1. Executive Summary
As the United States Department of Defense accelerates the procurement and deployment of unmanned aerial systems through massive capital investments such as the Replicator initiatives, a critical vulnerability paradigm has emerged that threatens to undermine these technological advancements. While strategic focus and procurement efforts remain heavily weighted toward the autonomous platforms, payload capabilities, and the attritable mass of the drones themselves, the systemic requirements to design, operate, command, and protect the human element in the kill chain are frequently overlooked. Specifically, the Ground Control Stations (GCS) and the personnel operating them are highly susceptible to advanced adversary detection and subsequent elimination.
The deployment of uncrewed systems is not an isolated airborne event; it relies upon a complex, ground-based ecosystem. The electromagnetic and thermal signatures required to command, control, and sustain drone fleets act as brilliant beacons on the modern battlefield. These emissions expose operators to rapid adversary direction-finding algorithms, signals intelligence collection, and long-range kinetic strikes. Adversaries, notably the armed forces of the Russian Federation and the People’s Liberation Army of China, have spent decades heavily investing in reconnaissance-strike complexes designed specifically to detect radio frequency emissions, trace them to their source, and paralyze opposing command and control nodes. Evidence from contemporary conflicts demonstrates that the survival of drone operators is contingent not upon the sophistication of the aerial vehicle, but upon the operator’s ability to mask emissions, employ physical standoff, and operate within decentralized, mobile networks.
To successfully enable and protect warfighters, defense leadership must shift organizational, procurement, and doctrinal focus toward rigorous signature management, the physical decoupling of transmission antennas from human operators via remote split operations, and the implementation of self-healing mesh communication networks. The objective of this report is to analyze the inherent vulnerabilities of ground control nodes, evaluate adversary capabilities in targeting these systems, extract operational lessons from the Ukrainian theater and regional conflicts, and provide strategic pathways for enhancing operator survivability through mobility, emission control, and decentralized architectural frameworks. This analysis establishes that without immediate structural and doctrinal adaptation, the deployment of massive drone fleets will inadvertently map friendly positions for adversary artillery and loitering munitions, resulting in unacceptable attrition of specialized personnel.
2. Strategic Context: The Illusion of Unmanned Warfare
The contemporary military landscape is undergoing a structural shift driven by the proliferation of uncrewed systems across all domains. This shift is most visibly encapsulated by the Department of Defense’s Replicator initiative, a modernization campaign designed to counter massive military buildups by incentivizing domestic production capacity and the adoption of drones en masse.
The first iteration, Replicator 1, focused on fielding thousands of all-domain attritable autonomous systems within a highly compressed timeframe of 18 to 24 months, allowing commanders to tolerate a higher degree of risk in employing affordable, uncrewed platforms. The subsequent phase, Replicator 2, specifically targets the development and fielding of counter-unmanned aerial systems (C-UAS) to protect military installations and critical infrastructure, demonstrating an evolving understanding of the drone threat environment.1 To achieve these goals, organizations like the Defense Innovation Unit are working closely with regional commands, surveying existing autonomous capabilities, and accelerating technology transitions to the warfighter at unprecedented speeds.5
However, the terminology of “unmanned” or “uncrewed” warfare is inherently deceptive. While the aircraft itself is devoid of human occupants, the broader system remains heavily tethered to human operators, logistical supply chains, and complex ground infrastructure. The assumption that removing the pilot from the cockpit removes the human from danger ignores the reality of how these systems are commanded and controlled. The United States military possesses the most advanced unmanned aerial systems globally, yet the integration of these systems at the tactical level—down to the infantry platoon or squad—introduces new risks to the personnel required to operate them.6
As the military expands its drone inventory, including the Marine Corps’ search for new medium-range tactical drones capable of launching from austere environments and the Army’s continuous transformation of its Future Tactical Unmanned Aircraft System ecosystem, the physical footprint of operators expands correspondingly.7 Each new system fielded requires an operator interface, a data link, and a power source. Consequently, the proliferation of drones inevitably leads to the proliferation of localized C2 nodes. If the strategic focus remains fixated purely on the technological capabilities of the drone—such as sensor fidelity, flight endurance, and autonomous navigation—while ignoring the survivability of the ground control element, the resulting force structure will be inherently fragile. The strategic advantage of massed attritable drones is instantly nullified if the specialized personnel required to launch and orchestrate them are systematically targeted and eliminated by adversaries exploiting the physical and electronic requirements of the operating equipment.
3. The Vulnerability Paradigm: Multi-Spectral Signatures as Beacons
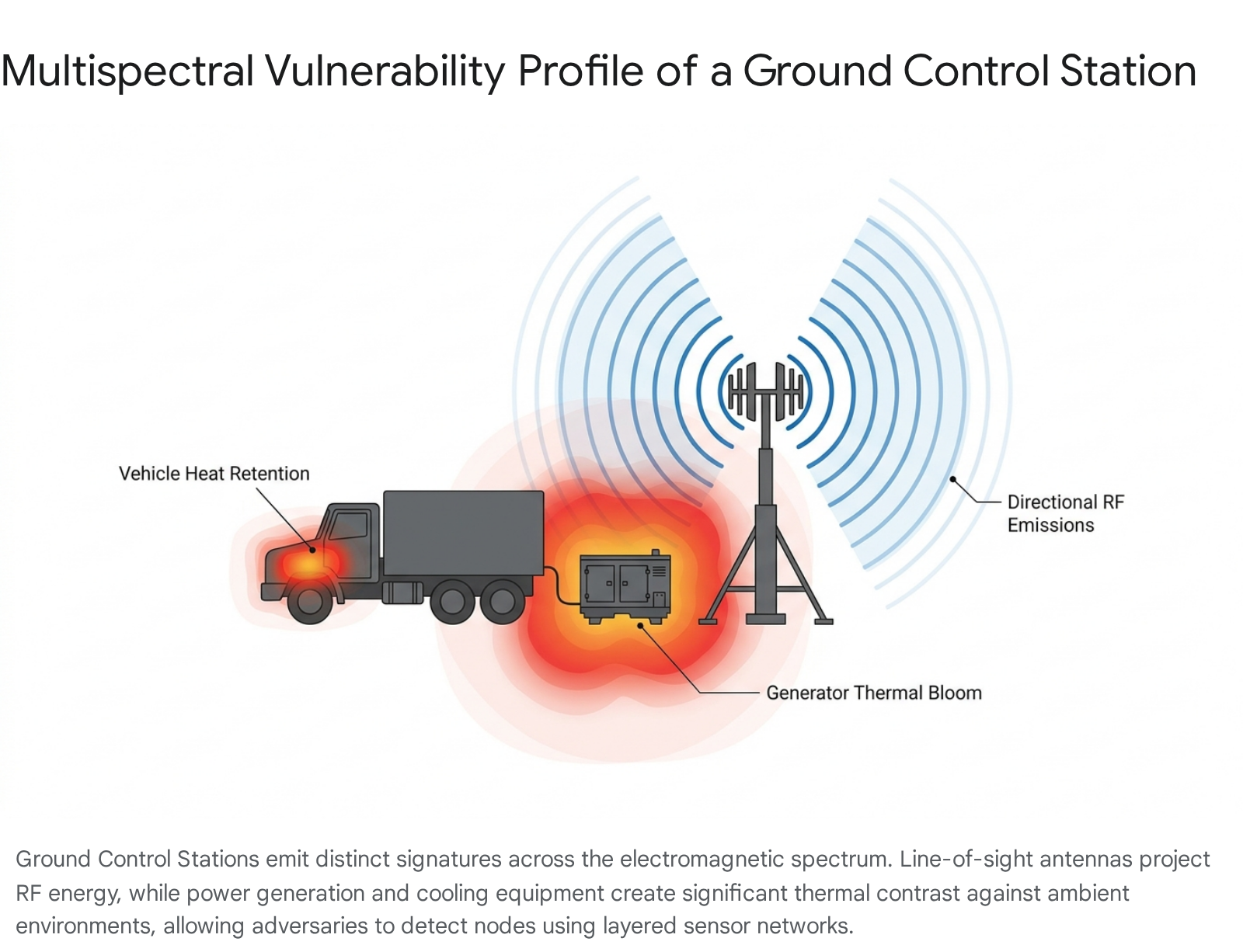
The operational deployment of an unmanned aerial system requires a continuous exchange of data, power consumption, and physical movement. These activities generate distinct signatures that disrupt the ambient baseline of the environment. Modern sensor networks do not rely on a single method of detection; they aggregate data across multiple spectrums to locate anomalies. Ground Control Stations, regardless of their size, emit signatures across three primary domains: radio frequency, thermal radiation, and physical presence.
