for … – CSIS, accessed April 24, 2026, https://www.csis.org/analysis/collection-edge-harnessing-emerging-technologies-intelligence-collection
- Defense Company – Latent AI, accessed April 24, 2026, https://latentai.com/industry/defense/
- Artificial Intelligence (AI) in Drones Market Report 2025-2030 [279 Pages & 340 Tables], accessed April 24, 2026, https://www.marketsandmarkets.com/Market-Reports/artificial-intelligence-drones-market-43722301.html
- Countering Swarms: Strategic Considerations and Opportunities in Drone Warfare, accessed April 24, 2026, https://ndupress.ndu.edu/Media/News/News-Article-View/Article/3197193/countering-swarms-strategic-considerations-and-opportunities-in-drone-warfare/
- An Urgent Matter of Drones: Lessons for NATO from Ukraine – CEPA, accessed April 24, 2026, https://cepa.org/comprehensive-reports/an-urgent-matter-of-drones/
- JADC2 Begins With Intelligence | AFCEA International, accessed April 24, 2026, https://www.afcea.org/signal-media/jadc2-begins-intelligence
- The Business of Military AI | Brennan Center for Justice, accessed April 24, 2026, https://www.brennancenter.org/our-work/research-reports/business-military-ai
- United States Marine Corps – ARTIFICIAL INTELLIGENCE IMPLEMENTATION PLAN, accessed April 24, 2026, https://www.marines.mil/Portals/1/Publications/NAVMC%203000.1%20(SECURED).pdf
- MLOps at the Edge in DDIL Environments for SPIE DCS 2024 – IBM Research, accessed April 24, 2026, https://research.ibm.com/publications/mlops-at-the-edge-in-ddil-environments
- MLOps at the edge in DDIL environments – ResearchGate, accessed April 24, 2026, https://www.researchgate.net/publication/381277033_MLOps_at_the_edge_in_DDIL_environments
- Solving the Hidden Challenges of JADC2 – Booz Allen, accessed April 24, 2026, https://www.boozallen.com/insights/jadc2/solving-the-hidden-challenges-of-jadc2.html
- DOD Data Strategy – Department of War, accessed April 24, 2026, https://media.defense.gov/2020/Oct/08/2002514180/-1/-1/0/DOD-DATA-STRATEGY.PDF
- Summary of the Joint All-Domain Command and Control Strategy – Department of War, accessed April 24, 2026, https://media.defense.gov/2022/Mar/17/2002958406/-1/-1/1/SUMMARY-OF-THE-JOINT-ALL-DOMAIN-COMMAND-AND-CONTROL-STRATEGY.PDF
- Artificial Intelligence Strategy for the Department of War, accessed April 24, 2026, https://media.defense.gov/2026/Jan/12/2003855671/-1/-1/0/ARTIFICIAL-INTELLIGENCE-STRATEGY-FOR-THE-DEPARTMENT-OF-WAR.PDF
- Department of Defense Chief Data Officer DoD Data Stewardship Guidebook – Chief Digital and Artificial Intelligence Office, accessed April 24, 2026, https://www.ai.mil/Portals/137/Documents/Resources%20Page/DoD%20Data%20Stewardship%20Guidebook.pdf
- department of the air force data strategy, accessed April 24, 2026, https://www.af.mil/Portals/1/documents/2026SAF/DAF_Data_Strategy.pdf
- Department of War Announces New Cybersecurity Risk Management Construct, accessed April 24, 2026, https://www.war.gov/News/Releases/Release/Article/4314411/department-of-war-announces-new-cybersecurity-risk-management-construct/
- Mapping the MilTech War: Eight Lessons from Ukraine’s Battlefield – Ifri, accessed April 24, 2026, https://www.ifri.org/en/studies/mapping-miltech-war-eight-lessons-ukraines-battlefield
- Unleashing U.S. Military Drone Dominance: What the United States Can Learn from Ukraine, accessed April 24, 2026, https://www.csis.org/analysis/unleashing-us-military-drone-dominance-what-united-states-can-learn-ukraine
- Inside the Pentagon’s AI acceleration STRATEGY – Apogee Magazine, accessed April 24, 2026, https://apogee-magazine.com/features/inside-the-pentagons-ai-acceleration-strategy/
- Army’s ISR Task Force looking to apply AI to intel data sets – DefenseScoop, accessed April 24, 2026, https://defensescoop.com/2024/10/17/army-isr-task-force-apply-ai-intel-data-sets/
- Strategic competition in the age of AI: Emerging risks and opportunities from military use of artificial intelligence – RAND, accessed April 24, 2026, https://www.rand.org/content/dam/rand/pubs/research_reports/RRA3200/RRA3295-1/RAND_RRA3295-1.pdf