Radio Frequency Signatures and Data Links
The most critical and vulnerable component of drone operations is the command and control link. To maintain flight control, receive telemetry, and download high-bandwidth full-motion video or sensor data, a GCS must continuously transmit and receive electromagnetic signals.9 In a standard configuration, tactical systems use direct point-to-point connections, while larger systems employ both Line-of-Sight and Beyond-Line-of-Sight communications via satellite.10
The radio frequency emissions generated by data link terminals are highly structured and clearly distinguishable from background electromagnetic radiation. The modulation schemes and bandwidths required to send high-definition video cannot be easily hidden or encrypted to the point of appearing as natural static. Furthermore, the physical properties of antennas create vulnerabilities. Directional antennas used for satellite communications or LOS links must often be aimed at shallow angles depending on the position of the aircraft or the satellite.11 While the main lobe of the antenna is directed toward the receiver, side lobes and back lobes inevitably leak radio frequency energy in unintended directions, providing a detectable signal for ground-based electronic support measures.11
This vulnerability is particularly acute during launch and recovery phases. The LOS antenna is highly susceptible to electronic attack when it must maintain unbroken communication with a low-flying aircraft attempting to land. If an adversary detects the emission, they can choose to jam the receiver, potentially causing the loss of the aircraft, or use direction-finding algorithms to triangulate the exact position of the transmission source to target the operator.11
Thermal and Infrared Heat Generation
While the RF spectrum serves as an immediate beacon for signals intelligence, the thermal signature of a GCS provides a secondary and highly precise targeting vector. Military-grade control elements, computing hardware, cryptographic systems, and the data link terminals require significant electrical power.11 This power is predominantly supplied by fuel-combusting generators or drawn from vehicle alternators.
The conversion of chemical energy to electrical power, and the subsequent operation of high-performance computing equipment, generates substantial heat. Air conditioning units are frequently required to cool the electronic infrastructure within shelters or vehicles, further increasing power consumption and heat exhaust.11 This creates a massive thermal contrast against the ambient environment. In environments where the background temperature is relatively low, thermal imaging and infrared sensors can identify the presence of a GCS from distances spanning several kilometers.11
Even when operations are paused and engines are switched off, the latent heat retained in generator exhaust manifolds, vehicle firewalls, and engine compartments continues to glow brightly on thermal sensors.12 Furthermore, the human operators themselves contribute to the thermal footprint. Modern thermal imaging technology identifies infrared radiation emitted by objects based on their absolute temperature, operating effectively in complete darkness and capable of detecting heat signatures through gaps in foliage or traditional visual camouflage.13
Physical Footprint and Acoustic Indicators
Beyond the invisible electromagnetic and thermal spectrums, the physical deployment of a C2 node creates visual and acoustic anomalies. A larger GCS requires specialized vehicles, telescopic antenna masts, support shelters, fuel storage, and personnel movement. This logistics footprint differentiates the site from civilian or natural surroundings, making it susceptible to identification by high-resolution satellite imagery or long-range optical sensors.11
The acoustic signature generated by portable generators, vehicle engines, and the high-frequency whine of cooling fans provides auditory cues to adversary acoustic detection systems or dismounted reconnaissance units.14 These physical and auditory indicators provide confirmation data once an adversary has localized the general area of a node using radio frequency direction-finding, allowing them to pinpoint the exact coordinates for a kinetic strike.
4. Adversary Threat Landscape: The Russian Federation
The vulnerabilities of ground control elements must be evaluated against the sophisticated targeting capabilities developed by peer adversaries. The Russian Federation has spent decades refining a doctrine that treats electronic warfare not as a supporting function, but as a primary combat arm designed to dismantle the enemy’s ability to command and control forces.15
The Reconnaissance-Strike and Reconnaissance-Fire Contours
Russian military doctrine operates on the concepts of the Reconnaissance-Strike Complex (RUK) and the Reconnaissance-Fire Complex (ROK). The reconnaissance-strike complex refers to the coordinated employment of high-precision, long-range weapons linked to real-time intelligence data provided to a fused fire-direction center, typically operating at the operational or strategic depth.16 The reconnaissance-fire contour is its tactical equivalent, relying on artillery, mortar units, and drone assets to crush enemy formations near the forward line of contact.17
These complexes are designed specifically to wage “noncontact warfare,” utilizing deep precision fires to hold enemy nodes at risk.16 Central to this capability is Russia’s extensive inventory of mobile electronic warfare platforms. Systems such as the R-330Zh Zhitel are deployed explicitly to locate and disrupt enemy communications. The Zhitel system, mounted on a cargo chassis for high mobility, is designed for the automated detection, direction-finding, and analysis of radio signals operating between 100 MHz and 2,000 MHz.19 With an estimated operational range of up to 25 kilometers, the Zhitel can detect the specific radio control signals emitted by drone operators, establish a fix on the ground station, and instantaneously transmit those coordinates to artillery batteries or missile units.19
The Proliferation of Loitering Munitions
While traditional artillery serves as the primary kinetic effector, Russian forces are increasingly closing the tactical sensor-to-shooter gap through the mass incorporation of loitering munitions.17 Systems such as the Zala Lancet-3 and the Vostok Scalpel effectively fuse the sensor and the effector into a single platform.17 Once an operator’s general location is identified via direction-finding, a loitering munition is dispatched to the area. Utilizing advanced optical sensors, the munition hunts for the thermal or visual signature of the GCS vehicle, antenna mast, or personnel before initiating a terminal dive.
Recent intelligence indicates that Russian developers are aggressively upgrading these systems to operate beyond the constraints of traditional radio line-of-sight. Debris from Lancet munitions recovered in central Kyiv—over 200 kilometers from the nearest Russian lines—suggests the integration of decentralized mesh modem architectures and artificial intelligence modules based on advanced computing platforms.22 By granting these munitions autonomous targeting capabilities, Russian forces can dispatch them into areas where signal jamming prevents direct control, allowing the AI to independently identify and strike command nodes based on pre-programmed visual or thermal profiles.22 Furthermore, the utilization of Orlan-30 drones equipped with laser designators allows Russian forces to illuminate stationary C2 nodes for precision-guided artillery shells like the 152-mm Krasnopol or air-to-surface missiles, creating a highly responsive and resilient kill chain that is exceedingly difficult to disrupt.17
5. Adversary Threat Landscape: The People’s Republic of China
While the Russian military focuses heavily on kinetic artillery integration, the People’s Liberation Army of China approaches the vulnerability of enemy command networks through a distinct doctrinal framework known as “System of Systems” (SoS) warfare.24
System Destruction Warfare
The PLA conceptualizes modern conflict as a confrontation between opposing operational systems rather than a simple clash of massed forces. System Destruction Warfare aims not to annihilate the enemy physically, but to disrupt, paralyze, or destroy the critical nodes that allow the adversary’s operational system to function cohesively.25 Under this doctrine, the PLA specifically targets the data links, information network sites, and command, control, communications, computers, intelligence, surveillance, and reconnaissance (C4ISR) capabilities of the opposing force.25
If the United States deploys a vast swarm of autonomous drones, the PLA’s primary objective is not to shoot down every drone, but to blind or destroy the ground control stations and orchestration nodes managing the swarm. By severing the communication links, the autonomous platforms lose their synchronized intelligence and become ineffective, rendering the technological advantage moot.
To execute this strategy, the PLA has integrated artificial intelligence into a decentralized kill web designed to overwhelm enemy forces in high-intensity environments. Unlike traditional linear kill chains, the Chinese model allows assets to swap roles dynamically, orchestrated by central nodes such as KJ-500 airborne early warning and control aircraft.27
Spectrum Dominance and Targeting Capabilities
The PLA has produced specific targeting protocols for electronic warfare attacks, explicitly listing the radars, sensors, and communication systems of US formations as high-priority targets.28 To locate these targets, China fields a sophisticated array of signals intelligence and electronic warfare platforms. Unmanned systems such as the FH-95 are deployed to provide near-real-time reconnaissance and EW disruption capabilities deep into contested airspace.30 Larger platforms, such as the Y-9JB special mission aircraft, utilize fields of blade antennas and circular interferometer arrays to measure the angle of arrival of electromagnetic signals, allowing them to passively calculate precise bearings to enemy drone control stations without emitting detectable radar signatures themselves.31
Once a node is located, the PLA can employ traditional precision-guided munitions or utilize heavily equipped J-16 electronic attack aircraft to deliver overwhelming noise and deceptive jamming, neutralizing the GCS’s ability to communicate.27 Furthermore, the PLA is rapidly developing non-nuclear electromagnetic pulse weapons designed to deliver targeted pulses of radiation across specific frequency bands.32 These weapons are intended to induce massive electrical charges in conductive materials, instantly destroying unhardened electronic systems at the speed of light. Because many C2 systems and legacy platforms remain inadequately hardened against EMP effects, a targeted strike could permanently disable the electronic infrastructure required to operate a drone fleet before conventional hostilities even commence.32
| Adversary Doctrine | Primary Targeting Methodology | Key Systems & Platforms | Impact on Drone Operations |
| Russian Federation | Reconnaissance-Fire Contours; rapid linkage of EW detection to artillery/loitering kinetic strikes. | R-330Zh Zhitel, Zala Lancet-3, Orlan-30, Tornado-S MLRS. | Forces extreme standoff distances; high attrition rate of stationary operators via kinetic fires. |
| People’s Republic of China | System Destruction Warfare; severing C4ISR networks and blinding data links via AI kill webs. | KJ-500 AWACS, Y-9JB SIGINT aircraft, FH-95 EW drones, EMP munitions. | Paralyzes entire drone swarms by isolating or destroying the central GCS orchestration nodes. |
6. Operational Realities: Lessons from the Ukrainian Theater
The ongoing conflict in Ukraine serves as the most comprehensive, data-rich laboratory for modern uncrewed operations. It has systematically dismantled pre-war academic theories which posited that drones would either deliver decisive strategic victories unchallenged, or be entirely neutralized by traditional air defenses without achieving tactical impact.33 Instead, the operational reality has emerged as a grueling domain characterized by mass production, extreme attrition, and a highly lethal, transparent electromagnetic environment where the survival of the operator dictates the success of the mission.33
The Electromagnetic Attrition of the Operator
While public discourse and procurement offices often fixate on the destruction of armored vehicles by cheap quadcopters, the unseen and arguably more critical battle is the continuous electronic contest to locate, isolate, and eliminate the human operator orchestrating the attack. In Ukraine, the sheer density of unmanned systems has created an incredibly cluttered segment of the electromagnetic spectrum. It is reported that the Ukrainian defense industry produces hundreds of thousands of first-person view drones annually, necessitating a massive number of active control frequencies.35
In active sectors of the front line, dozens of drone teams frequently compete for a limited number of radio channels. If operators fail to utilize sophisticated de-confliction procedures, their signals interfere, resulting in immediate drone crashes. This congestion often forces teams to delay launches, reducing operational tempo.36
However, the primary threat to these operators is the pervasive presence of Russian electronic warfare. Frontline data indicates that up to 31 percent of all FPV drone sorties fail due to enemy jamming severing the control link.36 Furthermore, operators are vulnerable to friendly fire jamming, with Ukrainian forces frequently activating portable jammers upon hearing any drone acoustic signature due to the inability to distinguish friend from foe.36
When a drone team powers on its equipment to establish a connection, it instantly alerts adversary direction-finding systems. To mitigate the risk of immediate counter-battery artillery fire or Lancet strikes, operators have been forced to push their operational standoff distances to the absolute limit of their equipment, frequently situating themselves up to 10 kilometers away from the intended target zone.36 This vast physical separation introduces new challenges, as radio-controlled drones require a clear line of sight. Buildings, terrain, and the curvature of the earth degrade signal quality as the drone descends toward its target, forcing operators to execute blind terminal dives and rely on inertia to secure a hit.36
The Mathematics of Shoot-and-Scoot Tactics
To survive in an environment where any radio frequency emission invites rapid kinetic retaliation, ground control personnel have adopted “shoot-and-scoot” tactics traditionally utilized by self-propelled artillery units. Mathematical modeling of these tactics demonstrates a direct correlation between stationary transmission time and the probability of destruction. While remaining in a single location allows operators to launch multiple drones rapidly and adjust to the environment, it exponentially increases the risk of the adversary’s counter-battery radar or EW sensors achieving a precise fix.37
For drone teams, this dictates strict operational timelines. Planners must establish maximum threshold times for remaining “loud” on the spectrum. Once a mission concludes, or the transmission time limit is reached, the node must immediately cease all RF emissions. Post-mission procedures emphasize restoring any physical camouflage disrupted during the launch to avoid detection from loitering surveillance drones cued by the initial RF burst, followed by an immediate physical relocation to a new launch site.39 This constant necessity for movement severely limits the continuous operational up-time of the drone fleet, highlighting the friction between maximizing offensive lethality and preserving operator lives.
Radical Adaptations: Fiber Optics and Extreme Standoff
The intense pressure of the electromagnetic environment has driven radical technological adaptations. One of the most significant shifts is the operational deployment of drones controlled entirely by fiber-optic cables.40 By trailing a physical spool of micro-fiber rather than relying on radio wave propagation, operators completely negate the threat of RF jamming, spoofing, and direction-finding.36 This allows the drone to operate unhindered in dense EW environments while simultaneously eliminating the RF beacon that exposes the operator’s location to the enemy. While fiber optics introduce physical constraints—such as wires limiting maneuverability or snapping on terrain—the adoption of this technology underscores the desperate necessity to sever the RF link between the operator and the aircraft.36
Conversely, when physical tethers are impossible, survival requires expanding the control link to unprecedented distances. This was demonstrated when a Ukrainian pilot successfully intercepted and destroyed two Russian Shahed loitering munitions using a specialized STING interceptor drone controlled from a distance of 500 kilometers.41 This operation, enabled by advanced digital control ecosystems providing low-latency, high-definition video over massive distances, represents a fundamental shift in operator survivability.41 By physically removing the operator hundreds of kilometers from the tactical edge, the human element is completely insulated from tactical counter-battery fire and localized electronic warfare, preserving the highly trained personnel regardless of the attrition rate of the interceptor drones themselves.
7. Modernizing Signature Management and Emission Control
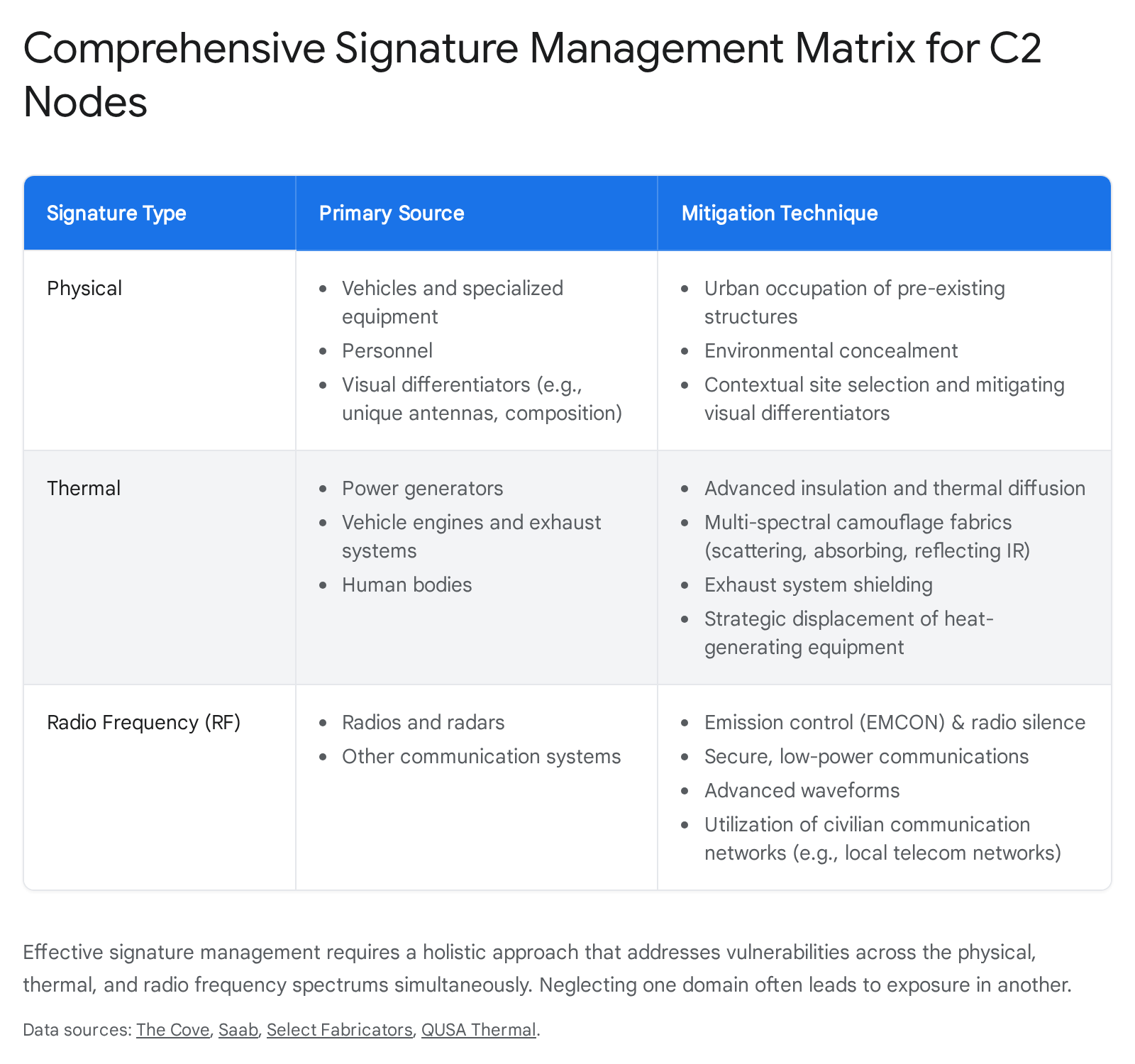
If the Department of Defense is to successfully field the massive quantities of systems envisioned by the Replicator initiatives without incurring catastrophic personnel losses, doctrinal concepts must evolve far beyond basic visual camouflage and rigid, binary concepts of radio silence.3 A holistic approach to Signature Management and Emission Control (EMCON) is required to actively shield command and control nodes across the entire multi-spectral environment.
Expanding the Scope of EMCON
Historically, the application of EMCON has been primarily centered on the simple mitigation of radio frequency emissions from radios and radars, often resulting in complete radio silence which degrades command functionality.14 Modern EMCON must be redefined as the selective, intelligent, and controlled use of electromagnetic, acoustic, and other emitters to optimize C2 capabilities while minimizing the risk of adversary detection.43 This requires units to dynamically adjust their emissions based on real-time threat assessments in the operational environment.
Developing robust EMCON Standing Operating Procedures requires specialized training. Planners must appoint dedicated signature management officers within operations cells to coordinate with intelligence and communications cells, ensuring that all maneuvering elements are synchronized in their spectrum usage.14 Operators must be trained to understand the specific radiation patterns of their internal electronic components. For instance, personnel must practice aiming directional LOS and BLOS antennas at optimal angles that utilize terrain masking, intentionally blocking the signal’s side lobes from reaching adversary sensors positioned near the forward line of contact.11
Furthermore, EMCON SOPs must incorporate the strategic use of civilian communication infrastructure. When the tactical situation permits, utilizing low-earth orbit satellite networks like Starlink or routing data through local civilian telecommunications networks allows military nodes to blend their RF signatures into the ambient civilian background noise, making it significantly harder for adversary signals intelligence to isolate the military transmitter.14
Thermal Shielding and Multispectral Camouflage
Managing the thermal signature is widely recognized as the most difficult aspect of nodal survivability.14 The heat generated by power generators and recently driven vehicles provides a beacon for infrared sensors. Mitigating this requires advanced insulation and strategic displacement. Heat-generating equipment, such as massive power generators, should be placed at a substantial physical distance from the primary command post and the operators themselves. This physical separation diffuses the thermal concentration, forcing adversary sensors to evaluate a wider area and decoupling the primary heat source from the critical personnel.14
Engineered thermal shielding applied directly to equipment has proven highly effective. Complex insulation structures applied to vehicle exhaust manifolds, firewalls, and engine compartments can reduce exterior heat signatures from 600°C down to 110°C, significantly shrinking the thermal footprint and preventing heat ingress into the operator cabin.12
However, structural shielding must be paired with advanced multispectral camouflage. Standard visual camouflage netting is obsolete against modern Persistent Intelligence, Surveillance, Target Acquisition, and Reconnaissance (ISTAR) environments characterized by drones equipped with multi-sensor payloads.44 Units must deploy advanced fabrics, such as those utilizing LUNA Select technology, which are designed to scatter, absorb, and reflect infrared radiation.45 These materials adapt to temperature changes, providing a layered defense against near-infrared, mid-wave infrared, and long-wave infrared detection.45
Crucially, signature management planners must be trained to avoid creating thermal anomalies. If thermal blankets are used aggressively to block heat in a warm environment, the resulting localized “cold spot” relative to the ambient background temperature will stand out to a thermal imager just as clearly as a heat source. This temperature contrast will alert an adversary to the presence of hidden assets, prompting them to apportion additional ISR resources to the anomalous area.14 Effective camouflage requires matching the background temperature precisely, not simply eliminating heat entirely.
8. Structural Decoupling: Standoff and Antenna Remoting
Even with the most rigorous EMCON protocols and advanced multispectral camouflage, a ground control station must eventually emit detectable signals to accomplish its mission during active operations. Because completely hiding the signal is often physically impossible, the architecture of the C2 node must be designed to structurally decouple the human operator from the point of emission. This ensures that the warfighter survives the inevitable detection and subsequent targeting of the transmission antenna.
Tactical Remote Split Operations (TRSO)
The concept of remote split operations is deeply embedded in US military doctrine, originally developed to allow operators sitting in the continental United States to fly strategic assets like the MQ-9 Reaper over foreign theaters via massive satellite relays.46 However, this concept must now be aggressively scaled down and applied to the tactical level. Tactical Remote Split Operations involve physically separating the pilot and payload operator workstations from the actual transmission antennas controlling Group 1 through 3 drones.47
This critical separation is primarily achieved through the implementation of Radio Frequency over Fiber (RFoF) technology. RFoF systems intercept the drone’s flight control RF signals generated at the operator’s controller, convert those signals into modulated optical waveforms, and transmit them over expendable single-mode fiber-optic cables to a remote antenna site located far from the operator.49 At the remote site, the optical signal is converted back into an RF signal, amplified, and broadcast to the drone. The return telemetry and video signals follow the reverse path.
This technology allows the transmission antenna—which is the primary target for adversary direction-finding algorithms and anti-radiation missiles—to be placed several kilometers away from the human operators.49 If an adversary successfully detects the emission and executes a kinetic strike, the remote antenna hardware is destroyed, but the highly trained personnel survive unharmed, ready to plug their controllers into a secondary antenna node and immediately resume operations. This transforms the antenna into an attritable asset, mirroring the attritable nature of the drones themselves.
Extended Standoff Capabilities and Mobility
Advancements in remote tracking technologies further enhance this standoff capability, providing unparalleled distance between the operator and the battlespace. Modern Long Range Tracking Antennas (LRTA) provide omnidirectional and directional tracking that can maintain robust command and control over unmanned platforms at ranges extending from 60 kilometers up to 130 miles, even in congested and contested RF environments.50
By utilizing auto-calibrating, multi-band tracking systems mounted on collapsible parabolic dishes, operators can remain deeply hidden within complex urban structures or dense forested terrain, far behind the forward line of own troops, while maintaining uninterrupted command over assets conducting strikes at the zero line.51
This decoupled architecture inherently necessitates a shift toward high mobility. Mobile Ground Control Stations, designed for rapid deployment and straightforward operation in austere environments, allow operators to adhere strictly to shoot-and-scoot survival timelines.52 By utilizing compact, portable structures rather than large, fixed-site installations, operators can launch a system, monitor the mission, pass control to an adjacent node if necessary, and physically relocate their equipment before adversary kill chains have the time to complete their detection-to-strike cycle.52
9. Architectural Resilience: Decentralization and Mesh Networking
The legacy architecture of military command and control relies heavily on centralized hubs. Massive, fixed-site installations or extensive Distributed Common Ground System nodes are traditionally designed to gather, process, exploit, and disseminate intelligence from multiple platforms across a theater.54 While highly efficient in permissive environments, these centralized nodes present glaring high-value targets in a high-intensity conflict against a peer adversary. They represent catastrophic single points of failure; the kinetic destruction or cyber disruption of one centralized DGCS hub could effectively blind an entire sector of airspace and ground operations.
To ensure the survivability of massive drone fleets and their operators, C2 architecture must evolve aggressively toward fully decentralized, self-healing mesh networks.57
The Power of Self-Healing Mesh Topology
A mesh network is a decentralized wireless communication system where every integrated device—referred to as a node—acts simultaneously as both a transmitter and a receiver.57 Instead of relying on a central command tower to route information, mesh communication distributes data routing dynamically across the entire network. In the context of modern drone operations, this means that every single drone in a swarm, every ground vehicle, and every dismounted operator carrying a compatible software-defined radio acts as a relay point within a unified, constantly shifting operational network.59
This architecture provides unparalleled resilience against both electronic warfare interference and physical attrition. If an adversary successfully detects and jams the direct line-of-sight signal between a drone and its primary operator, or kinetically strikes a specific C2 relay node, the network does not collapse. Instead, systems utilizing intelligent edge routing automatically evaluate all available communication paths in real-time, instantly selecting the optimal alternative route for every data packet.59 Telemetry and control data seamlessly reroute through other drones in the swarm or adjacent ground units, maintaining unbroken connectivity.57
Altering the Adversary’s Cost-to-Benefit Ratio
Transitioning to decentralized mesh architectures fundamentally alters the economic and tactical cost-to-benefit ratio for adversary targeting.60 In a centralized system, an adversary can easily justify expending a multi-million dollar precision-guided missile, such as a Russian Iskander, to destroy a single GCS housing critical intelligence personnel and the C2 uplink for a dozen drones.17
In a fully decentralized mesh network, that exact same operational capability is distributed across dozens of small, highly mobile split-teams equipped with man-portable radios.51 This diffusion of capability forces the adversary into a highly unsustainable economic exchange. They must attempt to identify and target individual, low-signature operators with high-end, expensive munitions—a strategy that rapidly depletes their precision-strike inventory without collapsing the US operational system.60
Furthermore, mesh infrastructure enables seamless control handoffs between operators across the battlespace. A drone launched by a heavily concealed operator deep in the rear echelon can be seamlessly handed off to a forward-deployed infantry unit for terminal guidance, and then handed off again to an artillery spotter, ensuring that no single operator maintains a prolonged RF link that can be easily traced by direction-finding equipment.27 When coupled with advanced encryption standards (AES-256) and cyber survivability attributes, warfighters ensure that data moving across these dynamic pathways remains completely secure from interception, even as the physical routing constantly shifts.62
| Network Architecture | Routing Mechanism | Vulnerability Profile | Impact of Node Loss |
| Centralized (Hub-and-Spoke) | All data flows through a primary Ground Control Station or DCGS node. | High. Creates a massive, singular RF and thermal beacon. | Catastrophic. Loss of hub disables all connected drones in the sector. |
| Decentralized (Mesh Network) | Data routes dynamically through all available drones and operator radios. | Low. Signatures are distributed; no single high-value target exists. | Minimal. Network automatically self-heals and reroutes data around the destroyed node. |
10. Doctrinal Adaptation and Force Design Implications
The successful implementation of autonomous initiatives and the broader integration of uncrewed systems into the joint force requires more than the procurement of advanced hardware. It demands a fundamental transformation in military doctrine, force design, and training methodologies to ensure that the personnel operating these systems can survive the modern, sensor-rich battlefield.
Rethinking Tactical Assembly Areas and Dispersion
Current operational training observations highlight a dangerous lag in doctrinal adaptation. Aviation task forces and drone units consistently establish large, static Tactical Assembly Areas that resemble the exposed, sprawling command posts utilized during previous counter-insurgency conflicts in permissive environments.63 This practice is fatal against peer threats equipped with space-based sensors, advanced electronic warfare, and mass loitering munitions.63
The Russian-Ukraine conflict has definitively demonstrated how vulnerable strategic and tactical assets are when they remain stationary in clustered formations.63 Commanders must deliberately plan for the extreme, permanent dispersion of their assets. Aircraft, drone launch rails, Class III/V resupply points, maintenance teams, and mission command elements must be broken down into highly decentralized, mobile nodes spread across a wide geographical footprint.63 Ground equipment requires constant cover and concealment, while the survivability of the command elements depends on their inherent agility and constant movement.63
Applying Special Operations Methodologies to Conventional Forces
To achieve this necessary dispersion, conventional forces must look to the methodologies honed by Special Operations Forces. Modern battlefields demand agility, deception, and timely action. Special Forces employ these characteristics through split-team operations—deliberately dividing into small, independent elements, sometimes down to singleton operators, to achieve stealth and increased operational coverage behind enemy lines.61
Institutionalizing this approach across conventional units, such as Marine Corps expeditionary forces or Army Brigade Combat Teams, requires codifying these procedures into standard operations.8 Rather than operating a drone fleet from a centralized command tent, forces must be trained to operate in dispersed split-teams, infiltrating, persisting, and rapidly cueing joint effects while maintaining a minuscule physical and electronic footprint.61
Multi-Tiered Manning and Composite Formations
The personnel structure must also adapt to the sheer scale and complexity of managing these dispersed fleets. As the variety of UAS expands—ranging from simple, hand-launched surveillance quadcopters to complex, networked swarms of kinetic effectors—the military can no longer rely on a one-size-fits-all approach to the drone operator.
The implementation of a multi-tiered approach to manning UAS operators is strictly necessary.48 This approach should encompass:
- Additional Duty Operators: Infantrymen trained to operate simple, attritable Group 1 systems for immediate, line-of-sight situational awareness.
- Designated Position Operators: Personnel embedded within platoons whose primary role is managing slightly more complex systems, requiring specialized training in EMCON and signature management.
- MOS-Specific Roles: Highly specialized personnel holding a dedicated Military Occupational Specialty, tasked with operating complex, beyond-line-of-sight systems, managing mesh network C2 architecture, and orchestrating multi-domain swarms.48
Furthermore, these specialized operators cannot fight in isolation. The concept of the Composite Air Defense formation must be applied to drone operations. These are permanent, modular organizations designed to integrate kinetic shooters, electronic warfare teams, multispectral sensors, and signature-management units under a unified command structure.64 By integrating EW and decoys directly alongside the drone operators, commanders can generate multiple defeat chains rapidly while actively shielding their own C2 nodes from adversary targeting.64
11. Strategic Recommendations for Defense Leadership
The push to field thousands of autonomous systems at the speed of relevance is a necessary strategic endeavor to counter peer adversaries. However, leadership must recognize that the autonomous drone is only the tip of the spear; the shaft is the communication network, and the hand wielding it is the human operator. Protecting that hand is an absolute strategic imperative that must shape future procurement and doctrine.
Procurement strategies must shift to holistically fund the entire UAS ecosystem, rather than fixating solely on the airframe. Acquiring thousands of attritable drones without simultaneously procuring the necessary multispectral camouflage, RF-over-Fiber remoting equipment, and mesh network radios will result in catastrophic personnel losses in the opening hours of a high-intensity conflict. The attrition of irreplaceable human operators will instantly neutralize the numerical advantage of the drone swarms they control.
Defense leadership must prioritize immediate investments in mandating remote antenna systems for all future tactical GCS designs, ensuring physical separation between the operator and the RF emitter. Furthermore, all C2 nodes, power generators, and support vehicles must be outfitted with advanced, adaptive thermal shielding and radar-absorbent materials as a baseline requirement, not an optional upgrade. Finally, the modernization of communication infrastructure from legacy point-to-point data links to self-healing mesh architectures must be accelerated to eliminate centralized points of failure. In the modern battlespace, technological overmatch is temporary, and the electromagnetic spectrum is completely transparent. The ultimate metric for the success of future unmanned deployments will not be defined solely by the lethality of the drone, but by the survivability, agility, and spectral discipline of the human operators commanding them.
Works cited
- Joint Interagency Task Force Announces First Replicator 2 Purchase to Counter Homeland Drone Threats – Department of War, accessed April 24, 2026, https://www.war.gov/News/News-Stories/Article/Article/4377021/joint-interagency-task-force-announces-first-replicator-2-purchase-to-counter-h/
- Replicator and beyond: The future of drone warfare – Brookings Institution, accessed April 24, 2026, https://www.brookings.edu/events/replicator-and-beyond-the-future-of-drone-warfare/
- DOD Innovation Official Discusses Progress on Replicator – Department of War, accessed April 24, 2026, https://www.war.gov/News/News-Stories/Article/Article/3999474/dod-innovation-official-discusses-progress-on-replicator/
- DOD touts ‘successful transition’ for Replicator initiative — but questions linger, accessed April 24, 2026, https://defensescoop.com/2025/09/03/dod-replicator-drone-tech-transition-fielding-questions-linger/
- Implementing DoD Replicator Initiative at Speed and Scale – Defense Innovation Unit, accessed April 24, 2026, https://www.diu.mil/latest/implementing-the-department-of-defense-replicator-initiative-to-accelerate
- The Army Needs to Quickly Adapt to Tactical Drone Warfare – Fort Benning, accessed April 24, 2026, https://www.benning.army.mil/infantry/magazine/issues/2024/Summer/pdf/10-Padalino_txt.pdf
- Continuous Transformation: Transforming in Contact with Future Unmanned Aircraft Systems | Article – U.S. Army, accessed April 24, 2026, https://www.army.mil/article/280379/continuous_transformation_transforming_in_contact_with_future_unmanned_aircraft_systems
- Marine Corps looking into new medium-range tactical drone as it pushes small UAS capabilities | DefenseScoop, accessed April 24, 2026, https://defensescoop.com/2026/02/17/marine-corps-medium-range-tactical-drone-suas/
- Towards the Unmanned Aerial Vehicle Traffic Management Systems (UTMs): Security Risks and Challenges – arXiv, accessed April 24, 2026, https://arxiv.org/html/2408.11125v1
- Handover Management for Drones in Future Mobile Networks—A Survey – PMC, accessed April 24, 2026, https://pmc.ncbi.nlm.nih.gov/articles/PMC9460841/
- The Vulnerabilities of Unmanned Aircraft System Components …, accessed April 24, 2026, https://www.japcc.org/chapters/c-uas-the-vulnerabilities-of-unmanned-aircraft-system-components/
- Thermal Insulation for Military & Armored Applications, accessed April 24, 2026, https://qusathermal.com/military-and-armored-applications/
- Thermal Imaging Stealth: Tactics for Staying Undetected | UF PRO Blog, accessed April 24, 2026, https://ufpro.com/us/blog/thermal-imaging-stealth-tactics
- Expanding the Scope of Emissions Control to Enhance Command …, accessed April 24, 2026, https://cove.army.gov.au/article/expanding-scope-emissions-control-enhance-command-and-control-node-survivability-within-3rd-combat-brigade
- Russia’s Electronic Warfare Capabilities to 2025 – International Centre for Defence and Security, accessed April 24, 2026, https://icds.ee/wp-content/uploads/2018/ICDS_Report_Russias_Electronic_Warfare_to_2025.pdf
- Operational Fires in the Age of Punishment – CSIS, accessed April 24, 2026, https://www.csis.org/analysis/operational-fires-age-punishment
- Adaptation Under Fire: Mass, Speed, and Accuracy Transform Russia’s Kill Chain In Ukraine, accessed April 24, 2026, https://cepa.org/comprehensive-reports/adaptation-under-fire-mass-speed-and-accuracy-transform-russias-kill-chain-in-ukraine/
- PR_20-3186_Russian Electronic, Information, Navigation, Reconnaissance-Strike and -Fire Operations – DTIC, accessed April 24, 2026, https://apps.dtic.mil/sti/pdfs/AD1123309.pdf
- Key Electronic Warfare Systems Destroyed in Russia Before Reaching Combat Zone – Kyiv Post, accessed April 24, 2026, https://www.kyivpost.com/post/47304
- R-330Zh Zhitel Russian Cellular Jamming and Direction Finding System – ODIN, accessed April 24, 2026, https://odin.t2com.army.mil/WEG/Asset/R-330Zh_Zhitel_Russian_Cellular_Jamming_and_Direction_Finding_System
- Russian Electronic Warfare Systems – Sprotyv G7, accessed April 24, 2026, https://sprotyvg7.com.ua/wp-content/uploads/2023/11/COGINT_Analytic_Insight_Report_Russian_EW_Systems__231119_114942.pdf
- News – Ukraine’s Military Intelligence publishes data on Russian Loitering Munition production – SAE Media Group, accessed April 24, 2026, https://www.smgconferences.com/editors-corner/6660-news–ukraines-military-intelligence-publishes-data-on-russian-loitering-munition-production
- Ukraine, the case of the LANCET loitering munition over Kyiv – Future Warfare Magazine, accessed April 24, 2026, https://www.fw-mag.com/shownews/977/ukraine-the-case-of-the-lancet-loitering-munition-over-kyiv
- Systems Confrontation and System Destruction Warfare: How the Chinese People’s Liberation Army Seeks to Wage Modern Warfare | RAND, accessed April 24, 2026, https://www.rand.org/pubs/research_reports/RR1708.html
- System Destruction Warfare and the PLA – National Defense University, accessed April 24, 2026, https://keystone.ndu.edu/Portals/86/PLA%20Systems%20Attack%20-%20Keystone%2025-1%20Jan%2025.pdf
- Winning the Kill Chain Competition – Mitchell Institute for Aerospace Studies, accessed April 24, 2026, https://www.mitchellaerospacepower.org/app/uploads/2023/05/Scale_Scope_Speed_Survivability_-KillChain_-Policy_Paper_40-New.pdf
- The New Chinese Kill-Web – by Amir Husain – Medium, accessed April 24, 2026, https://medium.com/@amirhusain_tx/the-new-chinese-kill-web-e3862eeb5119
- PLA’s electronic war ‘kill list’, ultra-powerful laser cutter sold: 7 science highlights, accessed April 24, 2026, https://www.scmp.com/news/china/science/article/3291137/plas-electronic-war-kill-list-ultra-powerful-laser-cutter-sold-7-science-highlights
- Kill chain clash: China and US battle for all-domain supremacy – Asia Times, accessed April 24, 2026, https://asiatimes.com/2024/12/kill-chain-clash-china-and-us-battle-for-all-domain-supremacy/
- China’s UAS Revolution Advances From Prototype To Practical Application – T2COM G2, accessed April 24, 2026, https://oe.t2com.army.mil/product/chinauasrevolution/
- Special Mission Aircraft and Unmanned Systems – Johns Hopkins University Applied Physics Laboratory, accessed April 24, 2026, https://www.jhuapl.edu/sites/default/files/2022-12/SpecialMissionAircraftandUnmannedSystems.pdf
- EMP Weapons Expose PRC Military Vulnerability – Small Wars Journal, accessed April 24, 2026, https://smallwarsjournal.com/2026/01/25/emp-weapons-expose-prc-military-vulnerability/
- Drone Warfare in Ukraine: From Myths to Operational Reality – Part 1, accessed April 24, 2026, https://researchcentre.army.gov.au/library/land-power-forum/drone-warfare-ukraine-myths-operational-reality-part-1
- Drones have boots: Learning from Russia’s war in Ukraine – Taylor & Francis, accessed April 24, 2026, https://www.tandfonline.com/doi/full/10.1080/13523260.2023.2262792
- Ukranian Loitering Munitions Market – Teal Group, accessed April 24, 2026, https://tealgroup.com/index.php/teal-group-media-news-briefs-2/teal-group-news-media/item/russian-loitering-munitions-market-copy
- I Fought in Ukraine and Here’s Why FPV Drones Kind of Suck, accessed April 24, 2026, https://warontherocks.com/i-fought-in-ukraine-and-heres-why-fpv-drones-kind-of-suck/
- Optimizing Firing Position in Artillery Shoot-and Scoot Tactics ‹ Carmenta, accessed April 24, 2026, https://carmenta.com/knowledge/optimizing-firing-position-in-artillery-shoot-and-scoot-tactics
- An Analysis of Artillery Shoot-and-Scoot Tactics – Calhoun, accessed April 24, 2026, https://calhoun.nps.edu/server/api/core/bitstreams/bf0c6584-f0a6-4f8d-b38d-11d2a62e2e5e/content
- Gunline Survival against Loitering Munitions: Lessons from Ukraine | The Cove, accessed April 24, 2026, https://cove.army.gov.au/article/gunline-survival-against-loitering-munitions
- Video – Drones – Lessons from Ukraine (master) – DVIDS, accessed April 24, 2026, https://www.dvidshub.net/video/984317/drones-lessons-ukraine-master
- Ukrainian Pilot Sets World Record—Two Shaheds Downed From 500 km Using STING Interceptor, Video – UNITED24 Media, accessed April 24, 2026, https://united24media.com/latest-news/ukrainian-pilot-sets-world-record-two-shaheds-downed-from-500-km-using-sting-interceptor-video-17600
- COUNTERAIR OPERATIONS – Air Force Doctrine, accessed April 24, 2026, https://www.doctrine.af.mil/Portals/61/documents/AFDP_3-01/3-01-AFDP-COUNTERAIR.pdf
- Adapting to Multi-Domain Battlefield: Developing Emissions Control …, accessed April 24, 2026, https://www.army.mil/article/284546/adapting_to_multi_domain_battlefield_developing_emissions_control_sop
- Market for Multispectral Camouflage May 2025 – Prnewswire.com, accessed April 24, 2026, https://mma.prnewswire.com/media/2697045/MultispectralCamouflageMarket_May2025_PickwickCapital.pdf?p=pdf
- IR and Thermal Signature Reduction and Shielding – Select Fabricators, accessed April 24, 2026, https://www.select-fabricators.com/ir-and-thermal-signature-reduction-and-shielding/
- UAV Ground Control Station (GCS) – Intelligence Resource Program, accessed April 24, 2026, https://irp.fas.org/program/collect/uav_gcs.htm
- Operational Requirements Document for the Unmanned Aerial Vehicle (UAV) Tactical Control System (TCS) version 3.0 – Intelligence Resource Program, accessed April 24, 2026, https://irp.fas.org/program/collect/uav_tcs_ord.htm
- Tactical UAS: Three-Tiered UAS Manning for Increased Lethality and Situational Awareness, accessed April 24, 2026, https://www.lineofdeparture.army.mil/Journals/Infantry/Infantry-Archive/Winter-2024-2025/Three-Tiered-UAS-Manning/
- Drone and UAV RFoF Remote Antenna – RFOptic, accessed April 24, 2026, https://rfoptic.com/Downloads/drones-and-UAVs/Drone-and-UAV-RFoF-Remote-Antenna.pdf
- Antennas | UAV Ground Control Solutions (GCS) | AV – AeroVironment, Inc., accessed April 24, 2026, https://www.avinc.com/uas/network-connectivity/antennas
- UAS Ground Control Station (GCS) Solutions – Persistent Systems, accessed April 24, 2026, https://persistentsystems.com/solutions/uas-gcs/
- The Role of Mobile Ground Control Stations in Modern UAV Operations, accessed April 24, 2026, https://www.unmannedsystemstechnology.com/feature/the-role-of-mobile-ground-control-stations-in-modern-uav-operations/
- UAV Ground Control Stations (GCS) Market Size, Growth [2034] – Fortune Business Insights, accessed April 24, 2026, https://www.fortunebusinessinsights.com/unmanned-aerial-vehicle-uav-ground-control-stations-gcs-market-108813
- Distributed Common Ground System – Wikipedia, accessed April 24, 2026, https://en.wikipedia.org/wiki/Distributed_Common_Ground_System
- Air Force Distributed Common Ground System, accessed April 24, 2026, https://www.af.mil/About-Us/Fact-Sheets/Display/Article/104525/air-force-distributed-common-ground-system/
- Distributed Common Ground System (DCGS) | Collins Aerospace – RTX, accessed April 24, 2026, https://www.rtx.com/collinsaerospace/what-we-do/industries/military-and-defense/battle-management/dcgs
- Mesh Network Topologies and Architectures Explained – Mobilicom, accessed April 24, 2026, https://mobilicom.com/insight/mesh-network-topologies/
- Comparative Analysis of Centralized and Distributed Multi-UAV Task Allocation Algorithms: A Unified Evaluation Framework – MDPI, accessed April 24, 2026, https://www.mdpi.com/2504-446X/9/8/530
- Military Mesh Networking Technology – Rajant, accessed April 24, 2026, https://rajant.com/defense/military-technology/
- An Urgent Matter of Drones: Lessons for NATO from Ukraine – CEPA, accessed April 24, 2026, https://cepa.org/comprehensive-reports/an-urgent-matter-of-drones/
- Getting Small: Institutionalizing Split-Team Operations for Large Scale Combat Operations, accessed April 24, 2026, https://www.swcs.mil/Special-Warfare-Journal/Article/4340661/getting-small-institutionalizing-split-team-operations-for-large-scale-combat-o/
- On Uncrewed Special Operations C2 – Mission Driven Research, accessed April 24, 2026, https://www.missiondrivenresearch.com/on-uncrewed-special-operations-c2/
- Aviation TAA Survivability in the Multi-Domain Fight | Article | The United States Army, accessed April 24, 2026, https://www.army.mil/article/289112/aviation_taa_survivability_in_the_multi_domain_fight
- Composite Air Defense Artillery Formations: Converging Non-Kinetic and Kinetic Capabilities – Line of Departure, accessed April 24, 2026, https://www.lineofdeparture.army.mil/Journals/Air-Defense-Artillery/ADA-Archive/2026-E-Edition/Composite-Air-Defense/
